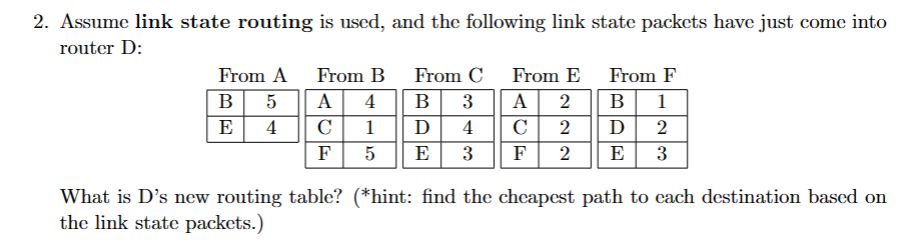
2. Assume link state routing is used, and the following link state packets have just come into router D: From A B 5 E 4 From B A 4B с F 1 5 From C 3 Ꭰ 4 E 3 From E From F A 2 B 1 C 2 D 2 F 2 E 3 What is D's new routing table? (*hint: find the cheapest path to each destination based on the link state packets.)
Q: Given the relation T below, use ordered pair notation to express the relation To T. ToT { Ex: (a,…
A: This question explores the concept of relation composition in mathematics. Specifically, it asks you…
Q: Scope and Limitation: Your program must include ONLY and ALL of the following C LANGUAGE statements:…
A: C is an imperative procedural language with a static type system that supports lexical variable…
Q: 2.Local variables have block scope. What does this mean?
A: Block scope promotes encapsulation by limiting the visibility of variables to the smallest…
Q: Use the recursion to solve the following problems using Java Programming Language 1. Calculate the…
A: In this question we have to write the list of Java Program1. Calculate the sum of an array of n…
Q: Explain how the OSI model facilitates understanding and troubleshooting in network protocols?
A: The Open Systems Interconnection (OSI) model is a conceptual framework that standardizes the…
Q: Can you please help me with this code because I am struggling on how to do this, This has to be in C…
A: Accept the list of numbers as command line arguments.Parse the command line arguments and store the…
Q: cell C21 for the Hours Worked. The regular pay will be the hours worked times the pay rate unless…
A: The following formulas in Excel can be used to determine regular pay and overtime compensation…
Q: QUESTION 6 What happens after every 210,000 blocks are recorded on the Bitcoin blockchain? The value…
A: The Bitcoin blockchain is a decentralized ledger that records all transactions made with Bitcoin.…
Q: Encipher the following plaintext using the Vigenère cipher and key = ‘MONEY’: “make the deposit by…
A: The Vigenère cipher is a polyalphabetic substitution cipher used for encrypting plaintext. It…
Q: 4. Password Check Given a password as string, the function will check whether it's valid. If it's…
A: The task is to implement a function is_password_valid that checks whether a given password meets…
Q: didn't understand the previous code and it didn't run to my software . can you do it again? I use…
A: In this question we have to write a Java Code classes, Player and Team, to manage a sports team…
Q: Write a program that calculates the total grade for N classroom exercises as a percentage. The user…
A: In this question we have to perform the programming task where the objective is to write a program…
Q: Which artificial intelligence (AI) algorithms are better with first order logic: Recurrent Neural…
A: First-order logic (FOL) is a fundamental concept in AI that deals with propositions, predicates, and…
Q: Hello. Please answer the following Algorithms question correctly. You don't have to give a long…
A: In this question we have to find the distance between the closest two points in a given set, using…
Q: If the data availability has the highest importance which RAID level you would use? How many disks…
A: Since data availability guarantees data accessibility and integrity, it is a crucial consideration…
Q: Encipher the following plaintext using the Row Transposition cipher and key = 3 5 2 4 1: “i have…
A: The plaintext "I have decided to give you a job offer" is to be deciphered using the Row…
Q: Let's consider that we have an IC that implements a four (4) bits adder. f. Use this IC to design an…
A: Kindly note that you have posted multiple sub questions of a single question. As per our guidelines,…
Q: How does Darktrace's Enterprise Immune System work for cybersecurity? What platforms are using it…
A: Organizations must tackle the difficult challenge of defending their digital infrastructure against…
Q: Why is the native function gets() problematic in the context of C string considerations? A. gets()…
A: The correct answer is D because it highlights one of the main reasons why gets() is problematic in…
Q: In MIPS assembly how do I open a file, write to the buffer, and write what is in the buffer to the…
A: MIPS assembly is a low-level programming language commonly used for programming MIPS…
Q: (Locate the largest element) Write the following method that returns the location of the largest…
A: The given programming exercise involves the creation of a Java class named Exercise08_13. The main…
Q: Fill in the blank: Data science involves using data to create new ways of modeling and understanding…
A: In records science, working with uncooked information is fundamental to the system of extracting…
Q: in python Integer num_athletes is read from input, representing the number of athlete names to be…
A: The objective of the question is to read a number of athlete names from the input, store them in a…
Q: What is computational complexity theory, and why is it important in computer science?
A: Computational complexity theory is a branch of computer science that deals with the…
Q: True or False a. If you do not write a constructor for a class, java will supply a default…
A: The objective of the question is to determine the validity of several statements related to Java…
Q: Two Unix users, Emily Jacobs and Tony Weber, need to access current product names and prices. Create…
A: The objective of the question is to create a solution in SQL Server that allows two Unix users,…
Q: If ParentClass is a Java class and we want the derived classes to have access to all the members of…
A: Access specifiers in Java define the visibility and accessibility of classes, methods, and variables…
Q: Alert dont submit AI generated answer. please explain in details. 6. Write a method that takes the…
A: StartDefine a method ConvertAndDisplayTable that takes three arguments: startingKm of type double,…
Q: a) In the dining philosophers problem, let the following protocol be used: An even-numbered…
A: When two or more processes or threads are stuck waiting for one another to release a resource or…
Q: . Write SQL statements to create a table named STUDENT, with the following columns: StdID:…
A: In this question we have to write SQL QUERY for the given table name STUDENT.Let's query and hope…
Q: The following problem shows up in a number of Java texts, including Savitch's textbook: The…
A: The below program prompts the user to enter weight, height, age and sex, then calculates the basal…
Q: Please find any article that relates to some specific malware. Elaborate what kind of malware is it…
A: We will be mentioning the malware but won't use any external links. WannaCry was a ransomware…
Q: python code: Assuming case sensitivity where changing a letter's case has a cost of 1, calculate the…
A: Here's a simple explanation of the algorithm used in the provided code:1. Initialization: We…
Q: Consider the following program: void doSomething (int n) { int i, j; i=2; while (i <= n) { } for (j=…
A: The given program is in Java language. Java is a general purpose, high-level programming language.
Q: Please help me with these questions. I am having trouble understanding what to do use ← Just draw…
A: In this question we have to design the flowcharts for the given program scenarios.As per bartleby,…
Q: Alert dont submit AI generated asnwer. please explain in details. 5. Write a method that takes a…
A: 1) Below is the program that implements method that display a Celsius to Fahrenheit conversion table…
Q: You will be using Relax again to help you build your RA expressions and answer questions based on a…
A: The objective of the question is to find the names of dealers who sell some black cars using…
Q: Employee Paycheck in C++ Programming:
A: In an employee paycheck program, we can use several functions to handle different aspects of the…
Q: Please solve the problem. part A specifically. Do not use AI. I'll be able to tell
A: it seems like the problem that you are grappling with is linked with process scheduling in an…
Q: ocode for the algoryt
A: Here is an assembly language Little Man Computer (LMC) software that takes a specified Little Man…
Q: lease answer this question- Implement Floyd's algorithm for the Shortest Path on your system, and…
A: In this question we have to implement Floyd's algorithm in Java to find the shortest paths in a…
Q: racteristic equation mogeneous linear
A: If a first order differential equation has the structure dydx=F(yx), where F(yx) F (y x) is a…
Q: python code Assign different costs to insertions, deletions, and substitutions to reflect varying…
A: In this question we have to calculate the Levenshtein distance between two strings, "Natural…
Q: a. Sunshine Seashore Supplies rents beach equipment to tourists. In previous chapters, you have…
A: Please refer to the following for the algorithm of the code =>Algorithm for Rental Class…
Q: Select the pair that correctly completes this sentence. In Java we derive classes from the _?__…
A: The derived class is a class which is extracted from the original class or a parent class. It is…
Q: The following decimal numbers are already in six-digit 10's complementary form. Add the numbers.…
A: Answer the above questions are as follows:
Q: Create a new project for this program called TestOldMaid and add a class with a main() method. In…
A: The question does not specify any particular programming language for the solution. We have done the…
Q: o this for me find another vulnerability and exploit within the Metasploit framework against the…
A: In this question we have to find and exploit a new vulnerability within the Metasploit framework…
Q: 1). Create the class called ArrayOperations2D and include the method findRowMax below public class…
A: The objective of the question is to create a class called ArrayOperations2D in Java that includes…
Q: It's time to implement an API. We’ll use express to do this. Replace the http module in your…
A: We import the Express module and create a router using express.Router().We import the OrderManager…
Step by step
Solved in 1 steps

- Question 1 Suppose P packets arrive simultaneously to a link at which three packets are currently queued and one just started transmission. All packets are of length L and the link has transmission rate R. What is the average queuing delay for the P packets? Full explain this question and text typing work only thanksIt has a total of four routers. Every single one of the four distinct kinds of routers Does router A need to recompute its distance vector as a result of the addition of routers B and D to the network as a result of the construction of a new link that connects routers A and C? The DV (distance vector) algorithm is the routing mechanism that is employed by the RIP protocol, which is executed on the routers.q33- What is one of the characteristics is commonly associated with dynamic routing protocols? Select one: A. Requre special subnets masks B. Require less processing power than static routes require C. Require device configuration D. Consume some bandwidth to exchange routes information
- Can someone help me with this question please? ASAP??!!! 6. Consider a packet of length L which begins at end system A and travels over three links to a destination end system. These three links are connected by two packet switches. Let di, si, and Ri denote the length, propagation speed, and the transmission rate of link i, for i = 1, 2, 3. The packet switch delays each packet by dproc. a. Assuming no queuing delays, in terms of di, si, Ri, (i = 1,2,3), and L, what is the total end-to-end delay for the packet? (10 Points) b. Suppose now the packet is 1,500 bytes, the propagation speed on all three links is 2.5×108 m/s, the transmission rates of all three links are 2 Mbps, the packet switch processing delay is 3 msec, the length of the first link is 5,000 km, the length of the second link is 4,000 km, and the length of the last link is 1,000 km. For these values, what is the end-to-end delay? (15 Points)It contains four routers in total. Every one of the four main types of routers Is it necessary for router A to recompute its distance vector as a result of the addition of routers B and D to the network due to the building of a new connection between routers A and C? The DV (distance vector) algorithm is the routing technique used by the RIP protocol, which runs on routers.0. AS1 has the following routing table, draw the network of AS’s that these paths imply: prefix path P1 AS2 P2 AS4 AS5 AS3 P1 AS4 AS2 P2 AS5 AS3 P1 AS5 AS2 Assuming AS 1 accepted all the paths advertised to it, what paths does AS4 advertise to AS1? What AS is P1 in? What about P2? AS5 no longer wants to forward packets destined for prefix P1 on behalf of AS1, but it is ok forwarding prefix P2, how would it change the paths it advertises to AS1? If AS1 sends a packet to AS4 destined for P1, what path will it take? How do we know AS4 won’t forward it back to AS1? If AS1 gets the following advertisement from AS4, P1 AS4 AS1 AS2 how would it update its table? Why?
- 0. AS1 has the following routing table, draw the network of AS’s that these paths imply: prefix path P1 AS2 P2 AS4 AS5 AS3 P1 AS4 AS2 P2 AS5 AS3 P1 AS5 AS2 Assuming AS 1 accepted all the paths advertised to it, what paths does AS4 advertise to AS1? What AS is P1 in? What about P2? AS5 no longer wants to forward packets destined for prefix P1 on behalf of AS1, but it is ok forwarding prefix P2, how would it change the paths it advertises to AS1? If AS1 sends a packet to AS4 destined for P1, what path will it take? How do we know AS4 won’t forward it back to AS1? If AS1 gets the following advertisement from AS4, P1 AS4 AS1 AS2 how would it update its table? Why? NOTE: I would appreciate it if the solutions of the paths were hand-drawn so I can visualize it better.There are four routers. Each of the four different types of routers With the installation of a new link to connect routers A and C, does router A need to recompute its distance vector in response to the inclusion of router B and D into the network? RIP runs on the routers and the DV (distance vector) algorithm is the routing technique used by RIP.Consider the network shown below, and Dijkstra’s link-state algorithm. Suppose that Dijkstra's algorithm has been run to compute the least cost paths from node E to all other nodes. Now suppose that source node E has a packet to send to destination node A. What is the first router to which E will forward this packet on its path to A?
- . Consider the network shown below. Assume AS1 and AS2 use OSPF as intra-AS routing protocol. AS3, AS4 and AS5 use RIP as intra-AS routing protocol. eBGP and iBGP are used as interAS routing protocols. Assume there is no physical line between AS2 and AS3 at startup.a) What protocol does the 5b router learn about x? Explain why.b) What protocol does the 2c router learn about x? Explain whyc) Router 2c enters the forwarding table (x, I) when it knows about x. Assume that the dotted line drawn between AS2 and AS3 represents a physical line. Router 2c learns that x is reached via AS1 as well as AS3. Once you know this, does I equal I1 or I2 or I3? Explain your reason.The usage of static routing has been met with opposition for several reasons, but which of the following is NOT one of them? O. Extra hardware or bandwidth is unnecessary. O.b. The routing tables are modest in size, need just occasional attention. Any alteration to the topology will, of course, have consequences for the setup. The path to the destination never deviates from that one.We have 5 routers labled A-E. Suppose we have the forwarding tables shown below after the routingalgorithm is stable. Let all links have cost 1. a. If a message is originated from A and a destination is E. Which path does it take?b. If a message is originated from C and a destination is D. Which path does it take?c. Give a diagram of a possible network consistent with these tables.



