1.7¹ mod 23 = 7 2.72 mod 23 = 3 3.74 mod 23 9 = 4.78 mod 23 = 5.716 mod 23 = || 6.732 mod 23 = 7.764 mod 23 =
1.7¹ mod 23 = 7 2.72 mod 23 = 3 3.74 mod 23 9 = 4.78 mod 23 = 5.716 mod 23 = || 6.732 mod 23 = 7.764 mod 23 =
C++ for Engineers and Scientists
4th Edition
ISBN:9781133187844
Author:Bronson, Gary J.
Publisher:Bronson, Gary J.
Chapter4: Selection Structures
Section: Chapter Questions
Problem 14PP
Related questions
Question
numbers 4,5,6,7
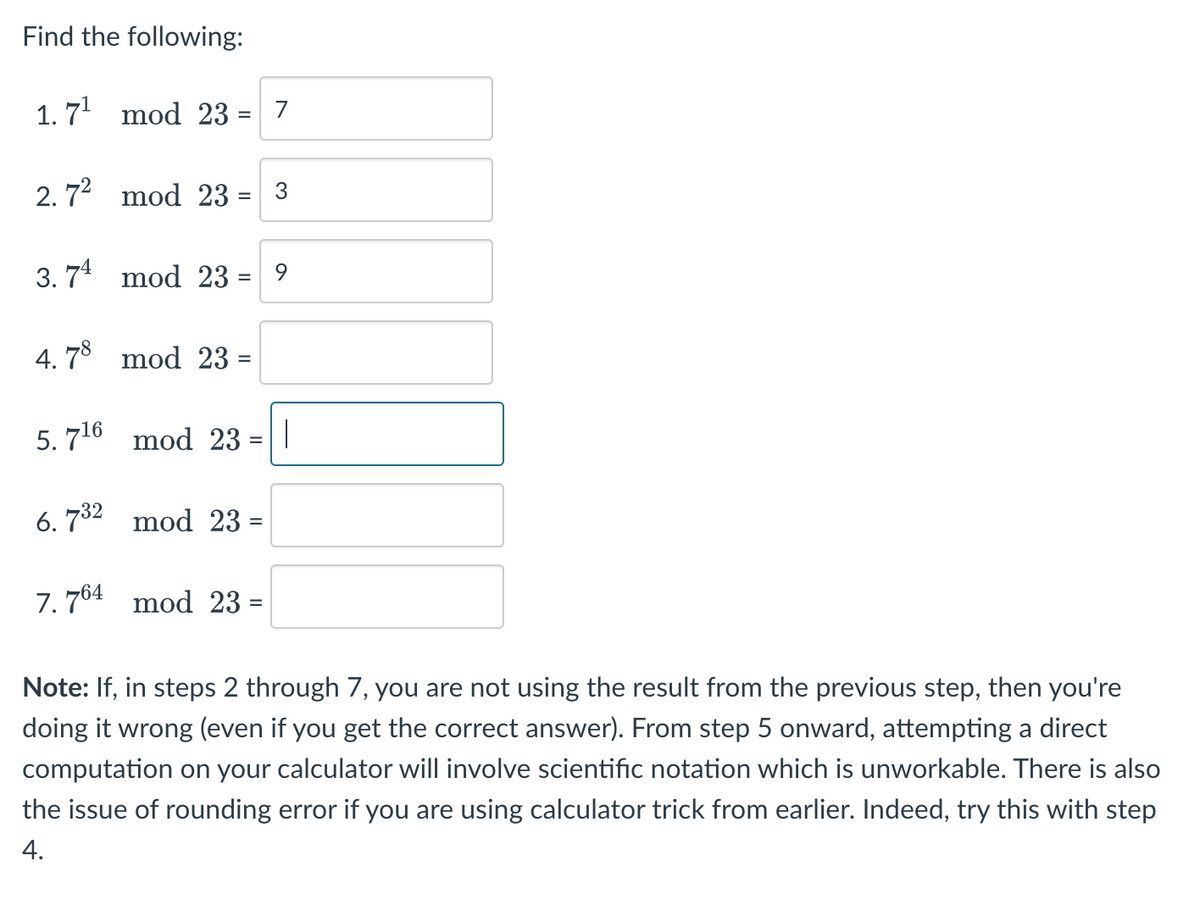
Transcribed Image Text:Find the following:
1.7¹ mod 23 = 7
2.7² mod 23 = 3
3.74 mod 23 = 9
4.78 mod 23 =
5.7¹6 mod 23
6.732 mod 23 =
7.764 mod 23 =
|
Note: If, in steps 2 through 7, you are not using the result from the previous step, then you're
doing it wrong (even if you get the correct answer). From step 5 onward, attempting a direct
computation on your calculator will involve scientific notation which is unworkable. There is also
the issue of rounding error if you are using calculator trick from earlier. Indeed, try this with step
4.
Expert Solution
This question has been solved!
Explore an expertly crafted, step-by-step solution for a thorough understanding of key concepts.
This is a popular solution!
Trending now
This is a popular solution!
Step by step
Solved in 2 steps

Knowledge Booster
Learn more about
Need a deep-dive on the concept behind this application? Look no further. Learn more about this topic, computer-science and related others by exploring similar questions and additional content below.Recommended textbooks for you

C++ for Engineers and Scientists
Computer Science
ISBN:
9781133187844
Author:
Bronson, Gary J.
Publisher:
Course Technology Ptr

C++ for Engineers and Scientists
Computer Science
ISBN:
9781133187844
Author:
Bronson, Gary J.
Publisher:
Course Technology Ptr