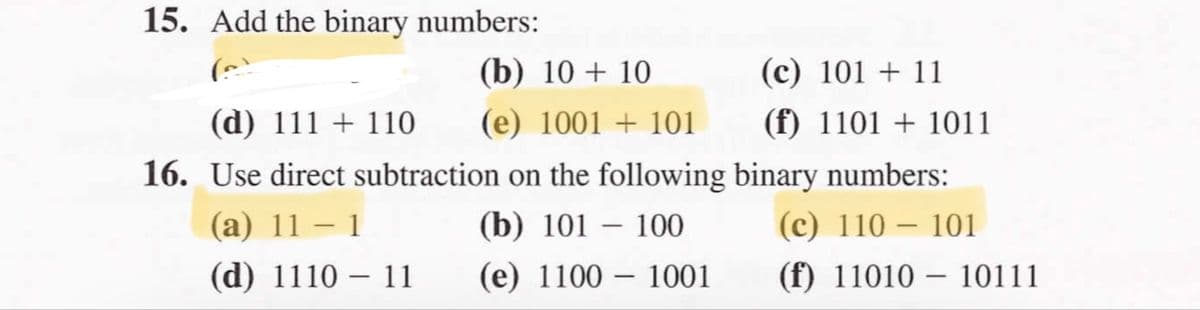
15. Add the binary numbers: (b) 10 + 10 (c) 101 + 11 (d) 111 + 110 (e) 1001 + 101 (f) 1101 + 1011 16. Use direct subtraction on the following binary numbers: (c) 110 – 101 (а) 11 — 1 (b) 101 – 100 (d) 1110 – 11 (e) 1100 – 1001 (f) 11010 – 10111 |
Q: CSS Disadvantages Come in different levels Fragmentation • Lack of security w3c link(same page itsel...
A: Program: disadvantage.html code <html> <title> Disadvantage Html </title> <head...
Q: Why is it necessary to utilize APIS rather than system calls?
A: Introduction: There are four leading causes for this:
Q: Write a program to draw polygon and use glTranslatef command to move this polygon from its location ...
A: polygon and use glTranslatef command
Q: Consider a project and map it both without and with the inclusion of architecture. How it will affec...
A: Introduction: The mapping of strategic needs to architectural choices is defined by software archite...
Q: Which is better, user-level threads or kernel-level threads? What distinguishes user-level and kerne...
A: INTRODUCTION: THREAD: A thread of execution is a minor sequence of programmed instructions that can ...
Q: Make a detailed note on multimedia and its types, as well as typical media for storage and transmiss...
A: Multimedia Multimedia means that computer information can be represented through audio, video, and ...
Q: create buying / selling books online website using php, html, sql, javascript and css
A: 1. Create a Database, Table, and Dump Sample Data 1 CREATE DATABASE allphptricks; To creat...
Q: Why would smart cards be necessary for authentication if magnetic stripe cards are insufficient?
A: Why would smart cards be necessary for authentication if magnetic stripe cards are insufficient?
Q: What exactly is a System Call? How does the operating system handle it?
A: Interfaces between processes and operating systems are provided by system calls. A system call allow...
Q: What techniques may be used to enhance email communication? Kindly offer specific examples.
A: INTRODUCTION: Technics helped in Email communication: Email communication is a fundamental mode of w...
Q: Why is it necessary to utilize APls rather than system calls?
A: Introduction: The primary distinction between an API and a system call is that an API is a collectio...
Q: Write a simple JavaScript program to calculate the average mark and to calculate the grade of a stud...
A: Program: script.js script.js // function for calculateAverageMarkfunction calculateAverageMark(...ar...
Q: Write an algorithm (pseudocode, or java, or python) which takes as input the adjacency matrix of an ...
A: code: def fun(adj): no_edges = [] for i in range(len(adj)): if sum(adj[i])==0: ...
Q: How did the word "spool come to be used to refer to printer output?
A: The term spool is really an abbreviation - it represents synchronous fringe activities on the web. S...
Q: How do you anticipate and prepare for the many cyber security dangers that may occur when developing...
A: Malicious software: Let's start with the most common and widely distributed security threat: malicio...
Q: Each software application is based on a distinct architectural basis. Describe the different archite...
A: There are five different architectural style are available
Q: Write a backtracking algorithm that generates all the combinations of n things chosen r at a time. Y...
A: ALGORITHM:- 1. Take the value of n and r from the user. 2. Pass it to the function that prints the c...
Q: Define the calculated unified device architecture.
A: Let's the solution what is calculated unified device architecture
Q: Where is the object's supertype stored?
A: Introduction: As the process through which subtypes in a hierarchy are linked to their supertypes, i...
Q: Convert an inputted value from the user in centimeters into its equivalent in meters.
A: Algorithm: Step 1 : Start. Step 2 : Read CM. Step 3 : M = CM/100. Step 4 : Print M. Step 5 : Stop.
Q: Thus, what is the ideal encoding scheme that is sufficiently thorough to represent all of the charac...
A: Unicode is a universal character set or a standard that specifies all of the characters required to ...
Q: Consider the following scenario: we have a byte-addressable computer with fully associative mapping,...
A: Mapping in Associative Mode: In associative mapping, the associated memory is used to store informat...
Q: Q1- Show How The Flag Register Is Affected By MOV CX,ABACH MOV CX,553 2H FIND CF,PF,AF,ZF,SF
A: We need to show the contents of flag register for given instructions.
Q: You were tasked with building an integrated interactive solution for computerizing registration and ...
A: Introduction: It means using technology tools in general curriculum areas so that students can apply...
Q: RTP (Real-time Transport Protocol) is a protocol that allows you to send and receive data in real-ti...
A: In the internet protocol the network of which the communication that is having the components of the...
Q: Describe structured, object-oriented, and agile application development methodologies.
A: Object-Oriented methodologies - It is a new system development approach, that encourages and facilit...
Q: m-19 all elements of the array are in range 1 to n and also all elements occur only once except two ...
A: The input will be size and the elements of the array Then we start comparing each element with later...
Q: What operations are possible with queues?
A: Intro Add an element to the end of the queue by using the enqueue command. Remove an element from t...
Q: Is it better to think about linked lists as linear or non-linear data structures?
A: For the given question, we need to understand if we can think of linked lists as linear or non-linea...
Q: Is batch processing a feasible alternative in the modern era? If it is the case, why or why not?
A: Introduction: When computers were first introduced in the 1960s, they were not widely used and did n...
Q: What strategies might be employed to decrease the overhead imposed by page table shadowing?
A: INTRODUCTION: Shadow page table: A shadow page table is a virtual page table contained within a comp...
Q: Mobile networks are absolutely free of wires and cables when it comes to the air interface that link...
A: Introduction: Data processing is another term for data storage. Data processing is the technique of ...
Q: What exactly is a spinner? Find a summary and summarize it.
A: Introduction: A spinner or wheel spinner is a graphical control element that allows the user to eith...
Q: Demonstrate the process of video recording and how it connects to multimedia production.
A: Answer is given below-
Q: What is the difference between event bubbling and event capture?
A: 1) Event bubbling and event capturing are the two concepts of JavaScript. They are two ways of event...
Q: How are data storage methods carried out?
A: Introduction: Data processing is another term for data storage. Data processing is the technique of ...
Q: What was John von Neumann's residential address?
A: Introduction: A single, shared memory for programmed and data, a single bus for memory access, an ar...
Q: 4. What is the purpose of networking software's where instructors and fellow students are communicat...
A: The Answer is in given below steps
Q: In the realm of information technology, LCD stands for Liquid Crystal What does this really mean?
A: Lets see the solution.
Q: How is a cloud service provider's SLA (Service Level Agreement) evaluated?
A: Introduction: SLA specifies the amount of service you anticipate from a vendor, as well as the metri...
Q: Explain client/server architecture, including tiers, cost-benefit analysis, and performance.
A: Introduction: Architecture of client/serverClient/Server Architecture refers to systems that split p...
Q: Q3-IF CS=24F5H AND IP=237AH Find logical address ,physical address, lower and upper range
A: Data given isa s follows:- CS = 24F5H IP = 237AH
Q: COMPLETE SOLUTION Derive the truth table, simplified Boolean function (equation), and draw the logic...
A: The answer of this question is as follows:
Q: How did the word "spool" come to be used to refer to printer output?
A: How did the word "spool" come to be used to refer to printer output?
Q: What happens if you add an entry to a map that uses a key that already exists
A: EXPLANATION: A map is a special kind of collection that stores data in the form of key-value pairs. ...
Q: Computer experts generally believe that increasing the amount of Random Access Memory (RAM) availabl...
A: RAM is also called the main memory and is used to run applications on a system.
Q: Is it feasible to identify software development's four most essential characteristics? Kindly indica...
A: Introduction: IBM Research defines software development as "a collection of computer science activit...
Q: A local area network (LAN), as the name implies, is a kind of networking technology that connects de...
A: Let's see the solution
Q: What precisely are microcomputers searching for?
A: Introduction: Microcomputer: A microcomputer is a compact, relatively affordable computer with a sin...
Q: Explain the notion of polymorphism and how it pertains to software in no more than 250 words
A: The Answer is in given below steps
Trending now
This is a popular solution!
Step by step
Solved in 2 steps with 1 images

- 1.What is the minimum number of binary bits needed to represent each of the following unsigned decimal integers? 4095 65534 42319 2.What is the hexadecimal representation of each of the following binary numbers? 0011 0101 1101 1010 1100 1110 1010 0011 1111 1110 1101 1011 3.What is the binary representation of the following hexadecimal numbers? 0126F9D4 6ACDFA95 F69BDC2A 4.What is the unsigned decimal representation of each of the following hexadecimal integers? 3A 1BF 1001 5.What is the unsigned decimal representation of each of the following hexadecimal integers? 62 4B3 29FSuppose .3A42 base 16 is converted to base 10. What is contributed by the hex digit 3 if the value in decimal of .3A2 base 16 is computed? a. 0.1875 b. 0.0390625 c. 0.00048828125 d. 0.22705078125Suppose .3A42 base 16 is converted to base 10. What is contributed by the hex digit A if the value in decimal of .3A2 base 16 is computed? a. 0.1875b. 0.0390625c. 0.00048828125d. 0.22705078125
- Show Steps Please 5. Compute the Hamming distance of the following code: 0011010010111100 0000011110001111 0010010110101101 0001011010011110 6. Suppose we are given the following subset of codewords, created for a 7-bit memory word with one parity bit: 11100110, 00001000, 10101011, and 11111110. Does this code use even or odd parity? Explain. 7. Given that the ASCII code for A is 1000001, what is the ASCII code for J? b. Given that the EBCDIC code for A is 1100 0001, what is the EBCDIC code for J? 8. Decode the following ASCII message, assuming 7-bit ASCII characters and no parity: 1001010 1001111 1001000 1001110 0100000 1000100 1001111 1000101In an 8-bit binary number, which is the most significant bit (MSB)? What is the decimal representation of each of the following unsigned binary integers? 00110101 b. 10010110 c. 11001100 What is the sum of each pair of binary integers? 10101111 + 11011011 10010111 + 11111111 01110101 + 10101100 Calculate binary 00001101 minus 00000111. How many bits are used by each of the following data types? word doubleword quadword double quadword What is the minimum number of binary bits needed to represent each of the following unsigned decimal integers? 4095 65534 42319 What is the hexadecimal representation of each of the following binary numbers? 0011 0101 1101 1010 1100 1110 1010 0011 1111 1110 1101 1011 What is the binary representation of the following hexadecimal numbers? 0126F9D4 6ACDFA95 F69BDC2A Whatistheunsigneddecimalrepresentationofeachofthefollowinghexadecimalintegers? 3A 1BF 1001…Computer Science Write a program to multiply two 32-bit binary numbers stored starting from 0300H and 0310H respectively. And also store the result starting from 0320H. USING TASM
- CCTT211 Assignment: 1. Normalize the following binary floating-point numbers. Explicitly show the value of the exponent after normalization.a. 0.1011.1 * 26b. 1101.11 * 2-2 2. Convert the following numbers in 32-bit IEEE format.a. 16.25b. -12.75 3. Convert the following decimal integers to sign-and-magnitude with 8-bit allocationa. 45b. -78 4. One method of representing signed numbers in a computer is one’s complement representation. In this representation, to represent a positive number, we store the binary number. To represent a negative number, we apply the one’s comple- ment operation on the number. Store the following decimal integers to one’s complement with 8-bit allocation.a. 63b. -63 Note: For the problems, follow the instructions and provide the answers in the required format. Show your work and any calculations needed to arrive at the final answer.For example: Binary value of character ‘B’ from ASCII table is 01000010Dataword is 1000010 Even Parity Bit is 0 Codeword: 10000100 Even Parity – Complete the following table using Even Parity Character Binary Datawordfrom ASCII table(7-bit value) Parity BitValue TransmittedCodeword ReceivedCodewordat Receiver Check ifthecodewordisrejected t 1010100 10101101 h 1101000 11010000 i 1101001 11010010 s 1110011 11100110What are the mantissa and exponent values if 6.75 is represented in 8-bit binary floating-point representation? a) Mantissa is 1011 and exponent is 101 b) Mantissa is 0011 and exponent is 100 c) Mantissa is 1011 and exponent is 100 d) Mantissa is 0011 and exponent is 101
- QUESTION 1 Which of the following is the ordinary binary representation of 6 5/8? A. 110.11 B. 10.011 C. 110.101 D. 100.1016. Convert the following numbers from unsigned binary notation to decimal notation, and from 6-bit 2's complement notation to decimal notation: i) 110011, ii) 001101, iii) 101101 7. Show how each of the following floating point values would be stored using IEEE-754 single precision (be sure to indicate the sign bit, the exponent, and the significand fields): a. 12.5 b. −1.5 c. 0.75 d. 26.625 8. The following is a representation of a decimal floating value using IEEE-754 single precision. Find out the value in decimal. 0 10000011 10101000000...0The number 12.410 is to be written using the closest 8-bit unsigned binary representation. i.Show, using a table of column weightings, that 1100.01102 represents the decimal value 12.37510. ii.Show, using a table of column weightings, that 1100.01112 represents the decimal value 12.437510. iii.Using your results from (i) and (ii) write down the 8-bit unsigned binary number and its decimal equivalent that gives the best approximation to 12.410. iv.Write the decimal number you wrote down in (iii) as a percentage of 12.4. Write your final answer as a percentage rounded to two decimal places.

