10) Compute the weakest precondition for the sequence of statements: (Statement 1) b = 2b + 1; (Statement 2) b = b-3{b < 0}
Q: As wireless networks are essentially distinct, they may provide their users with their own set of…
A: Explanation: User problems with wireless networks are: network connection issues A user does not…
Q: Please provide an explanation of real-time systems and support it with examples.
A: A package called Real-time System is designed to support real-time applications that handle data…
Q: Security, cybercrime, privacy, social interaction, and governance are just a few examples of the…
A: Introduction: In today's technology-driven world, the importance of computer ethics cannot be…
Q: To do this, there are many other approaches that may be used, but the following are the five that…
A: The only difference between Distributed Denial of Service (DDoS) and Denial of Service assaults is…
Q: How linked are scientific inquiry and technological innovation, and what effects do they have on our…
A: Overview: Several strong technologies help homes and businesses. New technologies impact autos,…
Q: Can the workings of a computer be explained in this way? Following that, we'll probably talk about…
A: Yes, the workings of a computer can be explained in a simple and easy-to-understand way.…
Q: If the numbers in our list were not unique and therefore the largest number could occur more than…
A: We need to discuss if the algorithm finds the first occurrence of largest number Or not. We have to…
Q: How did the current trends that are associated with cybercrime come to be so popular? If you want a…
A: PC misbehavior, or cybercrime, utilises computers to perpetrate crimes like deceit, dealing with…
Q: Discussing software design's numerous facets is crucial.
A: Software design is a multifaceted, intricate process. The technical features of the software, the…
Q: ake, for example, a piece of software that, through the internet, allows a surgeon to do surgery on…
A: Answer is
Q: discuss non-technical cyberattacks
A: Your answer is given below.
Q: Waterfall Systems Development may be summarized: What distinguishes this from Agile?
A: Waterfall and Agile are two different software development methodologies with distinct approaches…
Q: Please enlighten me on the different domains in which Automata Theory finds useful application.
A: There are several varieties of automata. An illustration of one of such automata is as follows: Push…
Q: Under a wide range of situations, the network's performance might suffer.
A: Network: Network is a collection of connected devices that communicate with each other over a shared…
Q: JAVA PROGRAMMING I need an expert to write Test application to run the MyArrayStack class. import…
A: Answer: We have done complete your code and also attached the code and coed screenshot and output…
Q: How can we stop a central processing unit from squandering cycles by processing a huge number of…
A: When a CPU is squandering cycles, it means that it is spending a significant amount of time and…
Q: What options do I have for backing up my Windows 10 installation, and what are the biggest benefits?
A: There are several options available for backing up a Windows 10 installation, including: File…
Q: A key team member should be named in system development. Is it feasible for the engineers and other…
A: Your answer is given below as you required.
Q: What are common system development methods? Examine each method's pros and cons.
A: The answer to the question is given below:
Q: This is due to the exponential growth in computing power over the last several decades. How can we…
A: Given: Since their invention, computers have shown to be dependable, but they are also pervasive; we…
Q: Please explain the pros and cons of integrating a gateway into your current network.
A: A gateway serves as a network's entrance and exit point. Every data packet must travel through a…
Q: Think about the challenges you'll have as you build the framework, and then evaluate the problems…
A: Introduction: As technology continues to evolve, the need for efficient and effective management of…
Q: However the OSI model requires more layers than are present in the vast majority of current computer…
A: Your answer is given below.
Q: You are a consultant at a major beverage company right now. Include a conversation with the firm…
A: Introduction: As a consultant at a major beverage company, I understand the importance of having a…
Q: Where are Honey Pots commonly deployed? (Select all that apply.) a. In a SAN. b. In a WAN. c. In an…
A: Introduction of Honeypots: A honeypot is a decoy system designed to attract potential attackers and…
Q: In the context of software updates, what do the phrases "slipstream upgrade," "patch," "release,"…
A: Repairs: System upkeep helps users and businesses. It involves updating documentation, user…
Q: What software testing and development tools and technologies are available? Provide examples.
A: Mission-critical systems can't afford bugs or performance issues, hence software testing is a…
Q: Learn the ins and outs of the various forms of virtualization and articulate their implications…
A: Answer is
Q: Is there a predetermined sequence of events that must occur before a website may be launched? Show…
A: Software development:- Software development is the process of creating, designing, testing,…
Q: How can one learn about mice in a variety of settings? What is the precise sequence of events? To…
A: To learn about mice in a variety of settings, one could follow a sequence of steps like the…
Q: Understanding the differences between encoding and encrypting data is crucial.
A: Your answer is given below.
Q: Making the switch from on-premises networks to the cloud has several benefits.
A: Cloud computing is on-demand access, via the internet, to computing resources—applications, servers…
Q: What heuristics can you use to improve your system design in order to achieve this?
A: Improving system design is a complex task that involves a combination of skills and techniques. Here…
Q: Add statement here to compute ((z1-z2).(z3/z4))/(z4/z3) and print the result Please use C++ coding
A: Introduction C++ Programming: C++ is a programming language that allows you to write instructions in…
Q: All of a business' electronic papers don't have to be encrypted, although it's a good idea.
A: Data encryption's benefits are becoming important due to data breaches, threats, and assaults.…
Q: Using a computer with both subsystems and logical divisions is helpful. Some of these advantages are…
A: Introduction Computer systems are complex machines, composed of both hardware and software…
Q: A "distributed denial of service attack" is what it's termed, and a single individual might be…
A: Introduction: What exactly is a distributed denial-of-service assault, and how is it possible for a…
Q: In what ways do educational institutions use computer networks? As compared to similar types, what…
A: Introduction Computer network: A computer network is a collection of interconnected computers and…
Q: SSL supports what kinds of protocols? Is a secure session different from a secure connection??
A: The Secure Sockets Layer (SSL) protocol is compatible with a variety of protocols, such as HTTP,…
Q: Download the sample Ratings.txt file from NUoodle and put it in the same directory as numbers.txt…
A: The C++ code is given below with output screenshot A sampleRatings.txt file is taken as example for…
Q: What is "complete and consistent"
A: The requirement analysis step of the software development process is very important since the end…
Q: virtualization in application server virtualization in file server
A: Virtualization means making a use of system with using any ohysical devices. In simple term we can…
Q: Why are microcontrollers used in embedded systems on such a widespread basis?
A: Given: Why are microcontrollers employed in embedded applications on such a widespread scale? A…
Q: The 'type' of a variable isn't the only thing that has to be specified when defining it. To…
A: In certain C programmes, we do not specify storage classes because they have default values. For a…
Q: Think about the benefits and drawbacks of using wireless technology. Give the network a choice of no…
A: Benefits of wireless technology Drawbacks of wireless technology Mobility Interference…
Q: What are common system development methods? Examine each method's pros and cons.
A: "Waterfall development," "scrum development," and "agile software development" are a few examples of…
Q: Detail the advantages that middleware receives from the OS's characteristics. Furthermore, you…
A: Introduction: As the network operating systems already have network functionality built in, they are…
Q: Question 4. Use a for loop to evaluate the series 200 4 Σ(1)", 2n + 1 n=0
A: Step-1: StartStep-2: Declare variable result and assign value 0 Step-3: Start for loop from 0 to 201…
Q: Firewalls protect computer networks and the internet. Explain the sentence using business examples…
A: Firewalls: We must first explain the relevance of network scanning and assessment as a critical…
Q: Assume int[] t = {0, 1, 2, 3, 4, 5}; What is t[6]? undefined, there is an error in this code 4 6…
A: Introduction : An array is a collection of elements of the same data type that are stored in a…
please answer with proper explanation and step by step solution.
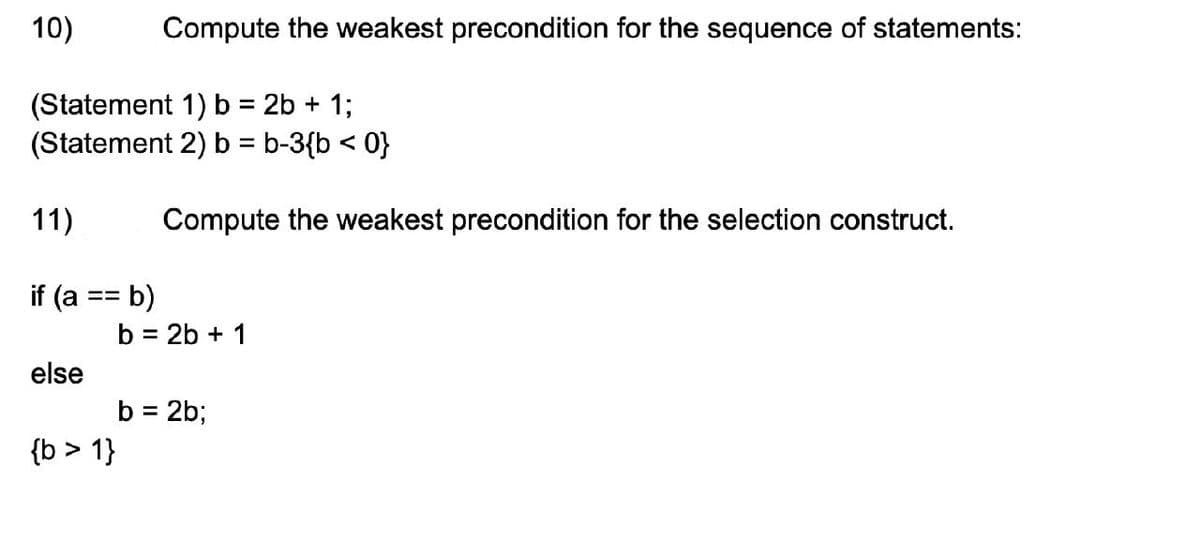
Step by step
Solved in 3 steps

- Book: C++ Programming: From Problem Analysis to Program Design 8th edition, D. S. Malik In C++ In this programming exercise, you use abstract classes and pure virtual functions to design classes to manipulate various types of accounts. For simplicity, assume that the bank offers three types of accounts: savings, checking, and certificate of deposit, as described next. Savings accounts: Suppose that the bank offers two types of savings accounts: one that has no minimum balance and a lower interest rate and another that requires a minimum balance and has a higher interest rate. Checking accounts: Suppose that the bank offers three types of checking accounts: one with a monthly service charge, limited check writing, no minimum balance, and no interest; another with no monthly service charge, a minimum balance requirement, unlimited check writing, and lower interest; and a third with no monthly service charge, a higher minimum requirement, a higher interest rate, and unlimited check…1:- USE " ARITHMETIC OPERATIONS USING OPERATOR OVERLOADING " WHILE SOLVING PROBLEM 2:- AND USE PROVIDE TEMPLATES PROVIDED AT END OF QUESTION. --------------------------------------- Write a C++ program using the operator overloading concept and display its results. Strictly adhere to the Object-Oriented specifications given in the problem statement. All class names, member variable names, and function names should be the same as specified in the problem statement. Consider a class named Complex with the private member variables. Datatype Variable int real int imaginary Include the private member variables and the constructor in the class Complex.Define the following public methods in the class Complex. Method Name Description Complex operator+(Complex a2) This function is used to perform the additional operation ofthe two complex numbers and returns the result. Complex operator-(Complex a2) This function is used to perform the subtraction operation ofthe two complex…2.18 Most programming languages now use the free format pioneered by Algol60, in which state- ments can begin anywhere, but must end, not with the end of a line of text, but with an explicit end symbol, such as a semicolon. By contrast, Python and a few other languages use fixed format, in which statements begin in a particular column and end at the end of the line of code, unless continuation marks are provided. Discuss the effect of fixed or free format on readability, writability, and security.
- (5) Discrete structure: Solve it on urgent basis please! Question # 5 : Express the negations of each of these statements so that all negation symbols immediately precede predicates. a) ∀x∃y∀zT (x, y, z) b) ∀x∃yP(x, y)∨∀x∃yQ(x, y) c) ∀x∃y(P(x, y)∧∃zR(x, y, z)) d) ∀x∃y(P(x, y)→Q(x, y))5. State whether the following statements are TRUE or FALSE (PS: No explanation is needed and very optional)(a) One of the striking features of object-oriented programming is the division of programs into objects that represent real-world entities.(b) Inheritance means ability to reuse the data values of one object by other objects.(c) Wrapping up of different types into a single unit is known as encapsulation.(d) One problem with OOP is that once a class is created, it can never be changed.(e) Object-oriented programs are executed much faster than conventional programs.**use c++ and use string and vector abstract data types. Use iterators as appropriate. Design and implement an abstract data type called Car. Support the following operations: ability to set make and model, ability to shift gear up or down (assume a max of 6-speed), ability to shift lanes (left or right; assume a max of three lanes), accelerate and decelerate (in units of 5 mph), and display the current state of the car (show the make, model, current gear number, current lane and speed). Also, support operator overloading for a few operators that make sense for a Car object including: =, ==, < and >. Instantiate some Car objects in your main function and take them for a spin.
- Describe how memory allocation is done to objects and also develop a C++ programfor employee class with following attributes such as Employee ID, Employee Name,Designation and Salary. Program should sort and display the list of employees inascending order of their salaries using object as a function argument. (Note:Employee ID must not be inputted by the user i.e., auto incremented.)1.4 An abstraction allows programmers to say more with less in their code. Justify this statement with two examples.Solve the following questions: a)Solve the following postfix expressions i)2 3 + 1 - ii)3 4 - 10 + 7 2 3 * - 9 * /a) Convert the following infix to postfix expressions i)2 * 3 - 5 / 2 + 4 ii)1 * 2 * 3 * 4
- Asymptotic function relationships. Verify each of the following statements by the definitions to see if they are true or false 1. If ?(?) = Θ(?), then ??(?) = Θ(?2 ) 2. If ?(?) = ?(?2 ) and ?(?) = Ω(?(?)), then ?(?) = ?(?2) 3. If ?(?) = ?(0. 5?2 ) and ?(?) = Ω(7?2 + ?????), then ?(?) = Θ(?2 ) 4. If ?(?) = ?(?3 ), then ?(?) = Ω(2?3 ) 5. If ?(?) = Θ(?3 ), then ?(?) = ?(2n )C++ : Defining class Person, class Student, class Teacher and class Graduate. Note that class Student and class Teacher inherits from Person, and class Graduate inherits from Student. Defining two constructors (including a default constructor) for each class. Defining virtual function print() for three classes (person, teacher and graduate), where each has different function body. Writing a main function to test the above definition and run each print function.2.15 The principle of locality maintains that variable declarations should come as close as possible to their use in a program. What language design features promote or discourage this principle? How well do Python, C, C++, and Java promote this principle?

