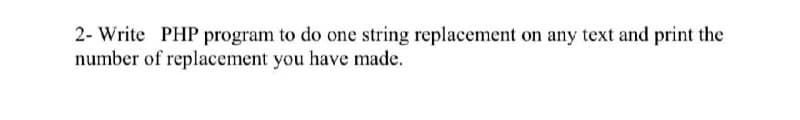
2- Write PHP program to do one string replacement on any text and print the number of replacement you have made.
Q: What are the advantages and disadvantages of enforcing Internet neutrality?
A: Advantages •It protects innovation and if big companies like Google and Netflix could pay to get…
Q: In multimedia, standard construction components are critical. Explain the different types of…
A: Introduction: Text, audio, graphics, video, and animation are all examples of multimedia components.…
Q: IT Infrastructure as a Service (IaaS) Is there a definition for resource management?
A: Given: A sort of cloud computing service known as infrastructure as a service (IaaS) provides…
Q: Which of the cache consistency protocols do you know about?
A: The protocols to maintain the coherency for multiple processors are called cache-coherency…
Q: What are today's most critical IT security issues? Was there a change in the last five years, and…
A: Threats to IT security that firms face today include: The following are some of the most major IT…
Q: What what is an unnormalized design, and how do you convert one to 1NF?
A: Unnormalized database: An unnormalized database design is made up of a table or a series of tables…
Q: Computer Science Please create the activity model for stock trade order Hint: verify order, send…
A: Activity model is use for whole activity process
Q: What are some of the risks associated with a server database migration project?
A: Justification: Data is transferred from one server to another using the server migration method.…
Q: What function does a foreign key play in maintaining the integrity of a database? What kind of…
A: Answer : They help to define the relationship in the table. They allow developers to maintain…
Q: The CS2220 Hard Disk Drive (HDD) is advertised with an average seek time of 3ms, 2048 byte sectors,…
A: We are going to calculate required time to read the entire file of size 512Kbytes. Required Time =…
Q: Consider the following recognising Finite State Machine (FSM) S3 1,0 1,0 S2 S4 So State which of the…
A:
Q: What exactly is the invisible web, and how huge is it in terms of area?
A: Introduction: Bergman's work was the only effort to quantify the magnitude of the Invisible Web that…
Q: 4)Show the decoding logic for each of the following codes if an active HIGH. 1000 , 11100 ,101010,…
A: As per the Bartleby policy we need to give only one question's Answer but I am providing for 2…
Q: Why do two Internet service providers (ISPs) at the same level of the hierarchy frequently peer with…
A: ISP is also known as Internet service providers.
Q: Consider a Label control named dogLabel in an application's GUI. Put a sentence in the dogLabel…
A: Forms in Windows Label controls are used to show non-editable text or pictures. They are used to…
Q: What exactly do you mean by attribute interpolation?
A: Introduction: Angular translates interpolation into property binding using a specific syntax (pair…
Q: Would you allocate newly hired systems analysts to maintenance projects as an IT manager? Why do you…
A: Introduction: An analyst collects, analyses, and applies complicated data in order to create…
Q: Is it necessary to have a remote administration system?
A: According to the question the RSAT allows the administrators to run snap INS and the tools on the…
Q: We may use the traceroute software to transmit datagrams of various sizes to a certain destination,…
A: Introduction: capturing packets from a traceroute executionThe traceroute software is used to…
Q: Define the notation for arrays.
A: Justification: Arrays are a form of data structure that may hold a sequential collection of items of…
Q: 2. What are the new features added for Interfaces in Java 8 and Java 9? Give an example of an…
A: INTRODUCTION: Here we need to tell new features added for interfaces in java 8 and Java 9 and also…
Q: 1) Write a query in SQL to create all the information of the student's class: Relation Name:…
A:
Q: What does it mean to optimise a database? Even if DBMSS automatically optimise SQL queries, why do…
A: Internet protocol: IP packets are the made up of two parts: a header and a payload. There are fixed…
Q: Isn't it possible to use a Parent Class object in a Child Class and take use of all of its features?
A: Introduction: Object and classes are the concept in object oriented programming languages. Through…
Q: Implement the following class and test its methods: Fraction - numerator. int - denominator. int +…
A: Created 2 versions of the program. 1st version takes input from the user and 2nd version doesn't…
Q: List the criteria that indicate a system's useful life has come to an end.
A: The following criteria suggest that the system's end of life is approaching: At some point, every…
Q: Is there a relationship between technology and human behaviour when it comes to cyber security?
A: Introduction: As indicated by the present review, digital social way of behaving is portrayed as a…
Q: Question 5 Consider the following recognising Finite State Machine (FSM) S3 1,0 1.0 S1 S2 S4 So…
A: Find the answer with explanation given as below :
Q: Describe the system's design requirements.
A: Given Question: Describe the design requirements for the system.
Q: In addition to receptacles for personal computers and peripherals like printers and scanners, it is…
A: INITIATION: Along with outlets for personal computers and accessories such as printers and scanners,…
Q: What is the result of a function that substitutes the operator of a class with another operator of…
A: Administrators may be made to work for client-defined classes in C++. C++ may provide administrators…
Q: RAID systems, and what are the advanta
A: RAID systems are the most common means of data storage on computers. RAID systems combine multiple…
Q: C program to get 3 number from user and find average of all three numbers and print it to user
A: ALGORITHM:- 1. Take input for 3 numbers from user. 2. Calculate the average of the input numbers. 3.…
Q: what Con ue con about Pufumona optimitotion Perm Andohl's low?
A: The Answer is in step-2
Q: What distinguishes embedded systems programming from application development in general?
A: The distinction between embedded system programming and the development of broad applications…
Q: In the context of Dara warehousing, what precisely is the hybrid approach?
A: Please find the detailed answer in the following steps.
Q: What is the truth behind the notion that data structures and algorithms are becoming outdated in the…
A: The Data structure ideas can be executed in any programming language. Software engineers can compose…
Q: What distinguishes TPC from SPEC in terms of its focus?
A: Introduction: The Transaction Procession Council (TPC) is a non-profit organization that creates…
Q: m and how can you e
A: Introduction A database management system (DBMS) is a system for managing data that must remain…
Q: What are the most critical decisions to be made when it comes to physical database design and how do…
A: Various critical decisions to be made when it comes to physical database design are: The client…
Q: 2. Find the regular expression for the following Finite Automaton. For this you are requested to…
A:
Q: C program for getting name from user and print welcome message with that name Ex. Welcome name
A: The following program demonstrates how to scan a user's name and welcome with name. In this program,…
Q: TASK 1a Patient Personnel Treatment Test Bed Department Using the list of entities a
A: Query to create each table: CREATE TABLE Patient ( patientID INTEGER PRIMARY KEY AUTOINCREMENT NOT…
Q: Name the three methods for dealing with exceptions.
A: We have to understand the three methods in which we can handle or deal with exceptions. Let's…
Q: Explain the advantages and downsides of taking use of online learning possibilities.
A: These days due to COVID outbreak, the online learning and classes have been ramped up a lot. There…
Q: A team undergoes numerous stages of growth. Discuss each of these steps in detail, referencing a…
A: Everyone's best interest is served by following the five stages of team development: forming,…
Q: In multimedia, standard construction components are critical. Explain the different types of…
A: Multimedia Components: 1. Textual Materials The text takes us back to the origins of the web when…
Q: How do restore points in Windows 7/Vista work?
A: Protection of the system: It's a feature included in the Windows operating system. It's used to…
Q: Instructions: Create a complete ERD in Crow's Foot notation that can be implemented in the…
A: a) Crowfoot Notation:
Q: A team undergoes numerous stages of growth. Discuss each of these steps in detail, referencing a…
A: Introduction: Stages of team development Forming - The first stage of team growth, when there is…
Step by step
Solved in 2 steps

- 1.2 Write a PHP program to read a string from the user and check whether the word "Hello" is present in the string or not.21) Write a PHP program to find the sum of all natural numbers which are multiple of 7 in the range 1 to 1000(including both) and print the sum in the output. Asap.Write a program in php to take input a string and reverse it. And print both input string and reversed string.
- Write a PHP functional program to remove the character in a given position of a given string. The given position will be in the range 0..string length -1 inclusive.d) Write a program in PHP to read a string from the user and check whether the word "Hello" is present in the string or not.3. Write a PHP program to read input a string str and a positive integer n in the range [1,10] from the user. Then concatenate the string str for n times and display the string formed in the output.
- Write a php program to take input a string and an integer from user and print if the integer is equal to the length of the string or not.Write a php program which print a string. The string must be l am beginner in php. When I try to doing that unable to read the script error is comingIn Php b) Write a PHP program to find the sum of all natural numbers which are multiple of 7 in the range 1 to 1000(including both) and print the sum in the output.

