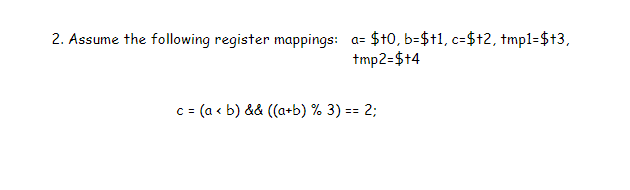
2. Assume the following register mappings: a= $t0,b=$t1, c=$+2, tmpl=$+3, tmp2=$+4 c = (a < b) && ((a+b) % 3) == 2;
Q: Interpolation is the name given to the procedure that includes guessing the value of a function at a…
A: Interpolation is a mathematical technique used to estimate the value of a function between two known…
Q: What what is "data mining," and how exactly does it function?
A: Introduction: Data mining is the process of collecting information from data by identifying…
Q: How does the organisation of data change between a solid-state drive and a magnetic disc? What are…
A: Data storage technology has come a long way since the early days of computing, and today we have two…
Q: In comparison to other types of data structures, such as linked lists and arrays, how does a binary…
A: Data structures are essential in computer science as they help in organizing and managing data…
Q: Please provide a condensed description of the different regulatory methods that might be used to…
A: Description of the various regulatory methods that can be used for device requests. This information…
Q: Examine how people who use computers and mobile devices respond to issues with software and…
A: Users of computers and mobile devices often encounter issues with software and applications. These…
Q: How deeply should end users be engaged in the process of selecting the database management system…
A: End users ought to be taken part in the process of selecting the database management system (DBMS)…
Q: Is the introduction of new technology, such as the internet, making society more or less harmonious?…
A: The internet has revolutionized the way people communicate and access information. It has allowed…
Q: There may be a variety of drawbacks and challenges associated with disjointed information systems.
A: Disjointed information systems can refer to a situation where different parts of an organization or…
Q: List At least three registers designed specifically for use by the FPU that are devoted to their…
A: List At least three registers designed specifically for use by the FPU that are devoted to their use…
Q: How will the workplace use ethical reasoning?
A: Ethical reasoning helps to determine and differentiate between right thinking, decision and actions…
Q: A piece of data that can only be read by computers is referred to as a binary file.
A: When it comes to storing information on a computer, data can be stored in different file formats.…
Q: How can the integration of cloud computing best fulfil the most urgent requirements of a business?
A: Cloud computing has become an integral part of modern businesses, offering numerous benefits such as…
Q: What exactly are firewalls, and how exactly do you make use of them?
A: In the realm of cybersecurity, firewalls play a critical role in protecting computer networks and…
Q: Compare and contrast the strengths and weaknesses of different software testing approaches. It has…
A: Foreword to Software Testing Approaches: Among the most critical processes in the Creation of…
Q: Concerning the short-term and long-term effects of information technology on individuals and…
A: Information technology refers to the use of computers, software, and other electronic devices to…
Q: ome of the challenges that come w
A: Describe some of the challenges that come with dealing with vast volumes of data.
Q: Give an explanation of how Random Access Memory (RAM) in a computer works using only your own words…
A: Random Access Memory (RAM) is a type of computer memory that allows the computer to temporarily…
Q: Can you take any measures to guarantee that your model gets entry to all the information it…
A: Computer graphics play a crucial role in various industries, such as entertainment, advertising, and…
Q: What are the repercussions of the revolution brought on by cloud computing if it starts to affect…
A: Cloud Computing has revolutionize how businesses function by as long as on-demand admission to…
Q: RAID 5: what exactly is it, and how does it function? When is using RAID 5 a better choice than…
A: RAID 5, or Redundant Array of self-governing Disks level 5, is a storage answer that Combine…
Q: It is possible that a variety of difficulties will arise as a result of the existence of a diverse…
A: The most effective strategy to address issues arising from a diverse assortment of information…
Q: 4.01-1. Packet scheduling (a). Consider the pattern of red and green packet arrivals to a router's…
A: a) FCFS scheduling FCFS, or first come, first served, is an acronym. This means that packets will be…
Q: The ideas of computer architecture and computer organization are separate from one another; yet,…
A: Computer architecture and computer organization are two important concepts in the field of computer…
Q: It would be helpful if you could provide a brief summary of the various regulatory channels for…
A: The regulatory channels for medical device requests can vary by country or region, but generally…
Q: What exactly is meant by the term "scripting language" when referring to Windows? (Pick all of the…
A: A scripting language is a programming language used to automate tasks, perform batch processing, and…
Q: Give citation guidelines. Plagiarism consequences?
A: A. Importance of Citations B. Citation Styles IEEE ACM APA MLA C. How to Cite Books Journals…
Q: What are the most significant differences between traditional computer usage on a desktop and the…
A: Mobility with Accessibility: One of the most significant differences between customary desktop…
Q: make a code seizure in visual studio. Note: explaining the steps
A: In today's fast-paced world, the development of efficient and reliable software is essential for a…
Q: Is it essential to have a Master file given that it contains a significant quantity of data that…
A: A master file is a centralized repository that contains important data or information that pertains…
Q: There are a number of potential problems that might arise as a result of the characteristics that…
A: Wireless networks have become an essential part of our daily lives, providing convenient and easy…
Q: In the context of software engineering, discuss three compelling reasons in favour of the necessity…
A: Software design is a basic cycle in software engineering, where designers make an arrangement or…
Q: What exactly does it imply when people talk about a "central processing unit"?
A: In this answer, we’ll discuss about central processing unit.
Q: What exactly are you referring to when you say "build a programme" in this context?
A: Here is your solution :
Q: Does it make a difference if a Master File contains data that will be there for all of eternity?
A: There are different types of files that we use to store data for different purposes. Some of the…
Q: Determine the maximum number of physical controllers and displays that can be located. a) Make a…
A: In the modern world, a plethora of physical controllers and displays are available to cater to…
Q: How should a company go about investigating the possibilities offered by cloud computing?
A: With the boundless reception of cloud computing, many companies are investigating its advantages.…
Q: Simplify ¬(m∧(n∨¬m)) to ¬m∨¬n
A: The expression ¬(m∧(n∨¬m)) is a logical formula in propositional logic. It involves two…
Q: Specify a few of the challenges that are faced by global information systems, and describe them…
A: Global Information Systems (GIS) are complex and dynamic systems that allow organizations to…
Q: Could you perhaps explain what exactly is meant by the term "cloud scalability"? In the context of…
A: The term "cloud scalability" describes a system's or service's capacity to effectively manage…
Q: how to build a bookstore database with Entities for Tables Books This entity will store…
A: To build a bookstore database, you can follow these steps: Identify the entities: The entities for…
Q: Why was it decided to create a database with three levels in the first place, and what…
A: What is database: A database is a collection of organized and structured data that can be accessed…
Q: In Checkpoint B, the game will be playable as a two-player game, albeit the competition will be a…
A: Python is often used as a support language for software developers, for build control and…
Q: Which methods of firewall administration are the most efficient? Explain.
A: A crucial component of network security is firewall administration, which includes a variety of…
Q: Refer to image to answer this; Show the runtime stack with the activation record instance for the…
A: There are some syntax errors as mentioned in the image . There are some closing brackets issues…
Q: There are a few different routes that may be taken to get to a basic situation.
A: statement implies that there is more than one way to reach a basic situation. It is a common…
Q: Why is the file space hierarchical?
A: File space hierarchical A Hierarchical File System is a way to organize digital files on a computer…
Q: What is internet? Select one: O a. a single network O b. a vast collection of different networks O…
A: As per bartleby policy im supposed to answer first 3 questions Below are the given answers
Q: What are some of the various software testing techniques that are utilised in the creation of…
A: There are different types of software testing techniques that are utilised in the creation of a…
Q: When should data be removed from a Master file?
A: Master files are central data repositories used by organization to store and run large volumes of…
Please help and show work
Step by step
Solved in 3 steps

- A(n) ____________________ instruction copies data from one memory location to another.Section 3: The Control Unit For the Control Unit, you can simply use an 8-bit input switch or otherwise, which will act as the control wordinput to the data-path (we will not focus on using a control store nor selector). The control word input shouldbe based on the format shown in table 2. These values should be sent to the data-path to accomplish a giventask. In addition to the control word, you will need to implement a way of ensuring the correct register(s) areselected to either input (LOAD) or output (Open Enable) a value. Again, think about using a multiplexer orotherwise. For X0, you will not be using the value, but include it in the design.3X0 C0 C1 B0 B1 F2 F1 F0Table 2: Control Unit control word format. If the base register holds 500 and the limit register is 300, Then the program can legally access all addresses A. From 300 to 500 B. From 500 to 799 C. From 300 to 799 D. None of the above
- The table shows the delays (pico second) of the components in Figure 4.17. Read/write PC I-mem D-mem Register file Mux ALU Adder And, Shifter Sign extend Control 10 250 150 25 200 150 10 50 50 Calculate the delay of the 4 types of instructions. You need to show which components are used in each instruction. Instructions: instruction delay time sd add beq ldSpecify the register contents and flag status as the following instructions are executed. A B S Z CY MVI A, FFH RRC MOV B,A ADD B RAR DCR A HLTWhat will be the values of EDX:EAX after the following instructions execute?mov edx,100hmov eax,80000000hsub eax,90000000hsbb edx,0
- Assume that the contents of the register r16 and carry flag are 0xA5 and 1, respectively. What will be new values for r16 and C after the execution of: (a) lsl r16 (b) lsr r16 (c) rol r16 (d) ror r16 (e) asr r16 (f) swap r16Assume you have three input pins called Pin 1, Pin 2, and Pin 3. Assume you have a single 2-bit register called A. Please draw a circuit that does the following: When Pin 1 is on and Pin 2 is off and Pin 3 is off, then A stores integer 1 in binary. When Pin 1 is off and Pin 2 is on and Pin 3 is off, then A stores integer 2 in binary. When Pin 1 and Pin2 are off and Pin 3 is on, then A stores integer 3 in binary. When Pin 1, Pin 2 and Pin 3 are all off, then A stores integer 0 in binary. No other pin combinations are defined.Q2. [Structural Verilog] Design a 2-bit subtractor unit. Inputs are A and B, and output is S, 2-bits each. As a sub-module you can call the Full Adder module (E Assume this is given to you as library) which takes in 3 inputs (X, Y and Z) and produces 2 outputs (F, C). Write structural HDL
- In this instance, the operand would be the Instruction Register (IR).When a word is divided by a byte, the word must be in the a. DX register O b. BX register O c. CX register O d. AX register1. The _______represents the internal description of the design (how it works). 2. Given a universal 4 bit shift register that shifts the loaded value 0101 to the left one timethe decimal value would be______. 3. Given a universal 4 bit shift register that shifts the loaded value 0100 to the right two times, the decimal value would be______.

