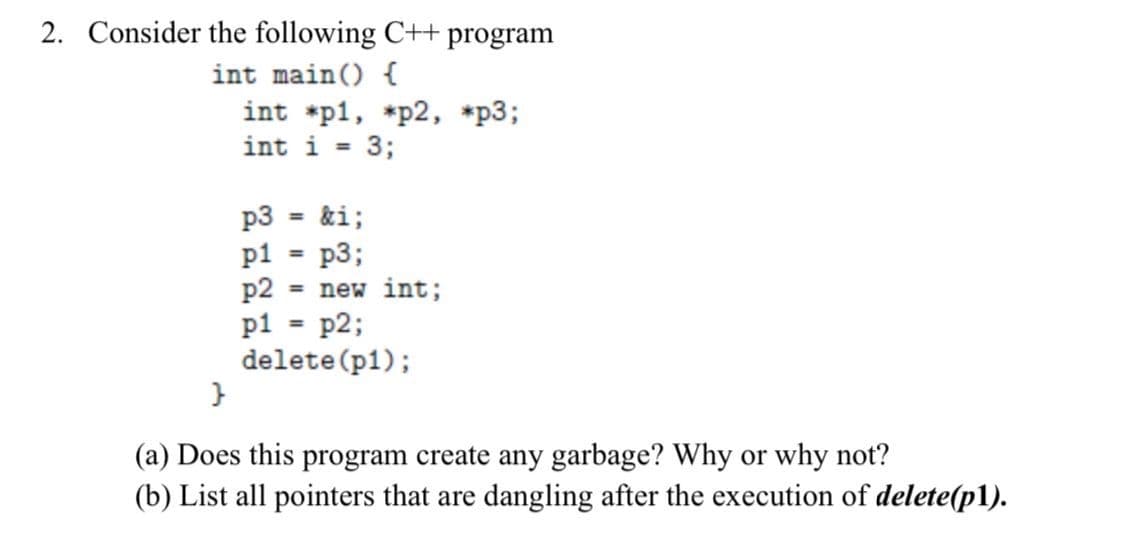
2. Consider the following C++ program int main() { int *p1, *p2, *p3; int i = 3; p3 = &i; p1 = p3; p2 = new int; p1 = p2; delete (p1); }
Q: make all icons as auto-arrange-4
A: As I have already answered the first three sub-parts. Please check on it. Thank You. 4) Make all…
Q: QUESTION 5 What number does val store at the end of the following code snippet? data = [85 64 128…
A: Question (6) given - A MATLAB code snippet is given. What number does the variable val is store at…
Q: What kind of financial repercussions might result from the push toward cloud computing
A: Please find the answer below :
Q: Explain why Solaris and Linux use a variety of locking mechanisms. Describe how spinlocks, mutexes,…
A: Introduction: Explain why Solaria and Linux use a variety of locking mechanisms. Describe how…
Q: Cloud computing and social networking blogs seem to be popular these days.
A: let us see the answer:- Introduction:- Cloud computing: Cloud computing is the on-demand,…
Q: As network administrator, you must construct a new network for newly installed workstations. Which…
A: Solution: Network topology describes how network components are grouped and how connections and…
Q: Determine the kind of communication that is carried out via a wireless local area network (WLAN)…
A: The answer is given below.
Q: Is there a relationship between software design and cohesion and coupling?
A: Cohesion and Coupling: The term "coupling" refers to the interdependencies that exist between the…
Q: What two technologies do the majority of wireless systems use?
A: Introduction: Without the need of wires, wireless technologies and networks allow devices to…
Q: 02 Write a function which will be given as input an array, its size and an integer p. The function…
A: /*Function to rotate arr[] of siz n by p*/void Rotate(int arr[], int p, int n){ /* To handle if d…
Q: To illustrate your understanding of the concepts, please provide a non-technical example of…
A: According to the information given:- We have to define non-technical example of identification,…
Q: What is wireless network "infrastructure mode"? If the network isn't in infrastructure mode, what…
A: The network is considered infrastructure mode when a personal computer is connected to either a…
Q: What are some of the recommended procedures for installing a firewall?
A: Basic System Performance Function is the answer: Process of Management. During the process, the…
Q: What techniques does a social engineering hacker do in order to get knowledge about a user's login…
A: What techniques does a social engineering hacker do in order to get knowledge about a user's login…
Q: It is possible for a computer system to generate and process information in a variety of distinct…
A: Introduction: Similar to people, computers use their brains to process information. The central…
Q: determine the time taken to execute the instruction if the clock frequency of 8085 is 10MHz. Lxi h,…
A: Find the required answer with calculation given as below :
Q: ter architectu
A: Solution - In the given question, we have to tell the two main computer architectures used in…
Q: What would be the overhead of a Code Division Multiple Access scheme with chip sequence of length…
A: Answer :
Q: A technician with a PC is using multiple applications while connected to the internet. How is the Pc…
A: A computer is able to keep track of the data flow between application sessions and has the ability…
Q: en and for how long should a network upgrade be sch
A: Introduction: If you use a lot of smart home devices or have a tendency of buying the latest…
Q: Justify why the following assertion is true: The wait time for a single-channel system is more than…
A: Customers' origins and the whole process are two aspects of a larger whole: When there are more…
Q: Q3.B. Write a VHDL code for the ASM chart below, designing on the highest level possible that…
A: This design have both moore and melay type outputs.Start_timer is melay type output and major_green…
Q: In the process of developing apps for the internet, what function does MVC serve? What are some…
A: Model-View-Controller, or MVC, is widely regarded as one of the most significant advancements in…
Q: One of the most important parts of a personal computer is called the Central Processing Unit, or CPU…
A: As a result: The Central Processing Unit (CPU) is one of the most important components of a…
Q: Talk about frequency multiplexing as well as time division multiplexing (According to commuter…
A: Multiplexing is the sharing of a medium or bandwidth. It is the process in which multiple signals…
Q: Get as much knowledge as you can about the various social media platforms. What precisely is meant…
A: Autonomic Computing is a visionary computer program developed by IBM. This is done to make flexible…
Q: What do you mean by subnet mask?
A: According to the question the subnet cover are by and large utilized for 32 pieces manage used to…
Q: The individual components of a high-level programming language are identified by their names.
A: Start: Input refers to the process of providing the computer with data and instructions. output…
Q: ." IblMessage.integer=" Hello World true .a O false bO
A: "lblMessage.integer=" Hello World Answer - b) False
Q: Determine the kind of communication that is carried out via a wireless local area network (WLAN)…
A: A wireless local area network (WLAN) is a method of linking two or more devices wirelessly. WLANs…
Q: What is the output of the following code? import java.util.*; class Main { public static void…
A: import java.util.*;public class Main{ public static void main(String args[]) {…
Q: Can you try and make a context diagram inventory system interacting with supplier, admin, customer,…
A: Data Flow Diagram Data Flow Diagram (DFD) provides a visual representation of the flow of…
Q: t by the phrase "virtual machine se
A: Introduction: Below the phrase "virtual machine security."
Q: When you talk about "network security," what precisely do you mean by that term? elucidate in…
A: Security threat is any negative event that can lead to unwanted impact to a computer system possibly…
Q: Determine and explain the problems that big data may pose when there is a vast amount of data
A: Introduction: Big Data is an area of research that entails evaluating a large amount of data…
Q: Determine how a new sort of cloud computing, such as software as a service (SaaS), may benefit the…
A: remote cloud network is accessible via the internet. a) SaaS vendors provide users with software and…
Q: Give me 5 vulnerabilities and 5 Risk for Web or database server level control
A: answer is
Q: A savings account is opened with £100000 at the beginning of January. A deposit is then made of…
A: A savings account is opened with £100000 at the beginning of January. A deposit is then made of…
Q: What is the difference between TCP and UDP when it comes to networking? Compare and contrast these…
A: TCP is a connection-orientated protocol, whereas UDP is a connectionless protocol. A key distinction…
Q: What exactly is meant by the phrase "networking"? What are the positive and negative aspects of…
A: answer is
Q: Classify and explain with example the instruction that used to transfer .the data between the…
A: Instructions to transfer data between processor and system in 8085 are: Classification:- MOV M, Sc…
Q: Explain the details about the abstract Class InputStream that includes read(), skip(), available(),…
A: InputStream class is the superclass of all the io classes for example addressing an information…
Q: What is the difference between TCP and UDP when it comes to networking? Compare and contrast these…
A: Introduction TCP: TCP stands for Transmission control protocol which is a connection-oriented…
Q: The individual components of a high-level programming language are identified by their names.
A: Solution: A high-level language (HLL) is a programming language like C, FORTRAN, or Pascal that…
Q: What exactly does it mean to communicate inside a company via a private network?
A: An intranet is a private network inside an organization that securely enables workers to share…
Q: PYTHON!! Solve problem by using PYTHON Program to remove the ith occurrence of the given word in…
A: The question is to write python code for the given problem.
Q: What kind of hardware are necessary for computers to communicate, particularly when several…
A: Explanation: A network is created whenever two or more computers are connected to each other in some…
Q: What two technologies do the majority of wireless systems use?
A: Without the need for wires, wireless technologies and networks make it possible for electronic…
Q: What are the problems associated with networking in the enterprise? Describe the problems as well as…
A: Given: Some of the challenges that might occur from enterprise-wide networking are as follows:
Q: Please enumerate the many ways in which TCP and UDP vary from one another.
A: TCP:It is a connection-oriented networking protocol that enables the exchange of messages between…
Trending now
This is a popular solution!
Step by step
Solved in 2 steps

- Consider the following C++ code: int* length = new int; int* height = new int; *height = 12; *length = *height; Length = Height; delete height; Provide detailed explanations of the effect of each statement. After this code has completed, there is an inaccessible object on the heap and a dangling pointer. What is the inaccessible object and how did it become inaccessible? What is the dangling pointer in this example? Briefly explain the danger associated with dangling pointers?Problem 8. What is the correct syntax of declaring array of pointers of integers of size 10 in C++? a) int arr = new int[10]; b) int **arr = new int*[10]; c) int *arr = new int[10]; d) int *arr = new int*[10];Write a C program that uses the following: a main() to read two integer values from the user, val1 and val2, and prints the returned value from swap().a swap() that uses call by reference (takes the addresses into pointers) to swap values, and prints their values after the swap "num1 = # and num2 = #". This function returns the largest of the two values. If these are equal, it returns their sum.
- In C++, how simple is it to duplicate an array of shared pointers into a new array? Create a list of potential solutions to the issue at hand. Do the objects controlled by a shared pointer also get copied when it's copied? ExplainWrite a c++ program that collects from the user(keyboard) the first few lines of Hamlet. Inputting text lines into the program should use cin.getline( …..) function. The program should contain the following parts: an array of char pointers *ptr[15] – there are more char pointers than text lines declare a temporary char pointer (*tmp) declare a char Phrase[120] which is used to store temporarily each input line of Hamlet each new line of text is stored in Phrase and should be copied onto the heap and its memory location assigned sequentially to ptr[i]. Recall that you must allocate memory on the heap via new memory function. after collecting all lines of text – print all input text lines (track # of input lines with int LineCnt) change each uppercase letter to lowercase on the entire text Hamlet print all text lines containing a punctuation symbol(; , . ?) print all text lines that contain the letter ‘d’ copy line #10 to the end and print again all text lines compress…3.) Write a C++ program that will prompt the user for the size of a list of integers. Your program will 1. dynamically allocate an array of that size and allow the user to enter the values. 2. Your program will then go through the list and copy all even numbers to another dynamically allocated array. The functionality of 1 and 2 need to be accomplished by separate functions. 4.) Redo question number 3 with these changes. Instead of dynamically allocating an array to store the data, your program will will an STL array. Even numbers will also be copied to an STL array. The input of the data and copying of even numbers will require the program to start at the beginning of the array and walk thorugh the values to the end. This must be done using iterators.
- Write a program in C++ that contains code addressing the following: (New code and with detailed steps!) a. Create an integer array of 100,000 items (static binding – before compiling) b. Create the same large array on the run time stack (in a function) c. Create the same large array from the heap (dynamic memory – dynamic binding). Call each of the subprograms 1,000,000 times and output the time required by each to finish all 1,000,000 calls. Which was the fastest? Here is code for calling time. #include <time.h> //in main() clock_t start = 0, end = 0; //variables start = clock(); //calls time function stores result in start end = clock(); // calls time function stores result in end //display the time by subtracting the start from the end //displays in clock ticks.Solve the following C++ Program. you are supposed to DYNAMICALLY create 2 arrays of length 5 using pointer, Then take values from the user and put those values in ONE of the dynamic arrays and COPY those values from the first array to the second Array.Can anyone convert this c++ code to python? //THIS PROGRAM IS CREATED TO DEMONSTRATE THE OPERATIONS PERFORMED ON STACK & ITS IMPLEMENTATION USING ARRAYS #include <iostream>#include <stdio.h>#include <conio.h>#include <stdlib.h>#include <process.h> //Defining the maximum size of the stack#define MAXSIZE 7 using namespace std; //A class initialized with public and private variables and functionsclass STACK_ARRAY { int stack[MAXSIZE]; int Top; public: //constructor is called and Top pointer is initialized to -1 when an object is created for the class STACK_ARRAY() { Top = -1; } void push(); void pop(); void traverse(); }; //This function will add/insert an element to Top of the stackvoid STACK_ARRAY::push(){ int item; //if the top pointer already reached the maximum allowed size then we can say that the stack is full or overflow if (Top == MAXSIZE-1) { cout << "\nThe Stack Is Full"; }…
- Can anyone convert this c++ code to python? //THIS PROGRAM IS CREATED TO DEMONSTRATE THE OPERATIONS PERFORMED ON STACK & ITS IMPLEMENTATION USING ARRAYS #include <iostream>#include <stdio.h>#include <conio.h>#include <stdlib.h>#include <process.h> //Defining the maximum size of the stack#define MAXSIZE 7 using namespace std; //A class initialized with public and private variables and functionsclass STACK_ARRAY { int stack[MAXSIZE]; int Top; public: //constructor is called and Top pointer is initialized to -1 when an object is created for the class STACK_ARRAY() { Top = -1; } void push(); void pop(); void traverse(); }; //This function will add/insert an element to Top of the stackvoid STACK_ARRAY::push(){ int item; //if the top pointer already reached the maximum allowed size then we can say that the stack is full or overflow if (Top == MAXSIZE-1) { cout << "\nThe Stack Is Full"; }…C++ By defining a dynamic allocation for pointer array, ask the user to enter some numbers and then return a sorted list of those numbers.1. a) When a function is called in a given running program, an _____________ is created in the stack section of the virtual address space of the program that stores all the variables local to the function 1.b) Will the code below change the value of x? Explain why your answer is correct. All codes in c++ #include <iostream> using namespace std; void change(int); int main() { int x = 10; change(x); cout << "x = " << endl; return 0; } void change(int n1) { n1++; }

