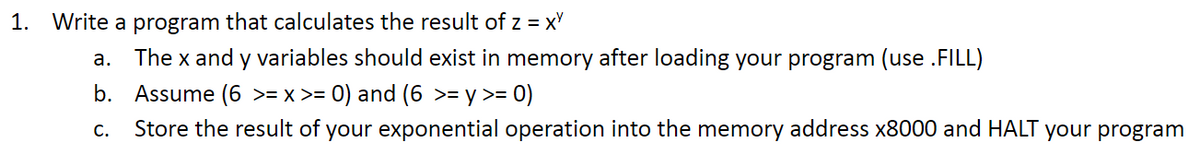
1. Write a program that calculates the result of z = xy a. The x and y variables should exist in memory after loading your program (use .FILL) b. Assume (6 >= x >= 0) and (6 >= y >= 0) C. Store the result of your exponential operation into the memory address x8000 and HALT your program
Q: Create a CRUD matrix to check the consistency between your domain model class diagram (create it)…
A: To check the consistency between the domain model class diagram and the list of use cases provided,…
Q: Which Qualys sensors collect the type of data needed to perform vulnerability assessments? Select…
A: Vulnerability assessments are crucial for maintaining the security of systems and networks. They…
Q: List and briefly describe the TLB error response of a computer or operating system. Poor performance…
A: TLB (Translation Lookaside Buffer) is a hardware component used in modern computer processors to…
Q: Create the truth table for F2 without simplifying the expression F₂ = ABC + ACD + ABC
A: A truth table is a table used in logic to display all the possible combinations of truth values…
Q: Create an automobile class that will be used by a dealership as a vehicle inventory program. The…
A: Java is a high-level, general-purpose programming language that is widely used for developing a…
Q: } public String getPassword() { return password; } public void setUserName(String userName) {…
A: Dear Student,Our goal here is to output the customer's password. To achieve this, the cust object…
Q: Write a program that initializes a blank array and allows the user to input their own numbers (0 to…
A: Initialize a blank array of size n (5 <= n <= 20) to store user inputs.Create a loop that will…
Q: Describe the evolution of the Internet as well as the technological infrastructure underlying its…
A: The evolution of the Internet has been a remarkable journey, transforming from a small-scale…
Q: The case when A and B are connected by a many-to-one connection R (Figure 1). Match R up with A's…
A: In Database system, a many-to-one friendship (also recognized as a "many-to-one Association") is an…
Q: 3. Write a non-deterministic algorithm to perform sorting of all the rows of a matrix into ascending…
A: A non-deterministic algorithm is an algorithm that may…
Q: Using the Online SQL Editor, answer the following question with screenshots. Link:…
A: To create a new table named "Production" with the specified columns and constraints, you can use the…
Q: This is the error I am getting could I get an explanation on why this is please and how to fix it
A: From the given expected output in green, we are expected to display message only if it is the first…
Q: Determine the distance between point (x1, y1) and point (x2, y2), and assign the result to…
A: Declare variables: x1, y1, x2, y2, xDist, yDist, pointsDistance as doublesInitialize xDist, yDist,…
Q: point alg ti+1 approx the following must hold for the algorithm to converge quadratically? Select…
A: solution for the problem is in next step
Q: can you please fic the error I am getting in the LC3 simulator: Oh no! You've got an error in your…
A: The issue here is that you're trying to use the label 'PROMPT' as an offset, but the LEA instruction…
Q: Please explain how and why database architecture is so crucial in an educational setting.
A: The magnitude of database building in educational backgrounds cannot be overstated. Properly…
Q: Object-oriented design must be utilised wherever it makes sense to do so. When the situation calls…
A: When it comes to software design, both object-oriented design and structured design have their…
Q: Why does replacing old systems with new ones necessitate such a substantial financial investment and…
A: What is system:A system refers to a set of interconnected components or elements working together to…
Q: Now, then, what exactly is digital audio? a break down of how analogue audio is converted to digital…
A: In this question we need to explain the concept of digital audio and break down of how the analogue…
Q: the largest linkedlist in terms of the number of nodes it contains is unknown. Is there one that you…
A: As you mentioned, the size of the largest linked list in terms of the number of nodes it contains is…
Q: Define the following propositions: • s: a person is a senior • y: a person is at least 17 years of…
A: Logical expressions are statements or propositions expressed using logical operators to convey…
Q: I'd be very grateful if you could provide TWO potential ways out of any data security issues.
A: Data defense is a critical concern in computer science and information technology. As our reliance…
Q: Good afternoon, Assistance with this Discrete Math question would be greatly appriciated. Thank…
A: The problem of finding the maximum value in a list of numbers is directly related to discrete…
Q: Now, then, what exactly is digital audio? a break down of how analogue audio is converted to digital
A: What is analogue audio: Analog audio refers to sound that is represented by continuous waveforms. It…
Q: Match each API-related term below with its description. API Mediation API Portal API Portfolio API…
A: This question is related to Application Programming Interfaces (APIs) and their associated terms. An…
Q: array of integers, find the maximum sum of any contiguous subarray. Example: Input: [-2, 1, -3, 4,…
A: The given code implements the max_subarray_sum function that takes in an array of integers and…
Q: How does data mining affect privacy and safety?
A: Data mining, the practice of drawing patterns and insights from huge databases, is becoming more and…
Q: define fast ios_base::sync_with_stdio(false);cin.tie(NULL);cout.tie(NULL); using namespace std;…
A: I have rewrite the code below:The provided code is written in C++ and aims to convert an integer…
Q: What are some of the most efficient methods for regulating your firewall? Explain.
A: One of every system's most important aspects robust network security infrastructure. Its role is to…
Q: Write a program in C++ using a heap sort and test it with the following data. You need to give the…
A: Step1 : We have created a heapify function that passed the arguments array and size of arrayStep2:…
Q: What is Amazon's enterprise system for its cloud computing platform?
A: Amazon's enterprise system for its cloud computing platform is known as Amazon Web Services (AWS).…
Q: Describe the cycle of fetch-decode-execute. Explain the activity of each register.
A: The fetch-decode-execute cycle, or the instruction cycle, is how a computer retrieves a program…
Q: Design focuses on the logical design of system files and databases Oturning design specifications…
A: Design is a crucial aspect of the software development process, encompassing the creation of visual…
Q: What are the requirements for determining if a linked list T is empty if T is one of the following:…
A: The requirements for determining if a linked list T is empty depend on the type of linked list. Here…
Q: Simplification of context-free grammars Eliminate all l-productions from S -> ABCd A -> BC B ->bB…
A: Given:S -> ABCdA -> BCB ->bB | λC -> λRemoving C -> λ //place λ where ever C is…
Q: . Answer must
A: The code provided contains two functions: int_to_base and base_to_int, which perform integer base…
Q: To what ends does a firewall primarily serve? At the moment, I'm developing a packet filtering…
A: a firewall primarily serves to control network traffic, enforce security policies, and protect…
Q: Most of an organization's operations are performed by servers on a flat network, making network…
A: A flat network style is one where all technology are strapped to the same network segment. This…
Q: Firewalls' major purpose? Writing packet-filtering software. Where are the rules?
A: The primary purpose of a firewall in a network is to control by examining the data Packets and…
Q: How challenging was it to install a system that all employees of the company could use? Please…
A: Installing a system that all employees can use effectively within a company is complex and…
Q: Q14: Ayşe attaches his laptop to campus network with wired connection, opens his browser and…
A: In today's digital age, accessing web pages and online content has become an integral part of our…
Q: When compared, the Internet and the World Wide Web (WWW) have some fundamental differences. What are…
A: 1) The Internet and the World Wide Web (WWW) are two fundamental components of the modern digital…
Q: What is the precise meaning of the term "invisible web," and how large is one on average?
A: Invisible web is also known as deep web which is the place where the websites are not indexed by the…
Q: what is a Nested selection in Programming and how it is used specifically in Python. Provide an…
A: A nested selection, often referred to as nested conditionals or nested if statements in the…
Q: RAID live backups may limit hard disc storage. Are backups worth half your disc space? What RAID…
A: RAID (Redundant Array of Independent Disks) configuration plays an important role in protecting data…
Q: Within the Management Studio, you can build a SQL statement without having to write your own code by…
A: A computer language called SQL (Structured Query Language) is used to manage and work with…
Q: D
A: Setting up a big grid computing project such as the Large Hadron Collider (LHC) is a complex…
Q: Write a program REMOVE_DUPLICATES that will remove duplicate elements in a list L that occur…
A: Initialize an empty list called result.Initialize a variable prev to None.Iterate over each element…
Q: Data storage and visualisation. Explain how each Business Intelligence component would be utilised…
A: What is Business Intelligence component: Business Intelligence (BI) components are the various…
Q: Describe how advances in Very Large Scale Integration (VLSI) technology have improved the efficacy…
A: The development of a technology known as Very Large Scale Integration, or VLSI, has considerably…
please meet the following requiremtents using the LC3 simulator
Trending now
This is a popular solution!
Step by step
Solved in 3 steps

- In each of the following cases, write a short program in Vole to perform the requestedactivities. Assume that each of your programs is placed in memory starting at address 0x00.a. Move the value at memory location 0xD8 to memory location 0xB3.b. Interchange the values stored at memory locations 0xD8 and 0xB3.c. If the value stored in memory location 0x44 is 0x00, then place the value 0x01 in memorylocation 0x46; otherwise, put the value 0xFF in memory location 0x46(Practice) a. Using Figure 2.14 and assuming the variable name rate is assigned to the byte at memory address 159, determine the addresses corresponding to each variable declared in the following statements. Also, fill in the correct number of bytes with the initialization data included in the declaration statements. (Use letters for the characters, not the computer codes that would actually be stored.) floatrate; charch1=M,ch2=E,ch3=L,ch4=T; doubletaxes; intnum,count=0; b. Repeat Exercise 9a, but substitute the actual byte patterns that a computer using the ASCII code would use to store characters in the variables ch1, ch2, ch3, and ch4. (Hint: Use Appendix B.)a- Write a program which adds the values D8H, F5H and E9H. Put the sum in file register 15H for (low byte) and file register 16H for high byte. b- What is the content of (low byte) and (high byte) registers in Hex?
- Write an assembly program to set R0=1 if there's a 5 in one of ten memory locations, starting at x3100. At the beginning of the program, set R0 = 0. If no 5 is found, it should leave R0 set to 0. Please submit your assembly program below. I will run it with my data. If a 5 is found, output the following message to the console. "A 5 was found at x31xx." 31xx is the hex address of the 5. Here is the test data I used to generate the screen print below. It is not the test data I will use to grade your project. .ORIG x3100.FILL #10.FILL #20.FILL #30.FILL #40.FILL #50.FILL #5.FILL #70.FILL #5.FILL #90.FILL #100.ENDP1:Given the following memory values and a one-address machine with an accumulator,whatvalues do the following instructions load into the accumulator?·Word 20 contains 40.·Word 30 contains 50.·Word 40 contains 60.·Word 50 contains 70.a. LOAD IMMEDIATE 20b. LOAD DIRECT 20c. LOAD INDIRECT 20d. LOAD IMMEDIATE 30e. LOAD DIRECT 30f. LOADINDIRECT 30If the memory location at address 5 currently stores the value 8, what is the functional difference between writing the value 5 into cell number 6 and copying the contents of cell 5 into cell 6?
- Q2: Write program based on the following sequence of conditions: . Overwrite memory location $2800 with a value of $12345678 By using indirect addressing, copy a byte value in memory location $2000 into D3 by using address register A3. Increase value in D3 by $10.Write an assembly program to set R0=1 if there's a 5 in one of ten memory locations, starting at x3100. At the beginning of the program, set R0 = 0. If no 5 is found, it should leave R0 set to 0. Please submit your assembly program below. I will run it with my data. If a 5 is found, output the following message to the console. "A 5 was found at x31xx." 31xx is the hex address of the 5.Write a program to find the average of 32 bytes started at memory location [Mem 1]. If the average is greater than 42H then store the average at memory location [Mem 2] otherwise, store it at memory location [Mem 3].(microprocessor)
- Modify the following program in lc-3 to get the input(numbers) from the keyboard and print the result to console. .ORIG x3000Loop LD R0, number1 ; load number1 into R0LDR R1, number2 ; load number2 into R1ST R2, SaveR2 ; save register R2LD R5, goSUB ; load address of SUB into R4JSRR R5 ; go to subroutine whose address in R5STR R3, result ; store resultLD R2, SaveR2 ; restore old value R2HALTnumber1 .FILL #10number2 .FILL # -8goSUB .FILL SUB ; initialize goSUB to address of SUBSaveR2 .BLKW #1; reserve space SaveR2 and SaveR3result .BLKW #1SUB NOT R1, R1ADD R2, R1, #1ADD R3, R0, R2RET.ENDWrite programs that will accomplish the desired tasks listed below, using as few lines of code as possible e) Divide the data in RAM location 3EH by the number 12H ; put the quotient in R4 and the remainderin R5.f) Divide the data in RAM location 15H by the data in RAM location 16H ; put the quotient inexternal RAM location 7CH and the remainder in in external RAM location 7DH.g) Double the number in register R2, and put the result in register R3 (high byte) and R4 (low byte).Use logic operations.h) OR the contents of ports 1 and 2 ; put the result in external RAM location 0100Hi) Set Port 0, bits 1, 3, 5 and 7 to one, set the rest to zero.j) Clear bit 3 of RAM location 22H without affecting any other bit.k) Invert the data on the port 0 pins and write the data to port 1.Write a program to multiply the contents of the PINB by the contents of the RAM location 0x600 and store the lower and the higher bytes of the result in the RAM locations 0x500 and 0x501 simultaneously LDI R16, blank blank DDRB, R16 blank blank , PINB blank R16, blank blank R10, R16 blank 0x500, blank blank 0x501,

