1. The bad symbol shift dl is computed by the Boyer-Moore algorithm which can be expresse the formula of (b) dl (a) dl max {tl (c) *k,1} (b) dl max (t1(c) + k, 1} max {tl (c)- k, 1} max {t1(c) - k} (d) dl II. Which of the following is not an Algorithm design technique. (a) Brute Force (c) Divide & Conquer (b) Dynamic Programming (d) Hashing III. The Decrease-and-Conquer technique is used in (a) Bubble Sort (c) Insertion Sort (d) Heap (b) String Matching
1. The bad symbol shift dl is computed by the Boyer-Moore algorithm which can be expresse the formula of (b) dl (a) dl max {tl (c) *k,1} (b) dl max (t1(c) + k, 1} max {tl (c)- k, 1} max {t1(c) - k} (d) dl II. Which of the following is not an Algorithm design technique. (a) Brute Force (c) Divide & Conquer (b) Dynamic Programming (d) Hashing III. The Decrease-and-Conquer technique is used in (a) Bubble Sort (c) Insertion Sort (d) Heap (b) String Matching
Principles of Information Systems (MindTap Course List)
13th Edition
ISBN:9781305971776
Author:Ralph Stair, George Reynolds
Publisher:Ralph Stair, George Reynolds
Chapter3: Hardware And Mobile Devices
Section: Chapter Questions
Problem 1WE
Related questions
Question
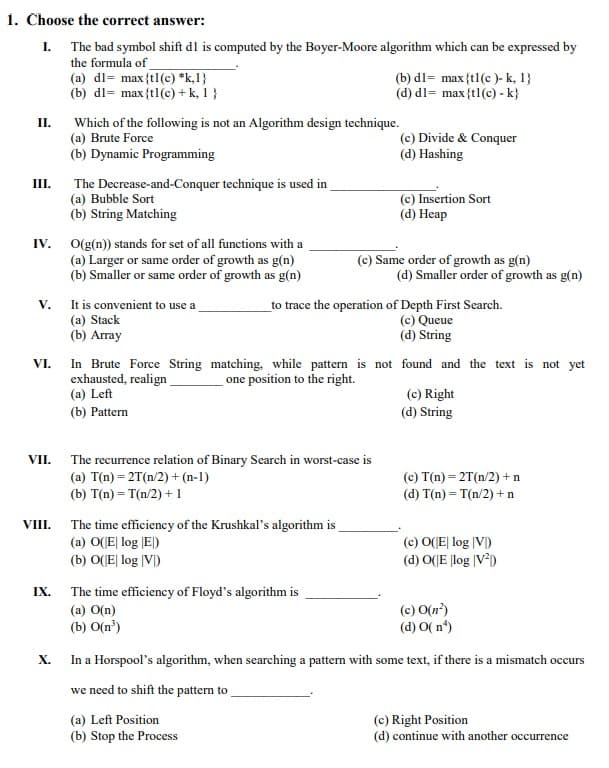
Transcribed Image Text:1. Choose the correct answer:
I. The bad symbol shift dl is computed by the Boyer-Moore algorithm which can be expressed by
the formula of
(a) dl= max {tl (c) *k,1}
(b) dl= max {t1(c)-k, 1}
(b) dl= max {tl (c) + k, 1 }
(d) dl= max {tl (c) - k}
II.
Which of the following is not an Algorithm design technique.
(a) Brute Force
(c) Divide & Conquer
(b) Dynamic Programming
(d) Hashing
III.
The Decrease-and-Conquer technique is used in
(a) Bubble Sort
(b) String Matching
(c) Insertion Sort
(d) Heap
IV.
O(g(n)) stands for set of all functions with a
(a) Larger or same order of growth as g(n)
(b) Smaller or same order of growth as g(n)
(c) Same order of growth as g(n)
(d) Smaller order of growth as g(n)
V.
It is convenient to use a
to trace the operation of Depth First Search.
(a) Stack
(c) Queue
(d) String
(b) Array
VI.
In Brute Force String matching, while pattern is not found and the text is not yet
exhausted, realign
one position to the right.
(a) Left
(c) Right
(d) String
(b) Pattern
VII.
The recurrence relation of Binary Search in worst-case is
(a) T(n) = 2T (n/2) + (n-1)
(c) T(n) = 2T(n/2) + n
(b) T(n) = T(n/2) +1
(d) T(n) = T(n/2) + n
VIII.
The time efficiency of the Krushkal's algorithm is
(a) O(E log E)
(c) O(E| log |V)
(b) O(E| log |V)
(d) O(E log |V²)
IX.
The time efficiency of Floyd's algorithm is
(a) O(n)
(c) O(n²)
(d) O(n)
(b) O(n³)
X.
In a Horspool's algorithm, when searching a pattern with some text, if there is a mismatch occurs
we need to shift the pattern to
(a) Left Position
(c) Right Position
(b) Stop the Process
(d) continue with another occurrence
Expert Solution
This question has been solved!
Explore an expertly crafted, step-by-step solution for a thorough understanding of key concepts.
Step by step
Solved in 3 steps

Knowledge Booster
Learn more about
Need a deep-dive on the concept behind this application? Look no further. Learn more about this topic, computer-science and related others by exploring similar questions and additional content below.Recommended textbooks for you

Principles of Information Systems (MindTap Course…
Computer Science
ISBN:
9781305971776
Author:
Ralph Stair, George Reynolds
Publisher:
Cengage Learning

Principles of Information Systems (MindTap Course…
Computer Science
ISBN:
9781305971776
Author:
Ralph Stair, George Reynolds
Publisher:
Cengage Learning