2. The following ciphertext message was encrypted using Vigenére Cipher cipher with keyword JEDI. MS. RZ MS QWC. XKMAI LA WS WZH.
2. The following ciphertext message was encrypted using Vigenére Cipher cipher with keyword JEDI. MS. RZ MS QWC. XKMAI LA WS WZH.
Computer Networking: A Top-Down Approach (7th Edition)
7th Edition
ISBN:9780133594140
Author:James Kurose, Keith Ross
Publisher:James Kurose, Keith Ross
Chapter1: Computer Networks And The Internet
Section: Chapter Questions
Problem R1RQ: What is the difference between a host and an end system? List several different types of end...
Related questions
Question
Question 2
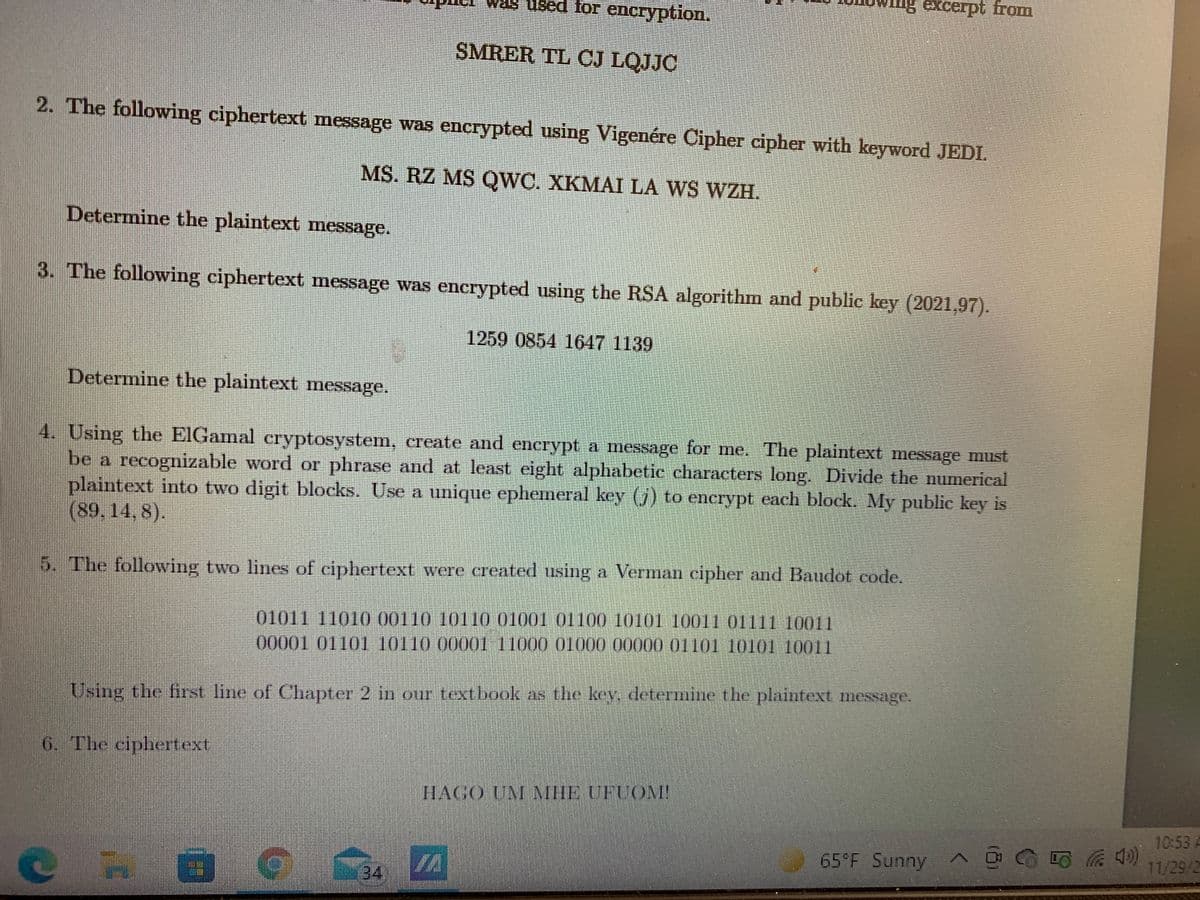
Transcribed Image Text:s Used for encryption.
SMRER TL CJ LOJJC
2. The following ciphertext message was encrypted using Vigenére Cipher cipher with keyword JEDI.
MS. RZ MS QWC. XKMAI LA WS WZH.
Determine the plaintext message.
3. The following ciphertext message was encrypted using the RSA algorithm and public key (2021,97).
1259 0854 1647 1139
Determine the plaintext mnessage.
4. Using the EIGamal eryptosystem, create and encrypt a message for me. The plaintext message must
be a recognizable word or phrase and at least eight alphabetic characters long. Divide the numerical
plaintext into two digit blocks. Use a unique ephemeral key (j) to encrypt each block. My publie key is
(89. 14, 8).
CO
5. The following two lines of ciphertext were created using a Verman cipher and Baudot code.
01011 11010 00110 10110 01001 01100 10101 1001 01111 10011
00001 01101 10110 00001 11000 O1000 00000 01101 10101 10011
Using the first line of Chapter 2 in our textbook as the key. deteTmine the plaintext message.
6. The ciphertext
1HAGO UM MHEUFUOM
10:53 A
11/29/2
65 F Sunny
34
TA
Expert Solution
This question has been solved!
Explore an expertly crafted, step-by-step solution for a thorough understanding of key concepts.
Step by step
Solved in 2 steps

Recommended textbooks for you

Computer Networking: A Top-Down Approach (7th Edi…
Computer Engineering
ISBN:
9780133594140
Author:
James Kurose, Keith Ross
Publisher:
PEARSON

Computer Organization and Design MIPS Edition, Fi…
Computer Engineering
ISBN:
9780124077263
Author:
David A. Patterson, John L. Hennessy
Publisher:
Elsevier Science

Network+ Guide to Networks (MindTap Course List)
Computer Engineering
ISBN:
9781337569330
Author:
Jill West, Tamara Dean, Jean Andrews
Publisher:
Cengage Learning

Computer Networking: A Top-Down Approach (7th Edi…
Computer Engineering
ISBN:
9780133594140
Author:
James Kurose, Keith Ross
Publisher:
PEARSON

Computer Organization and Design MIPS Edition, Fi…
Computer Engineering
ISBN:
9780124077263
Author:
David A. Patterson, John L. Hennessy
Publisher:
Elsevier Science

Network+ Guide to Networks (MindTap Course List)
Computer Engineering
ISBN:
9781337569330
Author:
Jill West, Tamara Dean, Jean Andrews
Publisher:
Cengage Learning

Concepts of Database Management
Computer Engineering
ISBN:
9781337093422
Author:
Joy L. Starks, Philip J. Pratt, Mary Z. Last
Publisher:
Cengage Learning

Prelude to Programming
Computer Engineering
ISBN:
9780133750423
Author:
VENIT, Stewart
Publisher:
Pearson Education

Sc Business Data Communications and Networking, T…
Computer Engineering
ISBN:
9781119368830
Author:
FITZGERALD
Publisher:
WILEY