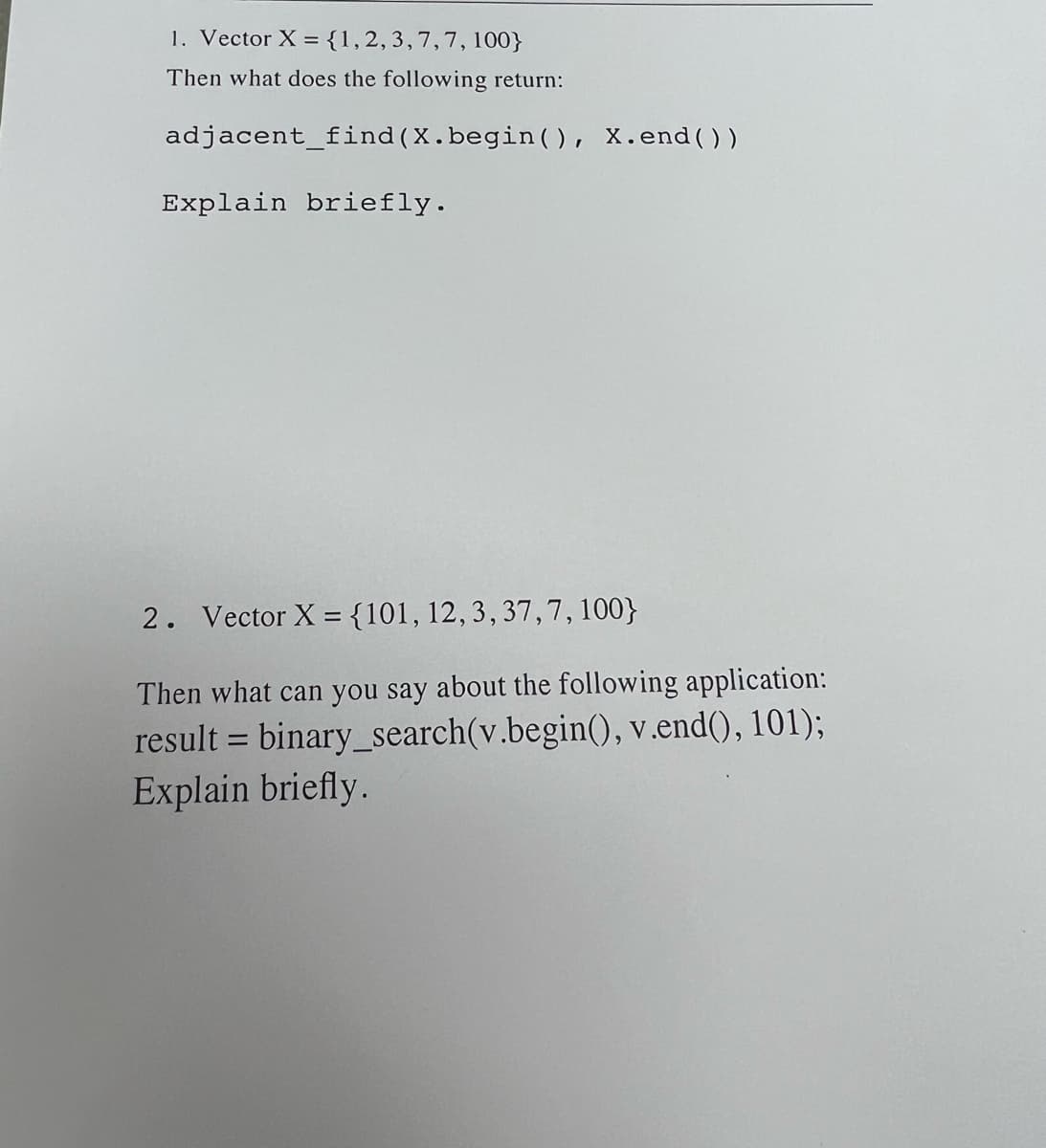
1. Vector X = {1, 2, 3, 7, 7, 100} Then what does the following return: adjacent_find (X.begin(), X.end()) Explain briefly. 2. Vector X = {101, 12, 3, 37, 7, 100} Then what can you say about the following application: result = binary_search(v.begin(), v.end(), 101); Explain briefly.
Q: System and network risk classifications? Real-life dangers?
A: Risk classification is an essential aspect of cybersecurity that involves categorizing potential…
Q: What is software engineering and what are its three components?
A: The software development procedure is a systematic approach to create software so as to involve…
Q: Compilers and assemblers generate object code from source files. Linking object files allows them to…
A: When a compiler produces an executable without linking, it means that it generates an object file…
Q: How do password managers save encrypted passwords? Local, web-based, cloned, or USB-based?
A: Given, How do password managers save encrypted passwords? Local, web-based, cloned, or USB-based?
Q: multiprogramming
A: What exactly is the meaning of the term "multiprogramming"?
Q: The Problem: strcat is unsafe The following code overflows the array name and corrupts memory. //…
A: The C code is given below with output screenshot
Q: homogeneous and heterogeneous distributed databases and their main problems in real-world…
A: Explain homogeneous and heterogeneous distributed databases and their main problems in real-world…
Q: TPS development with Android Studio. The SQLite DB browser shows my records but not my list view…
A: Transactional Processing System (TPS) is a computer system that manages organizational transactions.…
Q: Create a program using java data structures That has the user enter their pay rate; the program…
A: The Java program below prompts the user for their pay rate and number of hours worked on two…
Q: Investigate the many ways information systems are put to use in different industries.
A: Hello student Greetings Information systems (IS) refer to a set of interconnected components that…
Q: As more and more computers are connected to the internet, the need of keeping networks secure is…
A: Net safety ensures the secrecy, integrity, and readiness of computer nets and their associated…
Q: What makes OOP distinct from other programming paradigms?
A: Object-oriented programming (OOP) is a programming paradigm that is widely used today. It is a style…
Q: Why cyber kill chain?
A: Cyber kill chain The concept of the cyber kill chain is based on the kill chain model used…
Q: The Problem: strcat is unsafe The following code overflows the array name and corrupts memory. //…
A: A buffer overflow is a type of software vulnerability that occurs when a program tries to write data…
Q: Why would an IT business use separate installation techniques for different operating systems,…
A: An IT company could utilize distinct installation methods for various operating systems, hardware…
Q: Experts suggest adding RAM to slow computers. Increasing RAM may delay the system. Is this true?…
A: The role of RAM in computer performance is often debated, with some suggesting that increasing RAM…
Q: Explain why a software does not need to be flawless to be done. accessible to customers
A: Software development involves a complex process and success can be difficult. Sometimes, time and…
Q: Identify the risk associated with each authentication method and offer a remedy. Bob compares a…
A: When Bob matches a hashed password to a record containing hashes, there are several risks associated…
Q: Describe how a malfunctioning system might compromise network security and how to avoid it.
A: A malfunctioning system can compromise network security in several ways, making it vulnerable to…
Q: Computer Science A left-child, right-sibling tree T with n nodes holds a score, a real integer >0,…
A: In this question we have to write a C++ code for the method to solve on the max sum for nodes with…
Q: Word's table creation tools help visualize data. Are you wondering about Word's on-the-fly table…
A: "Word's on-the-fly table creation" refers to a function of Word that allows users to quickly and…
Q: My efforts to get the book's access code have so far failed. Can you help me find it on my Yuzu…
A: Yuzu is a digital inspecting and note-captivating platform that keeps users access to a vast library…
Q: Why do different operating systems put disc directories on separate hard drive tracks? Which places…
A: Operating systems place disk directories on separate challenging drive tracks for a few reasons.…
Q: Broadly speaking, the assignment requires you to produce a 3000-word report that provides a critical…
A: To complete this assignment, you should begin by reviewing the case study and identifying the…
Q: What is the information system's structure, management, and technology?
A: Hello student Greetings Information systems (IS) have become an integral part of modern businesses…
Q: What is the precise meaning of the term "virtual desktop," and how is it used in practise?
A: What is virtual: In computing, virtual refers to a technology that allows multiple operating systems…
Q: Hello, Time and Space Complexity for the Metropolis Algorithm in Monte Carlo (Subject:Algorithm…
A: The Metropolis algorithm is a popular Monte Carlo method used for sampling from complex probability…
Q: What kinds of challenges do businesses face while making the transition to an infrastructure that is…
A: Small business often encounter various challenges when transitioning to a cloud-based organization,…
Q: What sets User Datagram Protocol (UDP) different from Transmission Control Protocol (TCP)?
A: The User Datagram Protocol (UDP) and Transmission Control Protocol (TCP) are the two primary…
Q: What are the implications of using different computer algorithms?
A: Computer algorithms are a crucial component of modern technology, powering everything from search…
Q: Who was the pioneer in the development of the first computer monitor?
A: We have to explain who was the pioneer in the development of the first computer monitor?
Q: Explain the pros and cons of each Linux installation option.
A: Linux has several installation options, each with its own set of benefits and drawbacks. The best…
Q: Where did the concept of a "fat binary" come from in the first place, and what was its intended use?
A: Early Apple Macintosh computers introduced the idea of a "fat binary" or "universal binary," notably…
Q: The amount of space used up on the hard disc by statically linked programmes is much more than that…
A: Your answer is given below.
Q: We upgrade our local area network by connecting to the web. Which TCP/IP protocol suite levels…
A: foreword to TCP/IP Protocol Suite Levels : The TCP/IP protocol set is also known as a compilation of…
Q: Fractals from the Lorenz Equations Determine the fractal that arises from using Newton's method to…
A: Given, Determine the fractal that arises from using Newton's method to compute the fixed-point…
Q: Explain why it would be beneficial to get corporate needs within the context of business performance…
A: One of the main reasons it is beneficial to get corporate needs within business performance…
Q: Internet influence on system architecture?
A: The internet has changed the way we interact with technology and has had a huge impact on design.…
Q: Why do some Linux distributions promote sudo but allow root access? Which has benefits and…
A: Sudo is a command letting users to perform executive tasks with momentarily elevated rights. In…
Q: During the process of configuring and installing Linux, please explain all of the choices that are…
A: Linux: It is an open source and free operating system which allows with knowledge of…
Q: There are three types of relationships in a database: identifying, non-identifying, and generic.
A: Relationships between tables are used in database design to create links between the data.…
Q: Name four external disc interfaces.
A: External disk interfaces: External disk interfaces are technologies that allow external hard drives…
Q: Discuss the three most important database innovations.
A: In today's digital age, data is the lifeblood of many businesses and organizations. Managing and…
Q: Make a Java user interface for a simple calculator that can multiply and divide. Switches for…
A: Given, Make a Java user interface for a simple calculator that can multiply and divide. Switches…
Q: Compare stack alterations when confined and unbounded.
A: Stack: A stack is a data structure that stores data in a linear and sequential fashion. It follows…
Q: What are the three steps that need to be completed before a piece of software may utilize a certain…
A: It is typical to run into files that need to be opened, read and processed when dealing with…
Q: How responsible are organizations for security breach contingency plans?
A: Security breach contingency plans are vital for organizations in today's digital age. As…
Q: Does it matter what composite attributes you use to determine whether you may use composite keys?
A: A composite key is a key that consists of two or more attributes that together uniquely identify an…
Q: go about gaining access to a file system? What precisely differentiates these two possibilities from…
A: How exactly does one go about gaining access to a file system? What precisely differentiates these…
Q: Explain one technological subject you know.
A: One technological subject that I know is Artificial Intelligence (AI). AI is a branch of computer…
Trending now
This is a popular solution!
Step by step
Solved in 3 steps

- Suppose that two arraysx1,x2,…,xnandy1,y2,…,yn.( Need only handwritten solution please otherwise downvote).Write code for determining the index of a value in an OrderedVector. Be aware that if the value is not in the Vector, the routine returns the ideal location to insert the value. This may be a location that is outside the Vector(use java)#include <iostream> #include <fstream> using namespace std; struct Triple { int value, row, col; }; ostream& operator<<(ostream& os, Triple& t) { os << "(" << t.row << ", " << t.col << ", " << t.value << ")" <<endl; return os; } class Matrix; // forward declaration class MatrixNode { friend class Matrix; friend istream& operator>>(istream&, Matrix&); // for reading in a matrix friend ostream& operator<<(ostream&, Matrix&); private: MatrixNode *down, *right; bool head; union { // anonymous union MatrixNode *next; Triple triple; }; MatrixNode(bool, Triple*); // constructor }; MatrixNode::MatrixNode(bool b, Triple* t) { head = b; if (b) {right = next = this;} // row/column head node else triple = *t; // head node for list of headnodes OR element node } typedef MatrixNode* MatrixNodePtr; class Matrix { Matrix operator+ (const Matrix & b) const; Matrix operator*(const…
- Implement binary search algorithm as a template function.Part B: Given a vector of size S and a number N. Write a function that calculates if there is any pair of numbers in the vector whose sum is equal to N?Hint: you can use the binary search function you implemented in part A.Notes:You must use iterators in your implementation.Input Format: The input consists of 2 lines. The first line contains 2 numbers, S and N. The second line contains S numbers which represent the contents of the vector.Implement the following function without using any additional data structure, and without sorting the input vectors. /* Given two vectors of integers, check if the two vectors contain same set of values: e.g., V1=[3,4,10,4,10,11] and V2=[3,3,4, 11, 10] stores same set int: {3, 4, 10, 11}. Note that duplicates are removed when considering set */ @param list1, list2: two vectors of integers@pre: list1, list2 have been initialized@post: return true if list1 and list2 stores same values (in same or different order); return false, if not. */ bool SameSet (const vector<int> & list1, const vector<int> & list2) {//for each value in list1, check if it appears in list2, if not, return false //for each value in list2, check if the value appears in list1, if not return false //return true}Integer dataSize is read from input. Then, strings and integers are read and stored into string vector subjectList and integer vector pageList, respectively. Lastly, integer pageThreshold is read from input. Set matchCount with the number of element pairs with a page greater than or equal to pageThreshold. Output the subject of each pair found with a page greater than or equal to pageThreshold. End with a newline. Ex: If the input is: 3 Environment 416 Cooking 353 Science 306 349 Then the output is: Environment Cooking Total: 2 By using the following code: #include #include using namespace std; int main() { int numElements; int pageThreshold; int matchCount; unsigned int i; cin >> numElements; vector subjectList(numElements); vector pageList(numElements); for (i = 0; i < subjectList.size(); ++i) { cin >> subjectList.at(i); cin >> pageList.at(i); } cin >> pageThreshold; /* Your code goes here */ cout << "Total: " << matchCount;…
- Program this in java the state and variable display must be:Unsorted Partition Reference Index: 0, Traversing Index: 7, Current Traversing Index Value: mango, Next Index Value: plum, Swapping Condition: FalseCurrent Array: ['apple', 'avocado', 'orange', 'banana', 'strawberry', 'pineapple', 'plum', 'mango'] The input:["apple", "avocado", "orange", "banana", "strawberry", "pineapple", "plum", "mango"]Note:The sorted partition is on the left side. Then, the order is increasing based on the number of vowels of a string.the output must be like this:['plum', 'apple', 'strawberry', 'mango', 'orange', 'banana', 'avocado', 'pineapple']Which is a proper way to free the following dynamic array? double *sales = new double[ count ]; A. delete sales[ ]; B. delete sales[ count ]; C. delete sales; D. delete [ ] sales;What is the correct way to assign the pointer p to the address of x?. Single choice. p = %x; p = &x; &p = *x; *p = &x;
- You are going to implement hashing with chaining with separate chaining. Please implement your hash function accordingly to distribute the data evenly in the array. Fill in the missing code! C only! ASAP!!! THE CODE: #include <stdio.h> // RecordTypestruct RecordType{int id;char name;int order;}; // Fill out this structurestruct HashType{ }; // Compute the hash functionint hash(int x){ } // parses input file to an integer arrayint parseData(char* inputFileName, struct RecordType** ppData){FILE* inFile = fopen(inputFileName, "r");int dataSz = 0;int i, n;char c;struct RecordType *pRecord;*ppData = NULL; if (inFile){fscanf(inFile, "%d\n", &dataSz);*ppData = (struct RecordType*) malloc(sizeof(struct RecordType) * dataSz);// Implement parse data blockif (*ppData == NULL){printf("Cannot allocate memory\n");exit(-1);}for (i = 0; i < dataSz; ++i){pRecord = *ppData + i;fscanf(inFile, "%d ", &n);pRecord->id = n;fscanf(inFile, "%c ", &c);pRecord->name =…Computer Science Done in Perl. Someone gave me a wrong/incomplete answer. Write a function, hashsum, which takes a hash reference as its first argument and an array reference as its second argument. The function should take the elements of the array and use them as keys in the hash. The values in the hash corresponding to the keys in the array should be totaled, and the sum should be returned to the user. If a key passed in the array does not exist in the hash, ignore it. Write a sample program to call this function.6) While there is a built-in pop_back() method for vectors, there is no built-in pop_front method. Suppose a program needs a pop_front() method that will remove the first element from the vector. For example if the original vector is [1, 2, 3, 4, 5], then after passing in this vector to pop_front() the new resulting vector will be [2, 3, 4, 5]. Which of the options below is the correct implementation of pop_front()? Group of answer choices D-) void pop_front(vector<int> &v){ for(int i=0; i<(v.size()-1); i++)v[i+1] = v[i]; v.pop_back(); } C-) void pop_front(vector<int> &v){ for(int i=0; i<(v.size()-1); i++)v[i] = v[i+1]; v.pop_back(); } B-) void pop_front(vector<int> &v){ for(int i=0; i<v.size(); i++)v[i+1] = v[i]; v.pop_back(); } A-) void pop_front(vector<int> &v){ for(int i=0; i<v.size(); i++)v[i] = v[i+1]; v.pop_back(); } 7) Suppose a program has the following vector: [99, 23, 55, 71, 87, 64, 35, 42] The goal is to…

