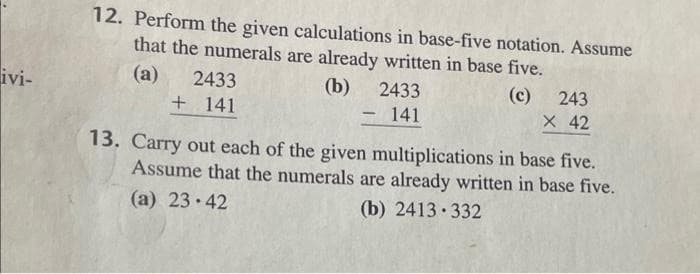
12. Perform the given calculations in base-five notation. Assume that the numerals are already written in base five. (a) 2433 (b) 2433 (c) 243 X 42 + 141 141 -
Q: An airline can reconfigure the seating in an aircraft to respond to demand and to maximise revenue. ...
A: An airline can reconfigure the seating in an aircraft to respond to demand and to maximise revenue. ...
Q: Viewing HTML in web development software is called____. Group of answer choices Code View D...
A: Given :- Viewing HTML in web development software is called____. Group of answer choices Code Vi...
Q: mplementation Part Use appropriate data structure for the given search space and heuristic values. ...
A:
Q: 31. During the implementation phase of a project, the developer revises part of the project that has...
A: Regression testing is a sort of testing that is used to ensure that a software change does not affec...
Q: Create a C++ program that create this output. 1st Output Sample Output: Input: Enter eggs per chi...
A: C++ code to find total number of eggs
Q: Identify the clusters in Figure 7.36 using the center-, contiguity-, and density-based definitions. ...
A: Given :- Identify the clusters in Figure 7.36 using the center-, contiguity-, and density-based defi...
Q: Host A and Host B are connected by a single 2 Mbps (Megabits per second) link that has a propagation...
A: The answer as given below:
Q: What is a wireless network's basic service set configuration? how are they put to use?
A: Let us see the answer:- Introduction As the name implies, a Basic Service Set (BSS) is a network des...
Q: Write a C++ program to input a string and print the length of the largest "block" in the string. A b...
A: Please refer below commented code and screenshot attached : language used is C++: #include <iostr...
Q: Is it possible for a router to direct packets to MAC addresses? If your response is YES, please desc...
A: Yes, a router direct packets to the MAC addresses The router contains forwarding table which contain...
Q: In C++, how you can handle files.
A: Introduction: Files are used to store data on a storage device indefinitely. File handling is a meth...
Q: Which distribution underpins the Ubuntu Linux distribution?
A: Introduction: Ubuntu Linux distribution: It is a free and open-source Linux distribution. It is ...
Q: What is Responsibility Driven Design, and how does it work?
A: Introduction: Object-oriented programming, abbreviated as OOPS, is a programming technique based on ...
Q: Now suppose that you are given two unsorted arrays A and B, containing m and n elements respectively...
A:
Q: 1.01 0.79 0.56 0.34 0.11 -0.5 -0.11 -0.34 -0.56 -0.79 -1.01 F0.0 -0.5 -4 -2 0 -2 2.
A: For 3D plotting in python, by showing you one example using the matplotlib library because as such y...
Q: in C programming Write a main function that declares an array of 100 doubles. In a for loop, assign...
A: #include <stdio.h>#include <stdlib.h> #include <time.h>int main(){double array[10...
Q: Write two versions of each of the string-copy and string-concatenation functions in Fig. 8.14. The f...
A: #include <stdio.h> void copyPointer(char *destination2, char *ptr) { while(*ptr) { ...
Q: What is the principal protocol used for communication between a browser and a web server in the clie...
A: Introduction: the question is about What is the principal protocol used for communication between a...
Q: What is the major distinction between key-value and document stores?
A: Introduction: There are 4 types of NoSQL databases: 1. Document database2. Key-value stores3. Colum...
Q: Give five different examples from each Regular Expression and explain in words what does everyone do...
A: 1. Consider the regular expression (1+0)* (1+0) (1+0) (1+0) The set of strings that satisfy given...
Q: In terms of security, distinguish between symmetric and asymmetric cryptography (key length, securit...
A: Introduction: Key Length is a word that is used to describe the length of a key. The key length in...
Q: It is possible to distinguish two different services provided by database logs. What or who are they...
A: Introduction: Every database management system requires a database log, also known as a transaction ...
Q: Which of the OSI layers is responsible for each of the following: a. allows the tasks to be synchron...
A: Intro Seven layers of OSI network model: Physical layer Data link layer Network layer Transport la...
Q: What are your opinions on employers and/or whistleblowers monitoring Facebook posts (including socia...
A: A whistleblower could be an employee, contractor, or supplier who becomes aware of any illegal activ...
Q: Based on the maturity of the testing process, write a short essay on three testing goals.
A: Using a testing maturity model offers the twin role of detecting existing maturity levels and establ...
Q: Binary search necessitates the sorting of data before it can be used. If we start with unsorted data...
A: Introduction: Binary search requires the array to be sorted before searching an element in the array...
Q: Which of the below command is used to check the logged on users on a Server * O quser O net user O l...
A: Which of the below command is used to check the logged on users on a Server ? a.) quser b.) net use...
Q: What is the name of the modulation technique that is utilized by twisted pair cable computer network...
A: Modulation: Modulation is nothing but a way to convert useful data into digital signals for just tra...
Q: Write a Java program to take a string & a number(N) from the user and print the string made starting...
A: 1) Beow is JAVA Program to read a string and number from user and print the string that starts with ...
Q: Write a Java program to take a string & a number(N) from the user and print the string made starting...
A: Required:- Write a Java program to take a string & a number(N) from the user and print the strin...
Q: Give an example of a situation where an database inde would not be useful and an example of a situat...
A: Although indexes are intended to enhance a database's performance, there are times when they should ...
Q: What exactly is content validity?
A: Introduction: The extent to which the items on a test are reasonably reflective of the full area the...
Q: Which email protocol enables an email client to download emails to a local computer? a. IMAP4; b....
A: Intro Option C (TCP)A Transmission Control Protocol (TCP) is used for maintaining and establishing n...
Q: Write a Python program to convert JSON data to Python object. import json json_obj = '{ "Name":...
A: Here I written python program for given problem. I hope you like it.
Q: Identify and explain two of the expected effects of virtualization on operating systems
A: Virtualization on the operating systems - Based on the operating system Virtualization is a feature ...
Q: main Duties (testing, documentation and communication) Skills and toolbox Mobile devices Virtual mac...
A: NOTE :- As per our guidelines we are supposed to answer only one question. Kindly repost other quest...
Q: Data warehousing services delivered using a cloud-based architecture provide several benefits.
A: Introduction What is cloud computing? Simply put, cloud computing is the delivery of computing serv...
Q: create a TimeLine animation that shows a line with one end at the centre of a 300 * 300 stage and th...
A: protected void updateCSS() { final long now = System.nanoTime(); final double diffMillisSinceL...
Q: What is the CPU time if the programme executes 500 instructions at 5 cycles each instruction and the...
A: Intro CPU time: The formula for computing the CPU time is provided below:
Q: C++ PROGRAMMING EXERCISE Given an array of integers below, write a program to reverse all the elemen...
A: Algorithm: Start Read array size n Read n numbers and store them in an array named a Iterate throug...
Q: What exactly is database security? What are two methods for keeping a database safe?
A: Introduction: What exactly is database security? What are two methods for keeping a database safe?
Q: supplies the reasoning and understanding behind the actions implemented in training.
A: Given :- _______ supplies the reasoning and understanding behind the actions implemented in training...
Q: When comparing a static stack to a dynamic stack, what is the difference?
A: A static stack has a defined size at the start of the program, thus if you coded your stack to have ...
Q: 2 Using Divide and Conquer technique, sort the given number using quick sort 9,1,3,5,2,6,4
A: Given:
Q: What are the rules of business? What value do they have for a database designer?
A: Introduction: Business rules play a critical role in database design and are critical to the databas...
Q: Why would a system designer want Unicode to be the default character set for a new system? What reas...
A: Intro Reasons for the system designer to use Unicode as default character set: Operating systems s...
Q: Software Engineering QUESTION Create a Use Case Description, Sequence Diagram, and Activity Diagram ...
A: Let's see the solution in the next steps
Q: A gate has a standard key pad with the digits 0 through 9. How many possible code combinations are t...
A: A standard keyboard consists of the following keys are Alphabetical keys, Numeric Keys, Punctuation ...
Q: Oracle SQL Packages Create a stored procedure to display top three of cheapest course in terms of ...
A: To return the smallest value of the selected column we use the MIN( ) function. And to return the ma...
Q: clared a dynamic array after the number of records is known. After data is read, perform the analysi...
A: In the below code the input data is stored in a Data.csv file as per the below example. ID,Income,Ho...
Trending now
This is a popular solution!
Step by step
Solved in 2 steps

- Please please don't copy Computer Science for BCH (16,12). when input is (0, 4, 14, 14, 4, 4, 15, 2, 4, 2, 15, 13), what are the check digits?32) Let a = 1.0 × 29, b = − 1.0 × 29 and c = 1.0 × 21. Using the floating-point model described in the text (the representation uses a 14-bit format, 5 bits for the exponent with a bias of 15, a normalized mantissa of 8 bits, and a single sign bit for the number), perform the following calculations, paying close attention to the order of operations. What can you say about the algebraic properties of floating-point arithmetic in our finite model? Do you think this algebraic anomaly holds under multiplication as well as addition? b + (a + c) = (b + a) + c = Show Steps PleaseExplain how to multiply two complex numbers, a + ib and c+ id, using just three multiplications of real numbers, where a, b, c, and d are real numbers and I (= v-1) is an imaginary number. The algorithm must accept the inputs a, b, c, and d and create the real component ac – bd and the imaginary component ad + bc separately.
- Addition, subtraction, and multiplication are binary operations on _________ I. Z II. Q III. R IV. N a. IV and I only b. II and III only c. I and II only d. I, II, and III17(2) Perform the following arithmetic operation: 62C16 / 12E16 = ____________1. Write down the mathematical notation for fixed point representationand floating representation and also explain each term. 2. Consider the following machine number in 64 bit and Precisely represent the above machine number in decimal digits. 0 10000000011 1011100100010000000000000000000000000000000000000000
- As necessary, the blank should be filled up.Leibniz's invention allowed for addition, subtraction, multiplication, and division.Work on the following questions: 1. Convert the following decimal numbers into binary (show the steps): i) 75, ii) 64, iii) 1023Answer the given question with a proper explanation and step-by-step solution. Convert the following numbers into binary numbers and preform the operations. Show all your working details? a) 10710 + (- 210) b) 13310 - 9010 c) 1110 x 510
- 1. Prepare the following floating-point number in a 32-bit format. 0.0000000000000019852. Elaborate the requirements to compute 100102 x 110012 using Booth’s algorithm based on the following aspects. (i) Arithmetic operations. (ii) Registers.18.Convert 4 square miles to square inches.x Relevant conversions: 1 mile = 5,280 feet, 1 foot = 12 inchesx Express the result in decimal and also in scientific notation.19.Convert 3 square hectometers to square micrometersx Required conversions: use table of metric prefixes.x Decide if it is preferable to display in scientific notation.20.Convert 8 square inches to square nanometersx Necessary conversions: 1 inch = 2.54 cm and table of prefixesmetric.x Decide if it is preferable to display in scientific notation.Q 3 Using the floating point format described in problem 5.19 of your text, convert the binary number -10011101001100.101001011 to the floating point representation. Please show work clearly Full explain this question and text typing work only thanks

