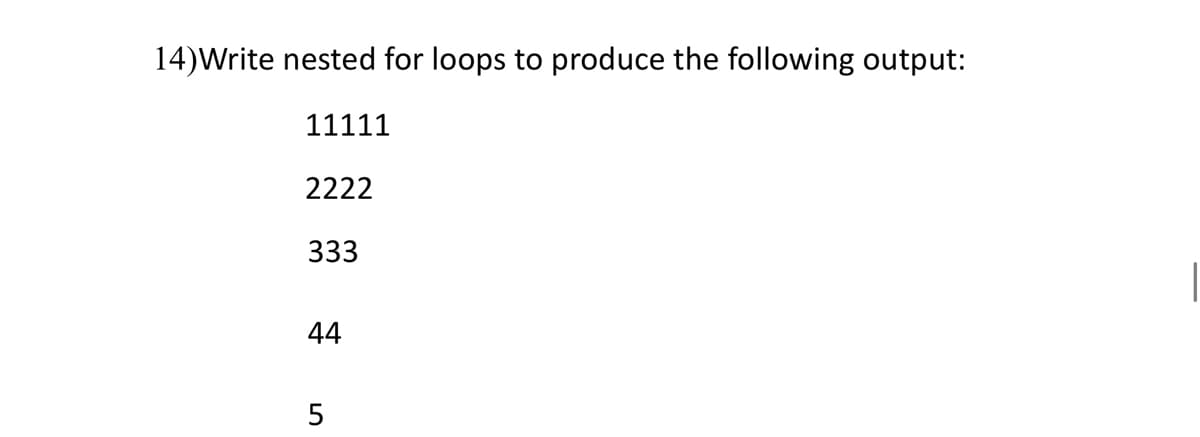
14)Write nested for loops to produce the following output: 11111 2222 333 44 5
Q: Describe the different components of an information system. What role does the individual play in…
A: Intro These components interact to create information systems. Also, an academic education of…
Q: Describe the systems analyst's function in the creation of information systems.
A: An IT professional who is specialized in analyzing, designing and implementing information systems…
Q: Wireless networks' inherent features generate a number of challenges. Describe three of these…
A: Introduction: The following are some of the challenges that users of wireless networks face:
Q: What are the indicators that a software development project is going to fail? Why is an explanation…
A: Some of the warning indications that a software project is about to fail are as follows: The market…
Q: What are the differences between the incremental and synoptic approaches?
A: We need to mention the differences between the incremental and synoptic approaches.
Q: What are the two most typical kinds of files that people use? What distinguishes these two file…
A: File management system: Basically, A file management system is used, for file management or…
Q: When they are operational, computers generate a significant amount of heat. Learn to differentiate…
A: Introduction: To work, all computers require power, and certain computer components demand more…
Q: Compare and contrast top-down versus bottom-up database design approaches.
A: Data model designing approach –In the data model designing, the data model to be developed is…
Q: What are the risks associated with resume screening programmes? How does resume screening, as it…
A: Introduction: The following are the risks linked with resume screening programmes:
Q: Does analysis and design of object-oriented programming allow for the specification of coupling and…
A: Introduction: "Coupling" refers to the connections that exist between modules, whereas "cohesion"…
Q: There are two categories of creatures that may be found in computing: viruses and worms.
A: Inspection" Human viruses that propagate from person to person are named after computer viruses. A…
Q: What's the distinction between computer organization and computer architecture?
A: Solution: Difference between Computer Organisation and Computer Architecture The study of the…
Q: Explain how the usage of paging causes space and time overheads, and how the Translation Lookaside…
A: Intro Paging: Paging is a memory the executive's plot that wipes out the requirement for touching a…
Q: Define Software engineering and examine the importance of applying software engineering concepts to…
A: Lets see the solution in the next steps
Q: List and describe the approaches used to improve software quality.
A: 1. Test early and Test often with Automation2. Implement quality controls from the beginning3.…
Q: Identify a past technology that has influenced current inventions and technologies. Describe how the…
A: Introduction: The majority of inventions have been created in the previous one hundred years. People…
Q: There is a property on a Label control that may be used to change the way that the text that is…
A: Solution: Border Style, Font, Text Align, and other characteristics of the Label control may be…
Q: "Should information systems be created with societal security in mind, as well as the needs of the…
A: Introduction: It is essential to take into consideration the security element of an information…
Q: Q3/estimate the results when you execute the following code: y-l Z=1 tl=x+y*z
A: I have provided PYTHON CODE along with CODE SCREENSHOT and OUTPUT-----
Q: What is the main function of a firewall system?
A: The primary purpose of a firewall system: A firewall is basically the boundary that sits between a…
Q: Determine if the information system you've selected has functional or non-functional requirements,…
A: Information system: A formal, sociotechnical, organisational system intended to gather, process,…
Q: When it comes to software development, what is prototyping?
A: Introduction: "Prototyping" is a term used in software development.
Q: For the sake of this illustration, let's pretend that there is a database for an airline that uses…
A: Introduction: A database is a collection of structured data that has been logically arranged and…
Q: When developing a system, why is it critical to use systems analysis and design methodologies? The…
A: The question has been answered in step2
Q: Q2: A) Apply DeMorgan's theorems for the following expression :- ABCD+E+F+GH B) Draw the logic gates…
A: Demorgan's theorem: (A+B)' = A'B' (AB)' = A'+B' Gates used in expression: A' : Not gate A+B : Or…
Q: What are the four distinct design concerns in a multiprocessor operating system?
A: Introduction: In a multiprocessor system, even if one processor fails, the system will not come to a…
Q: What exactly is the background of the field of computer science?
A: Computer science means it is branch which deals with the study of computers by applying the…
Q: What are the distinctions between cloud security platforms such as ScoutSuite, Pacu, and Powler? How…
A: Introduction: Cloud-based systems and the data they store are protected by a combination of a wide…
Q: C program only Hi! The 'divide' function should apply recursion. Please fix the code below.
A: In this question, a code is given in C language which divides the two numbers and we have to…
Q: We will look at four possible logical security measures that, if adopted, would increase the amount…
A: Introduction: Logical security measures limit user access and prevent unwanted access. Operating…
Q: The following is a list of the many different entry points you may use to access your files. It has…
A: Answer: The following list outlines the benefits that come with viewing specified files both as a…
Q: the study of computers Computer usage in daily life has what effects on people, families, and…
A: Study of computers: Computer science is the theoretical and practical study of computers and…
Q: The files on your computer may be accessed in a number of different ways. In each scenario, what are…
A: Introduction: The following are the primary methods for accessing files: The process of organizing…
Q: Based on Open Foam CFD - why grid independence needs to be justified for Every Reynolds number?
A:
Q: TASM/Assembly Language Develop and execute a program to read 10 characters from keyboard…
A: We need to write an assembly code to read 10 characters from keyboard.
Q: What is the distinction between Negative Patterns and Rare Patterns? Can you give an example of each…
A: Intro Rare patterns and negative patterns are the terms used to describe these phenomena. In this…
Q: How can secondary clustering in quadratic probing be resolved?
A: Intro The main disadvantage of primary clustering (linear probing) is cluster formation, a greater…
Q: What exactly is the wi-fi evildirect assault technique, and how does it work?
A: The solution to the given question: EXPLANATION METHOD OF ATTACK USING Wi-Fi evil direct You can…
Q: What is the objective of the Internet Control Message Protocol, or ICMP, and how does it work?
A: Network devices communicate data transport concerns using the Internet Control Message Protocol,…
Q: Why is it important for a systems analyst to be able to translate? What organisations might be…
A: Introduction: A systems analyst's job is to act as a translator for individuals who are not…
Q: If the device is operational and ready to transmit, the processor requests the transfer of data due…
A: Dear learner , hope you are doing well , I will try my best to answer this question. Thank You!!
Q: Explain how access log data may be utilised to determine the true identity of a computer impostor…
A: Introduction: In the control log, the impersonator noticed the following:
Q: How long has the field of computer science been around?
A: This makes computing a precise science: Computer scientists use a systematized set of information to…
Q: What four traits do you consider to be the most important when it comes to software development?…
A: Software Development process: A software development process in software engineering is a method for…
Q: It is crucial to have a knowledge of the difference between operational and denotational semantics…
A: Syntax and Semantics: Syntax and semantics are two aspects of programming language research.…
Q: In assembly language, what are some of the rules that are the most often used?
A: Assembly language is a sort of programming language that interacts with a computer's hardware.
Q: What does the phrase "interdependence" mean in the context of system ideas,
A: In this question we have to Understand the term interdependence phrase in context of system ideas.…
Q: nitial values are assigned to the text attributes of Label controls such that those values…
A: Introduction: When you first create the control, the Text property of the Label control will be set…
Q: Create a Java Program 1D array accepts input from user and use address calculation sort
A: Code in java: import java.util.Scanner; public class Ascending { public static void…
Q: Why are SE ethics important for software engineers?
A: Introduction: People make a range of mistakes and behave in disrespectful ways when standards or…
Step by step
Solved in 2 steps with 2 images

- Write a nested for loop that displays the following output:(b) Use a while loop to display the following output. You have to double up the value foreach increment. Declare necessary variables to hold the no and value.No Value--- -------1 0.012 0.023 0.044 0.085 0.16. .. .32 .Q: Write a program which displays the following pattern as an output. 1 22 333 4444 55555 (Hint: using loop
- Complete the code to return the output. q = [17, 25, 42, 35, 47, 45] print( ___ (q)) 17 min count sum [0]Using the starting code, create the following output.#include <stdio.h> int main(){ int a; /* for loop execution */ for ( a = 1; a <= 100; a++){ printf("%d\n",a * a); } return 0; } write a code using while loop that will provide the same output as the code given above.
- Use nested loops that display the following patterns in four separate programs:Use nested loops that display the followingpatterns in four separate programs:python-Write while loop to repeats while user_num ≥ 1. for each loop iteration, divide the user_num by 2, and print user_num.example output with input: 2010.0 5.0 2.5 1.25 0.625 please consider---- If code has infinite loop, system will prevent running the code after few secs and say "Program end never reached." system will not print test case in this scenarioo just been trying forever and need to understand
- After the break statement in (a) is executed in the following loop, which statement is executed? Show the output. After the continue statement in (b) is executed in the following loop, which statement is executed? Show the output.Using nested loop, create a java program that produces the following output: 111 22 3Using the C#, create programs using the do-while loop that will produce the following outputs: abc abc abc abc

