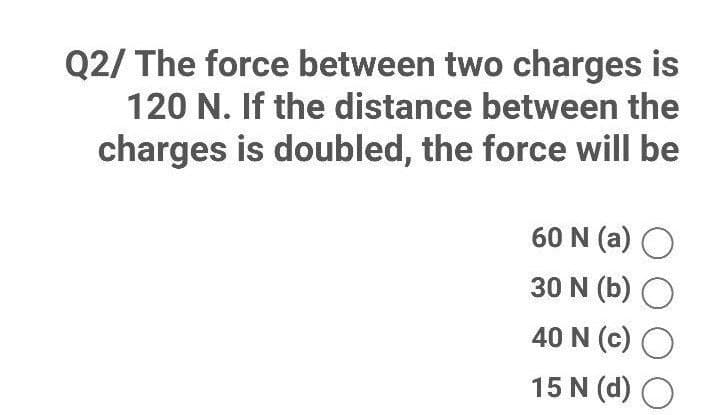
2/ The force between two charges is 120 N. If the distance between the charges is doubled, the force will be 60 N (a) O 30 N (b) O 40 N (c) O 15 N (d)
Q: What would you recommend as a Big Data Architecture for a business that offers its clients access to…
A: Introduction : A big data architecture is designed to handle the ingestion, processing , and…
Q: Does this circumstance need a certain network topology?
A: Network topology refers to the physical configuration of a set of connected computing devices. It…
Q: Write a pseudo-code on how to import global COVID cases data. Assume you have a CSV file containing…
A: import require librariesimport pandas as pdimport numpy as npimport matplotlib.pyplot as…
Q: A serious accident occurred on the National Highway, so an ambulance arrived immediately and the…
A: Input/Output Process: First line contains five space separated integers N, M, R, X and Y denoting…
Q: Homework 12. Use NAND gates, NOR gates, or combinations of both to implement the following logic…
A:
Q: How important is it that students make use of various forms of technology to assist them in their…
A: The answer of this question is as follows:
Q: Write only the nested for loop that prints the following numbers in columns and rows using only the…
A: We need to write a Java program using nested for loops that prints the given pattern. Algorithm : 1.…
Q: ry explained in detail?
A: Introduction: Any physical component that can store data either permanently, like ROM, or…
Q: "My favorite number is " + 7correct data type that the above expression evaluates to in C#
A: C# (pronounced "See Sharp") is a cutting edge, object-oriented, and type-safe programming language.…
Q: SOLVE STEP BY STEP IN DIGITAL FORMAT Make a comparison chart that includes: The characteristics of…
A: We need to include the characteristics of the following in the comparison chart. trees. isomorphic…
Q: What exactly are encapsulation and de-encapsulation?How does it function in a network?
A: Introduction: One of the core concepts behind OOP is called encapsulation (object-oriented…
Q: Active hosts and their network ports are detected by network scanning programmes. Scanning tools…
A: Intro Network Scanning: Network scanning is the process of signaling devices on a network and…
Q: CPU Scheduling may be accomplished in a variety of ways. In terms of overall system performance,…
A: Intro Scheduling methods: According to Bartleby's rule, we can only answer one question at a time.…
Q: When it comes to reviewing security operations and making suggestions for improvements, why would a…
A: To keep your company's data secure, security is crucial. High security prevents data breaches and…
Q: Describe the advantages of using a third party.
A: Third party: A third party is defined as the other significant, competing political party in a…
Q: speed=input("Enter your speed in mph: ") speed = int(speed) distance = input("Enter your distance in…
A:
Q: In terms of speed, what is the difference between virtual memory and RAM
A: Introduction: The performance difference between two types of computer system memory is…
Q: This refers to data structures that have keys and values. (A) Dictionary (B) Matrix C) Lists D…
A: The answer will be Dictionary(option A) Explanation:- The dictionary in the python are used to store…
Q: Determine which of the programming codes has less time (perform algorithmic complexity calculation…
A: Solution: Code 1, has less time.
Q: What exactly is meant by the phrase "Rational Unified Process"?
A: Rational unified process is an iterative software development process framework. This process is…
Q: What is the meaning of the phrase "Parallel Run"?
A: Introduction: The inquiry seeks to comprehend the notion of parallel running.
Q: Give an explanation of the connection between Boolean logic and the workings of computer circuits.…
A: Logic gates: Logic gates are the building blocks of computer circuits. Current flows through the…
Q: It is everyone's responsibility to combat dangerous hacking. Do you believe that to be true? What…
A: Below is the answer to above question. I hope this will be helpful for you...
Q: What are the benefits of creating "connection points" across different networks? How do they factor…
A: Connection points: The attachment points are connected by a route, which is a path on a graph. It…
Q: What is risk management in the context of information systems?
A: The Answer is in step2
Q: To create commercial software, incremental development is the most effective strategy, therefore…
A: Company software systems are often complex, software-escalated, and prone to change when business…
Q: What advantages do assert statements have?
A: Introduction: In the software, assertion conditions are handled through the usage of assert…
Q: atrays agic arrays if the sun of their valses located at the same position indices are equal to each…
A: Java Program: import java.util.*; class Test{ public static void main(String args[]) { Random…
Q: What does DES (data encryption standard) mean?Explain.Please do it the right way. Information…
A: Introduction: Because DES encrypts and decrypts a message with the same key, both the sender and the…
Q: Give many instances of real-time operating systems so that the reader may better understand them.…
A: Real Time Operating System can be explained as the operating systems which are being used in…
Q: Discuss the difficulties of concurrency in a multiprogramming system.
A: The concurrency in a multiprogramming system is running or executing more than one programs at a…
Q: Consider the following MATLAB code: a=1; while a<=6 a=3*a-1; end How many times the loop repeats?…
A: Given a=1 The condition of the while loop is a<=6 1<=6 (condition true) So, the code inside…
Q: Complete this code using python language #Write the conditions to check if anyone has won the game.…
A: It is defined as an interpreted, object-oriented, high-level programming language with dynamic…
Q: In order to be an effective CIO, you'll need to possess the following five leadership…
A:
Q: When is it preferable to work as a team or as an individual?
A: Introduction: Everyone in a team is unique and may provide a fresh perspective to the challenge.…
Q: Since the 1950s, the Turing Test has been used to measure the intelligence of computers. If you had…
A: Turing Test: The Turing Test is a straightforward way for determining whether or not a computer can…
Q: Four kinds of computer-based system needs should be identified and briefly described.
A: Intro Requirements for computer-based programmes include the following: System requirements are…
Q: Big Data Cluster's infrastructure has become reliant on cloud computing.We could have a large data…
A: One of the most discussed topics in IT is big data. And big data as a service really benefits as a…
Q: If a project like mobile banking includes the creation of new technologies, how might the four…
A: A model with four frames: The Four Frame Model is a conceptualization that splits every organization…
Q: Explain any two features that can enhance a hub's intelligence.
A: Introduction: As a multiport repeater, a hub is similar to that. In a star architecture, for…
Q: Access to management must be maintained while protecting sensitive information (such as an…
A: There is much more to protecting sensitive data than preventing data breaches. It entails evaluating…
Q: What causes connections to stay in the FIN WAIT 2 state, and what can you do about it?
A: Introduction: When the server has an active connection with a client and chooses to end the TCP…
Q: What's the best way to sum up Ubuntu OS in terms of server operating systems?
A: Ubuntu Desktop includes a graphical user interface, Ubuntu Server does not. It is because most…
Q: What precisely does it mean when someone says they are "opening a file"?
A: The term "file" refers to the standard unit of storage found in a computer. A computer's data and…
Q: Dear. The advantage of developing a found repecit fication in software development and using formal…
A: advantage are discussed in next step:
Q: Briefly define TinyOS and explain its goals as an embedded operating system.
A: Introduction Small, flexible, low-cost nodes that interact with their environment and each other…
Q: What is the function of a TPM in the encryption of the whole disc?
A: TPM: The Trusted Platform Module (TPM) technology is designed to offer hardware-based security…
Q: Sequential and direct access are two methods for finding data in memory. In this article, I'll…
A: Definition: Because each data chunk is saved in a discrete and separate location from other chunks,…
Q: Complete the code to return the output. x = 1 print (x)) True A) float (B) bool C int D str Question…
A: Here we have to solve the MCQ questions regarding python. 1) The correct answer is option (B) bool…
Q: The advantage of circular arrays for queues raises the question: Would the circularly-linked list…
A: Basics An array is a collection of the items stored in contiguous memory locations. The idea is to…
Step by step
Solved in 2 steps with 2 images

- You have 20 bottles of pills. 19 bottles have 1.0 gram pills, but one has pills of weight1.1 grams. Given a scale that provides an exact measurement, how would you find the heavy bottle?You can only use the scale once(Mechanics) The deflection at any point along the centerline of a cantilevered beam, such as the one used for a balcony (see Figure 5.15), when a load is distributed evenly along the beam is given by this formula: d=wx224EI(x2+6l24lx) d is the deflection at location x (ft). xisthedistancefromthesecuredend( ft).wistheweightplacedattheendofthebeam( lbs/ft).listhebeamlength( ft). Eisthemodulesofelasticity( lbs/f t 2 ).Iisthesecondmomentofinertia( f t 4 ). For the beam shown in Figure 5.15, the second moment of inertia is determined as follows: l=bh312 b is the beam’s base. h is the beam’s height. Using these formulas, write, compile, and run a C++ program that determines and displays a table of the deflection for a cantilevered pine beam at half-foot increments along its length, using the following data: w=200lbs/ftl=3ftE=187.2106lb/ft2b=.2fth=.3ftA standard science experiment is to drop a ball and see how high it bounces. Once the “bounciness” of the ball has been determined, the ratio gives a bounciness index. For example, if a ball dropped from a height of 10 feet bounces 6 feet high, the index is 0.6, and the total distance traveled by the ball is 16 feet after one bounce. If the ball were to continue bouncing, the distance after two bounces would be 10 ft + 6 ft +6 ft + 3.6 ft = 25.6 ft. Note that the distance traveled for each successive bounce is the distance to the floor plus 0.6 of that distance as the ball comes back up. Write a program that lets the user enter the initial height from which the ball is dropped, the bounciness index, and the number of times the ball is allowed to continue bouncing. Output should be the total distance traveled by the ball. Below is an example of the program input and output: Enter the height from which the ball is dropped: 25 Enter the bounciness index of the ball: .5 Enter the number of…



