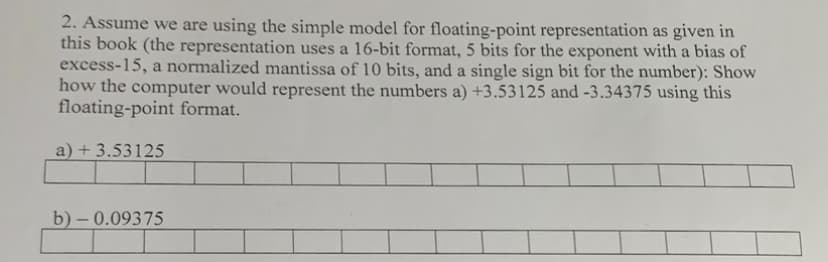
2. Assume we are using the simple model for floating-point representation as given in this book (the representation uses a 16-bit format, 5 bits for the exponent with a bias of excess-15, a normalized mantissa of 10 bits, and a single sign bit for the number): Show how the computer would represent the numbers a) +3.53125 and -3.34375 using this floating-point format. a) +3.53125 b)-0.09375
Q: It's as a result of how powerful computers have become. How can it be shown that computers have had…
A: The use of computers in teaching has a significant impact. Since it is crucial for every people in…
Q: Give the names of the three different kinds of servers that a local bank could use.
A: Here we describe three servers a local bank may utilise. DESCRIPTION Today, technology is…
Q: Can one identify the benefits and drawbacks of different verification methods from the perspective…
A: Introduction: The world is confronting an unfamiliar climb into the new digital scene. We are riding…
Q: Describe the purposes and applications of smartphones, digital cameras, portable and digital media…
A: The answer to the question is given below:
Q: What precisely is a Trojan horse and how does it work? Please provide three examples to support your…
A: A computer virus is a type of computer program that when executed replicates itself by modifying…
Q: Make a distinct contrast between the kinds of typefaces, the font sizes, and the font styles.
A: Required: Make a clear difference between the types of typefaces, the sizes of the fonts, and the…
Q: What exactly is a poison package attack and what does its occurrence mean? If you could give me two…
A: A cyberattack is an attempt to disable a computer, steal data, or use a compromised computer system…
Q: In order to reduce pipeline hazards, it is possible to develop compilers and assemblers that…
A: No, different compilers and assemblers may use different optimization techniques. However, common…
Q: Images are not shareable. When you email your real estate partner, you include images of a home that…
A: The solution is given in the below steps
Q: What kind of authorization, authentication, roles, and mitigation techniques are utilized in small,…
A: Given: Healthcare businesses need to be secure online in order to reduce their risk of ransomware…
Q: Choose the answer option that corresponds most closely to the question. This category includes…
A: The correct response to this query is FALSE. The following are examples of utility applications: -…
Q: What does ransomware really accomplish in terms of computer security?
A: Given: Ransomware infects a compromised computer, encrypting user data and locking it until a ransom…
Q: When the developers make the program in an architecture such that it can be used by other customers…
A: Answer to the mcq's have been provided in the subsequent steps.
Q: The relationship between digital devices and mobile cellphones, as well as the current convergence…
A: The digital devices have brought the revolution in this 21st century.
Q: What kind of processing, and what are its primary components, enables a computer processor to…
A: The fundamental steps a CPU follows to execute a job. The cycle of fetching and running a single…
Q: An understanding of the present convergence of digital gadgets and how those technologies relate to…
A: The question has been answered in step2
Q: Do you agree that "there is no concept of client and server sides of a communication session" in a…
A: As detailed below, a P2P file-sharing programme has no idea of the client and server sides of a…
Q: Programs created for zero, one, or two address architectures are thus more likely to be…
A: Training is more extensive (more number of instrcutions). Solution: Let's analyze the relationship…
Q: hat are your thoughts and feelings on computers and technology in general in your everyday life?…
A: Computers have a substantial effect on our lives. ' Regular use of computers with Internet…
Q: In the majority of retail locations, barcode scanners are already standard equipment. Include one…
A: Introduction: Optical scanners include barcode readers and barcode scanners. These…
Q: What are the most significant distinctions and instances between asynchronous, synchronous, and…
A: The most significant distinctions and instances between asynchronous, synchronous, and isochronous…
Q: Do you agree that "there is no concept of client and server sides of a communication session" in a…
A: The answer of the question is given below
Q: When explaining the DNS, be sure to mention authoritative and root servers, iterated and…
A: the domain name system, or DNS. The World wide web phone book is the Domain Name System (DNS). To…
Q: Using examples, explain the following components of the security triad for a college database that…
A: Confidentiality, integrity and availability, also referred to as the CIA triad, is a model designed…
Q: 28. In a linear linked list, a. the next pointer of each node has the value NULL b. the last node…
A: In this question i will define , what is linkedlist.
Q: text Q.4 Use polyalphabetic ciphers to encrypt plain VERY HAPPY AND BEAUTIFUL GIRL" use key…
A: Q.4 Use polyalphabetic ciphers to encrypt plain text SHE IS VERY HAPPY AND BEAUTIFUL GIRL" use key…
Q: Please do the exercise! Thank youuu
A: Truth Table : A truth table deconstructs a logic function by outlining all possible outcomes the…
Q: How does secret key cryptography function? Please provide a short explanation, maybe with an…
A: Given: How does secret key cryptography function? What is it? Please include a brief description,…
Q: Which steps while utilizing an application to access a database are mostly the same?
A: The vast majority of the services we use on the Internet are brought to us through web database…
Q: Ten well-known computer and information technology companies from across the world, together with…
A: Information technology is the use of computers to create, process, store, retrieve, and distribute…
Q: In many ways, laptop computers and mobile devices seem to be very unlike. Your argument should be…
A: In many ways, laptop computers and mobile devices seem to be very unlike. Your argument should be…
Q: Images are not shareable. When you email your real estate partner, you include images of a home that…
A: Introduction: This pertains to an email message that you are sending to your real estate partner in…
Q: Question 7 Match the items on the left with the ones on the right. Hint: program using sizeof…
A: Hey dear, I hope you will be fine the above questions are done below.
Q: Give real life example of tree topology and where to they use it
A: The answer to the question is given below:
Q: In brief. Avoid Handwritten. Question: Is self weight important at microscale ?Justify the same..
A: Is self weight important at microscale ?Justify the same answer in below step.
Q: Is it feasible to distinguish between various authentication mechanisms in terms of safety?
A: The answer to the question is given below:
Q: Print Floyd’s Triangle in java Program
A: Floyd’s Triangle in java Program:-
Q: How does ransomware function in terms of computer security?
A: Infected computers get infected with ransomware, which encrypts and locks the user's data until a…
Q: What is inheritance with respect to OOP? (You must mention appropriate terminology) In your…
A: Inheritance:- Inheritance is a way to represent the relationship between the objects. This is a…
Q: Since our birth in this century, dubbed as the Information Age, everything from computers to tablets…
A: According to the Cambridge Dictionary, technology is "the study and understanding of the practical,…
Q: What do personal computers and tablets have in common, and what do they share today?
A: Personal Computers : Any compact, reasonably priced computer made for a single user to use at home…
Q: Explain operation of polyalphabetic cipher.
A: Let's see the answer:
Q: 1 For-Loops and Strings It's common to write loops that process characters of strings. Remember that…
A: As per Bartleby's rules, we can only answer the first 3 questions I request you to post Question 4…
Q: Q.4 Use polyalphabetic ciphers to encrypt plain VERY HAPPY AND BEAUTIFUL GIRL" use key 'ANOTHER'…
A:
Q: What are mobile apps exactly, and why are they so crucial?
A: Apps are intended to operate on mobile devices such as tablets, phones, watches, etc. The…
Q: how data breaks down on each layer from top to bottom and from bottom to top in OSI layer
A: OSI LAYER:- Seven layers are used by computer systems to communicate with one another through a…
Q: What actions may be made to improve the security of cloud storage after a data breach? What are some…
A: The cloud is full of benefits, but they're also some risks and dangers. If your business depends on…
Q: What advantages come from knowing how to use computers? Technology improvements benefit society,…
A: Given To know the benefits of computer use and how technology is useful in education, business, and…
Q: impo sprea Б?
A: Spreadsheets are often used in the workplace to store and manipulate data to make informed choices.…
Q: When explaining the DNS, be sure to mention authoritative and root servers, iterated and…
A: DNS authoritative and root servers The 13 DNS root nameservers are known to each recursive…
Step by step
Solved in 3 steps

- Data represented in ________ is transmitted accurately between computer equipment from different manufacturers if each computer’s CPU represents real numbers by using an IEEE standard notation.A(n) __________ is an integer stored in double the normal number of bit positions.Assume we are using the simple model for floating-point representation discussed in the class (the representation uses a 14-bit format, 5 bits for the exponent with an Excess-M, a significand of 8 bits, and a single sign bit for the number): Convert -43.0735 to the floating-point binary representation. (Remember we learned "implied one" format in the lecture)
- Show Steps Please 18. If the floating-point number representation on a certain system has a sign bit, a 3-bit exponent and a 4-bit significand: a) What is the largest positive and the smallest positive number that can be stored on this?system if the storage is normalized? (Assume no bits are implied, there is no biasing, exponents use two's complement notation, and exponents of all zeros and all ones are allowed.) b) What bias should be used in the exponent if we prefer all exponents to be non-negative? c) Why would you choose this bias?Assume we are using the simple model for floating-pointrepresentation as given in the text (the representation uses a 14-bitformat, 5 bits for the exponent with a bias of 15, a normalizedmantissa of 8 bits, and a single sign bit for the number):1. a) Show how the computer would represent the numbers100.0 and 0.25 using this floating-point format.2. b) Show how the computer would add the two floating-pointnumbers in Part a by changing one of the numbers so theyare both expressed using the same power of 2. c) Show how the computer would represent the sum in Partb using the given floating-point representation. Whatdecimal value for the sum is the computer actually storing?Explain.Please answer parts a, b, and c of this question. Assume we are using the simple model for floating-point representation as given in the text (the representation uses a 14-bit format, 5 bits for the exponent with a bias of 15, a normalized mantissa of 8 bits, and a single sign bit for the number): a) Show how the computer would represent the numbers 100.0 and 0.25 using this floating-point format. b) Show how the computer would add the two floating-point numbers in Part a by changing one of the numbers so they are both expressed using the same power of 2. c) Show how the computer would represent the sum in Part b using the given floating-point representation. What decimal value for the sum is the computer actually storing? Explain.
- Please answer both part a and b of this question. If the floating-point number representation on a certain system has a sign bit, a 3-bit exponent, and a 4-bit significand: a) What is the largest positive and the smallest positive number that can be stored on this system if the storage is normalized? (Assume that no bits are implied, there is no biasing, exponents use two’s complement notation, and exponents of all 0s and all 1s are allowed.) b) What bias should be used in the exponent if we prefer all exponents to be non-negative Why would you choose this bias?Explain the term masking. How is it useful for data representation? Explain the concept using an example For a floating-point format with a k -bit exponent and an n -bit fraction, give a formula for the smallest positive integer that cannot be represented exactly (because it would require an n + 1 –bit fraction to be exact).Assume we have a byte system for the fixed number representation (the whole number is presented with 8-bits (one byte) and the fractional part is presented with 2-bits), find the 2's complement of 0110 0010.01 The answer should be formatted as a fractional 2's complement binary number representation with the exact format of the answer that is required of this particular calculation
- Representing 7 bit floating -point Given that the: Sign: 1 bit (MSB)•Exponent: 3 bits•Mantissa: 3 bits (LSB) State/provide the representation in 1s and 0s of the value indicated for each of the following subquestions. Make certain you include all of the bits required for a complete 7-bit representation. Please show all the steps a- 5.2510 B: -2.75101. Assume we are using the simple model for floating-point representation discussed in the class (the representation uses a 14-bit format, 5 bits for the exponent with an Excess-M, a significand of 8 bits, and a single sign bit for the number) Convert -123.075 to the floating-point binary representation. 2. a) What is "Approximation Error" in floating-point representation? b) Why is it happening? c) How can we minimize it? d) How can the character codes be a solution for this?Consider a hypothetical 8 bit floating point machine representation with a sign bit, a 3 bit exponent, and a 4 bit mantissa (se1e2e3b1b2b3b4), where the exponent bias is 3 (add 3 to exponent of number to form machine representation). Recall that actual mantissa has 5 bits, since the leading 1 is not stored on the machine. (a) What is the number ?≈2.718 in this 8-bit format? (b) What is the number that (10100111)2 represents in this 8-bit format? (c) What is the upper bound of the relative error when representing a real number in this 8-bit format?

