2. Problem: Use the encoding formula y = x + 15 (mod 26 1. Encode: D A W N 2. Find the decoding formula. 3. Decode: G W I
Q: Compute the determinant using a cofactor expansion across the first row. Also compute the determinan...
A:
Q: -10r+12s -6 S =
A:
Q: QUESTION Given p(x)=x-3 and &, = 0.01. a) Obtain the root of p(x) using False Position and Bisection...
A: Given : p(x)=x2-3
Q: Iculate | y?dx – yz²dy – sen(z)dz, where Cis the path connecting the point A(-2, 2, 4)to the point (...
A:
Q: A jar contains 6 white marbles, 4 orange marbles, 2 vellow marbles, and 3 black marbles, If a marble...
A:
Q: 4. Find the solution u(x, t) of uzz = u4, 0 0, which satisfies the boundary conditions u(0, t) = 3 ...
A: The given problem is to solve the given heat equation partial differential equation with given initi...
Q: Derive a power series expansion of the function e2x+1 by expanding in a Taylor series about a = 0.
A: We have to find the Taylor series for the given function at a=0
Q: Find the principal which amounts to $5,500 at simple interest in 5 years at 2% per annum
A: The formula for Simple interest is SI=P×R×T100, where P is the principal amount, R is the rate of in...
Q: Given the matrices and vectors below, perform the operations indicated in a to d. [1 0 1 0] [1 0 3 2...
A: According to guidelines here solution of only firt 3rd subparts (a,b,c)
Q: Solve the given equations using the indicated numerical method. Use a tolerance level of 0.001%, tha...
A: Solution :-
Q: Solve the following simultaneous equations. Using Gaussian Elimination Method. Show your solution 10...
A:
Q: d) If the coefficients are rounded off of 0.31x + 2.73 find the absolute and relative in y x + 0.35 ...
A:
Q: b. Recall that f(x) = 2*-1 - 1. Graph of f,(x) = f(-x) + 2, f2(x) = f(-x+ 1) +1, and fs(x) = f,(x) +...
A:
Q: GIVEN COMPLEX NUMBER 3 - i 2. 2 - i
A:
Q: 2. Provide a negation for each statement. The negations should be in simple form, i.e., there are no...
A: This is a problem of Logic.
Q: One eight-ounce glass of apple juice and one eight-ounce glass of orange juice contain a total of 25...
A: Lets say 1 ounce glass of apple juice contains x mg of vitamin C and 1 ounce glass of orange juice c...
Q: What is 0.849 rounded to 1 significant figure?
A: The method of rounding of to a significant figure can be done to any kind of numbers regardless of i...
Q: y" – y' – 5y = 5 sin(5t), y(0) = – 1, y'(0) = 0 Apply the Laplace Transform and solve for Y(s) = L{y...
A:
Q: product of it's prime factors and fin
A: Introduction: A prime factor is a factor of a given number that is also a prime number. Variables ar...
Q: 10x + 15y - 13z = 65 7x-3y+8z =104 -5x+1x+5y+2z+9z = 25 Using Gaussian Elimination Method.
A: To solve the below system of equations using the Gaussian Elimination Method. 10x+15y−13z=657x−3y+8z...
Q: Theorem 8o4 ŏ In a parallileguam, oppesitiangles ale equal aie
A:
Q: y" – 2xy' + 5y = 0. Determine the first three nonzero terms in each of two linearly independent solu...
A: The solutions are near the ordinary point x=0. Consider the solution is y=∑n=0∞anxn. Differentiate t...
Q: P5) For the flow field u = U + Q x x , where U and 2 are constant linear- and angular- velocity vect...
A:
Q: ) The price of gravel is $24 for every 3 ton. Kate wants to know the price of 2 tons of gravel. 8 1)...
A:
Q: QI.a) In R",the circular cylinder x+y= 36 is intersected by the plane y +z= 6. find a vector valued ...
A: Q.1 (a) we have given that in R3 the right circular cylinder x2+y2=36 by the plane y + z=6 we have ...
Q: Use the method of variation of parameters to find a particular solution to the following differentia...
A:
Q: (b) Compute the value of this summation. 3. Weak induction in steps Let P(n) be the following statem...
A: Let's say we need to prove a formula or a statement P(n). To prove this, we need to prove that The ...
Q: Use deductive reasoning to show that the following procedure always produces a number 5. Procedure:...
A: let the number be x step-1 add 4 to the number ⇒x+4 step-2 multiply the sum by 3 ⇒3x+4
Q: What is f(x) + g(x), if f(x) = -x + 5 and g(x) = 3x + 2
A: Introduction: Like numbers, two functions can also be added or multiplied. If the two functions are ...
Q: ন Show that (1+ ism) = 1. 1+ 5n-1
A: To prove: an1+isn1+s¨n-1=1 .......... *
Q: Find the general solution of the system of ODES: dyi 2у1 - Зу2 + 1, dt %3D dy2 = -3y1 + 2y2. dt
A:
Q: 1. Le that if same lin 2. Co converg
A:
Q: 1. Simplify: 12 O6 3 O6 5 ©6 24
A:
Q: [3 3 8 20, Mat C = 11 11 30 [-2 1 6 4 Mat B = |5 l10 7 11. -2 5 Find: DET(B/C)
A:
Q: H.W:- Find the deteminant for the following matrices:
A:
Q: find the equation in the form:y zab th lexponential). > points: (0,83), (30, 63) and (70,47)
A:
Q: Show that the o-algebra B of Borel sets contains all F,-sets.
A:
Q: Levi consumes an energy drink that contains caffeine. After consuming the energy drink, the amount o...
A: Given, 10 hour decay factor = 0.2428
Q: How fast is a 1.5g bullet moving if it has a momentum of 1.2kg m/s?
A: If the particle has mass m kg and moving at a velocity of v m/s Then the momentum of the particle is...
Q: GENERAL MATHEMATICS Identify the domain and range of the following logarithmic functions. y=log 5(x-...
A: The given logarithmic function is: y=log5x-1+3
Q: Determine if the function satisfy the Cauchy-Riemann equation. 1. f(z) = cos2(z)
A:
Q: ne series for an ev
A:
Q: A right-angled triangle has a base of 10 cm and a hypotenuse of 12 cm. Put the steps for constructin...
A: Given: We have to put the steps in correct order.
Q: Find x such that the matrix is singular. A = -3 -2 X =
A: Given A = 6x-3-2
Q: Jake's locker number has four digits and is not divisible by 3. The second digit is the square of th...
A:
Q: Find the harmonic conjugate of the following. 10. x2-у2+у
A:
Q: The Fourier cosine series for an even function f(x) is given by f(x) = ao + E an cos(nx) n=1 The val...
A: To find the coefficient a2 for the Fourier cosine series of the below function. fx=cos2x in 0,π
Q: 1. Give a proof of the following statement. 3 integer c > 0 V integers r > 0 3 integer d > 0 : x² – ...
A:
Q: Juan is making a collage, and he planned to form a circle by putting together various pieces of con...
A: A function f(x) is a rule used to associate a number to a particular x. If the input of the function...
Answer number two. Start with A = 1.
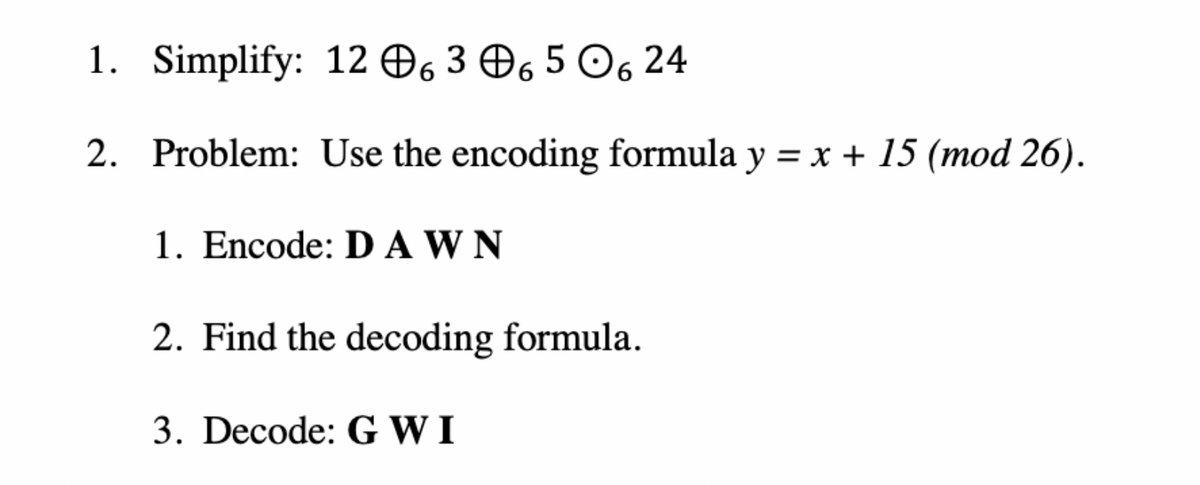
Step by step
Solved in 2 steps with 1 images

- Suppose that the check digit is computed as described in Example . Prove that transposition errors of adjacent digits will not be detected unless one of the digits is the check digit. Example Using Check Digits Many companies use check digits for security purposes or for error detection. For example, an the digit may be appended to a -bit identification number to obtain the -digit invoice number of the form where the th bit, , is the check digit, computed as . If congruence modulo is used, then the check digit for an identification number . Thus the complete correct invoice number would appear as . If the invoice number were used instead and checked, an error would be detected, since .Suppose that in a long ciphertext message the letter occurred most frequently, followed in frequency by. Using the fact that in the -letter alphabet, described in Example, "blank" occurs most frequently, followed in frequency by, read the portion of the message enciphered using an affine mapping on. Write out the affine mapping and its inverse. Example 2 Translation Cipher Associate the letters of the "alphabet" with the integers. Let and define the mapping by where is the key, the number of positions from the plaintext to the ciphertext. If our alphabet consists of through, in natural order, followed by a blank, then we have "letters" that we associate with the integers as follows:Rework Example 5 by breaking the message into two-digit blocks instead of three-digit blocks. What is the enciphered message using the two-digit blocks? Example 5: RSA Public Key Cryptosystem We first choose two primes (which are to be kept secret): p=17, and q=43. Then we compute m (which is to be made public): m=pq=1743=731. Next we choose e (to be made public), where e must be relatively prime to (p1)(q1)=1642=672. Suppose we take e=205. The Euclidean Algorithm can be used to verify that (205,672)=1. Then d is determined by the equation 1=205dmod672 Using the Euclidean Algorithm, we find d=613 (which is kept secret). The mapping f:AA, where A=0,1,2,...,730, defined by f(x)=x205mod731 is used to encrypt a message. Then the inverse mapping g:AA, defined by g(x)=x613mod731 can be used to recover the original message. Using the 27-letter alphabet as in Examples 2 and 3, the plaintext message no problem is translated into the message as follows: plaintext:noproblemmessage:13142615171401110412 The message becomes 13142615171401110412. This message must be broken into blocks mi, each of which is contained in A. If we choose three-digit blocks, each block mim=731. mi:13142615171401110412f(mi)=mi205mod731=ci:082715376459551593320 The enciphered message becomes 082715376459551593320 where we choose to report each ci with three digits by appending any leading zeros as necessary. To decipher the message, one must know the secret key d=613 and apply the inverse mapping g to each enciphered message block ci=f(mi): ci:082715376459551593320g(ci)=ci613mod731:13142615171401110412 Finally, by re-breaking the message back into two-digit blocks, one can translate it back into plaintext. Three-digitblockmessage:13142615171401110412Two-digitblockmessage:13142615171401110412Plaintext:noproblem The RSA Public Key Cipher is an example of an exponentiation cipher.

