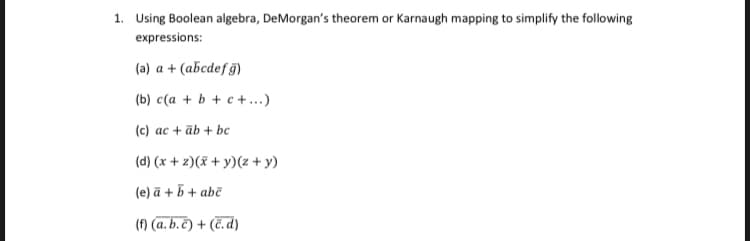
1. Using Boolean algebra, DeMorgan's theorem or Karnaugh mapping to simplify the following expressions: (a) a + (abcdef g) (b) c(a + b + c+...) (c) ac + āb + bc
Q: Isn't it true that different systems place disk folders at different track places on the disk for a ...
A: The answer is
Q: How did the linked-list operations of car and cdr influence linked-list data structures in Lisp/Sche...
A: The atomic S-Expressions or the basic operations on the contra cell Car and cadre are two programmin...
Q: Write a Java program to find the second highest number from an user entered array of integers.
A: Algorithm: for (initialExpression; testExpression; updateExpression){ // body of the loo...
Q: What does it mean to have a privilege?
A: Given To know about the privilege in computer.
Q: What are the four distinct design considerations in a n
A: What are the four distinct design consideration in a multiprocessor operating system? Answer: Multip...
Q: What is the difference between a suffient and necessary statement? Pleae give good examples
A: Step 1 The answer is given in the below step
Q: You can find out how many seconds have elapsed since Jan 1, 1970 using the time() function. #include...
A: Algorithm Steps:- 1. Find the number of seconds since Jan 1, 1970, using the time(NULL) function cal...
Q: PYTHON Suppose you are taking out a bank loan. The bank charges 10% interest each year. How much do...
A: total_amount=principal+simple_interest total_amount=P+Ptr where r=R/100 ...
Q: Indicate the ASCII and EBCDIC code for the following: The letters A, B, C, D, E and the numbers 1, ...
A: Let us see the answer:- ASCII value Number/alphabet ASCII value ...
Q: a) Two-dimensional array of integers named scores with 3 rows and 4 columns was defined by using the...
A: int scores[3][4]={{1,2},3,4,5,6,7}; scores will create 3 rows and 4 columns matrix Answer for a...
Q: Flow control is one of the main building blocks that determines how a program should run. Ghana Coco...
A: Controlling the flow of information (data): Flow management is the activity of controlling the pace ...
Q: Do you have any recommendations for data flow recording methods?
A: According to the information given we have to recommend data flow recording method.
Q: What exactly does "open architectural design" imply?
A: the anwser is given below:-
Q: A Wireshark trace of TCP traffic between hosts A and B indicated the following segments. Host A sent...
A: Surely correct option will be 7 second.
Q: A hospital is looking for a solution to connect multiple, newly established remote branch medical of...
A: Answers Private WAN or Wide area network is a network technology consisting of two or more networ...
Q: SRAM is typically used for on-chip memory because: SRAM is faster than DRAM. SRAM uses fewer transis...
A: SRAM is faster than DRAM.
Q: To declare a variable, 'Type' is insufficient. To put it another way, all variables contain data typ...
A: Storage as variable or function's class label is used to describe its properties. Some of these prop...
Q: What does it mean to have a privilege?
A: Given To know about the it mean to have a privillege
Q: The input to the function/method consists of two arguments - rideDuration, an integer representing t...
A: Program to pick the two song whos combine run time is 30 second
Q: Suppose N = 4 and D = 3. Start with the least-squares objective function, as show nd derive the grad...
A: The Objective FunctionIndeed, you in all actuality do involve polynomial math in reality. Science, s...
Q: Q1) Four function calculator ( addition, subtraction, multiplication, division) of a single expressi...
A: Q1) Four function calculator ( addition, subtraction, multiplication, division) of a single expressi...
Q: Provide a summary of the security services.
A: the answer is given below:-
Q: In computer architecture which different modes are defined such that in a given instruction set arch...
A: Generate the structure of the help: The new abilities structure (ISA), often known as a computer sys...
Q: You are working as a security adviser on a project that tries to upgrade a legacy network. During a ...
A: 1. Switch vs hub : A switch establishes a connection point for all the devices in the network. It is...
Q: Explaination A Wireshark trace of TCP traffic between hosts A and B indicated the following segm...
A: Answer: I have given answered in the handwritten format in brief explanation.
Q: Using opt-out links is the safest and most reliable way to reduce the amount of spam you get. Is thi...
A: Using opt-out links is the safest and most reliable way to reduce the amount of spam you get. Is thi...
Q: What trade-offs do you have to make when building enormously scattered data environments?
A: A trade-off is characterized in economics as a "opportunity cost." For instance, you may take a day ...
Q: Convert each of the following decimal numbers to excess-5code: a- (76)10 (67)1o then add the two num...
A: “Since you have asked multiple questions, we will solve the first question for you. If you want any ...
Q: Why do interrupt-driven operating systems outperform non-interrupted operating systems in terms of p...
A: Interrupts enable devices to tell the CPU when data needs to be sent or when an operation is complet...
Q: Consider the below commands i) sed "s/CSH/csh/g" temp >|Is ~/newtemp 11) Is -v grep wc -1 111) Is -a...
A: Some operating systems used need commands to execute the functions unlike the operating system used ...
Q: PHP program to create Login and Logout using sessions.
A: The Answer is in below Steps
Q: What is a deadlock, and what causes it?
A: The solution to the given problem is below.
Q: cloud is secured using the shared responsibility paradigm and identity access management (IAM).
A: here in this question we will discuss about shared shared responsibility paradigm and access managem...
Q: What are the four key security flaws in purchasing and merchandising systems? Examine the causes and...
A: Introduction: Security breaches occur when an attacker or intruder gets unauthorized access to an or...
Q: Suppose you want to achieve a speed-up of 90 times faster with 100processors. What percentage of the...
A: Parallel processing is a method in CPU in which two tasks are executed simultaneously at same instan...
Q: The transport layer of HTTP, SMTP, and POP3 uses TCP rather than UDP as the underlying protocol.
A: TCP is used instead of UDP for HTTP, SMTP, and POP3 because: 1) Dealing with a large quantity of cus...
Q: Imple guessing game (simi letter and then attempts to guess the word. man or Hangaroo). guesses Crea...
A: Big question mark: The above script is just an interactive mind game where the user must predict a v...
Q: Explain the difference between an application programming interface (API) and an application binary ...
A: Introduction: Binary software modules communicate through an application binary interface (ABI). In...
Q: (v) In JAVA, define a method that takes three integers as the parameters and returns the smallest nu...
A: In JAVA, define a method that takes three integers as the parameters and returns the smallest number...
Q: Q3: Cool Chemicals In an alternate reality, chemistry Professors Hodge and Sibia have teamed up to d...
A: Coded using Python 3.
Q: Translate from hexadecimal to RISC-V.
A: vscale/src/test/inputs have several hex inputs with similar format: 32 hex chars per line (16 bytes,...
Q: Discuss how the following pairs of scheduling criteria conflict in certain settings. I/O device util...
A: Step 1 The answer is given in the below step
Q: Over the last three years, a security breach of personal information has resulted in some identity t...
A: The term 'security breach' refers to illegal activity and access to computer data , application , de...
Q: automate data collecti
A: given - Tell us about the software you used to automate data collection.
Q: Write a Matlab function named reflect_polynomial that will: [a] accept a univariate polynomial defin...
A: The objective is to write MATLAB code for the given data.
Q: Now consider the same search graph with heuristic values given in brackets along the name nodes: STA...
A: The least complex of these calculations, unadulterated extends hubs arranged by their heuristic qual...
Q: It's important to compare and contrast the uniprocessor and multiprocessor systems. Computers come ...
A: the answer is given below:-
Q: Q2/ A- Convert each of the following decimal numbers to excess-5code: a- (76)10 (67)10 then add the ...
A: The problem statement is all about performing binary multiplication addition subtraction and divisio...
Q: What is an expert system, and how might a data warehouse help you build one?
A: Lets see the solution.
Q: In Java Determine the output of the following code. Place a box around your answer. int i = 30, j...
A: Output for the above java code
Step by step
Solved in 2 steps with 1 images

- Boolean Algebra Simplify the following functions to a minimum number of literals. Show step-by-step simplification and indicate the theorem/postulate used in each step. Draw the logic diagram of each of the simplified functions. (A’ + C)(A’ + C’)(A + B + C’D)9. Show that De Morgan's Law applies to Boolean algebra, by showing that for all x and y, (x ⋁ y)’ =x’ ⋀ y’ dan (x ⋀ y)’ = x’ ⋁ y’Boolean Algebra Simplify the following functions to a minimum number of literals. Show step-by-step simplification and indicate the theorem/postulate used in each step. Draw the logic diagram of each of the simplified functions. A’C’ + ABC + AC’
- Boolean algebra Simplify the following functions to a minimum number of literals. Show step-by-step simplification and indicate the theorem/postulate used in each step. Draw the logic diagram of each of the simplified functions. A’B (D’ + C’D) + B(A + A’CD)Simplify the Boolean function F(w,x,y,z) = (0,1,2,4,5,6,8,9,12,13,14)Simplify the expression using Boolean algebra theorem and postulates: F=(X+Z')(Z+WY)'+(VZ+WX')(Y+Z)'.
- Simplify the below expressions a) By using Boolean algebra b) By using Karnaugh maps. i) z=xy+xy' ii) z= x+xyBoolean Algebra Simplify the following functions to a minimum number of literals. Show step-by-step simplification and indicate the theorem/postulate used in each step. Draw the logic diagram of each of the simplified functions. ABC’D + A’BD + ABCDConsider the Boolean expression u = wx + yz + wx'z'+w'y (a) Draw the Karnaugh map for u. (b) Use the map in part (a) to obtain the Karnaugh map for u'. (c) Express u' as a minimal sum of products. (d) Hence design a simple logic network for u'.

