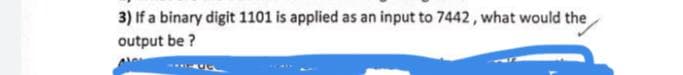
3) If a binary digit 1101 is applied as an input to 7442, what would the output be ?
Q: A virtual machine is perceived differently by the operating system and a user programme. What are…
A: A virtual machine's perceptions The operating system manages all virtual machines and is aware of…
Q: Write C code to swap two int numbers without using third variabl
A:
Q: The extent of the application of ‘Intellectual Properties Rights and Protection’ in the Arab World.…
A: In this question we have to explain and understand what is the Intellectual Properties Rights and…
Q: Modify the Item class to maintain a priority value. This value must also be set in the constructor.…
A: The given class has been modified as per the requirement.
Q: When does a proxy send an acknowledgement to a response and when does it simply forward the response…
A: If the proxy does not correctly handle the NATed callee device, it will propagate into the 200 OK…
Q: Why do we need visual aids? Indicate how you would use three sorts of visual aids in a presentation.
A: ANSWER:-
Q: Explanation of the mechanism used to build intra-AS routeing. Give an in-depth explanation of a…
A: Introduction: It is up to the administrator of the Autonomous System to decide which routing method…
Q: What are the information security and risk management distinctions between the perimeter network and…
A: Information Security Information security is preventing unauthorized access, disruption, inspection,…
Q: False True The microprocessor is a selenium chip and is often called the @ brain of the .computer…
A: As per company guidelines we are suppose to answer only first 3 subparts of the question. Kindly…
Q: 14. What will be the cipher text, if the plain text is 15? C= Show your work here: 15. Decrypt the…
A: Find the answer with calculation given as below :
Q: The Internet has had a significant impact on many parts of our culture. What are the most…
A: It is possible to have access to virtually any information, communicate with anyone else on the…
Q: What can we learn about performance optimization from Amdahl's Law?
A: The answer is given in the below step
Q: Try to give the demo(poplet, appendlet, pop,append) on the doubly ended queue In Python Programming…
A: Required:- Try to give the demo(popleft, appendleft, pop, append) on the double-ended queue.In…
Q: What makes using a VPN more secure than accessing the public internet is unclear. And how exactly…
A: VPN (Virtual Private Network) - VPN stands for virtual private network, and it is a secure…
Q: Find a "one-of-a-kind" article on how Big Data allows businesses to track vast volumes of personal…
A: The phrase "big data" refers to substantial data collections that exceed the capacity of primary…
Q: Outline the legal implications regarding the data issues
A: Information OwnershipWith that entrance and utilization of huge Data is ending up critical to future…
Q: What kind of tree do you get when you use the Java Standard Library to generate a tree for ordered…
A: About the ordered data in tree: Ordered data may be structured hierarchically using the TreeSet…
Q: Give three examples of robots that are employed in teaching. For each case, write out the tasks that…
A: In light of this: The subject is three examples of robots used for educational reasons. Education is…
Q: Maite a Python Program to take an liat of poaitive into, print a new list containing the firot Ceven…
A: Required:- Write a Python Program to take a list of positive ints, and print a new list containing…
Q: 10. Put the following data into a block of data: 011010 110011 101010 111111. Use an odd parity bit…
A: Basics: Because of noise, data can be sent with bit flipping. Consequently, we have created methods…
Q: Why the use of ER modelling is an essential part in the design of a database solution, and how you…
A: ER stands for Entity Relationship diagram and it is an example of conceptual model which is also…
Q: Large address space 2n where n = word length May be nested, multilevel, cascaded - e.g. EA = (((A)))…
A: Introduction
Q: When calculating the NPV of a project, the time value of money is an important consideration. Is the…
A: Time value of money: If the discount rate is more significant, it is preferable to pay future…
Q: What is the performance and cost difference between primary and secondary storage?
A: Answer: Introduction: Primary storage takes results or uses which may be precisely accessed…
Q: a Consider the following search space where we want to find a path from the start state A to the…
A: Introduction: Here we are required to perform a BFS operation on the given graph from source A to…
Q: What's the difference between database mirroring and database clustering?
A: Introduction: Mirroring is the process of storing copies of a database at a different place.…
Q: 2. Find the regular expression for the following Finite Automaton. For this you are requested to…
A:
Q: Assuming the code x = 5 % 2 / 3 * 7 + 4 /2 -6; has been executed correctly, what is the value of…
A: Given Question: To find the value of integer x.
Q: Make a list of six different access technologies. Sort them into three categories: personal access,…
A: Introduction: Sensors record a user's statement of functional intent (e.g., physical movement or…
Q: What format does a password manager store encrypted passwords in? Is it a hard disc, a website, a…
A: Password manager: A password manager is computer software that allows users to save, generate, and…
Q: Microkernels try to make the kernel as tiny as feasible by placing a lot of the operating system…
A: Introduction: It's the first element of the operating system to load, and it stays in main memory…
Q: Assume you're pitching your users on the data warehouse concept. For them, how would you define…
A: Introduction: Multidimensional data analysis is a strategy in which, in response to management…
Q: Create a Java program that requires the computer to generate two random numbers and the user will…
A: Start. Get two random integers. Ask the user what its sum will be. Check if the user input is…
Q: 1. The portion of the process scheduler in an operating system that dispatches processes is…
A: The portion of the process scheduler in an operating system that dispatches processes is concerned…
Q: Question 6 Construct a Turing Machine that takes a binary string and changes every 1 in the string…
A: Turing Machine that takes a binary string and changes every 1 in it to a 0, and only first 0 to 1…
Q: What makes a top-down rather than a bottom-up approach to information security more effective?
A: Overview: This question explains how a top-down approach to information security is more effective…
Q: It is a good idea to put lots of images and information on each slide to keep the viewer entertained…
A: The answer is given below step.
Q: F1= P’ST + PS’T + PST’ + PST + PS’T’ + PS’T + PST’ + PST How would I simplify the logic expression…
A: You need to know some rules of the k-map to simplify logic expression. K- map rules First identify…
Q: 11. (10 - medium) (PDA) Design PDA for L = {wcw“|w € {a,b}*}. %3D
A: here we have given solution for question number 11 as per the guidelines. You can find the solution…
Q: What distinguishes embedded systems programming from application development in general?
A: Unified System definitions include specialized hardware and software, which may be combined to form…
Q: Consider the following recognising Finite State Machine (FSM) S3 1,0 1,0 S2 S4 So State which of the…
A:
Q: Which of the following will result in a vector quantity?
A: For example, displacement, velocity, and acceleration are vector quantities, while speed…
Q: A backup of the critical system files essential for the operation of the operating system in Windows…
A: Introduction: Points to Restore Certain versions of the Windows operating system (ME, XP, and Vista)…
Q: What is the difference between V&V and V&V in the context of software engineering? There have to be…
A: INTRODUCTION: Independent verification and validation (IV&V) is V&V performed by a…
Q: In the random sampling approach for finding frequent itemsets, why should we not just choose and…
A: Random sampling is a kind of sampling technique in which each data has an equal probability of…
Q: Implement the following function that returns a vector of vectors of Item, each of which is a subset…
A: The problem is about slicing a vector
Q: Should a dataflow system's memory be associative or address-based? Explain.
A: Dataflow is a programming paradigm that divides computational actors into stages (pipelines) that…
Q: Define the notation for arrays.
A: Justification: Arrays are a form of data structure that may hold a sequential collection of items of…
Q: What are the information security and risk management distinctions between the perimeter network and…
A: Foundation: Perimeter security is the idea of establishing functioning equipment or tactics at the…
Q: Where and how do regions and availability zones come into play in order to improve application…
A: Introduction: The purpose of this question is to describe how regions and availability zones are…
Step by step
Solved in 2 steps

- ) Using booth algorithm, find out the following signed multiplications: 7 x (-5) 2) Convert the following decimals to standard floating-point representations: 22.62510 3) Convert the infix expression to postfix expression. Z = (X+Y) + (W/U)Two 8-bit numbers in a hexadecimal are 05 and 06. Obtain the checksum.1. If given the code 1001, how is it encoded with Hamming(7,4)? 2. Check if code 1101001 has errors and if so, indicate the position of the error and correct it, otherwise specify that it does not.
- q/Develop the 1- Shannon(binary and ternary) code. 2- Shannon-Fano(binary and ternary) code. 3- Huffman(binary and ternary) code. For the following set of symbols (0.2 , 0.25 , 0.25 , 0.15 , 0.15)1- Convert 2993 to hexadecimal and count in hexadecimal in the next ten digits ( no googling. show all work) 2- Convert 2993 to true binary ( no googling. show all work)Find the double precision representation fl(x) and rounding error for x = 2/3 , x = 9.6
- Q3- Develop the1- Shannon binary code2- Huffman ternary codefor the following set of symbols (0.2 , 0.25 , 0.25 , 0.15 , 0.15)Show how each of the following floating-point values would bestored using IEEE-754 double precision (be sure to indicate the signbit, the exponent, and the significand fields):1. a) 12.52. b) −1.53. c) 0.754. d) 26.625DIGITAL DESIGN COMP 231 Exersies: a) Perform the subtraction with the following unsigned binary numbers by taking the 2'scomplement of the subtrahend.i * (0.1101 - 10110)ii * 0.11011 - 1001 b). Convert the followinga.99710 =() 16b. 25710 =()sc- 65410 =() 2d. 10116=()10
- Please solve and show all work. Thank you. Write down the binary representation of the decimal number 63.75, assuming the IEEE 754 single precision format.Please slove and show all work and steps. Write down the binary representation of the decimal number 63.75, assuming the IEEE 754 double precision format.In a particular computer system, real numbers are stored using floating-point representation with:• 10 bits for the mantissa• 6 bits for the exponent• two’s complement form for both mantissa and exponent. (a) Calculate the normalised floating-point representation of +192.5 in this system. Show your working.

