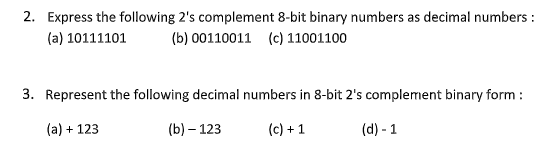
2. Express the following 2's complement 8-bit binary numbers as decimal numbers: (a) 10111101 (b) 00110011 (c) 11001100 3. Represent the following decimal numbers in 8-bit 2's complement binary form: (a) + 123 (b) - 123 (c) +1 (d)-1
Q: Please Enter the Program Code: 4 Please Enter the Number of Students: 5 Please Enter the Names of…
A: For the given program using sorting to string C++ Code is given below:
Q: ANSI stands for American National Standards Institute, which is the organisation responsible for…
A: The American National Standards Institute (ANSI) and the International Organization for…
Q: Q4) Write the result (value of B) in the following groups of commands? >> >> >> A=[1 2 3;... 456;…
A: The question is to write the result of the commands (value of B).
Q: dentify three (3) software that may help you electronically maintain your research diary,…
A: Mendeley History Mendeley was named after the biologist Gregor Mendel and chemist Dmitri Mendeleev,…
Q: There is power associated with every position and every career. In addition, having authority comes…
A: Start: Software engineers should make analysis, specification, design, development, testing, and…
Q: What are the most current technical developments in information technology, information systems, and…
A: The facilities and services required by a business are known as infrastructure. Coverage includes…
Q: PROBLEM: Based on the given class diagram, create a class implementation using C++. Voters -…
A: Code: #include <iostream>using namespace std; class Voters{ private: string…
Q: What is the internet of things and how is it used?
A: The Answer is in given below steps
Q: How does the field of computer science differ from the other academic fields in what ways? What…
A: Computer science: Computer science is concerned with the software and software systems that run our…
Q: Write a 6 - 9 research paper describing how you would design a super computer with the following…
A: Supercomputing has a proud history in the United States. Ever since the 1940s, our nation has been a…
Q: Consider the assembly code below MOV A,#4AH CPLA What is the final hexadecimal value stored in the…
A:
Q: Programming is done in a variety of methods. Before deciding on a programming language, what factors…
A: Here are the seven key considerations we examine when deciding on the best programming language for…
Q: Software quality assurance testing is the topic. Assume you're working on a website for a university…
A: software evaluation: Software testing is the process of examining and verifying that a software…
Q: When referring to software, this refers to its most fundamental form. What is it, and could you…
A: Simply, the software instructs a machine on how to work. Software is a collection of instructions,…
Q: It's important to know what precisely is expected from the software development project.
A: All physical and intangible outputs delivered within the scope of a project are referred to as…
Q: Create a list and provide a short description of the primary categories of systems used by the…
A: Describe the organization's key systems. Four systems are significant. TRANSPORTATION PROGRAMS: TPS…
Q: Suppose that f(5) = 7,f(9) = 5,f'(5) = 3, f'(9) = 6 and f" is continuous. Find the value of the…
A:
Q: context diagram for event booking project
A: Here below i am draw context diagram for event booking project:…
Q: Details about 10 well-known international information technology and computer science businesses…
A: An information technology company can be denoted as a company that provides information technology…
Q: TEST CASES: You have an Active Voters account! Your full name is Juan Dela Cruz. You are 25 years…
A: Please find the answer below :
Q: Q4)write a M-file to calculate area and circumference of circle, If the user runs this program, he…
A: fprintf("please enter value of radius\n") R = -5; while R < 0 R = input("R = "); if (R < 0)…
Q: Having the ability to learn new programming languages is helpful even if a programmer already has…
A: Given: Why is it necessary for a programmer to be able to learn new languages if he or she already…
Q: Question 6a: Convert the following NFA into a DFA. Follow the process described in the book and…
A: Answer has been explained below:-
Q: Internet is considered as the pinnacle of information and communication technology because of the…
A: Information and communication technologies (ICT): The abbreviation "ICT" refers to a set of…
Q: It is recommended that ten organisations related to computer science and information technology,…
A: Computer science and Information technology: Computer science is the study of the design and…
Q: A typical software project that follows the software development life cycle may be managed using WBS…
A: A typical software project that follows the software development life cycle may be managed using…
Q: Construct an - NFA for the regular expression 00* + 1.
A: Q: Create NFA for given expression
Q: What is IP spoofing, and how does it work? If so, how does it compromise security?
A: Answer in step 2
Q: What does a software product not have to include in order to be efficient? Explain?
A: Efficiency testing: Efficiency testing determines how many resources a software needs to execute a…
Q: Ten well-known global IT and computer science businesses should be included, along with their…
A: Global IT and Computer science businesses: World of Computer Science and Information is an…
Q: What are the advantages of using a life cycle strategy?
A: Given: A life cycle describes the steps that an individual organism goes through from conception to…
Q: How did the internet of things originate, and what are its uses?
A: Encryption: In fact, the Internet of Things (IoT) is a network of physical objects with sensors and…
Q: What's the point of learning programming languages in the first place? What is the best level of a…
A: We need to discuss: What's the point of learning programming languages in the first place? What is…
Q: Find out which tools and techniques are going to be used in the system's construction.
A: Tools and techniques: A tool is a tangible entity, such a template or software programme, used to…
Q: 1. Write a program that performs arithmetic division. The program will use two integers, a and b…
A: Declare variables a, b and c for division Take inputs from user Print the result
Q: Why is it that the internet is regarded as one of the most outstanding instances of information and…
A: ICT is an acronym for - "information and communications technology," and it refers to the…
Q: 4. Find the values to be loaded in the THO and TLO register in mode-2 of the 8051 microcontroller…
A: The answer is given in the below step
Q: How to keep your network safe from phishing assaults What can we do to prevent another attack of…
A: Intro: => Phishing tricks are one of the most widely recognized strategies for assault you…
Q: Is it feasible to evaluate software quality when the client continually altering what the product is…
A: Check the following statement: Is it feasible to evaluate software quality when the client…
Q: Many businesses store all of their critical data on cloud storage providers. What makes you believe…
A: Benefits Cloud storage saves money. Sсаlе economies. Cloud vendors acquire storage and pass the…
Q: Provide three guiding principles for the development of system requirements, and briefly discuss…
A: Given: The configurations required for the software to run at peak performance are known as system…
Q: Question 1 Q17. Output synchronization between the LC-3 and the monitor takes place by: Your answer:…
A: According to the information given:- We have to choose the correct option to satisfy the statement.
Q: What does the term "computer programming" truly mean? Before deciding on a computer programming…
A: Given: A method of instructing machines on what to do next is known as computer programming. This is…
Q: Write a subroutine in Assembly language (without timer) to put a delay equal to roll number (last…
A: We need to write an assembly code for the given scenario.
Q: What exactly is meant by the term "ForkJoinTask"? What are the key distinctions between the…
A: ForkJoinTask is a thread entity which is very lightweight than normal threads and it begins…
Q: Problem: Write a C++ program that would implement the function called filterString which accepts a…
A: #include <bits/stdc++.h>using namespace std; int filterString(string s){ int n=s.size();…
Q: So that we can do what, everyone in the software development team should be involved in the planning…
A: Given: The process through which computer programmers generate new computer programmers is known as…
Q: Improve your knowledge of cloud computing, social media blogging, and other important topics.
A: Given: Gain a deeper understanding of cloud computing, social media blogging, and other areas that…
Q: Name: Be Anne Nickname: Reese Phone: +63298612345 Fav Film: Doctor Strange Hobby: Collecting Stamps…
A: Answer:
Q: ation on the
A: Introduction: The application of engineering principles to the design, development, and support of…
Step by step
Solved in 2 steps

- A(n) __________ is an integer stored in double the normal number of bit positions.Convert the decimal number -19.625 to a floating-point number expressed in the 14-bit simple model given in your text (1 bit for the sign, 5 bits for exponent using excess-15 notation, and 8 bit mantissa with no implied bit). Question 16 Convert the following decimal Real number to fixed point binary: 19.62510 Assume 8 bits for the whole part and 8 bits for the fraction1) Using IEEE 754 representation for single precision floating point, give the 32-bit binary encoding for the numbers below.Show the sign, exponent, and mantissa (significand).a. -2.40625b. 11.2265625 2) Given the following binary number: 1101.0111, what will be its decimal numberequivalent?
- 1)Using IEEE 754 representation for single precision floating point, give the 32-bit binary encoding for the numbers below.Show the sign, exponent, and mantissa (significand).a. -2.40625b. 11.2265625 2) Given the following binary number: 1101.0111, what will be its decimal numberequivalent?2. What is the 2s complement of the following binary numbers? a. 01100 b 10001 3. Add the following 5-bit signed binary numbers together. Please indicate if overflow occurs. a. 00100 + 11000 b. 01010 + 01000 c. 11010 + 100111. Assume numbers are represented in 8-bit two's complement Show the calculation of the following: a) 5 + 10 b) 5 – 10 c) -5 + 10 d)-5 – 10 2. Represent the following decimal numbers or values according to the given requirements: a) +4 in both binary sign/magnitude and two's complement b) -6 in both binary sign/magnitude and two's complement c) -85 in two's complement d) +52 in two's complement 3. Find the following differences using twos complement arithmetic: a) 001000 – 110111 b) 10100101 – 011110 c) 100100001011 – 101010110011 d) 10011011 – 10100101
- 1) Answer the following questions: What is the greatest magnitude negative number one can represent in n-bit 2'scomplement code? 2)Show the 8-bit binary signed-magnitude representation for the following decimalnumbers: -109 10 +43 10 3)Perform the following additions and subtractions. Assume the numbers arestored in signed-magnitude base 2 representation. -1010111 + -100111. Using even parity, add parity bits to the following bit patterns: a. 0110 100 b. 1011 011 c. 0000 000 2. Using odd parity, add parity bits to the following bit patters: a. 0110 100 b. 1011 011 c. 0000 0001. List the octal and hexadecimal numbers from (16)10 to (32)10.2. Convert the following numbers with indicated bases to decimal.(a) (4310)5(b) (123)8(c) (2F A)16(d) (212)33. What is the largest binary number that can be expressed with:(a) 8 bits,(b) 10 bits,(c) 16 bits.In each case, write their decimal and hexadecimal equivalents.4. Determine the base of the numbers for the following operation to be correct: 54/4 = 135. Convert the hexadecimal number 68BE to binary, and then convert it from binary to Octal.6. Convert the decimal number 431 to binary in two ways:(a) Convert directly to binary.∗Engr. Sheraz Ali Khan, PhD 1 (b) First convert it into hexadecimal and then from hexadecimal to binary. Which is faster in youropinion?7. Express the following numbers in decimal:(a) (10110.0101)2(b) (26.24)8(c) (F AF A.B)168. Solve the following conversion problems:(a) Convert the decimal number 27.315 to binary.(b) Calculate the binary equivalent of 2/3 to eight places after the binary point.…
- a) Use the two’s complement binary representation to represent each of the following integers as 10-bit binary numbers. i) -13710 ii) 14510 iii) -15810 iv) 16710 v) -11510 b) If an 8-bit binary number is used to represent an analog value in the range from 0 to 100kg, what does the binary value 011001002 represent?Convert each of the following bit patterns into real numbers. Assume the values are stored using the floating point bit model. 00111111100000000000000000000000 = 11000001000101101011100001010010 =31 Convert the hexadecimal IEEE format floating point single precision number 0x40200000 to decimal: First convert hex to binary (Provide a space between four bit groups. Example 111 1010 not 1111010) Sign bit Exponent in decimal after removing excess 127. Just the exponent. Example 3 not 23 Mantissa or Significand (Provide a space between four bit groups. Example 111 1010 not 1111010) Put it together and convert to decimal

