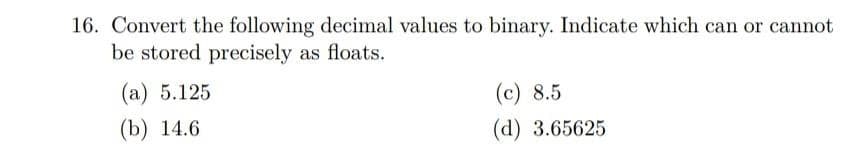
16. Convert the following decimal values to binary. Indicate which can or cannot be stored precisely as floats. (a) 5.125 (b) 14.6 (c) 8.5 (d) 3.65625
Q: What are the primary advantages of utilising a database-driven strategy?
A: Database-driven strategy: A data-driven strategy bases judgments on facts rather than gut feelings.…
Q: As a consequence, the CPU suspends all active processes until the interruption is resolved. This is…
A: The answer may be found here: 1) An interruption is a signal that comes from outside the central…
Q: Which metrics are used while doing maintenance on software?
A: software maintenance: Software maintenance involves upgrading, altering, and changing software to…
Q: Today, all businesses have adopted big data into their information technology systems. In a company…
A: Big Data is an assortment of coordinated, semistructured, and unstructured information assembled by…
Q: World Cup • Download links: Players.csv, Teams.csv • Description: 2010 World Cup data including last…
A: World Cup • Download links: Players.csv, Teams.csv • Description: 2010 World Cup data including last…
Q: To distinguish between the existence of system calls and their absence in a certain operating…
A: A system call is a mechanism that provides the interface between the user process and the operating…
Q: In your own words, explain the differences between EPROM, EEPROM, and Flash Memory.
A: Erasable Programmable Read-Only Memory is what is meant by the acronym EPROM. Electrically Erasable…
Q: What exactly are the components that make up a system?
A: Indeed, A System contains majorly five components software, hardware, database, people and network.…
Q: Discuss three popular RAID storage systems.
A: Answer: Introduction: RAID stands for Redundant Array of Independent Disks. For the system's two or…
Q: Assume three ready-to-run processes in secondary memory. Process 3 has no priority since 1 is most…
A: The function of the operating system that oversees the completion of a variety of different jobs. It…
Q: To begin with, what is a derived property? I'd want to see an example of this. Is it better to store…
A: A derived class is a Java class that inherits properties from its super class. Derived properties…
Q: What's the link between the system life cycle and the system development approach, exactly?
A: A systematic technique known as a system life cycle consists of six phases: Research into the…
Q: Create a list of the different types of legacy systems and the development processes.
A: Systems, technologies, software, and hardware that are outdated or obsolete are referred to as…
Q: The software development life cycle (SDLC) and approaches now have a significant knowledge gap…
A: SDLC is a process, while Agile is a methodology, thus both SDLC versus Agile must be taken into…
Q: Make a clear distinction between the Software Inspection and the Software Testing.
A: Similarity between software testing and software are- Software inspection processes generally call…
Q: Defect elimination, not prevention, is the principle of Cleanroom Software Engineering, which…
A: Introduction: A technique for improving the correctness of present software via engineering is…
Q: What exactly is a wifi evildirect attack, and how does it work? Please refrain from utilising…
A: Introduction: An EvilDirect may be created by setting a rogue GO running on the same channel as a…
Q: The creation of software makes use of a variety of models, with each model having a variable level…
A: Software development uses several models, and each with its own importance. The software development…
Q: The most important tools and procedures employed during the creation of a system are the tools and…
A: Software maintenance examples include: Corrective Maintenance This refers to software fault repair…
Q: Draw an Entity Relationship Diagram (ERD) using Unified Modelling Language (UML) notation according…
A: The solution is :
Q: PCs using Chrome OS need less internal storage space than those running rival desktop operating…
A: Android Wear Chrome is a very quick and lean operating system. Because Chrome solely provides Web…
Q: Where can I get information about the present state of the network management market? Is there a…
A: Introduction: An operating system that has a been specifically designed for a network of computers,…
Q: 1. What is Accessor? a. Explain using a proper java programming example and its output. PS: Please…
A: In step 2, I have provided ANSWER with EXAMPLE JAVA PROGRAM------------------
Q: Please identify four of the four particular requirements addressed by the information management…
A: Introduction: Name any four of the varied demands that the information management system fulfils via…
Q: Is it possible to have a smartphone experience today without using cloud services?
A: Introduction: Mobile cloud storage is a type of cloud storage that may be accessed using mobile…
Q: Explain what is meant by the zone routing protocol for advanced routing ?
A: Advance Routing:- Advance routing is a type of Netcloud service platform. And this is available for…
Q: Defect elimination, not prevention, is the principle of Cleanroom Software Engineering, which…
A: Cleanroom Software Engineering: Errors may be identified earlier in the lifecycle thanks to…
Q: What advantages does object-oriented analysis have in terms of system analysis and design?
A: Intro Object-oriented analysis and design (OOAD) is a mechanical way to deal with examining, and…
Q: Product support is affected by the amount of known flaws in a program at the time of delivery.
A: There are situations when such flaws can continue to be known even though they do not manifest…
Q: What is the system logs' default location?
A: Introduction: We use cloud technology to the access virtual space and the internet. Some people…
Q: Provide an explanation of the various software testing procedures that are used in the software…
A: Here we have given various testing procedures that are used in the software engineering process. You…
Q: What methods are utilized to hijack a session? What can you do to stop yourself from becoming a…
A: Session Hijacking is a kind of attack in which unauthorized access is obtained to authorized session…
Q: few instances of how customized software may be applied (Applications that are produced for people…
A: We must call attention to a few of the applications and customized software. Software that has been…
Q: The synchronisation of shared memory access is provided by multiprocessor systems. Unusual processes…
A: Memory access: Memory access is a term used in computer science to describe the act of reading from…
Q: Write a C++ program, using function, to multiply the array elements by 2.
A: Start. Take the array and pass it to the function. The multiply 2 to each element in the function.…
Q: Does the Internet of Things (IoT) employ deep learning? If so, could you elaborate?
A: Currently, most voice recognition, natural language processing (NLP), and picture identification…
Q: So, what's your take on email? An email is a two-way street. Take note of your understanding. What's…
A: The proper greetings 1 Hi [Name] An suitable salutation for formal email communication is this one.…
Q: hat are some of the best techniques for managing firewalls? Explain.
A: Firewalls acts as a barrier for preventing the entry of traffic that might be intended to do some…
Q: Describe the influence that software evaluation, control, and change methods have had on the amount…
A: INTRODUCTION: Program upkeep is the method of changing, adjusting, and upgrading program to keep up…
Q: a 32-bit microprocessor has 16Kbyte cache. Assume that cache has a line size of four 32 bits words.…
A: It is defined as a Computer's Central Processing Unit (CPU) built on a single Integrated Circuit…
Q: Calculate the waiting time and Turn Around Time (TAT) for each task and the average waiting time and…
A: - : Gantt Chart : - T2 T1 T3 0 5…
Q: Developing a system from scratch has several advantages.
A: The deployment of a custom system refers to the establishment of a system that is developed…
Q: The statement passes a value back to a function's caller.
A: The question has been answered in step2
Q: When it comes to the procurement of software, it is important to make a distinction between…
A: Software Purchase: A software interface with various features is needed in a traditional or…
Q: Real-time operating systems should be introduced before particular instances are discussed in…
A: Real-time system performance: It is often used when a lot of events need to be received and…
Q: Take a look at how system design has changed since the introduction of personal computers and the…
A: The process of creating a system's architecture, components, and interfaces to ensure that the…
Q: So, what exactly do you think of the email? One way or another, an email will get from A to B. Take…
A: This definition states that a mental model is an intuitive perception that a user has or develops…
Q: Recognize and distinguish between the primary tools and methodologies utilized in the creation of…
A: The Answer is given below step.
Q: It is well known that Linux and UNIX are command-line systems. Describe in detail how the command…
A: Introduction: Linux and Unix are PC working frameworks that sudden spike in demand for the CLI. CLI…
Q: Q. write a c++ program that draw a few shapes in the window.
A: I will explain it in details,
Step by step
Solved in 3 steps with 3 images

- 108. A data dictionary doesn't provide information about: a. where data is located b. the size of the disk storage device c. It allows a many-to-many relationship d. It is conceptually simple1. Using Huffman code, we can compress the bits used for saving the characters in a file: Total bits used for saving the character in table 1 is 264 bits using standard ASCII 8 bits for 1 character.Using Huffman code encoding in Table 2, the total bits used is 126 bits.The problem:➢ Input: list of characters such as table 1➢ Output: total bits using Huffman code encoding (table 2)➢ Task: Design an algorithm in pseudocode/code to print the total bits using Huffman codeencoding and write down the Algorithm analysis. The complexity of the algorithm must be inO(n) and proof it!➢ PS: you don’t need to sort the input since the input is already sorted! 2. In a square maze, we can have multiple steps from ‘s’ to reach ‘e’ with one place that can onlybe visited once. Example: Input 3s....#.e#Output 4These are the unique steps:*..*..**.*..**..*.**..*..*.**.**.**.input 4.s...#.##e.#.... output2These are the unique steps:.**...*..**..**..**...*..**..... The problem:➢ Input: an integer followed by…10. Fill in the following addition table for base 3.+ 0 1 201211. Identify the following statements as TRUE OR FALSE. a) BCD stands for Binary Coded Decimal and encodes each digit of a decimal number to an 8-bit binary form. b) Unicode is a 16-bit code, occupying twice the disk space for text as ASCII or EBCDIC would require. c) A signed-magnitude integer representation includes more negative numbers than it does positive ones. d) A byte is 8 bits, but a word may vary in size (16-bits, 32-bits, etc.) from one architecture to another. e)The largest value that a 60-bit unsigned binary integer can represent is (260-1). f) A 2's complement integer representation includes more negative numbers than it does positive ones.
- 9. Show how the text ‘HelloW’ will be stored in computer using 7-bit ASCII standard. You will need to consult the ASCII table. 10. Fill in the following addition table for base 3.File mangament(Contiguous Storage)using c++ and use pointer and char(don't use string): Write a class date (d, m, y), class file (name, size, creation_date) and class directory (name, directory_creation_date, array[files])Write the constuctors, destructors, set, get methods for each classCreate a directory object and fill it with its required data Find the size of the created directory object.
- answer this following question please.. within 1500 words and send me in text file77. ___________ allows uncommitted data to be read a. Read uncommitted b. Serializable c. Repeatable read d. Read committed76. What are the values of the following expressions:2**(3**2) (2**3)**2 2**3**2 a. 64, 512, 64 b. 64, 64, 64 c. 512, 512, 512 d. 512, 64, 512
- Please define the following file extensions: .stl and .gcodeWhat is the output of the following? [ ] data = [88,91,70,15,13] len(data)MCQS the following? 1) .The number of bytes required to store single precision floating point numbers is a) 2 b) 4 c) 8 d) 16 2) The number of bytes required to store the variable "a", where a = [4 , 6 , -8, 13], would be a) 4 b) 8 c) 16 d) 32 e) 64





