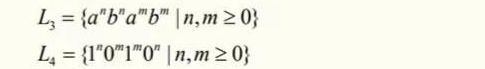
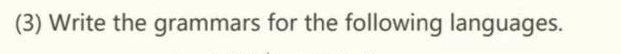
(3) Write the grammars for the following languages.
Q: Draw a MapReduce tracing diagram together with the phases involved for the following word count…
A: Counting number of occurrences of words using map reduce: there are 2 functions to implement…
Q: Discuss the influence of cookies on internet security in detail, mentioning at least four (4)…
A: In the given question Cookies are small text files placed on a user’s computer, which are commonly…
Q: Design a backup strategy for a computer system. One option is to use plug-in external disks, which…
A: According to the information given:- We have to follow the instruction in order to calculate the…
Q: We have learned a great deal about the industry via web design and development.
A: INTRODUCTION Web-based learning is many times called internet learning or e-learning since it…
Q: lease answer number 1 and 2 as they are all linked altogether with the subparts perfectly. Write…
A: The code is in step 2:
Q: The significance of continuous event simulation, in addition to four justifications for why it…
A: According to the information given:- We have to signify continuous event simulation, in…
Q: Suppose a stack is to be used by the processor to manage procedure calls and returns. Can the…
A:
Q: You are given 4 items as {value, weightpairs in this format {(20,5), (60, 20), (25, 10}, {X, 25).…
A:
Q: Given the following Turing Machine M1, 90 a/a R q1 b/b R O A. (a + ab + aba) O B. a(ba)* O C. ab(ab)…
A: In the given Turing machine, it contains, Set of states= {q0, q1, q2, q3} Initial state= q0 Final…
Q: Suppose that a DBMS recognizes increment, which increments an in- teger-valued object by 1, and…
A:
Q: Give examples of various session hijacking techniques. How would you defend yourself from this…
A: Introduction Session hijacking is a cyberattack in which a malicious hacker places himself between…
Q: i see the correction with my code. However the error is now occuring on input 1600.
A: About Gregorian Calendar Nowadays, everyone uses the Gregorian calendar. Pope Gregory XIII first…
Q: Explain in detail on the importance of Management of Technology. Discuss the various definitions of…
A: Definition of MOT: Engineering, science, and management disciplines come together in the field of…
Q: Question 5 What happens if you select Other in the drop-down below? Male Female Other 5 7 8…
A: Answer:-
Q: Write the following constraint in correct form with a number for the RHS. Supervisory labor hours…
A: Write the following constraint in correct form with a number for the RHS. Supervisory labor hours…
Q: show output of this html code: paragraph Paragraph with blue colour
A:
Q: The language accepted by the following pushdown automata is L = {w|w1 {a, b}* and Iwl is even}.
A: Yes it is True
Q: What is the difference between using +/- versus = when setting file permissions? Is there any…
A:
Q: What is difference between batch processing and streaming process??
A: Batch processing 1. Data scope query or analysis applied to all or the majority of the dataset's…
Q: What difficulties do data with a high valence face?
A: Introduction: Big data properties such as consistency, correctness, quality, and trustworthiness are…
Q: What Network Layer protocol is used for HTTP applications? IP BootP UDP TCP
A: Introduction: The Hypertext Transfer Protocol (HTTP) is a networking protocol for hypermedia…
Q: What is the equivalent regular grammar for the following context free grammar?. S→AB; A→aa; B→ aB |…
A: Given grammar is: S→ABA→aaB→aB | bB | λ The variables present in the grammar are S, A, B and the…
Q: Design an electronic form that may be used to record review comments and which could be used to…
A: There are several electronic forms that may be used to capture reviewer comments and send those…
Q: Define the features of static RAM ?
A: As long as power is being provided, SRAM (static RAM), a form of random access memory (RAM), keeps…
Q: Write a python program to get the specific line from a given File and that line number should be…
A: Introduction: Write a python program to get the specific line from a given File and that line number…
Q: A DMA module is transferring characters to memory using cycle stealing, from a device transmitting…
A: We need to find the percentage by which the processor will be slowed.
Q: #include int main() { float n; printf("Enter Number: "); scanf("%f", &n); sq = n*n; printf("Cube of…
A: #include <stdio.h>int main (){ float n; printf ("Enter Number: "); scanf ("%f", &n);…
Q: How is the UI of a website created?
A: Institution: Website is a collection of online pages and related material identified by a common…
Q: How do routers forward packets to the internet.
A:
Q: Name the functional dependence and provide the determinant(s) in the following equation: Length *…
A: Dependency: Dependency in terms of function for the given expression: Consider the statement stated,…
Q: Which of the five memory management approaches has which benefits and drawbacks?
A: Memory management is the process of controlling and coordinating a computers main memory.
Q: Considering a single linked list class, write a method to check whether it contains a number…
A: Please check the step 2 for solution
Q: Consider a floating-point format with 8 bits for the biased exponent and 23 bits for the…
A: ANSWER:-
Q: Suppose the page table for the process currently executing on the processor looks like the…
A: (a) Split the binary address into a VPN and also an offset. Use VPN binary address as an index into…
Q: A DMA module is transferring characters to memory using cycle stealing, from a device transmitting…
A: In this question, we have to calculate how much will the processor be slowed down due to the DMA…
Q: Which of the following regular expression resembles the given diagram? # is blank space #/#, R O A.…
A: To get regular expression for given machine : we must observe the paths from initial state 0 to…
Q: Examination of the timing diagram of the 8237A indicates that once a block transfer begins, it takes…
A:
Q: dard TCP/IP ports. To correctly build security, businesses need to be aware of the services' goals…
A: Introduction: The Microsoft client and server operating systems, server-based applications, and…
Q: Describe five memory-management approaches, highlighting the benefits and drawbacks of each.
A:
Q: Question 9. (C format: a. -7 b. -8 Express the following numbers in IEEE 32-bit floating-point c.…
A:
Q: 6.19 LAB: Password modifier Many user-created passwords are simple and easy to guess. Write a…
A: As per the requirement program is developed. Algorithm: Step 1: Write the main method Step 2: Create…
Q: Think about the standard TCP/IP ports. To correctly build security, businesses need to be aware of…
A: A personal computer network is a collection of individual computers connected through various…
Q: Write a one blog about the M1 chip and another about the M2 chip
A: Introduction: How does the new Apple M2 CPU compare to the previous M1 processor for the MacBook Air…
Q: 25)=3.54,p.01 c. t(.8128) = 7.0, p = α, tobt = 4.25 d. t(10), tcrit > 5.3, p < α
A: Solution As we know An APA format scenario contains the df,t value,p value compared with alpha and…
Q: Which rules should effect exposed and traceable project components if a software industry uses…
A: Given: The software industry use a method known as the Software Development Life Cycle (SDLC) to…
Q: JAVA Scrip// 1 DO NOT COPY FROM OTHER WEBSITES Upvote guarenteed for a co
A: Given :- According to the question The concept of query selectors using javascript (or Ecma script)…
Q: How is the UI of a website created?
A: We need to discuss how to create the UI of a website.
Q: Difference between DBMS and RDBMS?
A: Foundation This question comes from Database Management System which is a paper of computer science.…
Q: Give a brief explanation of the word "metadata," and cite some specific. instances.
A: Advantages of distributed databases management system:- -> In distributed database management…
Q: You have taken large number of photos during a family trip, and most of them are group photos (with…
A: Introduction: Different methods are used in digital image processing (DIP) to process digital…
Step by step
Solved in 2 steps with 2 images

- INT_MIN = -32767 def cut_rod(price): """ Returns the best obtainable price for a rod of length n and price[] as prices of different pieces """ n = len(price) val = [0]*(n+1) # Build the table val[] in bottom up manner and return # the last entry from the table for i in range(1, n+1): max_val = INT_MIN for j in range(i): max_val = max(max_val, price[j] + val[i-j-1]) val[i] = max_val return val[n] # Driver program to test above functionsarr = [1, 5, 8, 9, 10, 17, 17, 20].Question 6 Let A = {a, b} and B = {c, d} and C = {0}. Compute the following sets: a. A X (B X C) b. A X C ..Q1. Srikanth is a school student. He studies in class 8th. One day his Math’s teacher came to the class and told them that he is going to start a new chapter “Measurement”. In order to give them a demo of that chapter, he told the students to find the volume of the class room using Volume( ). Input Constraint 15<=Length<=25 10<=Breadth<=20 20<=Height<=30 Note:- It needs to be solved in Dev C++ using #include<stdio.h>
- Q2. ""Euler's totient function, also known as phi-function ϕ(n),counts the number of integers between 1 and n inclusive,which are coprime to n.(Two numbers are coprime if their greatest common divisor (GCD) equals 1)."""def euler_totient(n): """Euler's totient function or Phi function. Time Complexity: O(sqrt(n)).""" result = n for i in range(2, int(n ** 0.5) + 1): if n % i == 0: while n % i == 0: n //= i. .True or false set{(x,x2):x∈Z}canbeseeasafunctionZ→Q. set{(x2,x):x∈Z}canbeseeasafunctionZ→Q.Count consecutive summers def count_consecutive_summers(n): Like a majestic wild horse waiting for the rugged hero to tame it, positive integers can be broken down as sums of consecutive positive integers in various ways. For example, the integer 42 often used as placeholder in this kind of discussions can be broken down into such a sum in four different ways: (a) 3 + 4 + 5 + 6 + 7 + 8 + 9, (b) 9 + 10 + 11 + 12, (c) 13 + 14 + 15 and (d) 42. As the last solution (d) shows, any positive integer can always be trivially expressed as a singleton sum that consists of that integer alone. Given a positive integer n, determine how many different ways it can be expressed as a sum of consecutive positive integers, and return that count. The number of ways that a positive integer n can be represented as a sum of consecutive integers is called its politeness, and can also be computed by tallying up the number of odd divisors of that number. However, note that the linked Wikipedia de0inition…
- equality (5)/(9)x+(0)/(2)>=(5)/(2)x+(1)/(6). Enter your answer using intDebug the following program and answer the following questions. #include <stdio.h> typedef struct node { int value; struct node *next; } node; int ll_has_cycle(node *first) { node * head = first; while (head->next) { head = head->next; if (head == first) return 1; } return 0; } void test_ll_has_cycle(void) { int i,j; node nodes[5]; for(i=0; i < sizeof(nodes)/sizeof(node); i++) { nodes[i].next = NULL; nodes[i].value = i; } nodes[0].next = &nodes[1]; nodes[1].next = &nodes[2]; nodes[2].next = &nodes[1]; printf("Checking first list for cycles. There should be a cycle, ll_has_cycle says it has %s cycle\n", ll_has_cycle(&nodes[1])?"a":"no"); printf("Checking length-zero list for cycles. There should be none, ll_has_cycle says it has %s cycle\n",…Write a classifier algorithm for p(Y |X,α)
- Edit this program so that it returns ecg data instead of heart beat in BPM. #include <ArduinoBLE.h> #define BLE_UUID_HEART_RATE_SERVICE "180D"#define BLE_UUID_HEART_RATE_MEASURMENT "2A37"#define ECG_SERV_UUID 0x2D0D#define ECG_MEAS_UUID 0x2D37#define ECG_NUM_CHANS_UUID 0x2D38#define ECG_SAMPLE_SETS_UUID 0x2D39#define ECG_COMMAND_UUID 0x2D3A #define HRM_VALUE_FORMAT_8BIT 0#define HRM_VALUE_FORMAT_16BIT 1#define HRM_SENSOR_CONTACT_NOT_DETECTED ( 2 << 1 )#define HRM_SENSOR_CONTACT_DETECTED ( 3 << 1 ) typedef struct {uint8_t flags;uint8_t heartRate;} heart_rate_measurment_t; union heart_rate_measurment_u{struct {heart_rate_measurment_t values;};uint8_t bytes[ sizeof( heart_rate_measurment_t ) ];}; union heart_rate_measurment_u heartRate = { .values = { .flags = 0, .heartRate = 0 } }; #define BLE_DEVICE_NAME "Arduino HRM"#define BLE_LOCAL_NAME "Arduino HRM" BLEService heartRateService( BLE_UUID_HEART_RATE_SERVICE );BLECharacteristic heartRateCharacteristic(…last 3 digits of enrolment number - 308 Let a, b and c denote the last three digits of your enrolment number (so for example with enrolment number 001054321, you would take a = 3, b = 2 and c = 1) and then take each of them (mod 2). So in the example above, a, b and c would become 1, 0, 1 respectively (each digit taken (mod 2)). Consider the polynomial . (a) Create a polynomial code of codeword length 8 from this generating polynomial. (b) Is your code cyclic? Justify your answer.int a[10] = {0,1,2,3,4,5,6,7,8,9};int *m = &a[0];int *p = &a[5];int *q = &a[1]; p = (int) m + (int) p - (int) q; what is the value of of *p



