10 A Moving to another question will save this response. Question 9 Many of the internal OS services are provided by the module, which contains the most important operating system processing functions. CPU O root O kernal central A Moving to another question will save this response. MacBook Air 20 O00 O00 F1 F2 F3 F4 F6 F10 2 @ 3 # £ 4 $ 5% 7. & 01 O O
10 A Moving to another question will save this response. Question 9 Many of the internal OS services are provided by the module, which contains the most important operating system processing functions. CPU O root O kernal central A Moving to another question will save this response. MacBook Air 20 O00 O00 F1 F2 F3 F4 F6 F10 2 @ 3 # £ 4 $ 5% 7. & 01 O O
Chapter5: Advanced Personalization And Customization
Section: Chapter Questions
Problem 1AYK
Related questions
Question
100%
Please fast I have only 10 min
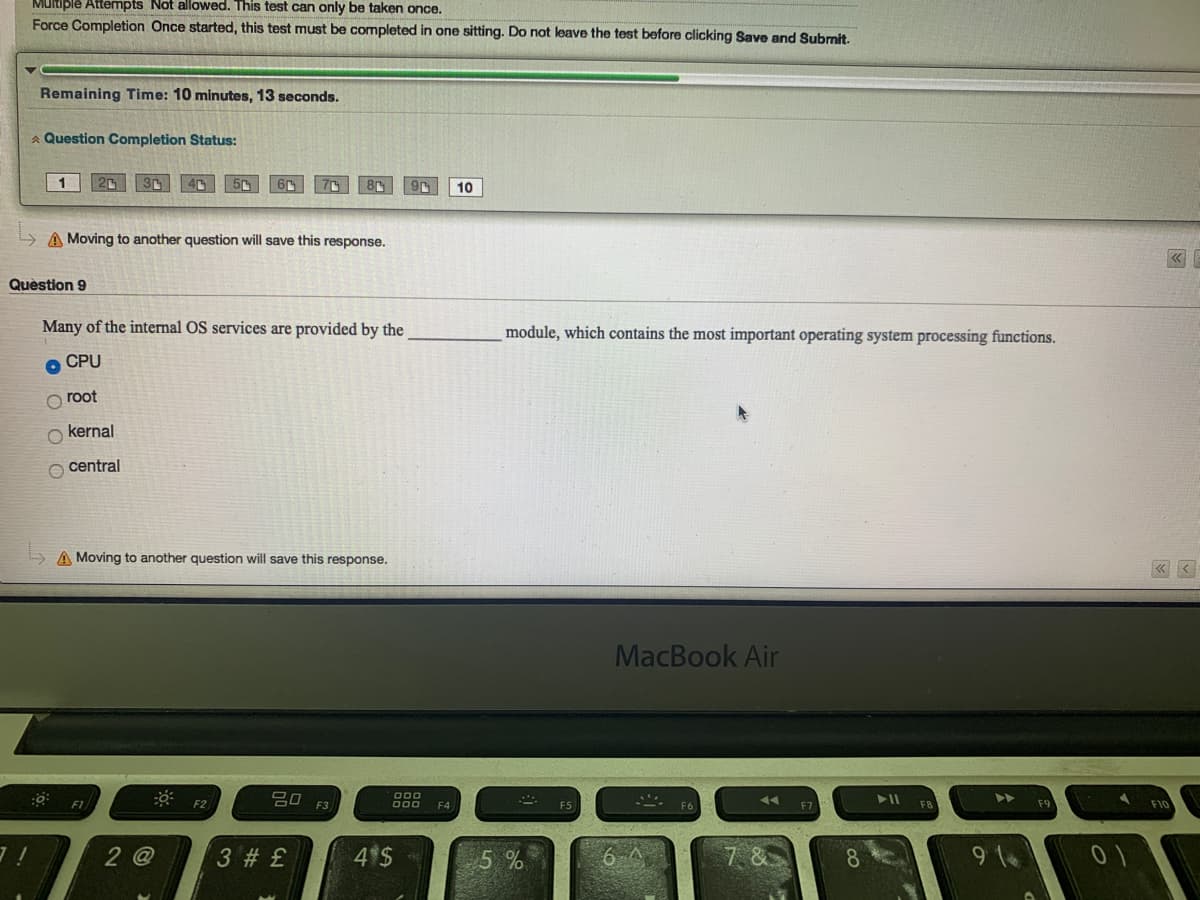
Transcribed Image Text:Multiple Attempts Not allowed. This test can only be taken once.
Force Completion Once started, this test must be completed in one sitting. Do not leave the test before clicking Save and Subrnit.
Remaining Time: 10 minutes, 13 seconds.
A Question Completion Status:
10
A Moving to another question will save this response.
Quèstion 9
Many of the internal OS services are provided by the
module, which contains the most important operating system processing functions.
O CPU
root
O kernal
O central
A Moving to another question will save this response.
« <
MacBook Air
吕口
O00
000
F2
F4
2 @
3 # £
4 $
5%
7. &
8.
9 1
Expert Solution
This question has been solved!
Explore an expertly crafted, step-by-step solution for a thorough understanding of key concepts.
This is a popular solution!
Trending now
This is a popular solution!
Step by step
Solved in 2 steps

Knowledge Booster
Learn more about
Need a deep-dive on the concept behind this application? Look no further. Learn more about this topic, computer-science and related others by exploring similar questions and additional content below.Recommended textbooks for you

Microsoft Windows 10 Comprehensive 2019
Computer Science
ISBN:
9780357392607
Author:
FREUND
Publisher:
Cengage

A+ Guide To It Technical Support
Computer Science
ISBN:
9780357108291
Author:
ANDREWS, Jean.
Publisher:
Cengage,

LINUX+ AND LPIC-1 GDE.TO LINUX CERTIF.
Computer Science
ISBN:
9781337569798
Author:
ECKERT
Publisher:
CENGAGE L

Microsoft Windows 10 Comprehensive 2019
Computer Science
ISBN:
9780357392607
Author:
FREUND
Publisher:
Cengage

A+ Guide To It Technical Support
Computer Science
ISBN:
9780357108291
Author:
ANDREWS, Jean.
Publisher:
Cengage,

LINUX+ AND LPIC-1 GDE.TO LINUX CERTIF.
Computer Science
ISBN:
9781337569798
Author:
ECKERT
Publisher:
CENGAGE L

Principles of Information Systems (MindTap Course…
Computer Science
ISBN:
9781285867168
Author:
Ralph Stair, George Reynolds
Publisher:
Cengage Learning