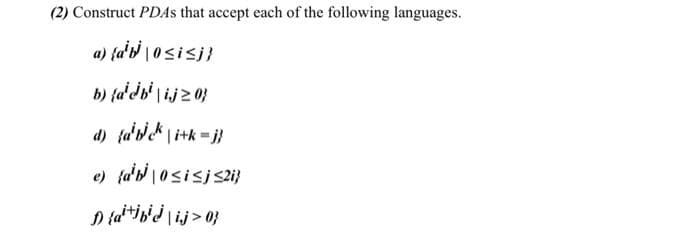
(2) Construct PDAS that accept each of the following languages. a) {d't |0sisi} b) {a'db' l ij2 0} d) fa'dc\i+k=j}
Q: Q2/ Reduce the following system by using Masson's method: G7 Hs G4 G5 G6 G G2 G3 H4 Hs H6 H2 H3 Gs…
A: According to the information given:- We have to reduce the system by using Masson's method.
Q: One of the most often used machine learning techniques is regression. These models are often useful…
A: It is necessary for us to make use of some of the linear regression's applications.
Q: What exactly are multiple fact taBles and how do they work?
A: Introduction: The FACT table contains the metrics, measures, and facts of the business process, and…
Q: One method of categorizing multiprocessor systems is based on how they communicate with one another.
A: What is the meaning of caret artificial intelligence? Answer: For the testing set, Caret offers…
Q: Write a query to display a brand name and the number of products of that brand that are in the…
A: GROUP BY is used to group the rows and count based on brand name ORDER BY is used to sort the result…
Q: Techniques for authenticating users using passwords have a lot of security flaws. What are three…
A: Overview: Password authentication is one of the most frequent ways of Authentication, and the user…
Q: Where do computer organization and computer design diverge from one another, and what are those…
A: Computer organisation is dealing with the behaviour&structure of the computer system as an…
Q: What does the term "routing" mean? What is a distance vector routing algorithm?
A: The process of determining which path traffic should take within a network, between networks, or…
Q: Declare a class named Vehicle as a base class with two data members model (string) and year (int).…
A: Introduction: In this question, we are asked to declare two classes only that are Vehicle(base…
Q: In shared memory architecture, talk about the bootstrap and application processors.
A: Solution : Shared Memory Architecture : A shared-memory multiprocessor is an architecture with a…
Q: In the field of computer science, discuss both the benefits and the drawbacks of using EDL.
A: Introduction: Paper, printing, replication, storage, filing, shipping, and document retrieval are…
Q: (c) What advantages are there to using static testing methods, in addition to dynamic testing?…
A: Static testing is better with finding errors then Dynamic testing. As static testing finds the…
Q: An input image has the size of 140x140 and we use a filter (kernel) with the size of 20x20. We then…
A: The answer is
Q: This code is correct but can you add to the code this instructions: If the father's age is equal to…
A: Your C++ program is given below as you required with an output. Below in source code i'm add to the…
Q: ingle ROM as a KOR and NAND = (X3X2X1X0 ar ress lines (the le put lines (the le
A: The smallest possible dimensions of the ROM is 64k x 16bits. Explanation: Input to ROM – 2 lines…
Q: 1. Create a class named Cat. Declare two (2) empty instance variables: catType (String) and…
A: In this question we have to create a java class and create some constructor methods which will set…
Q: Assuming the following C++ variable declaration statement int i = 2021, *pi = &i, **ppi = π leads…
A: Value of ppi=0x2024; value of **ppi=2021;
Q: Make a list of the pros and cons of the different operating systems available
A: 1. Windows Pros: Lots of hardware choices ranging from budget right through to crazy powerful. Lots…
Q: Assuming the following C++ variable declaration statement int i = 2021, *pi &i, **ppi π %3D %3D…
A: The value of ppi is 0x2024 and the value of **ppi is 2021. Explanation: #include <iostream>…
Q: How is the order of characteristics in a result table altered?
A: Intro In Database, each and every table have some attribute and they are listed in the table with…
Q: Question 8 V = {1, 2, 3, 4, 5, 6}, Consider the following graphs, each with vertex set G = (V, E),…
A: Degree of vertices are- 1 -> 1 2 -> 3 3 -> 2 4 -> 1 5 -> 3 6…
Q: Consider a B+tree in which the maximum number of keys in a node is 5. What is the minimum number of…
A: Answer: 2
Q: Which of these two scheduling approaches—preemptive or non-preemptive—requires more time and…
A: Non-preemptive scheduling assigns the CPU to a process until it terminates or enters the waiting…
Q: social networking software in the context of computer
A: social networking software in the context of computer science defined as online community of…
Q: The system's organisational and managerial components should be familiar to yo
A: Administrative: The information system's organizational, administrative, and technological aspects:…
Q: Indices can speed up query processing, but it's usually a terrible idea to index every a attribute,…
A: The answer is
Q: How will you check the equality of two integer variables without using the arithmetic comparison…
A: By comparing 2 integers using > and < symbols and if one number is greater or less than the…
Q: Iterated and non-iterated queries; authoritative and root servers; and DNS records are included in…
A: Domain names are translated into IP addresses via DNS. This is done by looking up the DNS records…
Q: Q.3): Which of the following names for string variables are correct? 1) AGE$ 2) COLLEGE 3) $sum 4)…
A: let us see the answer:- The correct answer is:- 2) College
Q: In your own words, explain the importance of operating systems and whether or not it is possible to…
A: According to the facts provided, we must determine the importance of operating systems and if it is…
Q: Operators are classified into four many types, these are: O Mathematical and String Operators.…
A: Introduction:
Q: The oHowing two statenments will generate two strings with the same content: std::string strl =…
A: False
Q: The next parts of this article discuss network applications and application layer protocols in…
A: The next parts of this article go into network applications and application layer protocols in…
Q: Please answer the question below. Your answer must be at least 2paragraphs and the example kindly…
A: Java Heap: A heap is a block of memory that is shared by all threads in Java. The array and all…
Q: Pleas help me to solve this sample code Please help me to solve this I post this three-time and no…
A: Program: with Ada.Text_IO; procedure jDoodle is--jDoodle is the main subprogram…
Q: What are the two ways in which IP security may be implemented?
A: IPsec is an abbreviation for Internet Protocol Security. It is a series of protocols that guarantees…
Q: Read This Carefully!! (For your eyes-only) Your task, should you choose to accept it, is to design…
A: //CODE import java.util.*;public class Main{ public static boolean isALetter(char letter){…
Q: When does a compiler build a default constructor, and what is its purpose
A: the term default constructor can allude to a constructor that is naturally created by the compiler…
Q: To solve what kinds of issues does a simultaneous multithreading design need an operating system?
A: Answer:
Q: What is the bug in the buildHeap code below, assuming the percolateDown method from the slides we…
A: Building a heap in linear time- A heap can be built in linear time from an arbitrarily sorted array.…
Q: In Data Acquisition Systems : Data to be measured is digitized by an Digital -to- Analog Converter…
A: Lets see the solution in the next steps
Q: in the similar notation. they have, however,a completely different meaning. with the aid of…
A:
Q: What exactly does it mean to explain caret's artificial intelligence?
A: What is the meaning of caret artificial intelligence? Answer: For the testing set, Caret offers…
Q: configuration of the network known as a star topology is one in which each node is linked
A: The configuration of the network known as a star topology is one in which each node is linked to the…
Q: ch affect a comp
A: Cyber Security: Cyber security is the utilization of technology, methods, and approaches to…
Q: ks connected via two routers, netwo: rk B has MTU of 200 Bytes, networ cion A needs to send a…
A:
Q: A directory is basically a list of names paired with inode numbers. When a directory is first…
A: Directory Directory is a container or location where files and folders are stored in a file system.…
Q: Consider yourself a system analyst in the workplace. Do you see any similarities or differences…
A: The SDLC is a method for developing high-quality software using well-defined processes. The software…
Q: More than 90% of the microprocessors/micro- controllers manufactured is used in embedded o…
A: The answer is
Q: 28. In a linear linked list,, a. the next pointer of each node has the value NULL b. the last node…
A: Linear linked list is a linear data structure. It is a collection of nodes . each node…
3
Step by step
Solved in 3 steps with 3 images

- Computer Science Consider the following Haskell functions:step x y = y + 1mystery iL = foldr step 0 iLWhat will the following expression evaluate to , show the execution and explainmystery ["ab","bc","cd","bc"]Computer Science Course: Reconfigurable Computing Content: Make an Experimental report on Implement a 2-D convolution using HLS C and Optimize the HLS with directives. Please include images of the task in the report.19. Find the 15th term of the series. Need C, C++, Java, Python, or Perl code for the below question. Important: Do not copy codes from prepinsta.com.
- Describe how memory allocation is done to objects and also develop a C++ programfor employee class with following attributes such as Employee ID, Employee Name,Designation and Salary. Program should sort and display the list of employees inascending order of their salaries using object as a function argument. (Note:Employee ID must not be inputted by the user i.e., auto incremented.)21. Find the Nth term of the series. Need C, C++, Java, Python, or Perl code for the below question. Important: Do not copy codes from prepinsta.com.C++ Programming. General setting. The program must contain: • base class X, which includes two elements x1, x2 of type int, • constructor with parameters for creating objects in dynamic memory area, • destructor, • virtual methods for viewing the current state and reinstalling base class objects to a new state. • derived class Y, including one element y of type int , • a constructor with parameters and an initializer list, passing data to the base class constructor, • overridden methods for viewing the current state of objects and reinstalling them to a new state. Create a Run method in the derived class that defines: Value (x1-x2)^2/y
- 2.15 The principle of locality maintains that variable declarations should come as close as possible to their use in a program. What language design features promote or discourage this principle? How well do Python, C, C++, and Java promote this principle?2.18 Most programming languages now use the free format pioneered by Algol60, in which state- ments can begin anywhere, but must end, not with the end of a line of text, but with an explicit end symbol, such as a semicolon. By contrast, Python and a few other languages use fixed format, in which statements begin in a particular column and end at the end of the line of code, unless continuation marks are provided. Discuss the effect of fixed or free format on readability, writability, and security.Describe a situation where the add operator in a programming languagewould not be commutative. ____________________________________________________________________ Let the function fun be defined asint fun(int *k) { *k += 4; return 3 * (*k) – 1;}Suppose fun is used in a program as follows:void main(){ int i = 10, j = 10, sum1, sum2;sum1 = (i/2) + fun(&i);sum2 = fun(&j) + (j/2);}What are the values of sum1 and sum2a. if the operands in the expressions are evaluated left to the right?b. if the operands in the expressions are evaluated right to the left?
- Provide examples of the data types required by each of the four user types.Explain how a C++ union conserves more memory than a struct. What is the primary disadvantage of the union over the struct?Define what the following do in C in relation to pointers: *, &, [], +, Note that there are 2 functions for *. Write code that uses all 5.

