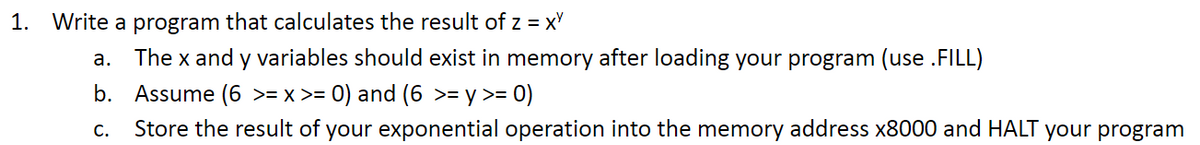
1. Write a program that calculates the result of z = xy a. The x and y variables should exist in memory after loading your program (use .FILL) b. Assume (6 >= x >= 0) and (6 >= y >= 0) C. Store the result of your exponential operation into the memory address x8000 and HALT your program
Q: hello. This is my code: #include #include #include typedef struct HuffmanNode { int…
A: Huffman Tree:The Huffman tree is a binary tree used in data compression algorithms. It assigns…
Q: Prototyping is most useful for requirements determination when communication problems have existed…
A: Prototyping is a valuable approach in the field of requirements determination, where the primary…
Q: What do you think are the most striking features of the internet when compared to a traditional…
A: The way individuals communicate, share information, and access services has been altered by the…
Q: Question 2 Saved what is the smallest value that can be represented in 10-bit, two's complement…
A: The smallest value that can be represented in a 10-bit, two's complement representation is…
Q: Which of the following is NOT an essential function performed by a firewall? What are the best…
A: A firewall is an essential safekeeping system that monitor and controls network traffic, including…
Q: We're using a rudimentary hash map in which all the keys and values are stored in the same…
A: Hash maps are data structures that provide efficient key-value pair storage and retrieval. They use…
Q: Provide an example of a context in which one of the four potential access control mechanisms may be…
A: What is potential access control mechanisms: Potential access control mechanisms refer to different…
Q: How different is it to have a licence to use software as opposed to owning the copyright to that…
A: The question investigates the distinctions between having a license to utilize software and owning…
Q: Is there a fixed number of linked lists in an m-size hash table? Please tell me what a hash function…
A: A hash table is a data structure that uses a hash function to map keys to their associated values.…
Q: How can various technical solutions help find intrusions in a network?
A: Technical Solutions for Network Intrusion DetectionNetwork intrusion refers to any unauthorized…
Q: What is the best way to implement a stack or a queue so that it can hold an arbitrary number of…
A: The best way to implement a stack or a queue so that it can hold an arbitrary number of elements:
Q: Create a stored procedure using the companyname, most recent order date, and ship address for…
A: Stored processes are database matches that may be reused for a predefined set of operations.By…
Q: What are some ways to prevent scope creep? How can you deal with users who make demands on a…
A: To prevent scope creep and effectively deal with user demands on a project, here are some strategies…
Q: After listing the different cloud computing services, the following part explains how organisations…
A: What is cloud computing: Cloud computing refers to the delivery of computing resources, such as…
Q: Expert data hackers are exploiting vulnerabilities in the banking industry. The efforts of The…
A: In today's digital age, cyber frauds perpetrated by hackers pose a significant threat to the banking…
Q: #include int main() { int N; scanf("%d", &N); int input[N], ind, rem;…
A: The code can be explained as follows:The code starts by reading an integer N from the standard…
Q: Show that: ¬q 1) p→¬q 2) (p∧r)∨s 3) s→(t∨u) 4) ¬t∧¬u where ¬ is denied.
A: To show that ¬q holds based on the given statements, we need to derive it using logical deductions.…
Q: How can Virtual Network Functions, which are implemented in software, improve the network's…
A: Virtual Network Functions (VNFs) are software-based network services that replicate the…
Q: How is a distributed encryption service defined in the context of big data and cloud computing?
A: Distributed encryption is a method of secure data, primarily focus on safeguarding in Order in an…
Q: Use the following confusion matrices to answer Questions 4 – 13. Please note that some of the…
A: Highest Recall Rate (also known as Sensitivity or True Positive Rate): Recall rate measures the…
Q: Technical duties of the DBA should be specified in depth, especially those related to the…
A: The Database Administrator, frequently called the DBA, is whoever or whatever is in cutting-edge…
Q: Choose the best answer. An algorithm to determine if a graph with n=>3 vertices is a star is:…
A: Graph theory, a fundamental branch of mathematics, studies graphs as mathematical structures that…
Q: A deque DQUE is to be implemented using a circular one-dimensional array of size N. Execute…
A: Define a circular array of size N to hold the elements of the deque. You'll also need to keep track…
Q: Please provide a concise explanation of memory addressing as well as the rationale for its utmost…
A: Memory address in computer systems is a basic concept. It refers to the scheme by which in order…
Q: The architecture of a CPU may consist of a universal register, a singular accumulator, or a stack.…
A: The architecture of the central processing unit (CPU) is an important part of computer design and…
Q: Create a software REMOVE_DUPLICATES that eliminates duplicate elements in a list L that appear…
A: Python program that removes consecutive duplicates from a list while maintaining the order of the…
Q: Is there a hash table that can handle m-sized linked lists? Is there a list of goals that should be…
A: Hash tables are widely used data structures that provide efficient key-value pair storage and…
Q: Explain the function of data independence within the ANSI SPARC architecture.
A: The question asked about the function of data independence within the ANSI SPARC architecture. The…
Q: Question 2 Saved what is the smallest value that can be represented in 10-bit, two's complement…
A: Two's complement and 7-bit sign/magnitude are two different ways of representing signed numbers in…
Q: Describe an API and its relationship to system operations.
A: APIs, short for Application indoctrination Interfaces, play a basic role in modern software…
Q: According to Wikipedia, IPv4 addresses are canonically represented in dot-decimal notation, which…
A: The code provided checks whether a given string s represents a valid IPv4 address or not. It returns…
Q: 9. Given the regular expression r = a(a+b)*b a) Show an nfa that accepts the language L(r) b) Show…
A: A regular expression is a sequence of characters that represents a pattern. It is a powerful tool…
Q: Thus, without the RET instruction, a procedure:
A: What is RET instruction: The "RET" instruction is an assembly language instruction that is used to…
Q: Object-oriented design must be utilised wherever it makes sense to do so. When the situation calls…
A: The decision to use object-oriented design or structured design depends on various factors,…
Q: What prerequisites must be met in order to determine whether a linked list T is empty, (i) simple…
A: A linked list is a linear data structure used to store and organize data elements. It consists of…
Q: Give information about the protocols, software, and hardware that are used by the most well-known…
A: Virtual Private Networks (VPNs) are widely used to enhance online privacy, security, and anonymity.…
Q: HTML HTML Web elements (header, footer, list, table, form …) Navigation (Links are clear and…
A: Web design which refers to the one it is the process of creating websites and involves combining…
Q: Use drawings to show the differences between scalar and superscalar processors. Compared to scalar…
A: It is type of processor that executes the scalar data it executes integers instructions and uses…
Q: Consider the following data entries: 21, 24, 4, 10, 30, 34, 12, 13, 16. Build up step by step an…
A: In this exercise, we will build an order 2 B+ tree index for the given data entries: 21, 24, 4, 10,…
Q: Maturity Model (Your response for this section should be limited to 6000 characters including…
A: Cybersecurity which refers to the practice of protecting networks, devices, programs, and data from…
Q: can you please fix the code to resolve the error:Oh no! You've got an error in your assembly code…
A: Assembler programming which refers to the one it is a type of computer programming that involves…
Q: Problem A5: For each graph G and H below, determine whether it has a hamiltonian cycle. Justify your…
A: Hamiltonian cycles are named after William Rowan Hamilton, an Irish mathematician who studied paths…
Q: Design a sequence detector circuit using the mealy model to detect when a value is not BCD, for…
A: A sequence detector circuit is a digital circuit that detects the occurrence of a specific sequence…
Q: Explain the concept of DNS (Domain Name System) and its role in the internet.??
A: The Domain Name System (DNS) is a vital component of the internet infrastructure that serves as a…
Q: What capabilities does the operating system of a desktop computer possess?
A: The question is getting some information about the capacities or functions that the operating system…
Q: When compared to one another, the Internet and the World Wide Web (WWW) have a number of…
A: The Internet and the World Wide Web (WWW) are two terms that are often used interchangeably, but…
Q: When compared, the Internet and the World Wide Web (WWW) have some fundamental differences. What are…
A: The Internet and the World Wide Web (WWW) are two interconnected but distinct concepts that have…
Q: Compare and contrast the three most popular types of networks and explain why each has its…
A: here is a comparison of the three most popular types of networks: local area networks (LANs),…
Q: Write a program that initializes a blank array and allows the user to input their own numbers (0 to…
A: Initialize a blank array of size n (5 <= n <= 20) to store user inputs.Create a loop that will…
Q: Natural and manmade disasters seem to be increasing in frequency and impact as the population grows,…
A: In this question we have to review the given website for the natural disasters discussion and then…
please meet the requirements regarding the LC3 simulator
Trending now
This is a popular solution!
Step by step
Solved in 3 steps

- In each of the following cases, write a short program in Vole to perform the requestedactivities. Assume that each of your programs is placed in memory starting at address 0x00.a. Move the value at memory location 0xD8 to memory location 0xB3.b. Interchange the values stored at memory locations 0xD8 and 0xB3.c. If the value stored in memory location 0x44 is 0x00, then place the value 0x01 in memorylocation 0x46; otherwise, put the value 0xFF in memory location 0x46(Practice) a. Using Figure 2.14 and assuming the variable name rate is assigned to the byte at memory address 159, determine the addresses corresponding to each variable declared in the following statements. Also, fill in the correct number of bytes with the initialization data included in the declaration statements. (Use letters for the characters, not the computer codes that would actually be stored.) floatrate; charch1=M,ch2=E,ch3=L,ch4=T; doubletaxes; intnum,count=0; b. Repeat Exercise 9a, but substitute the actual byte patterns that a computer using the ASCII code would use to store characters in the variables ch1, ch2, ch3, and ch4. (Hint: Use Appendix B.)a- Write a program which adds the values D8H, F5H and E9H. Put the sum in file register 15H for (low byte) and file register 16H for high byte. b- What is the content of (low byte) and (high byte) registers in Hex?
- Write an assembly program to set R0=1 if there's a 5 in one of ten memory locations, starting at x3100. At the beginning of the program, set R0 = 0. If no 5 is found, it should leave R0 set to 0. Please submit your assembly program below. I will run it with my data. If a 5 is found, output the following message to the console. "A 5 was found at x31xx." 31xx is the hex address of the 5. Here is the test data I used to generate the screen print below. It is not the test data I will use to grade your project. .ORIG x3100.FILL #10.FILL #20.FILL #30.FILL #40.FILL #50.FILL #5.FILL #70.FILL #5.FILL #90.FILL #100.ENDP1:Given the following memory values and a one-address machine with an accumulator,whatvalues do the following instructions load into the accumulator?·Word 20 contains 40.·Word 30 contains 50.·Word 40 contains 60.·Word 50 contains 70.a. LOAD IMMEDIATE 20b. LOAD DIRECT 20c. LOAD INDIRECT 20d. LOAD IMMEDIATE 30e. LOAD DIRECT 30f. LOADINDIRECT 30If the memory location at address 5 currently stores the value 8, what is the functional difference between writing the value 5 into cell number 6 and copying the contents of cell 5 into cell 6?
- Q2: Write program based on the following sequence of conditions: . Overwrite memory location $2800 with a value of $12345678 By using indirect addressing, copy a byte value in memory location $2000 into D3 by using address register A3. Increase value in D3 by $10.Write an assembly program to set R0=1 if there's a 5 in one of ten memory locations, starting at x3100. At the beginning of the program, set R0 = 0. If no 5 is found, it should leave R0 set to 0. Please submit your assembly program below. I will run it with my data. If a 5 is found, output the following message to the console. "A 5 was found at x31xx." 31xx is the hex address of the 5.Write a program to find the average of 32 bytes started at memory location [Mem 1]. If the average is greater than 42H then store the average at memory location [Mem 2] otherwise, store it at memory location [Mem 3].(microprocessor)
- Modify the following program in lc-3 to get the input(numbers) from the keyboard and print the result to console. .ORIG x3000Loop LD R0, number1 ; load number1 into R0LDR R1, number2 ; load number2 into R1ST R2, SaveR2 ; save register R2LD R5, goSUB ; load address of SUB into R4JSRR R5 ; go to subroutine whose address in R5STR R3, result ; store resultLD R2, SaveR2 ; restore old value R2HALTnumber1 .FILL #10number2 .FILL # -8goSUB .FILL SUB ; initialize goSUB to address of SUBSaveR2 .BLKW #1; reserve space SaveR2 and SaveR3result .BLKW #1SUB NOT R1, R1ADD R2, R1, #1ADD R3, R0, R2RET.ENDWrite programs that will accomplish the desired tasks listed below, using as few lines of code as possible e) Divide the data in RAM location 3EH by the number 12H ; put the quotient in R4 and the remainderin R5.f) Divide the data in RAM location 15H by the data in RAM location 16H ; put the quotient inexternal RAM location 7CH and the remainder in in external RAM location 7DH.g) Double the number in register R2, and put the result in register R3 (high byte) and R4 (low byte).Use logic operations.h) OR the contents of ports 1 and 2 ; put the result in external RAM location 0100Hi) Set Port 0, bits 1, 3, 5 and 7 to one, set the rest to zero.j) Clear bit 3 of RAM location 22H without affecting any other bit.k) Invert the data on the port 0 pins and write the data to port 1.Write a program to multiply the contents of the PINB by the contents of the RAM location 0x600 and store the lower and the higher bytes of the result in the RAM locations 0x500 and 0x501 simultaneously LDI R16, blank blank DDRB, R16 blank blank , PINB blank R16, blank blank R10, R16 blank 0x500, blank blank 0x501,

