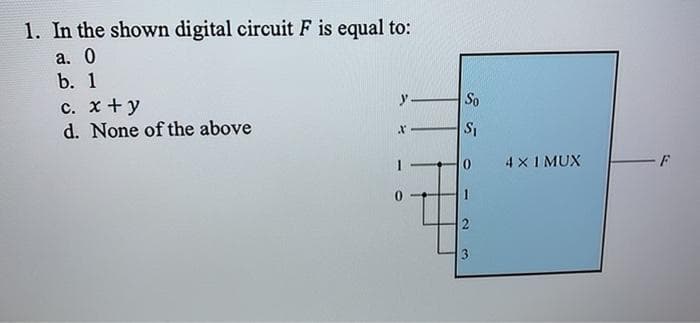
1. In the shown digital circuit F is equal to: а. 0 b. 1 c. x +y y- So d. None of the above 4 x I MUX 3
Q: What exactly does "software scope" mean?
A: Introduction: The scope of a software project is a clearly defined limit that comprises all of the a...
Q: Can you write a program in python for the dining philosopher problems that do not have deadlock? You...
A: The Dining Philosopher Problem – The Dining Philosopher Problem states that K philosophers seated ar...
Q: This syntax separates the execution of statements per labeled case so that there is no "fall-through...
A: The switch case has a switch variable and depending upon this switch variable the different switch c...
Q: C++ simple friend function. Create a C++ class called cube that calculates the volume of a cube. Use...
A: Code :- #include<iostream> using namespace std; class cube { public: double side; double volum...
Q: What is the difference between encoding and encrypting?
A: To differentiate between encoding and encrypting
Q: Abstraction is an important tool against complexity. It helps encapsulate constructs which would be ...
A: #include<iostream.h>#include<conio.h>#include<math.h> struct complex{float rel;flo...
Q: xplain with the aid of an illustration or block diagram how can FSK be
A: Lets see the solution.
Q: Is there a way to find out what the process ID of the first process that begins on a RedHat Enterpri...
A: Yes However, system on RHEL7 is not deterministic: PIDs are allocated in sequence but systemd runs...
Q: Problem 2 A number in base 2 (binary) is a number such that each of its digits is 0 or 1. To convert...
A: Introduction :
Q: What role does a security architecture play in the planning and implementation of a security infrast...
A: Creating and enforcing a security infrastructure using a security framework: « A security framework ...
Q: 8. The problem of template matching takes as input two nmatrices I[0 - 1,0 : n - 1] and T[0 m - 1,0:...
A: Proficient calculations for picture format matching on fine grained as well as medium grained MIMD h...
Q: Several instructions that are grouped into block enclosed in braces ({ }). Simple statements ...
A: According to the question this statements of braces are used for the program statements only and the...
Q: Give applications of the following patterns in problem solving: a. Power of 2 (2^n) b. Natural num...
A: In digital electronics, the power of 2 is used to implement logic circuits. In other words, the powe...
Q: The tamper-resistance attribute of a blockchain protects data that is stored on it. In what ways is ...
A: Introduction: Database in the conventional sense: These frameworks operate on a client-server model,...
Q: What is the router's boot-up procedure?
A: Router : A router is made up of numerous different sorts of parts. Any Cisco router, for example, wi...
Q: What are the three main issues that are causing problems for web-based applications?
A: Introduction: "The security of a web application is more challenging than the security of an infrast...
Q: If the buffer is unlimited and empty O a. Producer is blocked but consumer is not O b. Producer is n...
A: Ans: If the buffer is unlimited and empty is: b) Producer is not blocked but consumer is
Q: Because cache memory and random access memory (RAM) are both transistor-based, it is unclear why cac...
A: The size of cache memory is much smaller than the RAM.
Q: (a) Construct deterministic finite automata accepting the following languages: (i) {w e {0, 1}"| w i...
A:
Q: n of the MAC address during a T
A: Lets see the solution.
Q: H.W Find the inverse to the following matrices by using adjoint method. 1 a. A = 1 5 2 -5 -4 2. 3.
A: First Adjoint(A) and |A| needs to be calculated for getting the A-1.
Q: e in Python.
A: given - Build a web crawler function that starts with a URL representing a topic (a sport, your favo...
Q: What is the system catalogue, and how does it work? Please include at least three products for which...
A: Introduction: The system catalog is a set of tables that describe the database's structure. When a d...
Q: What exactly is autoscaling in the context of Microsoft Azure?
A: Introduction: When resources are dynamically allocated to satisfy performance needs, this is referre...
Q: Assume that there is a shared connection (for example, an Ethernet bus) with a speed of 1 Mbps. How ...
A: Introduction: The all-encompassing Ethernet LAN protocol has now been thoroughly examined. Today's E...
Q: Consider the structure of a categorization system. Describe the influence of increasing the regulari...
A: Introduction: Regularization: Regularization methods try to keep network weights as low as possible ...
Q: 1- A combinational circuit is defined by the following three functions F1= XY +XYZ F2= XY+ XYZ F3= X...
A:
Q: Discuss any one challenge in software evolution that is being built utilising agile approaches in a ...
A: Introduction: Agile approaches, which divide work into smaller iterations or sections, do not need l...
Q: In each, answer the following questions: Is AC B? Is BCA? Is either A or B a proper subset of the ot...
A: Below is the answer to above question. I hope this will meet your requirements...
Q: in CSS, In a short paragraph, explain how the Render Tree will differentiate from the DOM tree, and ...
A: The answer of this question is as follows:
Q: How to design CNN in Contactless Authentication System Using Hand Gestures Technique
A: Answer the above questions are as follows:
Q: Describe the various types of models which are used in software engineering.
A: Note: as per the guidelines I am solving only one question for you.kindly repost other questions. 2....
Q: When the DFA minimization algorithm merges states p and q, then a) p and q are dead-end states ...
A: DFA minimization is what? DFA minimization is a process in which the number of DFA states is reduc...
Q: and elabora
A: given - Compare and contrast the medium access protocols and elaborate any one of them.
Q: Column charts use:
A: We need to answer:
Q: 1. Find a connection between games and patterns. Look for a game in which patterns are involved. Exp...
A: Introduction 1. Find a connection between games and patterns. Look for a game in which patterns ar...
Q: Write a function call Occurrence that receives two arguments: an array of vectors (generic type) and...
A: Introduction
Q: Create a virtual machine in your mind.
A: EXPLANATION AND ANSWER: VIRTUAL MACHINE: A software-based system with its operating system on a host...
Q: Computer science Why is scope creep so common in information system design?
A: Introduction: Information System Design will be used to finish the project. A project is a client's ...
Q: Some of the devices in one of the buildings where your organisation has set up a network have comple...
A: Introduction: Protecting the network is critical today since there are many data breaches. The data ...
Q: What is the purpose of MAC filtering? When, if ever, would you use deny filtering rules and when, if...
A: Do you utilize refuse filtering rules in Mac Filtering? If so, when would you use allow filtering ru...
Q: I'm interested in learning more about how the Big Oh notations in Algorithms are implemented.
A: Introduction: The Big Oh sign is used to represent the upper bound on an algorithm's runtime, and he...
Q: Let U=(2,-1,0,-3) ,V=(1,-1,-1,3) and W=(1,3,-2,2) then U.V is:
A: Lets see the solution.
Q: When it comes to electronic payments, some credit card issuers provide a one-time-use credit card nu...
A: Yes definitely electronic payment gateways that need authentication. Because of the so many security...
Q: In what way does a netlist serve a purpose?
A: Typically, the netlist is a list of the electrical connections between components on a circuit board...
Q: What exactly is Business Intelligence?
A: Introduction: Business intelligence (BI) is the use of business analytics, data mining, data visuali...
Q: oding theory Explanation of the main goals of coding
A: given - Question: Description/definition of coding theory Explanation of the main goals of coding t...
Q: In a distributed database system, play around with all of the numerous ways users could request data...
A: INTRODUCTION: The phrase "distributed database" refers to a group of databases that are geographical...
Q: Rule 2: Dot Product has special properties Dot products are prevalent in matrix algebra, this implie...
A: Introduction : MAKE A PYTHON CODE WITH 6 matrix multiplication properties. You may create your own ...
Q: dered as a ___________ font. a. cursive
A: given - ``Arial" is considered as a ___________ font.
Handwritten
Solve it this is also present in Chegg u can solve like this
Step by step
Solved in 2 steps with 1 images

- Q1:bulid the circuit using the following boolean algebra expressions D=A+B+C, D=AC'+AB'+BCF= (~A xor ~B) or ~CF= ~A or ~B or ~CF= ((~A or B) and (~A or ~B)) or (C+~A) Use the functions above to create digital circuits.2- Use Boolean Algebra to simplify the following functions.F= (~A+B) (A+B)(C+A)F= ABC+ A(~B+~C)+C(A+B)F=(A+B)(A+C)(B+C)Given the truth table find the maxterm expansion and develop a max term digital circuit that runs the truth table. MAXTERM ONLY
- Design the simplest circuit that has three inputs, a, b, and c, which returns an output value of 1 whenever g and b are complements of each other or b and c are complements of each other, otherwise the output is 0. Realize the circuit using 4input , 3output PALF =A'BC'+A'CD'+ACD+AB'C'D' Draw the Logic Gates diagram please Need Asap(a) Find the output of the circuit corresponding to the input P = 1, Q = 0, and R = 1. (b) Write the Boolean expression corresponding to the circuit.
- Thanks! Here's the actual digital circuit. And the accomplish truth table.Chose the correct answer for the output F of the following circuit ( Assume that A= 101010, B= 100101, C=111101 and D =110100 and the first bit out from the circuit is bit 0)*Find the maxterm expansion of the truth table and develop a digital circuit that works with the given truth table.

