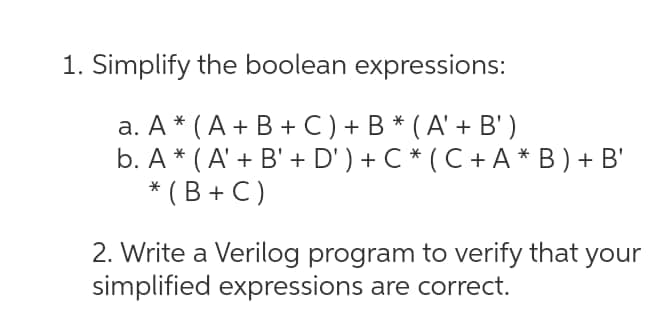
1. Simplify the boolean expressions: а. А * (А+ B +C)+ B* (А'+ В') b. A * ( A' + B' + D' ) + C * ( C + A * B ) + B' * (B + C) 2. Write a Verilog program to verify that simplified expressions are correct. your
Q: Identify at least three of the most recent routing methods. Instead than describing the algorithm,…
A: Most Popular Routing algorithms: Distance-Vector Algorithm. Link-state Algorithm. Hybrid Algorithm.…
Q: Write a complete interactive program that displays the alphabet on the canvas. • Each time the user…
A: ANSWER:-
Q: create a plugin that can retrieve the data from the database via jQuery Ajax function.
A: Find the required method that will retrieve data from the database via jquery Ajax function given as…
Q: -Problem -2 When you execute your program it should ask user to input any number then check if the…
A: Find the required code in python as language not mentioned given as below and output :
Q: In reverse Polish notation what is the value of the touOWing experession? 34+12-4 2/3-+
A: Find the required answer with calculation given as below :
Q: Comprehensive description of DNS, which includes iterated and non-iterated queries, authoritative…
A: Start: It is a client/server protocol that automatically supplies the Internet Protocol (IP) host…
Q: What are the applications of subneting?
A: According to the question the subnet allows to the community to carry out speedy and makes the…
Q: III. The figure below shows synchronous TDM, the data rate for each input connection is 1 Mbps. If 1…
A:
Q: Put another way, what does wavelength division multiplexing do?
A: Wavelength division multiplexing (WDM): Wavelength division multiplexing (WDM) is a technique for…
Q: What may possible trigger a return to the instruction presently being performed in the case of an…
A: It is a collection of instructions that constitutes the programmed that will be run: An expression…
Q: Scripting vs. programming languages: what's the difference?
A: Introduction: All writing languages are also programming languages in their own right, regardless…
Q: b. {a"b"cmdm,n, m 2 0}
A: These are 3 different questions, kindly post them separately. I am doing first one. a,a/aa is push…
Q: What are the many sorts of data structures that are available?
A: Data structures are easy ways of storing and organising data in a computer system so that actions on…
Q: Please describe how a company can prevent hackers from accessing its accounts and defining hacks and…
A: Introduction: Here we are required to explain how a company can prevent hackers from accessing its…
Q: The six components of an information system need to be recognized, enumerated, and defined.
A: Information system (IS): An information system (IS) is a system for organizing, storing, gathering,…
Q: Theft of one's identity is a regular and growing kind of cybercrime. How may identity fraudsters…
A: Answer: Whether an identity cheat hears you perusing out your credit card number on the telephone,…
Q: Is it more economical to use statistical TDM or synchronized TDM?
A: STDM (Synchronous Time-Division Multiplexing): => STDM guarantees that all data is transmitted at…
Q: 9. Which of the following variables is the most mnemonic? a. Variable 173 b. X c. Hours d. Xlq3z9ocd…
A: Your answer is given below.
Q: Why does the company want to network its workers' computers? What are the various network topologies…
A:
Q: What are the applications of subneting?
A: Subnetting - Subnetting is basically doing partitioning of a network into two or more networks. The…
Q: 1. What are the various sorts of crimes for which computers are used?
A: NOTE: As per Bartleby guideline, If there are multiple questions, then we are allowed to solve…
Q: Consider a birth-death process with three states: 0,1, and 2. Given that c1=5 and c2=4, what is TTo?
A: A birth-death Markov chain is a Markov chain in which the state space is the set of nonnegative…
Q: In GNS3, when connecting with an Ethernet cable a Router to a Cloud, should the port be Ethernet or…
A: The first version of Graphical Network Simulator-3 was published in 2008. It enables the use of both…
Q: When it comes to transferability, how may the blockchain work?
A: Given: Blockchain technology is a secure system that enables you to transmit and receive digital…
Q: Write a Python script to make a 5-by-5 zero array 1. Replace the first column by 1s. 2. Replace the…
A: Create a 5x5 array named arr.
Q: In what ways does a database-based strategy have the upper hand?
A: A database management system- (DBMS) is the software that allows users to designate, create,…
Q: Change this MIPS code to RISC-V Assembly using sll. Please add comments. Allow running in RARS.
A: MIPS to RISC-v assembly using Shift Right logical. The shift right logical instructions in RISC-v is…
Q: What sets cybercrime different from other types of crime? Please include any examples you can find…
A: Cybercrime : We recently ruled out cybercrime as a probable cause of the reduction in foreign…
Q: The goal of forensic software is to give particular investigation skills, but how exactly does it…
A: Explanation: Forensic software can automate numerous review operations, in addition to taking disc…
Q: If malicious traffic is transmitted from one VLAN to another, a network intrusion may occur, which…
A: Malicious network traffic results in network intrusion: We can avoid this by safeguarding the…
Q: Which approach of elicitation was utilized to collect the functional requirements for the…
A: Solution is given below :
Q: Big data's two most significant characteristics are speed and diversity. In reality, how do each of…
A: Given: Big InformationBig Data consists of a large amount of data that cannot be managed by…
Q: Using Matlab Find the error/s in the following code, highlight and write the correct code 1.…
A: Matlab == operator is used to check the equality of two values on the left side and right side…
Q: T→T.*F}). Compute GOTO( T →T.*F, *) and GOTO(F→
A: Compute closure({T→T.*F}). Compute GOTO( T →T.*F, *) and GOTO(F→.i,i).
Q: ication serve a specific purpose? What are the advant
A: Below are the advantages and disadvantages of different authentication methods
Q: QUESTION 43 Which of the following statements is correct regarding social engineering attacks? O…
A: Hackers usually do attacks in someone’s account in different ways by phishing. These attacks can be…
Q: The SNMP management primitives and protocol message structure may be explained in what way??
A: introduction : SNMP is a protocol that allows the SNMP administrator (controller) to control the…
Q: MCQS OF SOFTWARE QUALITY ASSURANCE 1.Testing the application as a whole for the modification in any…
A: Note: Since the question is multipart we are advised to do only first three parts. Kindly post other…
Q: Exactly what are the aims of the verification process? Do you know the pros and downsides of…
A: Verification Process: Authentication is the process of ascertaining whether someone or something is…
Q: What are the six stages of computer forensics? Any three of the six stages should be explained.
A: Given: The phases of identification, preservation, collection, examination, analysis, and…
Q: The modulus operator (%) can be used only with integers. O True O False
A: Q10. Modulus operator gives an integer value as output always. Thus the given statement is true.
Q: Determine the present network's advantages and drawbacks.
A: (1) Availability: You are rarely out of contact since wireless technology allows you to communicate…
Q: fgbgfrerfgbngrrg
A: Given: rfgbgfrerfgbngrrg
Q: -Problem -2 When you execute your program it should ask user to input any number then check if the…
A: I give the code in Java along with output and code screenshot
Q: Cybercrime Investigation: How Crucial Is It Today in the Battle Against It?
A: Cybercrime Investigation: A cyber crime investigation is the process of examining, analyzing, and…
Q: Network protection and cybersecurity depend on the use of traffic analysis. Explain why traffic…
A: INTRODUCTION: Network protection helps protect devices from Internet-based events. Network…
Q: What is the significance of documentation in a successful criminal investigation? Make a list of the…
A: Paperwork is essential in criminal investigations since every inquiry is exhaustive, and every item…
Q: Take WPA2 as an example of your chosen wireless access technique. What makes this choice superior…
A: WPA2: WiFi- Protected Access 2 (WPA2) is a WiFi standard. This is a wireless network security…
Q: What precisely is "Big Data"? What differentiates big data from traditional data?
A: Big Data entails: Big data refers to a large amount of data that grows rapidly over time. This…
Q: Do you know what the most current network security measures are? Provide an explanation for each of…
A: Network security : It is highly recommended that every organisation install protection for local…
Step by step
Solved in 2 steps with 2 images

- 1- Write a C++ program to compute cosh z, given that: Assume the user inputs the value of z, and the series terminates at =66, Hint: xy can be found in c++ by pow(x,y).2/ Write a C++ program to read an integer number and a temperature, then apply the rules of temperatures according to the following conditions: o If the integer number is positive and divisible by 4, C=(F-32) +1.8. o Else if the integer number is negative and divisible by 3, F=1.8*C+32. ¢ Else print the temperature is zero.A string is a palindrome if it reads the same from front to back as it does from back to front (e.g. "kayak", "rotator" and "noon" are palindromes). When determining whether an alphanumeric string is a palindrome, we often ignore spaces, punctuation and case in the string (e.g. "A man, a plan, a canal --Panama!" is also considered a palindrome). Write a complete C program to read a string, echo it to the screen, determine whether it is a palindrome, and write a message indicating whether it is or isn't. Your main function should prompt for the string, read the string, print it, call the clean function (to remove all spaces, punctuation, and turn uppercase letters into lowercase letters), print the new string, then call the reverse function (to place the characters into reverse order) and print the new string resulting. In the final step, you will compare the result of the reverse function with the original string and print a message if the string is a palindrome or not. The clean…
- Compute the weakest preconditions of the following statements for the given postconditions. Assume all variables are integers.(a) a = 2*b + 1;b = a*a + 1;{ a > 10 } (b) if (b > 0)a = 4*b - 10;elsea = b + 172;{ a > 0 }Write Boolean expressions that represent the given English expressions. Assume any variables used have been declared and initialized. c++ alpha is greater than 1 at least one of x or y is odd x is 1 or x is equal to y t is strictly between 3.2 and 3.3(USE C++ CODING) Based on the image attached, write the missing statements in the program so that it prompts the user to input two numbers. If one of the numbers is 0, the program should output a message indicating that both numbers must be nonzero. If the first number is greater than the second number, it outputs the first number divided by the second number; if the first number is less than the second number, it outputs the second number divided by the first number; otherwise, it outputs the product of the numbers.
- create a flowchart and a c++ program that will accept two integers. if the integers are equal, print the sum of the the integer, otherwise print the product.write a program to display pythagorean triplets up to 100? use c++ programWrite these statements using ^and, V or, ~not P ↑ Q P ---> Q P <---> Q
- Answer the given question with a proper explanation and step-by-step solution. Write an MIPS program that computes terms of the Fibonacci series, defined as: 1, 1, 2, 3, 5, 8, 13, 21, 34, 55 ... (This is sometimes started with a 0th term: 0, 1, 1, 2, etc.)The first two terms in the series are fixed, and each subsequent term in the series is the sum of the preceding two terms. So, for example, the term 13 is the sum of the terms 5 and 8.Write the program as a counting loop that terminates when the 100th term of the series has been computed. Use a register for the current term and a register for the previous term. Each execution of the loop computes a new current term and then copies the old current term to the previous term register. Count the number of passes to stop after the 100th term. Do not worry about overflow: this will FAR exceed the capacity of a register to hold the value. Stop the program with a syscall with 10 in $v0.Write a single C statement to accomplish each of the following: h) Print the message "This is a C program." with the words separated by tabs.10. Inverted Number-Triangle by Julian Semblante Write a C program that will ask for a positive integer and display the following figure: 1 2 3 4 5 1 2 3 4 1 2 3 1 2 1 Input 1. positive integer value Output 1·2·3·4·5 1·2·3·4 1·2·3 1·2 1

