2.1 In which Normal Form is the above table? Explain how you arrived at your answer. 22 Explain the steps required to convert from an unnormalized table to 3 Normal Form. 23 Comvert the given table into 1" Normal Form. Write your answer as a relation. Eg table namefatt1, at2) 24 Write out all the dependencies of 23.
2.1 In which Normal Form is the above table? Explain how you arrived at your answer. 22 Explain the steps required to convert from an unnormalized table to 3 Normal Form. 23 Comvert the given table into 1" Normal Form. Write your answer as a relation. Eg table namefatt1, at2) 24 Write out all the dependencies of 23.
Fundamentals of Information Systems
9th Edition
ISBN:9781337097536
Author:Ralph Stair, George Reynolds
Publisher:Ralph Stair, George Reynolds
Chapter4: Networks And Cloud Computing
Section: Chapter Questions
Problem 7SAT
Related questions
Question
100%
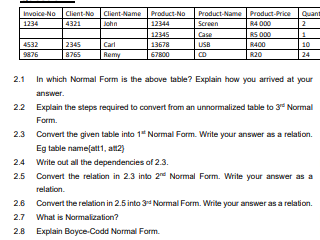
Transcribed Image Text:Invoice-No Client-No Client-Name Product-No
John
Product-Name Product-Price
RA 000
RS 000
Quant
1234
4321
12344
Screen
2
12345
Case
4532
2345
Carl
13678
USB
RA00
10
9876
8765
Remy
67800
R20
24
2.1 In which Normal Form is the above table? Explain how you arrived at your
answer.
22 Explain the steps required to convert from an unnormalized table to 3" Normal
Form.
2.3 Convert the given table into 1" Normal Form. Write your answer as a relation.
Eg table name(att1, att2)
2.4 Write out all the dependencies of 2.3.
2.5 Convert the relation in 2.3 into 2 Normal Form. Write your answer as a
relation.
2.6 Convert the relation in 2.5 into 34 Normal Form. Write your answer as a relation.
2.7 What is Normalization?
2.8 Explain Boyce-Codd Normal Form.
Expert Solution
This question has been solved!
Explore an expertly crafted, step-by-step solution for a thorough understanding of key concepts.
Step by step
Solved in 6 steps with 2 images

Knowledge Booster
Learn more about
Need a deep-dive on the concept behind this application? Look no further. Learn more about this topic, computer-science and related others by exploring similar questions and additional content below.Recommended textbooks for you

Fundamentals of Information Systems
Computer Science
ISBN:
9781337097536
Author:
Ralph Stair, George Reynolds
Publisher:
Cengage Learning

Fundamentals of Information Systems
Computer Science
ISBN:
9781337097536
Author:
Ralph Stair, George Reynolds
Publisher:
Cengage Learning