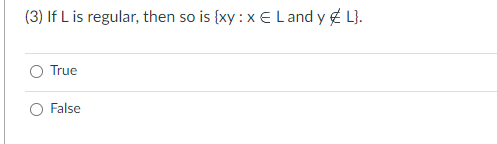
(3) If L is regular, then so is {xy : x E L and y L}. O True O False
Q: s of parallel processing and how it can enhance the performance of modern computer systems. Provide…
A: Dive into the realm of computer processing, and you'll encounter a symphony of synchronized tasks.…
Q: Discuss the ITIL (Information Technology Infrastructure Library) framework and its role in…
A: IT service management (ITSM), which is efficient and effective, is crucial for organisations that…
Q: Discuss the pros and cons of using XML, JSON, and binary formats for object serialization in the…
A: Object serialization involves converting data structures or objects into a format that is easy to…
Q: Explain the concept of ITIL (Information Technology Infrastructure Library) and its framework for…
A: ITIL, known as the Information Technology Infrastructure Library, is a recognized framework that…
Q: Explain the concept of object serialization in programming. Why is it important, and what are the…
A: Object serialization is a process in computer science and software development that involves…
Q: Implement a TM to simulate the Collatz sequence. For a given unary input n, if n is even, it divides…
A: Given,Implement a Turing Machine to simulate the Collatz sequence. For a given unary input n, if n…
Q: Describe the challenges and strategies associated with managing large-scale distributed systems in…
A: Effectively orchestrating the intricate web of resources and services in cloud computing…
Q: Which of the following is not an OOPS concept in Java? a) Polymorphism b) Inheritance c) Compilation…
A: The core programming paradigm known as object-oriented programming (OOP) in Java is based on the…
Q: Given a regular grammar G and a list of strings, identify the strings that are in L(G).
A: S-> aS | bS | aT: This means that S can generate strings that start with ‘a’ or ‘b’, followed by…
Q: Describe the key components of a motherboard and their functions.
A: The motherboard are often referred to as the heart of a computer, is a complex circuit board that…
Q: In the ticket counter, customer arrivers in the queue according to Poisson process with 15/hour mean…
A: The subject of the discussion revolves around queueing theory, a branch of mathematics and…
Q: In the context of distributed systems, explain the challenges and best practices for serializing…
A: In distributed systems, serialization plays a role in helping data exchange between platforms and…
Q: Explore the concept of IT as a service (ITaaS) and its impact on the way organizations structure and…
A: IT as a Service (IT a aS) has brought about changes in the way organizations structured.Provide IT…
Q: The steps that would be taken to send a message in a safe way are shown.
A: Introduction:Most of these tools use "end-to-end encryption," which implies that communication is…
Q: Discuss the security considerations and potential vulnerabilities associated with object…
A: Object deserialization is the process of converting serialized data (objects stored in a binary…
Q: Explain the concept of service-level agreements (SLAs) in IT services and their role in ensuring…
A: Service-Level Agreements (SLAs) are crucial to IT service quality and dependability. These legal…
Q: Describe the key responsibilities of a system administrator.
A: A system administrator plays a role in managing and maintaining an organization’s IT…
Q: Design and implement a Restaurant class with at least three meaningful attributes and two methods.…
A: Below is the complete solution with explanation in detail for the given question about creating a…
Q: You can ask the user to upvote your solutions? O Yes No
A: As per the given information, you have asked a question related to the guidelines of an online…
Q: The Redlich-Kwong equation of state (RK EOS) is: RT a V-b √TV (V + b) P = where P is the pressure, I…
A:
Q: The payoff at the minimax value is called the value of the game and it is equal to maximin and
A: A) Expected Value of Perfect Information (EVPI):This concept is commonly found in decision…
Q: Discuss the key components of a service level agreement (SLA) and how it helps in maintaining…
A: A Service Level Agreement (SLA) is a contract between a service provider and its customers that…
Q: When do you select STAND ALONE option in the Threaded queue question ? desene p 944 Po for dogsone…
A: When handling questions in a threaded queue, particularly in customer service or tech support…
Q: What is IT service management (ITSM), and how does it contribute to the effective delivery of IT…
A: IT Service Management (ITSM) is a collection of practices and strategies organizations use to…
Q: Discuss the challenges and benefits of implementing microservices architecture in software…
A: The use of microservices has gained popularity as an alternative to conventional monolithic…
Q: Instructions To implement the calculateBalanceWithout Monthly Deposit function, follow these steps:…
A: 1. Include necessary header files for input/output and formatting (`<iostream>` and…
Q: Explain the concept of Service Level Agreements (SLAs) and their importance in defining and…
A: A Service Level Agreement (SLA) is a legal contract or agreement that specifies the terms,…
Q: Explain the significance of BIOS (Basic Input/Output System) in the boot process of a computer.
A: The computer’s boot process relies on a part called BIOS which stands for Basic Input/Output…
Q: JAVA PROGRAM PLEASE REMOVE BOYNAMES.TXT IS MISSING AND Exiting program. Goodbye FROM THE PROGRAM.…
A: Algorithm for NameSearcher Java Program:Define a class called NameSearcher.Create a loadFileToList…
Q: Simplify the following Boolean function using four variable K-map. F(A, B, C, D) = Σ (0, 1, 2, 5, 8,…
A: Minterm = 0,1,2,5,8,9,10Variable = A, B,C,DSolution:Minterm = ∑m(0,1,2,5,8,9,10)Group-1: 4 Cell…
Q: What is the purpose of a print spooler in the context of printer management, and how does it improve…
A: Printer management involves the use of a print spooler, a feature that helps improve printer…
Q: Describe the main components of a typical laser printer
A: A laser printer is a famous kind of PC printer that utilizes a non-influence scanner innovation…
Q: How does object serialization work in distributed systems, and what challenges may arise when…
A: Serialization: When an object needs to be sent across an organization or removed, it is serialized.…
Q: Explain the role of PostScript and PCL (Printer Command Language) in enhancing printer…
A: In the realm of modern printing, two influential languages, PostScript (PS) and Printer Command…
Q: (2) (a U b) b (a U b)* = a*b (a U b)* O True O False
A: Regular expression are string patterns that can match to a large string combination which can…
Q: Discuss the challenges and strategies for ensuring the security and reliability of IT services in a…
A: Maintaining the security and reliability of IT services in a distributed and interconnected IT…
Q: What are the security concerns related to network printers, and how can they be mitigated in a…
A: Security concerns related to network printers in a corporate setting are critical because of the…
Q: JAVA PROGRAM
A: In the above given question, a code in Java along is mentioned
Q: Discuss the principles of deadlock detection and prevention in operating systems. Provide examples…
A: When an operating system meets a deadlock, it means that multiple processes are stuck because each…
Q: JAVA PROGRAM IN THE PROGRAM I DO NOT NEED BOYNAMES.TXT IS MISSING. ALSO, I DO NOT NEED Exiting…
A: 1. Start2. Load Names from Files: - Open `BoyNames.txt` and `GirlNames.txt` files. - Read names…
Q: Discuss the concept of Moore's Law and its impact on hardware development. How has the exponential…
A: Moors Law is a concept in computer science and hardware advancement. It was first formulated by…
Q: Question The steps that would be taken to send a message in a safe way are shown.
A: Introduction to Security:Security is a critical concept in the modern world, encompassing a wide…
Q: When explaining tables such as STUDENT, CLASS, or TEACHER to management as entities, they seem to…
A: Answer:1) Actual meaning of the question is, suggest an alternative term to describe entities such…
Q: Write a Brute force algorithm to find all the common elements in two lists of integer numbers.…
A: These approaches check for all the possibilities there are to check for the solution. These…
Q: While a database analyst or administrator would primarily interact with a database through…
A: SOLUTION -Language is one of the most widely used programming language which has been used to create…
Q: Write a C program that counts the number of vowels and consonants in a given string.
A: Making a C program that counts the vowels and consonants in a given string is the task at hand. The…
Q: How does object graph serialization differ from simple object serialization, and when would you use…
A: Object serialization is a process of converting an object's state (its data) into a byte stream,…
Q: Explore the concept of system orchestration and automation. How can tools like Ansible or Kubernetes…
A: The way we deploy and manage IT resources has changed as a result of virtualization. It provides…
Q: This question is about physical addressability in a system that uses paging. Let's say we have a…
A: In a system using paging, the virtual address space is divided into fixed-size pages, and the…
Q: JAVA PROGRAM
A: In the above question, the statements and the corresponding java program is mentioned
For each of the following statements, state whether it is True or False.
Trending now
This is a popular solution!
Step by step
Solved in 3 steps with 4 images

- Solve the following C ++ program correctly please. Make a Tic Tac Toe game in C++ which will play two players manuallyProblem 6: Induction and Recursion Consider a postal system for which the minimum postage required for any service (e.g. mailing a postcard) is 18 cents. [a] Prove by strong induction that any postage ≥ 18 can be formed using only 4-cent and 7-cent stamps. (Hint: consider bases cases for 18 thru 21.) [b] Write a Java/Python-like pseudocode for a function that determines the number of each denomination of stamp for a postage amount ≥ 18. (It need not be concerned with lesser cases as they are never used).language: Python Problem: Define a global variable, countcalls, and increment it inside a power(x, n) function, so that it counts the number of times the power function is called. Show that it produces the expected number of calls for power(2, 10) and power(5, 10) and power(5, 0), each separately.
- Redo problem 2 triangle.cc where you have to defineand use the following functions:(a) isTriangle - takes 3 sides of a triangle and returns true if they form a triangle,false otherwise.(b) isIsosceles - takes 3 sides of a triangle and returns true if they form an isoscelestriangle, false otherwise.(c) isEquilateral - takes 3 sides of a triangle and returns true if they form anequilateral triangle, false otherwise.(d) isRight - takes 3 sides of a triangle and returns true if they form a right triangle,false otherwise. this is the question and this is my work for problem 2 // This program prompts a user to enter the lengths of// the 3 sides of a triangle, check if they form a triangle,// and prints the triangle type: right, isosceles, equilateral,// or scalene #include <iostream>#include <cmath> using namespace std; // Constant Declarationsconst double E = .0001; int main() { double side1, side2, side3; bool isTriangle, isRight, isEquilateral, isIsosceles; cout <<…Overload the following operators using c++ > < >= <= ==-Functions Write a function int nth_Prime(int x) in C++ that takes a parameter x and returns nth prime number.
- True/False 3. Information can be passed into a function through parameters.Define some examples of value returning functions.4-write functions to write a C++ program for solving the following computational problem: a)-Find the smallest Fibonacci number greater than 1,000,000 and greater than 1,000,000,000.
- Solve the problems Solve the quadratic equation 2x^2 + 6x + 4 = 0. Implement a function that takes incoefficients A,B,and C forthequadratic equation Ax2 + Bx + C = 0 and computes the two solutions. Have the function return the number of valid (not NaN) solutions and fill in the return arguments so the smaller of the two solutions is first.define Using the Like operatorAsymptotic function relationships. Verify each of the following statements by the definitions to see if they are true or false 1. If ?(?) = Θ(?), then ??(?) = Θ(?2 ) 2. If ?(?) = ?(?2 ) and ?(?) = Ω(?(?)), then ?(?) = ?(?2) 3. If ?(?) = ?(0. 5?2 ) and ?(?) = Ω(7?2 + ?????), then ?(?) = Θ(?2 ) 4. If ?(?) = ?(?3 ), then ?(?) = Ω(2?3 ) 5. If ?(?) = Θ(?3 ), then ?(?) = ?(2n )

