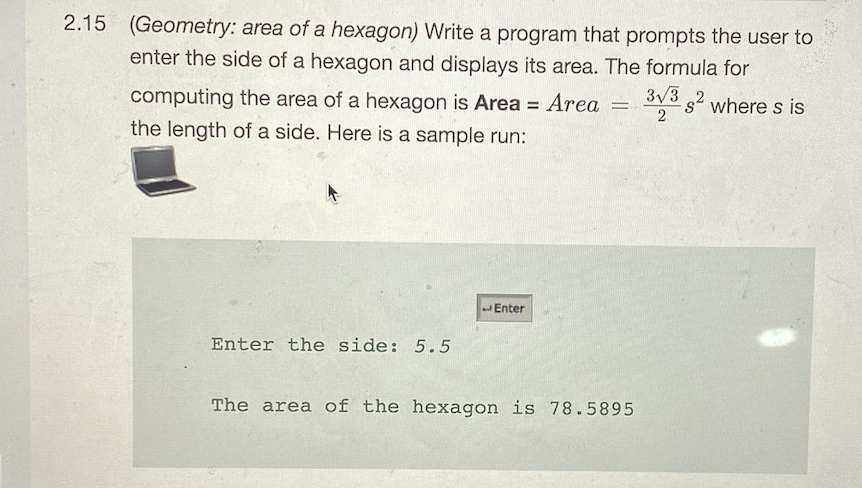
2.15 (Geometry: area of a hexagon) Write a program that prompts the user to enter the side of a hexagon and displays its area. The formula for 3v3 2 where s is computing the area of a hexagon is Area = Area the length of a side. Here is a sample run: %3D
Q: .Write the function heading of an overloaded * operator that multiplies two objects of the myArray c...
A: Note: Answering the question in python as no programming language is mentioned. Input : Create the ...
Q: Question1: What is meant by "bit-specific addressing" to access I/O ports? Question2: What is meant ...
A: Bit-Specific addressing: Bit-specific addressing allows you to access port pins in a variety of ways...
Q: Asymmetric and symmetric encryption algorithms each have their own set of benefits and drawbacks. Wh...
A: What is symmetric encryption ? The symmetric key cryptography as the name suggest is symmtetric ....
Q: 2. Consider the set AP = { A, B } of atomic propositions. Formulate the following properties as LT p...
A:
Q: I use an I2c protocol. How many devices can I control with an 8-bit address?
A: This means that you can have up to 256 devices on the I2c protocol, since a 8bit number can be from...
Q: Describe the sort of data redundancy you found. What are the chances that such redundancies will lea...
A: Detection of data redundancies Data redundancy is being detected when identical data is stored in t...
Q: Why is time a dimension that is always included in a data warehouse or a data mart?
A: Introduction: A data warehouse is a method that is necessary for retrieving information from one sou...
Q: Write a program that lets the user click the refresh button to display four cards from a deck cards.
A: import javafx.application.Application; import javafx.stage.Stage; import javafx.scene.Scene; import ...
Q: Explain the technique through which a segment can be in the address space of two separate processes ...
A: In paging systems, each method is assigned its page table, which establishes the mapping between the...
Q: Define an integer vector and ask the user to give you values for the vector. because you used a vect...
A: In this case, numbers that are entered by user are taken into vector until number entered is non-neg...
Q: 3. In the below PowerShell AD script why is ">>" used instead of "“>"? Get-ADForest >> ||dc1\shared\...
A: The answer as given below:
Q: Using the recursive maxmin algorithm complete the recursive calls tree for the following array: [1] ...
A: The code is given below.
Q: Mention what Amazon EC2 security best practises are. Computer science
A: Introduction: Identity federation, IAM users, and IAM roles are used to control access to AWS resour...
Q: a. Ifa new class Extend PartTime and FullTime class. What type of inheritance is used here for exten...
A: Multiple inheritance is used here for extending these classes. No, it is not possible to do it in JA...
Q: Purpose: Write array functions to solve a mathematical problem.
A: Vector Norms are any functions that map a vector to a positive value which is the magnitude of the v...
Q: Is it critical for database administrators to have access to a database management system as well as...
A: Introduction: Database administration is a technique for organising, storing, and retrieving data fr...
Q: Why is it necessary to have a cooling system in a computer? What are the various cooling procedures ...
A: Introduction: Computer cooling: Computer cooling is a method of removing waste heat created by compu...
Q: 4.Explain DFD & draw (L-0 and L-1) diagram for booking a ticket for flight through online service.
A: Introduction 4.Explain DFD & draw (L-0 and L-1) diagram for booking a ticket for flight throug...
Q: Computer Science Need a detailed answer with a proper diagram Your task is to read up on the Ke...
A: Hey there, I am writing the required solution of the above stated question.Please do find the soluti...
Q: s it a description of the operation of a computer? Then we'll talk about computer components, rig...
A: Intro A computer system works by combining input, storage space, processing, and output. let's disc...
Q: Find an nfa that accepts the language L (aa* (a + b))
A:
Q: There are blank 3 digit counting numbers that are made using only the odd digits 1,3,5,7,9?
A: Here in this question we have we have asked to make 3 digit numbers from 1,3,5,7,9. Note- here nothi...
Q: Write program to copy a block of 8 bytes of data to RAM locations starting at 50H from RAM locations...
A: Hey there, I am writing the required solution of the questin mentioned above. Please do find the sol...
Q: You have been hired as the Network architect at an organization 3 days ago. As you walk into your of...
A: Hey there, I am writing the required solution of the above stated question.Please do find the soluti...
Q: Explain Geo Restriction in CloudFront Computer science
A: Introduction: We're thrilled to introduce Geo Restriction, a new tool that lets you utilize Amazon C...
Q: Write a function can_write(letters, word) that returns True if the word of argument word can be writ...
A: Step 1 : Start Step 2 : Define the function can_write() which accepts 2 strings as parameter. Step 3...
Q: an be done about fragmentation from the outside? Computer science
A: Hey there, I am writing the required solution of the questin mentioned above. Please do find the sol...
Q: Write a Java program to take a list of strings, print a list where each string has "hi" added at its...
A: Step 1 : Start Step 2 : In the main method , create the scanner objects for integer and String input...
Q: What is inheritance? State the different types of inheritance supported by java with example and rea...
A: Inheritance:Inheritance is a system of driving another class from a current class. The current (old)...
Q: Discuss any five disadvantages of cloud computing that are frequently overlooked.
A: Introduction: The phrase "cloud computing" refers to a sort of Internet-based computing in which an ...
Q: What exactly is translation software, and how does it function? Give examples of the many categories...
A: Introduction: Translation software, in the context of text translation, refers to any program that a...
Q: c. Set up and solve a recurrence relation for the number of key comparisons made by your algorithm. ...
A: A divide and conquer algorithm is a strategy of solving a large problem by breaking the problem int...
Q: pplication. se OOP to create a Book Messenger Application that has the following functions: - Add a ...
A: Hey there, I am writing the required solution of the questin mentioned above. Please do find the sol...
Q: Write program to send 44H to ports P1 and P2, using (a) their addresses (b) their name
A: Below program to send 44H to ports p1 and p2
Q: A My Home Programming Exercise 7 A Courses Tasks TypingGrades.cs + >- Terminal 1 using System; 2 usi...
A: Please refer below for your reference: The code above yours have a small bug inside the for loop:
Q: Show how the decimal floating point number -76.310 is stored in the computer's storage using IEEE754...
A: Here in this question we have given a decimal number -76.3 and we have asked to convert it into IEEE...
Q: DRAW THE TURING MACHINE that accepts the string w contains twice as many 0s as 1s
A: Scan the input, looking for a 1 entry. If no 1 entry is found, check that there are no 0 entries lef...
Q: 23. Write a C++ program to input a positive integer n and find the difference in the number of set b...
A:
Q: Define, briefly, the following and provide an example for 1. FRS 2. NFRS 3. Inverse requirement 4. D...
A: The Functional Requirements Specification specifies what the system must accomplish, whereas the Des...
Q: write out the four logical forms of the statement: Cats make great pets.(Lable the four forms: State...
A: Here, The original statement is given.
Q: What security measures are database managers using to secure personal information held in business d...
A: When it comes to protecting your information base worker, this means enforcing access rules and lock...
Q: 5. Consider the following inheritance hierarchy: Anma Hamma Answer the following questions with prop...
A: We need to write answers about questions on inheritance.
Q: interrupts the starting address 10). In is fixed. A. External interrupt B. Vectored interrupts C. No...
A: Let's see the solution
Q: dian-3 quick sort and bubble sort. When using these two algorithms to sort a list of n elements that...
A: Quick sort: O(n log n), Bubble sort: O(n^2)
Q: What security flaws are exploited and how may these issues be addressed in the future in the case of...
A: Introduction: Data damage is defined as any decrease in integrity or data acquisition. Damage to a c...
Q: When wireless networks are compared to wired networks, wireless networks have lower throughput.
A: Introduction: When properly configured, wired networks provide longevity and stability. The installa...
Q: What exactly is cryptography? What exactly is cryptanalysis? What are the distinctions between them?
A: Intro Cryptography is the art of hiding messages by converting them into hidden texts. It is genera...
Q: Indicate whether or not the following is a valid Java statement. Whenever the statement is iavalid, ...
A: A Statement is an executable instruction that tells the compiler what to perform. Among the three ty...
Q: 1. Write a function called removePunct() that takes a string and remove the punctuations from that s...
A: Kindly Note: As per our guidelines we are supposed to answer only first question. Kindly repost othe...
Q: Brief information about matlab software
A: Full form of MATLAB is Matrix Laboratory, It is nothing but a programming language or we can say it ...
Write it in python
Trending now
This is a popular solution!
Step by step
Solved in 3 steps with 1 images

- 3.27 LAB: Login name Write a program that creates a login name for a user, given the user's first name, last name, and a four-digit integer as input. Output the login name, which is made up of the first six letters of the first name, followed by the first letter of the last name, an underscore (_), and then the last digit of the number (use the % operator). If the first name has less than six letters, then use all letters of the first name. Ex: If the input is: Michael Jordan 1991 the output is: Your login name: MichaeJ_1 Ex: If the input is: Nicole Smith 2024 the output is: Your login name: NicoleS_45.21 In Python: A year in the modern Gregorian Calendar consists of 365 days. In reality, the earth takes longer to rotate around the sun. To account for the difference in time, every 4 years, a leap year takes place. A leap year is when a year has 366 days: An extra day, February 29th. The requirements for a given year to be a leap year are: 1) The year must be divisible by 4 2) If the year is a century year (1700, 1800, etc.), the year must be evenly divisible by 400 Some example leap years are 1600, 1712, and 2016. Write a program that takes in a year and determines whether that year is a leap year. Ex: If the input is: 1712 the output is: 1712 is a leap year. Ex: If the input is: 1913 the output is: 1913 is not a leap year. Your program must define and call the following function. The function should return true if the input year is a leap year and false otherwise.def is_leap_year(user_year)5.23 In Python: Write a program with total change amount as an integer input that outputs the change using the fewest coins, one coin type per line. The coin types are dollars, quarters, dimes, nickels, and pennies. Use singular and plural coin names as appropriate, like 1 penny vs. 2 pennies. Ex: If the input is: 0 or less, the output is: no change Ex: If the input is: 45 the output is: 1 quarter 2 dimes Your program must define and call the following function. The function exact_change() should return num_dollars, num_quarters, num_dimes, num_nickels, and num_pennies.def exact_change(user_total)
- 13.16.1: Overload salutation printing. Complete the second PrintSalutation function to print the following given personName "Holly" and customSalutation "Welcome":Welcome, Holly End with a newline. #include <iostream>#include <string>using namespace std; void PrintSalutation(string personName) { cout << "Hello, " << personName << endl;} // Define void PrintSalutation(string personName, string customSalutation)... /* Your solution goes here */ int main() { PrintSalutation("Holly", "Welcome"); PrintSalutation("Sanjiv"); return 0;}(7) Implement the ShortenSpace() function. ShortenSpace() has a string parameter and updates the string by replacing all sequences of 2 or more spaces with a single space. ShortenSpace() DOES NOT output the string. Call ShortenSpace() in the PrintMenu() function, and then output the edited string. Ex: Edited text: We'll continue our quest in space. There will be more shuttle flights and more shuttle crews and, yes, more volunteers, more civilians, more teachers in space. Nothing ends here; our hopes and our journeys continue!10.25 LAB: Quadratic formula Implement the quadratic_formula() function. The function takes 3 arguments, a, b, and c, and computes the two results of the quadratic formula: x1=−b+b2−4ac2a x2=−b−b2−4ac2a The quadratic_formula() function returns the tuple (x1, x2). Ex: When a = 1, b = -5, and c = 6, quadratic_formula() returns (3, 2). Code provided in main.py reads a single input line containing values for a, b, and c, separated by spaces. Each input is converted to a float and passed to the quadratic_formula() function. Ex: If the input is: 2 -3 -77 the output is: Solutions to 2x^2 + -3x + -77 = 0 x1 = 7 x2 = -5.50
- Python 3.7.4 Given that add, a function that expects two int parameters and returns their sum, and given that two variables, euro_sales and asia_sales, have already been defined: Write a statement that calls add to compute the sum of euro_sales and asia_sales and that associates this value with a variable named eurasia_sales.4.19 C++ Write a program that takes in a line of text as input, and outputs that line of text in reverse. The program repeats, ending when the user enters "Done", "done", or "d" for the line of text. Ex: If the input is: Hello there Hey done then the output is: ereht olleH yeH5.28 LAB: Convert to binary - functions Write a program that takes in a positive integer as input, and outputs a string of 1's and 0's representing the integer in binary. For an integer x, the algorithm is: As long as x is greater than 0 Output x % 2 (remainder is either 0 or 1) x = x / 2 Note: The above algorithm outputs the 0's and 1's in reverse order. You will need to write a second function to reverse the string. Ex: If the input is: 6 the output is: 110 Your program must define and call the following two functions. The IntegerToReverseBinary() function should return a string of 1's and 0's representing the integer in binary (in reverse). The ReverseString() function should return a string representing the input string in reverse. string IntegerToReverseBinary(int integerValue)string ReverseString(string userString)
- 8.16 (Searching for Substrings) Write a program that inputs a line of text and a search string from the keyboard. Using function strstr, locate the first occurrence of the search string in the line of text, and assign the location to variable searchPtr of type char *. If the search string is found, print the remainder of the line of text beginning with the search string. Then, use strstr again to Locate the next occurrence of the search string in the line of text. If a second occurrence is found, print the remainder of the line of text beginning with the second occurrence. [Hint: The second call to strstr should contain searchPtr + 1 as its first argument.] Solve without using pointers7.24 LAB: Convert to binary-functions Write a program that takes in a positive integer as input, and outputs a string of 1's and O's representing the integer in binary. For an integer x, the algorithm is As long as x is greater than 0 Output x 2 (remainder is either 0 or 1) x = x // 2 Note: The above algorithm outputs the 0's and 1's in reverse order. You will need to write a second function to reverse the string Ex: If the input is the output is: 110 The program must define and call the following two functions. Define a function named int to reverse_binary() that takes an integer as a parameter and returns a string of 1's and O's representing the integer in binary (in reverse). Define a function named string reverse() that takes an input string as a parameter and returns a string representing the input string in reverse. def int_to_reverse_binary(integer_value) def string reverse(input_string) LAB ACTIVITY 7.24.1: LAB. Convert to binary-functions 0/10 1 # Define your functions here. 2…(Conversion) a. Write a C++ program to convert meters to feet. The program should request the starting meter value, the number of conversions to be made, and the increment between metric values. The display should have appropriate headings and list the meters and the corresponding feet value. If the number of iterations is greater than 10, have your program substitute a default increment of 10. Use the relationship that 1 meter = 3.281 feet. b. Run the program written in Exercise 6a on a computer. Verify that your program begins at the correct starting meter value and contains the exact number of conversions specified in your input data. c. Modify the program written in Exercise 6a to request the starting meter value, the ending meter value, and the increment. Instead of the condition checking for a fixed count, the condition checks for the ending meter value. If the number of iterations is greater than 20, have your program substitute a default increment of (ending value - starting value) / 19.



