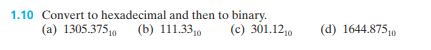
1.10 Convert to hexadecimal and then to binary. (a) 1305.3750 (b) 111.330 (c) 301.1210 (d) 1644.87510
Q: Introduce the procedures of model-based statistical testing process
A: Software testing is the act of examining the artifacts and the behavior of the software under test…
Q: Write a function named split-list in Scheme that takes a list and a length as input and returns two…
A: We need to write a function sit-lost in scheme.
Q: Write a program in C++ to do the following tasks. a) Read a number N from the user. b) Using…
A: Given requirement is, Write a program in C++ to do the following tasks. a) Read a number N from the…
Q: the following operation: write the operand as 4-bit 2's complement binary numbers, perform the…
A: The question has been answered in step2
Q: 4. Consider a node, t, in a decision tree. The set of training records in node t is Dt, which…
A: Dear Student, Formulae for finding Misclassification error = 1-max(p,1-p) //for two classes where…
Q: How do I code a Python program where get request to / should return index.html, get request to…
A: The question has been answered in step2
Q: If we have three categorical features, where each feature can take four values, and we have five…
A: The question has been answered in step2
Q: Write a complete Java program to read the final total mark of a student then assign and print the…
A: import java.util.Scanner; public class Main { public static void main(String[] args) {…
Q: Write a program that first asks a user for an input file name and an output file name. Assuming that…
A: This is a file handling program in python. Three basic operation we need to do: open the files with…
Q: Question 1 Write a Python program to implement a Bayesian classifier. The implementation is…
A: Solution: Given, Write a Python program to implement a Bayesian classifier.
Q: We have the following method used in a chess game: boolean canMoveTo(int x, int y). This method is…
A: Introduction One of the oldest and most widely played board games is chess. It is played between two…
Q: Create a Python language that is not key sensitive and will display the secondary color when you mix…
A: Case-insensitive: Case-insensitive means that both the string you are comparing and the…
Q: Write a Java program that computes the depth of a binary tree
A: code for the depth method would be as follows: depth(TreeNode root){…
Q: Complete the Python program to create a Horse table, insert one row, and display the row. The main…
A: Answer:
Q: Q.32 Explain role of key distribution centre in symmetric system.
A: The role of key distribution centre in symmetric system.
Q: 10 In (²+1) • e 2.ƒ(x)= 10ln ·(1²+1)
A: The given function is:- fx=10ln1x2+1×e-x2+x Python Introduction:- Python is a dynamic, interpreted…
Q: Question: in Excel, only one column or row can be inserted at a time. reqiured: please answer this…
A: Let's see the answer:
Q: logiesThinking about the ACME database, please explain which data technology would you use ODBC,…
A: Database Connectivity and Web TechnologiesThinking about the ACME database, please explain which…
Q: Elon Musk the CEO of Tesla, wants to distribute the ISP starting with 150.80.0.0/16. You ar assigned…
A: ISP: Imagine it as a cable company, but one that links you to the internet rather than TV channels.…
Q: The goal of this computational filter was to save company time, but right now it's pretty…
A: The Python code is given below with code and output screenshot Happy to help you ?
Q: ARM PROCESSOR & ASSEMBLY
A: Given :- In the above question, the statement is mention in the above given question Need to…
Q: 2. (a) Write down the formal definition (not the limit definition) for f(n) = (g(n)).
A: Here is the explanation regrading the equation f(n) = Θ(g(n)):
Q: C++ PROGRAMMING VARIABLE DECLARATION. Create a variable called carName, assign the value…
A: Answer the above question are as follows:
Q: Python For this assignment, you will write a program to allow the user to store the names and phone…
A: Answer: We have done code in the python programming language and attached code screenshot code…
Q: 8. Starting with array S[] = { 123 34 89 56 150 12 9 } indexed from 1 to 7, sort S[] using…
A: Merge Sort - Merge sort is an efficient, general-purpose, and comparison-based sorting algorithm.…
Q: Q.1 Explain the different regularization techniques used with Linear regression to handle…
A:
Q: Write short notes on: Ridge regression.
A: Dear student, the answer is provided below.
Q: Binary number to Hexadecimal number? (1101 1001 1011 0011)2
A: Introduction: All binary code used in computing systems is based on binary, which is a numbering…
Q: Assume that there are 12 records in training data and there are three classes: C1, C2, and C3. Write…
A: We need to find the number of records in each class so that the Gini index is maximum.
Q: There are many types of cybersecurity liability policies covering a host of eventualities. What…
A: The cybersecurity law which includes the insurance policy is IT act in which one has to pay full…
Q: n the example below, does the change to X in myMethod affect x in main? Does the change to y in…
A:
Q: JAVA CODE PLEASE Linked List Practice ll by CodeChum Admin Write a function printNodes that takes in…
A: As per the question statement, It is asked to write JAVA code.
Q: Write the following sequence of code into RISC-V assembler. Assume that x, y, and z are stored in…
A: RISV-V assembler: Integer, logic, and a few memory commands are all included in RISC-V. Integer…
Q: .32 Explain role of key distribution centre in ymmetric system.
A: Explain role of key distribution centre in symmetric system A key distribution center (KDC) in…
Q: True or False? i) Predicting earthquake by monitoring seismic waves is not a data mining task.…
A: The answers to the questions are given below with proper explanation for each Happy to help you ?
Q: You are asked to design a reservation framework. This could be expanded into an application to…
A: Framework A framework is a physical or conceptual structure that is meant to support or serve as a…
Q: Q.30 Explain how ElGamai scheme generate and verify the digital signature.
A: ElGamal signature scheme The ElGamal signature scheme is a digital signature scheme considering the…
Q: Question: 1) Column heads in Excel are made up of numbers required: please answer this question by…
A: Given statement is, Column heads in Excel are made up of numbers required.
Q: Show that the solution of LaTeX: T(n) = T(\lceil n/2 \rceil) + 1 is LaTeX: \mathcal{O}(\lg n).
A: Given
Q: Which of the following is correct code to open the file input.txt for reading? outfile =…
A: Answer:
Q: Write a Java expression that is the opposite of the following range. You MAY NOT simply use a NOT,…
A: The Java expression is given below:
Q: What is the result of the following expression? 45 % 7
A: Modulo Operator: The symbol % denotes the modulo operator. It is the arithmetic operator. A modulo…
Q: completed, use a queue to store the duration of each job in sequence, and calculate the turn around…
A: In first come first serve algorithm, the process which comes first will be executed first which…
Q: What are the disadvantages of firewalls?
A: Firewalls are essentially a form of barricade that stops hackers from attacking a network. One of…
Q: What is the Manhattan distance between the following two points? P₁ = (2, 1) and P₂ = (-1, 3)
A: Manhattan distance is also known as taxicab distance.
Q: Please give an example of a sequence diagram in relation to the analysis phase of the SDLC
A: HI THEREI AM ADDING ANSWER BELOWPLEASE GO THROUGH ITTHANK YOU
Q: Type the following solution in R-Code:
A: Answer: Answer: Name <- c("Penguins", "Knights", "Devils", "Rangers") Offense <- c(11,4,8,7)…
Q: Write a function named merge-sort in Scheme that takes a list of integers as input and returns a…
A: Given To know about the merge sort algorithm .it's time complexity is O(logn) .so it is very good…
Q: Draw an activity diagram for ticket vending process. A vending machine is used to dispense ticket.…
A: The activity is started by a commuter actor who needs to buy a ticket. The ticket vending machine…
Q: Redundant Inequalities:prove statement Let e1, e2 be two symbolic expressions defined in V ∪P and q…
A: given data: Let e1, e2 be two symbolic expressions defined in V ∪P and q ∈ V ∪P.c1, c2 are two…
just convert to binary, don't bother with hex
Step by step
Solved in 2 steps with 2 images

- 31 Convert the hexadecimal IEEE format floating point single precision number 0x40200000 to decimal: First convert hex to binary (Provide a space between four bit groups. Example 111 1010 not 1111010) Sign bit Exponent in decimal after removing excess 127. Just the exponent. Example 3 not 23 Mantissa or Significand (Provide a space between four bit groups. Example 111 1010 not 1111010) Put it together and convert to decimalCalculate (3.41796875 *10-3 * 6.34765625 *10-3) by hand, assuming each of the values arestored in the 16-bit half precision format described in in the textbook. Assume 1 guard, 1 roundbit, and 1 sticky bit, and round to the nearest even. Show all the steps, and write your answer inthe 16-bit floating point format.Calculate (4.41762275 *10-3 + 6.34225625 *10-3) * 1.05225 * 102 by hand, assuming each of the values are stored in the 16-bit half precision format described in in the textbook. Assume 1 guard, 1 round bit, and 1 sticky bit, and round to the nearest even. Show all the steps, and write your answer in both the 16-bit floating point format and in decimal.
- 98. Usually, it takes 10-bits to represent one character. How many characters can be transmitted at a speed of 1200 BPS? a. 12 b. 120 c. 1200 d. 12000Calculate (3.41700875 *10-3 + 6.34005625*10-3)* 1.25625* 102 by hand, assuming each of the values are stored in the 16-bit half precision format describedin in the textbook. Assume 1 guard, 1 round bit, and 1 sticky bit, and round to thenearest even. Show all the steps, and write your answer in both the 16-bit floating point format and in decimal.1. List the octal and hexadecimal numbers from (16)10 to (32)10.2. Convert the following numbers with indicated bases to decimal.(a) (4310)5(b) (123)8(c) (2F A)16(d) (212)33. What is the largest binary number that can be expressed with:(a) 8 bits,(b) 10 bits,(c) 16 bits.In each case, write their decimal and hexadecimal equivalents.4. Determine the base of the numbers for the following operation to be correct: 54/4 = 135. Convert the hexadecimal number 68BE to binary, and then convert it from binary to Octal.6. Convert the decimal number 431 to binary in two ways:(a) Convert directly to binary.∗Engr. Sheraz Ali Khan, PhD 1 (b) First convert it into hexadecimal and then from hexadecimal to binary. Which is faster in youropinion?7. Express the following numbers in decimal:(a) (10110.0101)2(b) (26.24)8(c) (F AF A.B)168. Solve the following conversion problems:(a) Convert the decimal number 27.315 to binary.(b) Calculate the binary equivalent of 2/3 to eight places after the binary point.…
- Question5) Given Two Integers 11 and 9 how many binary bits are required to represent the larger one?A. How many bits are needed to represent 214(octal) in binary?B. Show the 2’s complement binary (10 bits) representation of (-246)(10)C. Convert the following 2’s complement binary number to decimalrepresentation:10010010a) Use the two’s complement binary representation to represent each of the following integers as 10-bit binary numbers. i) -13710 ii) 14510 iii) -15810 iv) 16710 v) -11510 b) If an 8-bit binary number is used to represent an analog value in the range from 0 to 100kg, what does the binary value 011001002 represent?
- 1. Assume numbers are represented in 8-bit two's complement Show the calculation of the following: a) 5 + 10 b) 5 – 10 c) -5 + 10 d)-5 – 10 2. Represent the following decimal numbers or values according to the given requirements: a) +4 in both binary sign/magnitude and two's complement b) -6 in both binary sign/magnitude and two's complement c) -85 in two's complement d) +52 in two's complement 3. Find the following differences using twos complement arithmetic: a) 001000 – 110111 b) 10100101 – 011110 c) 100100001011 – 101010110011 d) 10011011 – 10100101given the 16 bit value 1001101011001101 . what operation must be performed in order to see to 1 the last eight bits?What decimal value does the 8-bit binary number 10010110 have if it is represented using Excess-M representation? a) If high-order interleaving is used, where would address 37 (base 10) be located? b) If low-order interleaving is used, where would address 28 (base 10) be located

