1.Challenge in using AI,IoT &Robot 2.what is digital privacy? Why it use? 3.explain digital privacy principle
1.Challenge in using AI,IoT &Robot 2.what is digital privacy? Why it use? 3.explain digital privacy principle
Principles of Information Security (MindTap Course List)
6th Edition
ISBN:9781337102063
Author:Michael E. Whitman, Herbert J. Mattord
Publisher:Michael E. Whitman, Herbert J. Mattord
Chapter11: Security And Personnel
Section: Chapter Questions
Problem 5E
Related questions
Question
1.Challenge in using AI ,IoT &Robot
2.what is digital privacy? Why it use?
3.explain digital privacy principle
Transcribed Image Text:{ 106 }
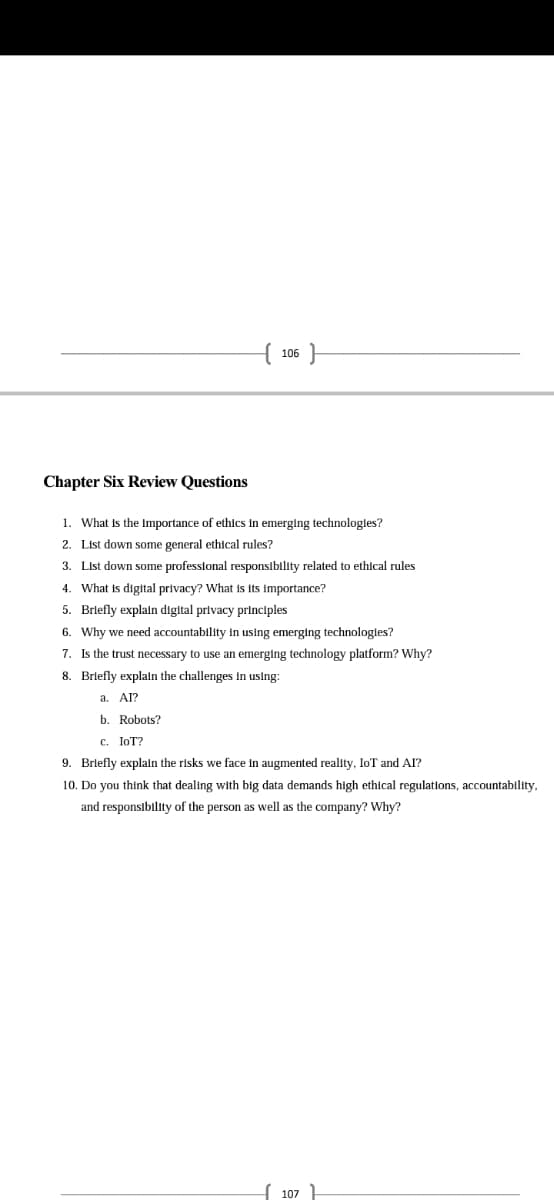
Chapter Six Review Questions
1. What is the Importance of ethlcs In emerging technologles?
2. List down some general ethical rules?
3. List down some professional responsibility related to ethical rules
4. What is digital privacy? What is its importance?
5. Brlefly explaln digital privacy principles
6. Why we need accountability in using emerging technologles?
7. Is the trust necessary to use an emerging technology platform? Why?
8. Brlefly explaln the challenges In using:
a. Al?
b. Robots?
c. IoT?
9. Brlefly explaln the risks we face In augmented reality, IoT and AI?
10. Do you think that dealing with big data demands high ethical regulations, accountability,
and responsibility of the person as well as the company? Why?
107
Expert Solution
This question has been solved!
Explore an expertly crafted, step-by-step solution for a thorough understanding of key concepts.
Step by step
Solved in 2 steps

Knowledge Booster
Learn more about
Need a deep-dive on the concept behind this application? Look no further. Learn more about this topic, computer-science and related others by exploring similar questions and additional content below.Recommended textbooks for you

Principles of Information Security (MindTap Cours…
Computer Science
ISBN:
9781337102063
Author:
Michael E. Whitman, Herbert J. Mattord
Publisher:
Cengage Learning

Fundamentals of Information Systems
Computer Science
ISBN:
9781337097536
Author:
Ralph Stair, George Reynolds
Publisher:
Cengage Learning

Principles of Information Security (MindTap Cours…
Computer Science
ISBN:
9781337102063
Author:
Michael E. Whitman, Herbert J. Mattord
Publisher:
Cengage Learning

Fundamentals of Information Systems
Computer Science
ISBN:
9781337097536
Author:
Ralph Stair, George Reynolds
Publisher:
Cengage Learning