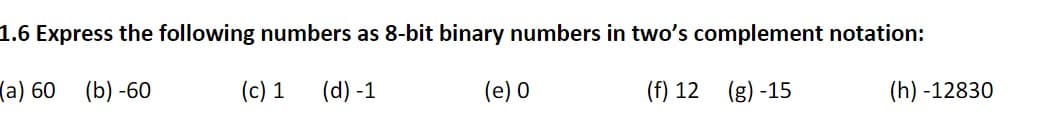
1.6 Express the following numbers as 8-bit binary numbers in two's complement notation: (a) 60 (b) -60 (c) 1 (d) -1 (e) 0 (f) 12 (g) -15 (h) -12830
Q: Suppose the implementation of an instruction set architecture uses three classes of instructions, wh...
A: Intro Suppose the implementation of an instruction set architecture uses three classes of instruct...
Q: *used for declaration for all forms global O dim form
A: Ans: Global
Q: in java eclipse ide Read from console a 3-digit integer Write code to sum digits in this number. Fo...
A: // statementimport java.util.Scanner; public class Main{ public static void main(String[] args) { ...
Q: Watch the video "Microsoft's Agile Transformation Story" by Donovan Brown. https://youtu.be/nno6Dwev...
A:
Q: SolarWinds is a major software company based in the USA, which provides system management tools for ...
A:
Q: Write a Java program to find the sum of digits of a user entered number till that number becomes one...
A: Introduction:
Q: Problem 1. Answer the following questions. No mark will be given if no valid reason is given. (a) (1...
A:
Q: 1. To keep track of students and their advisors, a university uses the table structure shown below. ...
A: Note: As per our company guidelines we are supposed to answer only first 3 sub parts. Kindly repost ...
Q: What type of input does the following program require, and in what order must the input be provided?...
A: what type of input does require
Q: What is the importance of linux partitioning?
A: The answer is
Q: Here is code of bubble sort. It's run time complexity is 0(n²). Change the code in a way so that its...
A: Best case scenario is when the list is already sorted. In that case, swapping of numbers does not ta...
Q: *used for declaration for all forms global O dim form O O
A: Here is the detailed explanation of the answer
Q: A micro instruction format has field which is divided into 2 subfields F1 and F2, each having 15 dis...
A: Logic , if there are n micro- operation then we can represent it in form of 2n where n will represen...
Q: Consider a two-link network where Host A is connected to the router by a 1 Mbps link with 10 ms prop...
A: What is the transmission delay (in ms) of the packet from therouter to Host B?
Q: *used for declaration for all forms global O dim form O O
A: global keyword makes the scope of variable global. It is not used for declaration for all forms. Bec...
Q: No stable storage can be achieved. a. State why it can't. b. Describe how database systems handle th...
A: It is known that by the definition, The information which is in the Stable Storage, can never be los...
Q: Write a program to create a new key pair, and then use the new key pair to launch an EC2 instance, w...
A: Lets see the solution in the next steps
Q: b) What does "cooperative" multithreading entail in a multithreading system? What are the benefits a...
A: Intro b) What does "cooperative" multithreading entail in a multithreading system? What are the bene...
Q: For the following situation, please indicate whether we should focus on having a very low false posi...
A: 1) An inspection for food in a restaurant in which we decide to skip a final test before serving it ...
Q: Given x = [2 45-10 8369-4 14], write a code using For loop to find the largest and the smallest Valu...
A:
Q: Open source software is a hot topic right now. and provide two instances, each with a short descript...
A: In basic terms, open-source software is software that anybody may modify and distribute since its de...
Q: What was the overall effect of the Capital One security breach? Is there any way this could have ...
A: Intro What was the overall effect of the Capital One security breach? Is there any way this could ...
Q: It might be hard for the database to stay up to date if some log records about a block aren't sent t...
A: Find the answer given as below:
Q: :the output of (Print "a", "b", "c") is abc O ab c abc O
A: According to the question this double quotes in print function help to print the string with the spa...
Q: turing machine a>b>c please also explain draw turing machine for a>b>c where a,b and >=0 please exp...
A: turing machine a>b>cplease also explain draw turing machinefor a>b>cwhere a,b and >=...
Q: Solve this attachment
A: Data dependencies are also termed Instruction Hazards. It arises when an instruction is trying to re...
Q: Is there anything good that comes from compiling to bytecode instead of machine code?
A: Is there anything good that comes from compiling to bytecode instead of machine code?
Q: What exactly is a pipe, and when is it used?
A: Introduction: A pipe is a conceptual link between two processes that allows the standard output of o...
Q: Compare and contrast the advantages of imperative, functional, and declarative programming languages...
A: Comparing and contrasting the advantages of imperative, functional, and declarative programming lang...
Q: between priva
A: given - Distinguish between private-key and public-key encryption. Include examples of when and why...
Q: Assume you want to use shared-nothing parallelism to manage a workload with a large number of tiny t...
A: INTRODUCTION: SHARED-NOTHING-PARALLELISM: No memory or disc space is shared between processors in a ...
Q: Give at least three reasons why restrictions should always be imposed by the database rather than th...
A: Introduction: Constraints: These are the rules/restrictions that are used in DBMS to ensure that t...
Q: Stanford Enterprises has provided its manufacturing estimated and actual data for the year end. The ...
A: Solution ::
Q: eering differ from software engineering? Support your answer with examples.
A: given - How does computer engineering differ from software engineering? Support your answer with exa...
Q: Three examples of instruction mnemonics are show
A: Actually, given given question regarding instruction mnemonics.
Q: Design the CMOS diagram for the following Table: (A, B & C are the inputs and Y is the output in the...
A: According to the information given:- We have to design CMOS diagram on the basis of the truth table ...
Q: Where can I get Wifi security for the following security type: When the conventional method on a Win...
A: Intro WIFI Protected Access II is a security protocol used to protect wireless computer networks. I...
Q: Give two reasons why a database could include null values.
A: Answer : 1. If the value is unknown.For example, if you have a form where the zip code is not mandat...
Q: Question 4 While connecting the inputs and the outputs of a circuit in a stick diagram, which type o...
A: A stick diagram is a diagram which is used to plan the layout of a transistor cell. Sticks or lines ...
Q: What do you mean by subnet mask?
A: Lets understand subnet mask: for every Ip (32 bit address), there is network part(network bits) and ...
Q: With practical examples, discuss the difference(s) between a Web Server software and a Web Client so...
A: Web applications are the application which runs on world wide web that is consuming both web server ...
Q: *used for declaration for all forms global O dim form O O
A:
Q: dentify all the strings for the following language:
A:
Q: Write a Python program to all the occurences of the strings other than "Java" from the list given be...
A: As per the requirement program is written in python. Algorithm: Step 1: Initialize a str_list with r...
Q: Show the representation of –22 (assuming 8-bit registers) using a) Signed-magnitude representation. ...
A: The question is to show the representation of -22 to the given formats.
Q: It's important to know what each part of an assembly language instruction is called.
A: answer is
Q: Why are there so many different partitioning algorithms in use by operating systems, and why differe...
A: In operating systems, it contains many partitioning algorithms which are used to decide which partit...
Q: Discuss security threats to databases and their respective countermeasures
A: Defined the security threats to databasesand their respective countermeasures
Q: 4. Write a Python program to remove all the occurrences of the strings other than "Python" from the ...
A: Write a Python program to remove all the occurrences of the strings other than "Python" from the lis...
Q: Why don't we use the ordinary least square to learn a linear regression model for a classification p...
A: Ans.) Option B i.e. OSL will learn a bad linear regression model for a classification.
According to the Bartelby guideline we are suppose to answer only First 3 sub part of question at a time.
Kindly repost the remaining question.
Trending now
This is a popular solution!
Step by step
Solved in 3 steps with 2 images

- 6. Convert the following numbers from unsigned binary notation to decimal notation, and from 6-bit 2's complement notation to decimal notation: i) 110011, ii) 001101, iii) 101101 7. Show how each of the following floating point values would be stored using IEEE-754 single precision (be sure to indicate the sign bit, the exponent, and the significand fields): a. 12.5 b. −1.5 c. 0.75 d. 26.625 8. The following is a representation of a decimal floating value using IEEE-754 single precision. Find out the value in decimal. 0 10000011 10101000000...0The most common binary code in use today is the 8 bit ASCII code. What do the letters ASCII stand for? A. American Standard Code for International Interchange B. American Standard Code for Information Interchange C. American Standard Code for Intelligence Interchange D. American Scientific Code for Information Interchange E. None of the above1. Suppose (27.625 base 10) is represented using IEEE754 Double Precision Floating Point Format. What is the Mantissa? Do not involve a space character when you type your answer. 2. Suppose (27.625 base 10) is represented using IEEE754 Double Precision Floating Point Format. What is the Exponent? Do not involve a space character when you type your answer. 3. Suppose (27.625 base 10) is represented using a 16-bit Floating Point Format where 1 bit is for the sign bit, 5 bits is for exponent and 10 bits is for mantissa. What is the mantissa? Do not involve a space character when you type your answer.
- Consider a 32-bit hexadecimal number stored in memory as follows: Address Value 100 2A 101 C2 102 08 103 1B If the machine is little endian and the number is an IEEE single-precision floating-point value, determine the decimal equivalent of the number stored at address 100 (you may leave your answer in scientific notation form, as a number times a power of two).CPU contains a special bit called the overflow bit , denoted by V. When CPU adds two binary integers, if their sum is out of range when interpreted in 2's complement representation, then V is set to _____, otherwise V is set to _______. Question 4 options: A. 0 : 0 B. 1 : 0 C. 0 : 1 D. 1 : 1 2 X = 0 0000 0000 1000 0000 0000 0000 0000 000 is an IEEE 754 single precision floating point number, what is the decimal value of X? Question 5 options: 1.5 × 2–127 0.5 × 2–127 1.5 × 2–126 0.5 × 2–126 None of the above1. List the octal and hexadecimal numbers from (16)10 to (32)10.2. Convert the following numbers with indicated bases to decimal.(a) (4310)5(b) (123)8(c) (2F A)16(d) (212)33. What is the largest binary number that can be expressed with:(a) 8 bits,(b) 10 bits,(c) 16 bits.In each case, write their decimal and hexadecimal equivalents.4. Determine the base of the numbers for the following operation to be correct: 54/4 = 135. Convert the hexadecimal number 68BE to binary, and then convert it from binary to Octal.6. Convert the decimal number 431 to binary in two ways:(a) Convert directly to binary.∗Engr. Sheraz Ali Khan, PhD 1 (b) First convert it into hexadecimal and then from hexadecimal to binary. Which is faster in youropinion?7. Express the following numbers in decimal:(a) (10110.0101)2(b) (26.24)8(c) (F AF A.B)168. Solve the following conversion problems:(a) Convert the decimal number 27.315 to binary.(b) Calculate the binary equivalent of 2/3 to eight places after the binary point.…
- The following is a string of ASCII characters whose bit patterns have been converted into hexadecimal for compactness: 73 F4 E5 76 E5 4A EF 62 73. Of the eight bits in each pair of digits, the leftmost is a parity bit. The remaining bits are the ASCII code. Convert the string to bit form and decode the ASCII.31 Convert the hexadecimal IEEE format floating point single precision number 0x40200000 to decimal: First convert hex to binary (Provide a space between four bit groups. Example 111 1010 not 1111010) Sign bit Exponent in decimal after removing excess 127. Just the exponent. Example 3 not 23 Mantissa or Significand (Provide a space between four bit groups. Example 111 1010 not 1111010) Put it together and convert to decimal1) Answer the following questions: What is the greatest magnitude negative number one can represent in n-bit 2'scomplement code? 2)Show the 8-bit binary signed-magnitude representation for the following decimalnumbers: -109 10 +43 10 3)Perform the following additions and subtractions. Assume the numbers arestored in signed-magnitude base 2 representation. -1010111 + -10011
- 8) A number with 6 digits (in its decimal notation) will: a)have between 15 and 21 digits in its binary notation b)have 10 digits in its base 6 notation c)always occupy less than 21 bits in its notation in the 2's complement encodingNegative signed binary numbers What is the decimal representation of the 2-bit signed binary number 11? What is the decimal representation of the 16-bit signed binary number 1111_1111_1111_1111? How do the signed binary representations differ (ignoring the underscores)? What is the decimal representation of the 8-bit signed binary number 1001_0001? What is the decimal representation of the 16-bit signed binary number 1111_1111_1001_0001? How do the signed binary representations differ (ignoring the underscores)? What is the decimal representation of the 9-bit signed binary number 1_0001_0001? What is the decimal representation of the 16-bit signed binary number 1111_1111_0001_0001?Negative signed binary numbers What is the decimal representation of the 2-bit signed binary number 11? What is the decimal representation of the 16-bit signed binary number 1111_1111_1111_1111?

