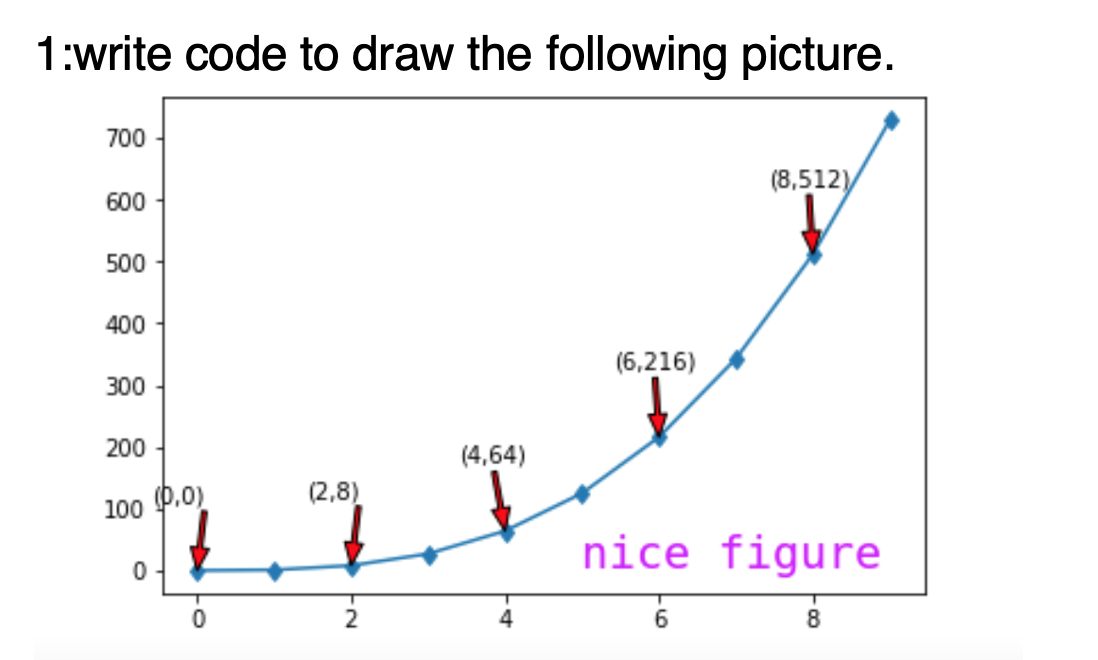
1:write code to draw the following picture. 700 (8,512) 600 500
Q: A static data structure is expected to be used in this application. Then identify a situation when a…
A: Here we have given a brief note on situation when a dynamic data structure might be useful. you can…
Q: take apart assembled" components" means
A: Given:
Q: Discuss TWO (2) device driver duties.
A: About responsibilities of device driver
Q: How many different steps are there in the process of creating a website, beginning to end? Talk to…
A: Creating a website requires a mission, a plan, and the tools and skills to pursue them. Beginners…
Q: 3. Convert the following two complement numbers into their signed decimal equivalents. i. 11111011…
A: First lets understand the process to convert two's complement number to signed decimal: if given : n…
Q: There are 3 algorithms to solve the same problem. Let n = problem size. Suppose that their runtime…
A:
Q: When it comes to modeling software systems, what factors should be taken into consideration?
A: Introduction Software systems are the systems that are used for the intercommunication components…
Q: + 0101 0100 0011 1001 0100 0101 0110 1010
A: The addition of the above to binary numbers will be
Q: It is really necessary to be aware of the purpose of the verification procedure. What makes certain…
A: It is really necessary to be aware of the purpose of the verification procedure. What makes…
Q: Explain in detail what data security is, as well as the three forms of data ownership and the duties…
A: Intro Security types Controls. These protections prevent physical and digital access to essential…
Q: Write a program to add a name to the list box when pressing add command and using the input box to…
A: Answer : 1. Create a Form & add the Listbox and 4 commandButton for Add, Remove, Search &…
Q: In this all-encompassing book, we will discuss a wide range of topics, including DNS records,…
A: Introduction: Globally, the DNS translates IP addresses into domain names that humans can type. Web…
Q: Describe some of the ways in which things have changed throughout the course of history. Interaction…
A: Introduction Human-Computer Interaction (HCI): HCI is review and convenience. It's about…
Q: My understanding of the two-factor authentication idea is lacking at the moment. How much of a…
A: Explanation: A kind of security known as multifactor authentication, sometimes abbreviated as MFA,…
Q: It is necessary to provide a description of the scope of an identifier.
A: The range of computer instructions within which an identifier is regarded as a valid name is known…
Q: Each of the following is not a correct FORTRAN statement Give reasons in each case. a) READ (2,1) K,…
A:
Q: What is clustering and how does it work? Describe any two types of clustering algorithms in a few…
A: Clustering, also known as cluster analysis, is a machine learning algorithm that groups unlabeled…
Q: It is possible that UDP and IP both have the same amount of unreliability. Is there a rationale for…
A: Given: In terms of the UDP/IP debate, each have different levels of unreliability. Because its…
Q: Give the names of three different sorts of servers, each of which a regional bank has the ability to…
A: Here, we'll go through the three basic types of servers that a local bank might utilise. DESCRIPTION…
Q: Getting people to visit a website is one of the most crucial issues that emerges during the…
A: Intro Informing others about the newly created website the user and making the website interesting…
Q: Explain why video data takes and makes use of a bigger amount of storage space than other sorts of…
A: Introduction: The request is to explain why video data requires and consumes more storage space than…
Q: and find where are the time order signals: There can be very few things more important than…
A: The paragraph is about the education.
Q: In terms of computers, what is the distinction between architecture and organisation?
A: Intro the distinction between architecture and organisation
Q: Give an explanation of the distinction between local IDs and global identifiers.
A: The difference between the local ID and global identifiers is given below.
Q: Complete the sentences with the correct preposition: At, of, on, in, to, from, with, for, about, at)…
A: Find the required answer given as below : As per company guidelines we are supposed to answer first…
Q: What is multifactor authentication and how does it work? Is it useful in avoiding the theft of login…
A: Intro Step 1 Multi-factor Authentication (MFA) is an authentication method that requires the user…
Q: Is it feasible to differentiate between the various kinds of authentication with regard to the level…
A: Distinguished: To be different from someone else means to value them. People who stand out are…
Q: IST's final set of criteria for evaluating potentia
A: Introduction: The three key areas of AES evaluation criteria are security, which is obviously the…
Q: What is the distinction between architecture and organisation in computing?
A: Introduction: The most obvious difference between computer architecture and computer organization.…
Q: There is an extensive discussion on DNS records, authoritative and root servers, iterated and…
A: Introduction: Domain Name Servers (DNSs) are the devices that map the hostname to the IP addresses…
Q: What exactly is an interface? What is the difference between a programme block and a module block?
A: Intro To verify a design we write verification module and test bench to check that it meet…
Q: How unreliable is UDP compared to IP in terms of reliability? What are your thoughts? IP address?…
A: Both UDP and IP are unreliable, but in different ways. UDP is more unreliable than IP. IP is a…
Q: use a computer programming language to get access to, and make changes to, data stored in a…
A: To begin, Structured Query Language, or SQL, is a standardized programming language that is used to…
Q: Explain why an operating system may be unable to integrate additional software.
A: Introduction: The most crucial programme that runs on a computer is the operating system.
Q: What does the Ubuntu Server Operating System look like, and how does it vary from other server…
A: Introduction: Before we compare Ubuntu Server to other operating systems, let us look at what is…
Q: `, Give the past form of the following verbs and put them in the sentence: take, arrive, walk, end,…
A: Present tense: It is used to refer something that happens now. It is also called simple present or…
Q: The abbreviation for the Global System for Mobile Communications (GSM) is Global System for Mobile…
A: Introduction: The term for Global System for Mobile Communications (GSM) stands for Global System…
Q: In most retail outlets, barcode scanners are now standard. Provide the common word for this type of…
A: A barcode scanner may be a device accustomed scan barcodes. Most businesses get scanners to be used…
Q: are application is consuming system resources and slowing down the system ?'s Is it possible to keep…
A: You may have to deal with the issue of system resources until the offending programmer is…
Q: 1.Balloon Emporium sells both latex and Mylar balloons. The store owner wants a pro-gram that allows…
A: Answer:-
Q: Explain the distinctions between block and convolutional codes.
A: Answer in step2
Q: In the context of computer systems, how are architecture and organization differentiated from one…
A: Introduction: The design of computers, data storage devices, and networking components that store…
Q: When it comes to the question of self-awareness, what kind of consequences does artificial…
A: When it comes to the question of self-awareness, what kind of consequences does artificial…
Q: Providing a comprehensive breakdown of the evolution of a programming language is requested.
A: The question has been answered in step2
Q: Do you know what a "poison packet attack" is? Use a few of examples to demonstrate your thesis.
A: Introduction: Local Area Network (LAN) ARP Poisoning is a sort of cyber attack used to alter a…
Q: What does the acronym PAID stand for when it comes to referring to the process of creating software?…
A: Answer: Predictable, Atomic, Independent, and Deterministic are the four components that make up the…
Q: What forms of internet connections (cable, DSL, dial-up, ISDN) make use of a local switching centre?
A: Introduction Local switching center: makes packets switch directly from access points to the…
Q: Provide an explanation of how to utilise the arithmetic operators.
A: The four basic arithmetic operators are addition for sum, subtraction for difference, multiplication…
Q: Do you have any previous experience with anything that's been referred to as a "poison packet…
A: Introduction: ARP Poisoning on a Local Area Network (LAN) is a kind of cyber attack that involves…
Q: What is the one situation where preemption is simple and effective?
A: Preemption as used with respect to operating systems means the ability of the operating system to…
Write a python code to draw the following picture.
Step by step
Solved in 2 steps with 2 images

- please find the area of a triangle in 2 ways given the points A, B, and C. Plot the points A= (0,2,6), B= (8,2,2), and C= (5,6,4) in Geogebra and 1): Use the polygon command: Polygon(A,B,C) --this will give the lengths of the 3 segments of the triangle and then give the area of this triangle 2) Using Heron's Formula: A=s(s−a)(s−b)(s−c) where s=a+b+c2 and the sides of the triangle are a,b,c (these are given in the Polygon command in step 1).Modify the code below according to what asking you to do. Please show your new modified code in a picture.Modify the below code according to what is asking you to do. Show your modified code in a picture, please.
- Please modify the given code based on the directions given. #include <iostream> #include <glad/gl.h> #include <GLM/glm.hpp>#include <GLFW/glfw3.h> #include "learnopengl/shader.h" #include "cs4722/x11.h" const auto number_of_vertices = 3; const unsigned int color_loc = 1; const auto b_position = 1; static const auto background_color = cs4722::x11::gray70; auto const verts_per_triangle = 3; glm::vec4 positions0[] = { glm::vec4(-.5, .8, 0, 1), glm::vec4(-.8, .2,0, 1), glm::vec4(-.2, .2, 0, 1)};auto size0 = 4 * 4 * verts_per_triangle;auto offset0 = 0;auto bOffset0 = 0;auto color0 = cs4722::x11::medium_violet_red; glm::vec4 positions1[] = { glm::vec4(.5, .8, 0, 1), glm::vec4(.2, .2,0, 1), glm::vec4(.8, .2, 0, 1)};auto size1 = 4 * 4 * verts_per_triangle;auto offset1 = offset0 + verts_per_triangle;auto bOffset1 = bOffset0 + size0;auto color1 = cs4722::x11::slate_blue; glm::vec4 positions2[] = { glm::vec4(.5, -.2, 0, 1),…Apply conditional formatting to the selected cells so cells with the 10 lowest valuesare formatted with green fill and dark green text in Excel.Print this from c++ Screenshot please

