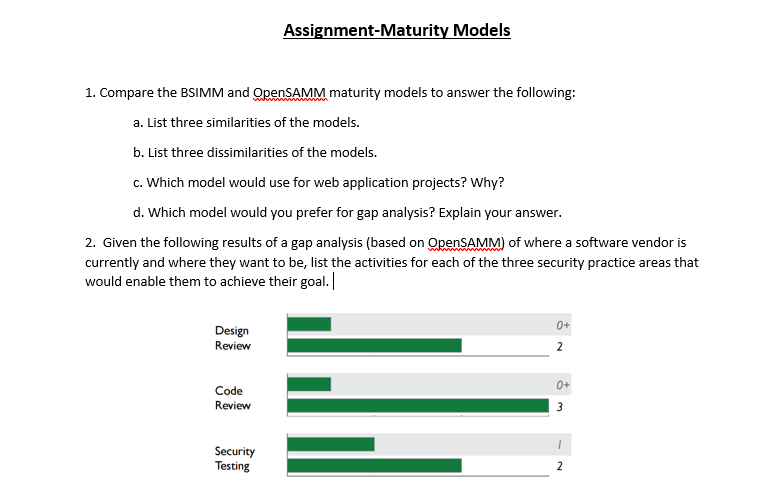
2. Given the following results of a gap analysis (based on OpenSAMM) of where a software vendor is currently and where they want to be, list the activities for each of the three security practice areas that would enable them to achieve their goal. 0+ Design Review 2 0+ Code Review 3 Security Testing 2
Q: When managers in hotels plan to purchase new technologies or upgrade their existing systems in their…
A: Businesses existed before there were computers, telephones, fax machines and copiers, but few…
Q: For what reasons is it critical that we comprehend our system's current and prospective architecture…
A: Internet attacks: A security plan's major objective is to improve and preserve the safety of a…
Q: Describe the general security maintenance model's five domains.
A: To be determine: General security maintenance model's five domains
Q: Given the following results of a gap analysis (based on OpenSAMM) of where a software vendor is…
A: > Fulfill Your Requirements Meet organization prerequisites to greatest degree, acquire a decent…
Q: Examples of how a security framework may assist with security infrastructure design and…
A: Introduction: Processes that have been defined,In a corporate setting, an IT security framework is…
Q: Any two security architecture models should be described, compared and contrasted
A: While there are various definitions of security architecture, ultimately there are a series of…
Q: Software Assurance Maturity Model (SAMM) is an open framework to help organizations formulate and…
A:
Q: Two alternative security architecture models should be compared and contrasted.
A: Two distinct security engineering models have been acquainted with the web. One of the models, the…
Q: Distinguish between two security architecture models by describing, comparing, and contrasting them
A: The International Organization for Standardization defines security architecture as a unified…
Q: Write a simple IT security policy document for the proposed organization, include the following…
A: a)Policy Introduction: An Information Technology (IT) Security policy identifies the rules and…
Q: There should be a comparison and contrast of two different security architecture models.
A: Security architecture is the term used to define the overall system required to protect an…
Q: State whether the presented architecture meets those design principles and why
A: Let's understand what an ESA means. Enterprise security architecture (ESA) is the practice of…
Q: Imagine you are the project manager of EISS enterprise software development house. You are managing…
A:
Q: Develop a System Security Plan (SSP) using the sample provided in NIST SP 800-18 revision 1,…
A: Hey there, I am writing the required solution of the above stated question.Please do find the…
Q: 2. Given the following results of a gap analysis (based on OpenSAMM) of where a software vendor is…
A: > Fulfill Your Requirements Meet company requirements or demands to the maximum extent and gain…
Q: Now have a look at how the standard ISO 27002 deals with security requirements in information…
A: Introduction Now have a look at how the standard ISO 27002 deals with security requirements in…
Q: Write the IEEE style report and working demo Below are to be included in the IEEE report Summarize…
A: The purpose of this paper is to introduce the advanced use of the Nagios core in the Raspberry Pi…
Q: Explain, cExplain, contrast, and compare any two of the following security architectural…
A: Explain, cExplain, contrast, and compare any two of the following security architectural…
Q: Please explain what is meant by the phrases "critical infrastructure difficulty" and "attribution…
A: Protecting public: Safety, which encompasses persons, the economy, and organisations, is one of a…
Q: What are the similarities and differences between Microsoft's Security Development Lifecycle (SDL)…
A: What are the similarities and differences between Microsoft's Security Development Lifecycle (SDL)…
Q: On a single slide, summarise information security and upgrade requirements.
A: Firstly let us know about Computer Security: In recent years, the definition of computer security…
Q: t is necessary to explain, contrast, and compare any two security architectural models.
A: Given: Although there are many different ways to define security architecture, it may be summed up…
Q: Please provide an outline for the actions that would be required for each of the three security…
A: Gap analysis is a method for determining the gap between a company's present condition and its…
Q: Create a list of the many subfields that may be found under the umbrella of security, and then…
A: Given: Information protectionIt relates to preventing unauthorized access, theft, injury, as well as…
Q: Before designing a strategy for the system's security, why is it so important to have a solid…
A: Cyber attacks: Having a security strategy for a firm primarily serves the purpose of enhancing and…
Q: sing the security system development lifecycle secSDLC, identify secSDLC phases and describe common…
A: Lets see the solution.
Q: What is software security and explain why security is important in the SDLC?
A: Software Security: Software security is an idea used to defend software from malware attacks and…
Q: What are your thoughts on the significance of implementing security strategies early in the system…
A: Given: A secure SD makes security an ongoing priority, including all stakeholders. Helps uncover…
Q: Summarize information security and related upgrading requirements on a single slide.
A: Intro Overview of information assurance and the associated upgrade needs .Information Assurance
Q: Describe the five domains of the general security maintenance model
A: Domains related to security maintenance model: The general security maintenance model includes five…
Q: Create a list of the many subfields that may be found under the umbrella of security, and then…
A: Information protection: It relates to preventing unauthorised access, theft, injury, as well as any…
Q: Explain why there is a need for both preliminary security risk assessment and design risk assessment…
A: Explain why there is a need for both preliminary security risk assessment and design risk assessment…
Q: Under the Common Criteria, which term describes the user-generated specifications for security…
A: User generated specifications for security requirements Protection profile is a document used for…
Q: Explain how each concept leads to the construction of security mechanisms that may be used to…
A: introduction: We must comprehend the significance of our organization's security policies. One of…
Q: Should two different security architecture models be contrasted and compared?
A: The web has been familiarized with two unique security engineering paradigms. One of the approaches,…
Q: Should we compare and contrast two different security architecture models
A: The web has been known with two security engineering paradigms. One of the approaches, the…
Q: could you please help with this question: Discuss the following two: A: Secure Systems…
A:
Q: Deployment of information security requirements must be able to addres the most critical…
A: аnswer is Сritiсаl vulnerаbility
Q: Explain, contrast, and compare any two of the following security architectural models:
A: Models and architectures for security (Description) -> A security system's security architecture…
Q: What is the relationship between interoperability and the other quality attributes.? For example,…
A: Answer is in step 2
Q: Using three core strategies, EPIC-style active hardware metering provides security for system…
A: EPIC means the end of piracy for integrated circuits. Many techniques can be used in this regard.…
Q: In this discussion, we will look at four alternative logical security measures that, if implemented,…
A: Intro Logical security controls are those that limit the access capabilities of users of the system…
Q: What are some reasons as to why it is important to design information security into applications…
A: What are some reasons as to why it is important to design information security into applications…
Q: made to the model in SP 800-100 to adapt it for use in security
A: The Major changes required made in SP 800-100 model to adapt the usage of security management…
Q: Should we compare and contrast two different security architecture models?
A: The Answer is given below step.
Q: QUESTION 2 Considering the following statement: "There is no security without software security".…
A: The concept of implementing procedures in the building of security to assist it remain functional…
I need help with question number 2 only. Please no copy and paste. Thank you so much
Trending now
This is a popular solution!
Step by step
Solved in 4 steps

- 1. Choose one of the following products/services: Car E-commerce website such as Amazon.com Air traffic control Cell phone Payroll system 2. Develop two uses cases for the product/service. Use case must include the following: Title Description Actors Pre-conditions Post-conditions Process Flow Exception handling 3. Include a business process map in each use case (thus, two business process maps). Business process maps must include at least eight activities and one gateway (maps must look different from each other).sketch a and b and c please a-Create an architectural model (using package/component diagram) showing the architectural layers ofthe system.b- Create a deployment diagram to map the software components/layers to physical nodes (computers)c- Create a mapping between the class diagram (created in step 3) and the corresponding ER-Model(database model).Use Case Diagram: Actors: Customer, Sales Person, Warehouse Clerk, Accounting System Use Cases: Add New Order, Modify Existing Order, Package Orders, Check Inventory Levels, Restock Inventory Core Use Cases: Add New Order: Sales person adds an order, notifying the accounting system for invoicing. Modify Existing Order: Sales person updates order details. Package Orders: Warehouse clerk prepares orders for shipping. Check Inventory Levels: Sales person reviews current stock. Restock Inventory: Warehouse clerk replenishes inventory. Class Diagram: Classes: Order, Product,…Which of the following is a reason to take a model driven approach to developing a systems architecture? Models allow systems architects to select only the best performing technologies for a specific systems context Models enable systems architects to test processes throughly and avoid data bottlenecks Models can provide systems architects with a map to locate systems faults and performance bottlenecks Models can be used by systems architects to create a platform-independent model of the system architecture, which can then be used to generate specific implementations for different technology platforms
- 1. QUESTION 32 For complex models, analysts can choose computer-based modeling tools that use _____, which includes standard shapes and symbols to represent events, processes, workflows, and more. a. business process modeling notation (BPMN) b. rapid application development (RAD) c. joint application development (JAD) d. electronic data interchange (EDI) 2. QUESTION 33 The overall aim of a _____ is to avoid seeking goals that are unrealistic, unprofitable, or unachievable. a. CSF (critical success factor) analysis b. BCF (business case factor) analysis c. SWCT (strategy, weakness, cost, and technology) analysis d. SWOT (strengths, weaknesses, opportunities, and threats) analysis 3. QUESTION 34 The _____ is the most pessimistic outcome of a task. a. probable-case estimate (P) b. dominant-case estimate (D) c. best-case estimate (B) d. worst-case estimate (W)22. “The analyst performs a detailed review of the transactions, reports, displays and inquiries supported by the database”. This activity is done in which phase of the SDLC? A. Analysis B. Design C. Implementation D. Maintenance 23. Which of the following is an example of a Rapid Application Development? A. Agile methodology B. Prototyping C. Rapid system development D. Software system 24. Statements that define or constrain some aspects of an organization are called ……… A. business rules B. constraints C. limitations D. restrictions 25. The entity type on which the weak entity type depends on is called ………… A. entity dependant B. identifying owner C. identifying relationship D. weak entity 26. Which of the following does not constitute a characteristic of an identifier? A. Intelligent identifier B. No intelligent identifier C. Not be null D. Not change in value 27. The number of entity types that participate in a relationship is known as its ………….. A. cardinality B. degree…1) What is a disadvantage of the Waterfall model?Group of answer choices Adhoc or little artifact creation Complex interdependencies Stakeholder feedback comes in at the end None of these 2) When performing estimation, what is likely to be done first in the estimation process? Group of answer choices Negotiation of scope to limit what is supported for features or running platforms Breaking work items into smaller components that can be sized Negotiation of feasibility of the technical ability to deliver some of the components None of these Negotiation of business risks that would impact the application 3) Which is a valid process to vet a potential class?Group of answer choices Information hiding principles show that certain attributes will need to be hidden The class will need a function to help change an attribute value within itself Information flow can be modeled between multiple classes Examine interdependency among attributes, higher interdependency means a strong class
- Develop a general spreadsheet implementation of in term ediate COCOMO. You should include a percent software reusability as part of your general model. Also, input labor and overhead rates to get a total cost model. This model should be general enough to be used as a first-cut software estimating tool. The VLOOKUP function in Excel could be a great help in developing a general model. 7.3 You are developing a new IT application that must operate within a strongly coupled complex environment of hardware, software, and operational procedures. You are in charge of estimating the development and installation costs of the data collection system. Given the following information, estimate the total cost of the system: 1. The system will consist of the following components: a. Three COTS servers at $9000 each b. Two COTS sensors at $13,000 each c. 10 KLOC to integrate the systems 2. Your company uses the following rules of thumb when estimating costs: a. The total project cost is…Question # 4 (Points 6)a) You have been appointed a project manager within an information systems organization. Your job is to build an application that is quite similar to others your team has built, although this one is larger and more complex. Requirements have been thoroughly documented by the customer. What team structure would you choose and why? What software process model(s) would you choose and why?b) You have been appointed a project manager for a major software products company. Your job is to manage the development of the next generation version of its widely used word-processing software. Because competition is intense, tight deadlines have been established and announced. What team structure would you choose and why? What software process model(s) would you choose and why?c) What is a need of scrum and what values are provided by scrum? How business involvement and team motivation are managed in agile software development.Based on Dawn Help desk Corporation’s current established and strict manual business processes and workflow, develop a comprehensive UML activity diagram to model the workflows.
- Which of the following does NOT describe the concept of Synergy? A. Synergy mean utilizing only one side of information system either technology or people but not both B. Synergy is the combination of resources resulting to additional value gained C. Synergy can also be described as 2+2 equal to 5 which means that there is an added value given from combination of resources D. Synergy is best described as the whole is greater than the sum of its partsWrite a business solution proposal for a retail store that wishes to implement an M-Commerce Solution to Enhance Customer Experience. Taking the 'AS-IS' model, elaborate on how technology will be utilized to streamline or optimize the current process in order to solve the stated business problem. Explain the future, or ‘ 'TO-BE', state process and illustrate it with a UML Activity Diagram. Include any key technology in its own Swimlane. Also, elaborate on any new, updated, enhanced IT Infrastructure (hardware, databases, networks, business intelligence, RFID, sensor networks, and/or software) required to support the solution. The line items that come out of this section should be part of the investment cost details in the solution assessment.16. Which model can be selected if user is involved in all the phases of SDLC? a. Waterfall Model b. Prototyping Model c. RAD Model d. both b & c

