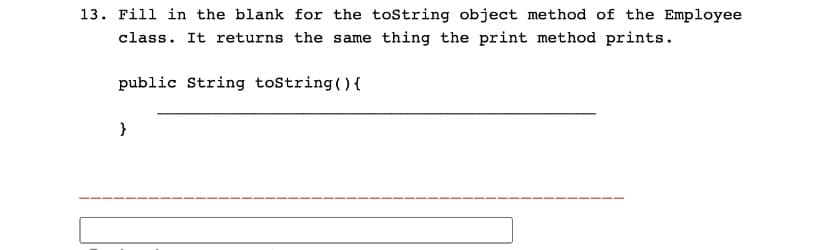
13. Fill in the blank for the toString object method of the Employee class. It returns the same thing the print method prints. public String toString() { }
Q: Learn to address common problems with Linux by exploring its documentation.
A: Definition: Linux hardware issues may develop for a variety of reasons. Before attempting a…
Q: Consider the arrangement of learning bridges shown in the following figure: B1 B3 B2 B4 Assuming all…
A: ANSWER:-
Q: Write proper pseudocode for FixHeapNode(A[1,..., n), p) that fixes the subtree rooted at A[p] to be…
A: In pseudo-code programming, all statements depend on each other. The pseudo-code includes while,…
Q: Boat Race Define a class named BoatRace that contains the following information about a Boat Race:…
A: Solution: Given, if __name__ == '__main__': the_race = BoatRace('the_big_one.csv')…
Q: When compared to other disk scheduling algorithms, how risky is the SSTF method?
A: Introduction Shortest Seek Time First: The technique known as SSTF, or Shortest Seek Time First, is…
Q: Which ONE of the following functions is performed by both transport layer protocols of the TCP/IP…
A: A network protocol which refers to the one it is an established set of rules that determine how data…
Q: If we conduct a quick survey among software engineers, we will realize that formal methods are still…
A:
Q: How to perform subnet addressing?
A: Dividing large network into many small networks is called as Subnetting. In the process of subnet…
Q: how do they compare to Influential Access? Please give an illustration. When comparing Direct and…
A: Direct Access: The value is immediately available in this access, thanks to the index. The data…
Q: This section should go over the IT Governance considerations that a company should think about…
A: Introduction: Before doing anything else, it is essential to determine the resources you already…
Q: 3 matalab Using Matlab, Write a script which should return the value of a polynomial p evaluated at…
A: Below I am giving the Matlab script to evaluate a polynomial and then I am going to display the…
Q: Thank you for your reply above. This is what I hace in Visual Studio but I can't (I am not able) to…
A: For running a C code in Visual Studio, follow the below-given steps. A C/C++ Extension can be…
Q: What is the tunneling procedure? What are the three kinds of tunneling protocols?
A: Introduction: In this case, the optimal encoding technique with a high data rate must be found.…
Q: What methods do software designers and developers use?
A: Software development methods are structured approaches to a software development project. Effective…
Q: For any [x] EZ/n and any kEZ, we can define k[x] by k[x] = [x] + [x] + ... + [x] k times where the…
A: The question is to find the multiples of [3] in z/9 and z/8.
Q: The prefix length of an IPv6 address is similar to the broadcast domain subnet mask DNS mask DHCP…
A: The question has been answered in step2
Q: When and why would you use distributed data processing?
A: Distributed data processing: Before talking about the distributed portion of data processing, we…
Q: IJCAI KDD ICDM SDM AAAI NIPS Conference Philip S. Yu Ning Zhong R. Ramakrishnan M. Jordan Author
A: Hello sir
Q: what is the feature that we have in public key cryptography in order to be sure that the digital…
A: Below I have provided a solution for the given question.
Q: define, describe and give an example for web 3.0, blockchain, NFT, crypto currency, and metaverse…
A: Your answer is given below .
Q: Can you explain the pros and cons of storing disk writes in a cache?
A: Disk Caching: Temporarily storing files so users may access them fast. Drive cache improves the time…
Q: In the realm of database management, what would you say are the top three responsibilities?
A: Managing Databases The act of putting information away in a particular location within a database…
Q: What is the maximum theoretical data transfer speed between an IEEE 802.11g rated HP laptop and…
A: IEEE 802.11g-2003 or 802.11g is an amendment to the IEEE 802.11 specification that operates in the…
Q: A database management system (DBMS) is precisely what? Create a list of the pros and drawbacks
A: Introduction Database management system: A database management system(DBMS) is a collection of…
Q: Consumer-oriented tablets are radically altering how organizations store, retrieve, and use…
A: The question has been answered in step2
Q: What are the different Computer Level Hierarchy? Briefly describe each
A: Definition: The combination of many levels that links the computer with the user and facilitates…
Q: Analysis: Q1: There are common attributes and methods between passengers and drivers. What is the…
A: Hello
Q: C++ CODERS! Please complete the lost password function and the sign in account function. Will rate,…
A: THE ALGORITHM OF THR CODE:- 1. Start.2. Initialize class Accounts.3. Create function getStd() and…
Q: Explain in detail how the ICT department can quickly and effectively provision software including…
A: The workings of antiviral software Antivirus software often operates in the background, checking…
Q: Question: Building a Multi-Table DB with Relationships (Include the tables creation query, I will…
A: Hello
Q: To what extent is this true? Suppose a TCP connection's most recent SampleRTT was 1 second. The…
A: Your answer is given below.
Q: Explain briefly how people can charge their smartphones via USB ports.
A: INTRODUCTION: These days, USB ports are built to withstand a more considerable current demand than…
Q: Explain what is the role of network administrator?
A: Network Administration:- A network administrator is a person responsible for the maintenance,…
Q: paring the R2 of Simple Linear Programming and the R2 of Multiple Linear Programming, pros and cons,…
A: Introduction: The best potentialactivity of productive resources will beearned with the employment…
Q: Explain what is Kerberos?
A: Definition: Kerberos provides a centralised authentication server whose function is to authenticate…
Q: A7 x 5 block with even parity checks is received as 0 0 0 0 0 0000 0 1 0 0 0 0 1 1 1 1000 0 0 1 a)…
A: Hello student
Q: Learn to address common problems with Linux by exploring its documentation.
A: Definition: Linux hardware issues may develop for a variety of reasons. Before attempting a…
Q: Given a binary search tree built to store data records, to determine the height of a subtree rooted…
A: Tree traversal means visiting nodes in some specific manner.
Q: This section should go over the IT Governance considerations that a company should think about…
A: Introduction: Identifying your resources is the first step in determining the capacity requirement.…
Q: Q2) Please design a circuit that has a red led and a blue led and simulates a police light (i.e: The…
A:
Q: In most cases, you can copy data either from one register to another or vice versa. The Memory…
A: Register:- The register is defined as the smallest set of data holding. It is part of the computer…
Q: 5. Fill out the spaces. (a) Low frequencies correspond to the highly) varying components of an…
A: (a) Low frequencies corresponds to the slowly varying components in an image. Explaination:-…
Q: Pipe data formatting is often accomplished with the help of filtering programs like sed and awk. So,…
A: commands using seed and ask Filtering text manipulation commands that use pipes can be accomplished…
Q: Explain how frames are constructed in HTML document.
A: Introduction Programming. Programming is the process of writing a set of instructions that inform…
Q: Must be in C++ and cannot come from any online source. Please include all requested parts in…
A: Solution: Given, Create a class named Employee that has the following member variables: name - a…
Q: What is a ForkJoinTask defined as? What are the differences between RecursiveAction and…
A: ForkJoinTask is a thread entity which is very lightweight than normal threads and it begins…
Q: While gathering evidence during the containment process is important, in your own words explain why…
A: Before an incident overwhelms resources or causes more harm, containment is crucial. Containment is…
Q: What are the computer laws/principles involved in computer architecture or computer organization?…
A: Computer Architecture and Organization Tutorial The Computer Organization and Architecture Tutorial…
Q: Consider the following Python code: ###### 1 2 "She is year + str(x) y = 12/x ##### #F E Ett #…
A: Q1 Second option: First line legal and second line is illegal is true This is because first line…
Q: Explain what is the role of network administrator?
A: Dear Student, The answer to your question is given below -
Step by step
Solved in 4 steps with 1 images

- Create a class Animal Create a class Cat, and a class Dog, and a class Bearded Dragon which extend Animal. Add to your Animal class: Member: name Methods: Public Animal (String name) //constructor public void makes Sound () with the implementation printing out a generic animal sound. Next, override (add) the makes Sound() method to your Cat and Dog class, with the implementation specific to each animal (i.e, cat says purr..). Do not override the makesSound() for your Dragon (bearded dragons don't make sounds!) Note, you'll also need a constructor in each of your subclasses which calls super(name) to initialize the common 'name' member of Animal. Next (in your test harness) create a List of different Animals ( a couple cats, a dog, a dragon... ) and add these Animals to your list. Iterate through your list & call makeSound on each. (you should observe the makeSound method called will be: cat -> from Cat class, dog-> from Dog class, bearded Dragon -> from Animal class ) EC:…Class student inherits from superclass Person. Which assignment is legal? a) Student s = new Person(); b) Person p = new Student(); c) Student s = new Student(); d) Person p = new Person();*using java* Create a class AnimalCreate a class Cat, and a class Dog, and a class Bearded Dragon which extend Animal. Add to your Animal class: Member: name Methods: Public Animal(String name) //constructor public void makesSound()with the implementation printing out a generic animal sound. Next, override (add) the makesSound()method to your Cat and Dog class, with the implementation specific to each animal (i.e, cat says purr..). Do not override the makesSound() for your Dragon (bearded dragons don’t make sounds!)Note, you’ll also need a constructor in each of your subclasses which calls super(name) to initialize the common ‘name’ member of Animal. --- Next (in your test harness) create a List of different Animals ( a couple cats, a dog, a dragon... ) and add these Animals to your list. Iterate through your list & call makeSound on each. ( you should observe the implementation of the makeSound() method called will be: cat -> from Cat class, dog-> from Dog class,…
- Java- Suppose that Vehicle is a class and Car is a new class that extends Vehicle. Write a description of which kind of assignments are permitted between Car and Vehicle variables.If A and B are reference variables to the objects of MyClass, what can we say aboutthis comparison? (Pick all true statements.)if (A.equals(B)) {...} A. It is identity test.B. It checks whether two objects are equal if the equals method is overridden in MyClass.C. None is correct.D. It checks whether both are referring to the same object if the equals method is not overriddenin MyClass.Answer the given question with a proper explanation and step-by-step solution. The base class Pet has protected fields petName, and petAge. The derived class Cat extends the Pet class and includes a private field for catBreed. Complete main() to: create a generic pet and print information using printInfo(). create a Cat pet, use printInfo() to print information, and add a statement to print the cat's breed using the getBreed() method.
- Create an interface Wheel with methods setWheels (int c) and getWheels () and a class Vehicle with abstract methods getColor () and getBrand (). Now, create a concrete class Taxi with additional method setDriver (String name) that inherits both Wheel and Vehicle. (Note: Concrete classes don’t have any abstract method)Suppose Child is a class derived from Parent. To call a method in Parent from Child, we use: a) super b) private c) public d) protectedPLZ help with the following IN JAVA When defining an inner class to be a helper class for an outer class, the inner classes access should be marked as: Public Private Protected Package access
- CLASS AND OBJECT WRITE! 1.) Write the main class of the given class Animal below that set the number of legs to “4” and display (get) the number of legs. class Animal { private int numberOfLegs; public void setNumberOfLegs(int numberOfLegs) { this.numberOfLegs = numberOfLegs; } public int getNumberOfLegs() { return numberOfLegs; } }Assume an Animal class defines a public eat method and a Dog class derived fromthe Animal class defines a different public eat method. And assume thedeclaration:Animal[] animals = {new Animal(), new Dog("Collie", "brown")};Indicate which eat method is invoked by each of the following statements, and explainwhy.animals[0].eat();animals[1].eat();Given the following class, I need help writing a constructor that initializes all instance variables using appropriate parameters. I need to make sure it enforces the preconditions public class BrowserTab {private String title;private int id;/*** Creates a BrowserTab* @precondition title != null && id >= 0*/}



