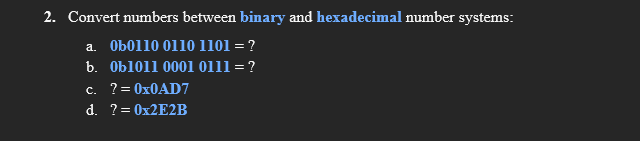
2. Convert numbers between binary and hexadecimal number systems: a. Ob0110 0110 1101 = ? b. Ob1011 0001 0111 = ? c. ?= 0X0AD7 d. ?= 0X2E2B
Q: Draw a linked list representation of the expression (a) x²y³ + 3x?y + y'z + 2x?y – 2y'z (b) 4x?y –…
A:
Q: In your opinion, what are ARM and core i3 architectures' main points of agreement and disagreement?
A: The Core i3 processor features integrated graphics. The Core i3 processor is capable of supporting…
Q: QUESTION 9 We are given a connected graph G with costs ci, ) on edges. Assume all costs are positive…
A: We need to check if the minimum spanning tree remains the same after costs are squared. ***As per…
Q: Why is it better to programme in a compiled language rather than one that is interpreted? Would you…
A: Introduction: Compilers convert compiled languages into machine code that the processor can execute.…
Q: Q1) Draw the ladder diagram for the logic circuits A&B А: A AB в AB AB AB
A: Determining the ladder diagram for the given logic circuit.
Q: Which features of Azure Domain are particularly useful? Beyond Microsoft, there are several more…
A: There are lot of features which azure domain offers . Some of them are listed below : 1. Identity…
Q: It is a static structure diagram that describes the structure of a system by showing the system's…
A: NOTE :- As per our company guidelines we are supposed to answer only first 3 sub-parts. Kindly…
Q: Character devices are usually faster in transmitting data than block devices. Is this statement true…
A: Introduction: Character devices, like as tape drives or serial ports, do not have physically…
Q: To prevent print the result statement in MATLAB we can put in the end.
A: A semicolon(;) indicates the end of a statement. If we want to suppress and hide the MATLAB output…
Q: Problem : For values x=[ 0.5 :25] , plot yl=2 x +1 and y2= x+ 1. Use different colors and line…
A: Given :
Q: Cause Effect Material Process Material Defects Wrong Order Problem or Defect Statement No Training…
A: This is a fishbone or cause and effect diagram. It is used to root cause analysis. The main problem…
Q: When implementing PPP authentication, you have the choice of utilising either PAP or CHAP as your…
A: Introduction: Password Authentication Protocol (PAP) and Challenge-Handshake Authentication Protocol…
Q: A bicycle costs $50 to hire for the first day and $40 for each extra day. If Cn is the cost of…
A: Let's see the solution
Q: The Positive Ones There are different kinds of numbers, but among them all, the most commonly used…
A: As given, we need to write a C++ program that takes four numbers as input and count all the positive…
Q: The distinctions between software and web engineering are many
A: The software engineering is a field that deals with creation of software's while as web engineering…
Q: a = O 2 4 6 1 3 7 9 8 1 11 2 13 4 0 6 V = 0 2 4 6 3 7 9 8 1 11 2 13 4 0 6
A: Command Window is the place where we enter commands at the command line, indicated by the prompt…
Q: Which features of Azure Domain are particularly useful? Beyond Microsoft, there are several more…
A: Introduction: Azure Active Directory (Azure AD) is a cloud-based identity and access management…
Q: I need help sorting a stack in DESCENDING ORDER so [44,32,21,11,0,-4,-5,-12,-24].
A: is_empty(S) : Tests whether stack is empty or not. push(S) : Adds new element to the stack.…
Q: An application programming interface (API) is referred to as a "programming language" in computers.…
A: Introduction: API stands for application programming interface (API) several software intermediaries…
Q: lowchart of this pseudocode using online chart
A: Due to the rules given to us, I can solve only one question at a time. So, the flowchart of the…
Q: Compose a list of two external obstacles to effective listening and two internal obstacles to…
A: Answer the above questions are as follows:
Q: As a result of our findings, we believe Flynn's taxonomy has to be raised by one level. High-level…
A: A high-level computers a PC with an undeniable level computational limit contrasted with a broadly…
Q: Compare Agile and XP as systems development methods.
A: Introduction: Although Agile techniques depend on well-defined procedures (change, risk, analysis,…
Q: n computing, an application programming interface (API) is referred to programming language." What…
A: Lets see the solution.
Q: Is there a way to lessen the overhead caused by page table shadowing?
A: The page table shadowing is also known as shadow page table.
Q: Is increasing the amount of duplication in a message beneficial or detrimental?
A: Any record in your marketing database that inadvertently shares data with another record is…
Q: These are some common challenges of distributed systems Scalability, Availability, Observability…
A: Option 1
Q: Create a program that declares variable to hold number of eggs of a chicken. Your program will…
A: import java.util.*;public class Main { public static void main(String[] args) { Scanner scan =…
Q: the F/C pin is placed at a logic 1 level, the crystal oscillator is disabled. Where is the timing…
A:
Q: What are the four most important roles of routers?
A: Introduction: When two or more packet-switched networks or subnetworks are linked together by a…
Q: How can a programmer get out of an unending loop?
A: The following is an explanation: The response is as follows: Detecting and escaping infinite loops…
Q: What is the distinction between Mealy state machines and Moore state machines?
A: Intro A Mealy Machine alters its output in response to the current condition of the machine and the…
Q: Discuss the scheduling of processes and threads in comparison and contrast.
A: A process is a living, breathing program. It includes the program counter, process stack, registers,…
Q: ebserver conn
A: Introduction The HTTPS protocol is used to create an encrypted connection between the browser and…
Q: d by what two key
A: IntroductionAggregation is the process through which one class (in the form of an entity reference)…
Q: Do you know what would happen if an instruction was rejected? When compared to a hardware-managed…
A: Page 30 contains the following information when an instruction is written to it: It tries to locate…
Q: When ICMPv6 Neighbor Solicitations are issued, it seems that they are transmitted as a multicast…
A: Introduction: Internet Control Message Protocol Version 6: Neighbor discovery defines five different…
Q: Based on direction and edge-weights there are four types of graphs. Give a practical example for…
A: We are going to learn 4 types of graphs and their real life examples. Please refer to the image for…
Q: Consider the following declarations: class xClass { public: void func(); void print() const ; xClass…
A: a. The constructor name is the same as the class name. In the given code, we have 2 constructors,…
Q: Here, you'll learn about dynamic scoping, its use cases, the performance consequences of employing…
A: INTRODUCTION: Dynamic scoping: The term dynamic refers to something that is constantly changing.…
Q: Convert the following if block to select case If x =10 and x <=15 then IblRes.Text = "Between 10 and…
A: If x<10 then LblRes.text="Below 10" else if x>=10 and x<=15 then LblRestext ="Between…
Q: Are you certain that employing wireless applications for mistake correction is more effective? You…
A: Introduction: "Yes," says the author, "the error correction is best employed with wireless…
Q: A command-line interface or a graphical user interface? Why?
A: ANSWER:-
Q: Character devices are usually faster in transmitting data than block devices. Is this statement true…
A: This statement is true Character devices are usually faster in transmitting data than the block…
Q: 1.) What is wrong in the given statement below? fmName.text = 123 Select one: a. text should be…
A: b. 123 should be “123”
Q: What happens if the sender receives an acknowledgment before the window size in Go back N arq…
A: GO-BACK-N ARQ utilizes the protocol pipelining thought, in which numerous edges can be conveyed…
Q: Exactly when should a network update be put on the calendar?
A: Introduction: Updates to network provider settings allow your network provider to change the network…
Q: What are the important things you have learn on this subject. Explain briefly machine learning and…
A: machine learning and DIGITAL AND DATA COMMUNICATION
Q: What are the advantages of keeping cable clutter to a minimal in a rack?
A: Introduction: Cord or cable clutter occurs when electrical cords get tangled on your desk. This…
Q: What are the most effective methods for assuring the resilience and availability of a LAN network?
A: Introduction: (Local Area Network): The network that connects two or more computers. An example of a…
Step by step
Solved in 2 steps

- A(n) __________ is an integer stored in double the normal number of bit positions.What decimal value does the 8-bit binary number 10011110have if:1. a) It is interpreted as an unsigned number?b) It is on a computer using signed-magnituderepresentation?2. c) It is on a computer using one’s complementrepresentation?3. d) It is on a computer using two’s complementrepresentation?4. e) It is on a computer using excess-127 representation?Convert the following numbers from their given base to decimal:a. 0.10010012b. 0.3A216c. 0.2A1122. What is the decimal value of the following binary numbers?a. 1100101.1b. 1110010.11c. 11100101.13. a. What is the ASCII representation of the numeral -3.1415 in binary?b. What is the ASCII representation of the numeral -3.1415 in octal?c. What is the ASCII representation of the numeral -3.1415 in hexadecimal?d. What is the ASCII representation of the numeral -3.1415 in decimal?4. What character string does the binary ASCII code1010100 1101000 1101001 1110011 0100000 1101001 11100110100000 1000101 1000001 1010011 1011001 0100001
- What decimal value does the 8-bit binary number 00010001have if: 1. a) It is interpreted as an unsigned number?2. b) It is on a computer using signed-magnituderepresentation?3. c) It is on a computer using one’s complementrepresentation?4. d) It is on a computer using two’s complementrepresentation?5. e) It is on a computer using excess-127 representation?For any given base, what does 10 represent? a) The base number -1 b) The base number +1 c) The base number itself (base raised to the 1 power) d) Depends on the base.What is the 17th decimal digit in the decimal representation of 14/11? a. 7 b. 8 c. 3 d. 2
- Fill in the missing values in this chart of positional values for the rightmost four positionsin each of the indicated number systems:decimal 1000 100 10 1hexadecimal ... 256 ... ...binary ... ... ... ...octal 512 ... 8 ...Convert IEEE Single-Precision Binary Format Real number 11000100101001000010101000000000 to decimal. Please show all the steps. a) [1] What is the sign? b) [1] What is the biased exponent value? c) [1] What is the unbiased exponent value? d) [2] What is the normalized representation of the number in BINARY? e) [1] What is the unnormalized representation of the number in BINARY? f) [1] What is the decimal value of the whole number part of the number? g) [2] What is the decimal value of the fractional part of the number? h) [1] What is the real number in base 10Answer the following Binary Multiplication: *similar to decimal multiplication* 5. 10 x 10 = 6. 101 x 10 = Binary Division: *Hint: very similar to decimal division* 7. 100 / 10 = 8. 1010 / 100 =
- a) How many bytes are needed to represent the following hex number: 0x77 88 f0 19add x5, x5, x8Every binary digit must be either 0 or 1 or X. If it appears in multiple bits, then you must input multiple bits, e.g.: 0011xx11Control Signal: ValueWhat is the minimum number of binary bits needed to represent the following unsigned decimal integer? 2134657

