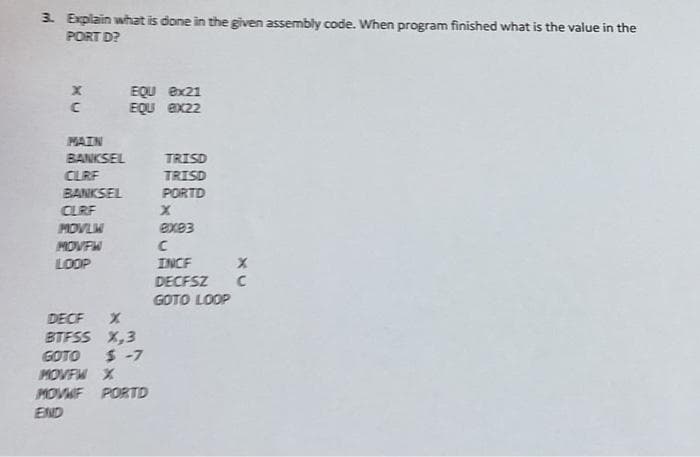
3. Explain what is done in the given assembly code. When program finished what is the value in the PORT D? EQU 8x21 EQU ex22 С MAIN BANKSEL TRISD CLRF TRISD BANKSEL PORTD CLRF X MOVLW exe3 MOVFW С LOOP X INCF DECFSZ C GOTO LOOP DECF X BTFSS X,3 GOTO $-7 MOLDU M
Q: Q2- What are the different types of Arduino boards? State 4 types only.
A: Find the required answer given as below :
Q: In software design, what is the relationship between cohesion and coupling, and how do they effect…
A: =>The Answer start from step-2.
Q: What precisely is an overlay? When it comes to massive computer systems, why is it no longer…
A: The most fundamental problem with fixed partitioning is that the maximum size of the partition binds…
Q: What component of hardware is responsible for a device's ability to connect to the Internet?
A: What component of hardware enables a device's physical network connection? Solution: In the network,…
Q: For a computer with six cores, each with two processing threads, explain the concept behind the…
A: Launch: The term "six-core computer" or "hexa-core microprocessor" refers to a single-die integrated…
Q: Compare the mobile and cloud connectivity. How may mobile devices benefit from cloud computing?
A: The question is to Compare the mobile and cloud connectivity and how may mobile devices benefit from…
Q: ter architectu
A: Solution - In the given question, we have to tell the two main computer architectures used in…
Q: Which of the following creates a drop-down list of values? A. Value1 … Value2 B.…
A: Please find the answer and explanation in the following steps.
Q: nding of the concept of social networking. What exactly is meant by the term "autonomous computing,"…
A: Introduction: Social networking refers to the use of internet - based social media sites to stay…
Q: Deduce X from the following, (i) (BA0.C),6 = (X)g (ii) (10101100)₂ = (X) 16 2 (iii) (FFE.C)₁ = (X) ₂…
A: The Answer is in Below Steps
Q: (1) Transform the following Boolean equation in SOP form to POS form: Y = F(A, B, C, D) = ĀB + CD
A: As per guidelines I can answer only first question. I hope you will understand. Thank You. Here is…
Q: Write python code to print difference between 55th term of Fibonacci series and 45th term * 5th term…
A: HI THEREI AM ADDING ANSWER BELOWPLEASE GO THROUGH ITTHANK YOU
Q: There is evidence presented in support of the contention that a relational database is incapable of…
A: A relational database is a kind of database that stores information in It's a kind of database that…
Q: Computing done by end users
A: End-user computing (EUC) refers to the technologies used by IT professionals to install, manage, and…
Q: Determine how contemporary network programs may accommodate numerous concurrent connection
A: For connected-web applications, it's common to open many persistent TCP or Transport Control…
Q: output of (Print "a", "b", "c") is abc O ab c abc O Ο Ο
A: Below the python program output
Q: Use social networking blogs and cloud computing to your advantage.
A: Cloud computing is a network of servers connected using the Internet. Its main function is to share…
Q: :the output of (Print "a", "b", "c") is abc C ab c abc C O оо
A: The solution to the given question is: EXPLANATION Python's print statement is used to display the…
Q: What's the difference between UDP and TCP, and what's the advantage of using one over the other? Why…
A: Find the required answer given as below :
Q: There are some IT experts that are worried about the new Linux distribution. What they're looking…
A: Linux distribution: Linux Mint, which is based on Ubuntu, is undeniably an Ubuntu-based Linux…
Q: You should describe how social networking and other online discussion groups and chat rooms function…
A: Given: Overall, 80% of social network users still use email to communicate with friends, whereas 59…
Q: Analyze how mobile devices and cloud computing are similar and how they differ in terms of the most…
A: Introduction: Cloud computing on the go cloud computing is used to provide programs to mobile…
Q: What's the difference between message-passing and shared-memory computers? Which has more pros and…
A:
Q: Write python code to print difference between 100th term of Fibonacci series and 80th term * 10th…
A: HI THEREI AM ADDING ANSWER BELOWPLEASE GO THROUGH ITTHANK YOU fd
Q: Acquire a deep and comprehensive grasp of social networking. What precisely is meant by the term…
A: Introduction: Acquire a deep and comprehensive grasp of social networking. What precisely is meant…
Q: 2. Using Divide and Conquer technique, sort the given number using quick sort 9,1,3,5,2,6,4
A: Answer : The answer of above problem is given below in step 2
Q: Give me 5 vulnerabilities and 5 Risk for Operating system level control
A: The vulnerability is a weakness in your infrastructure, networks or applications that potentially…
Q: What are some of the drawbacks associated with business networking? Specify a few of the issues, as…
A: Launch: Even if the services supplied by servers, applications, and gadgets are running properly…
Q: Disk -title: String -playTime: int // in minutes + Disk(title: String, playTime: int) + get Title():…
A: Solution - Programming language - Java OOPs All solution steps are included in program code…
Q: eness and coupling in software development: are t
A: Introduction: The relationship within the module is shown by cohesion. Coupling depicts the…
Q: At the time of runtime, the attribute of a control, in the same way that the attribute of other…
A: Introduction: Attribute Control Charts are a kind of control chart that was specifically designed to…
Q: What are the methods for avoiding deadlock? Hello, it seems that the ones I was provided were…
A: A deadlock occurs when two PC applications using the same asset effectively prevent each other from…
Q: Timing based simulation occurs before s
A: Toning based simulation gives that whether design of your device meets all the functional and timing…
Q: LAB TASK Let suppose you are working as a Software Developer at UOL, and you are required to develop…
A: Answer:
Q: 1.write Introduction to Web App, Software Required.
A: Complete Web application is the finalized and finished product which is a complete version of the…
Q: What exactly are the "rules of inference"? Provide an explanation of "ahead chaining" and "reverse…
A: Ahead chaining: Filters. (Theory of proof, logic) A rule for merging (changing) well-formed formulae…
Q: Alice and Bob use the ElGamal scheme with a common prime q= 131 and a primitive root a = 6. Let…
A: The answer is
Q: Describe a fictitious login management situation. Determine a number of different authentication…
A: Answer: Phishing attacks are a sort of attack that takes a user's credentials and uses them to…
Q: To what extent is it absolutely necessary to set up and install a firewall?
A: Given: It evaluates whether to allow or reject a certain kind of communication to enter or exit the…
Q: An analysis of the benefits and drawbacks associated with purchasing pre-made software rather than…
A: Advantages: Because the project is built for the mass market to meet the common criteria of many…
Q: 29. Compute each of these sums. a. Zies(i2 + 1) where S = {1, 3, 5, 7). b. [4i=0(k. 2¹) c. [2i=0…
A:
Q: Identify size, addressing mode, T-state machine cycles and functions of following 8085 instructions:…
A: Identify size, addressing mode, T-state machine cycles, and functions of following 8085…
Q: In addition to network-based firewalls, what additional kinds of firewalls are there?
A: Firewalls monitor traffic and the assist prevent unwanted traffic from entering your network, while…
Q: In the one-to-one threading model, when a thread makes a blocking system call ... O only the main…
A: HI THEREI AM ADDING ANSWER BELOWPLEASE GO THROUGH ITTHANK YOU
Q: Explain the concept of a computer having six cores and two threads per core. Describe the process in…
A: A six-core computer, sometimes known as a hexa-core microprocessor, is a single-die integrated…
Q: What exactly is meant by the phrase "networking"? What are the positive and negative aspects of…
A: answer is
Q: Determine how a new sort of cloud computing, such as software as a service (SaaS), may benefit the…
A: remote cloud network is accessible via the internet. a) SaaS vendors provide users with software and…
Q: Talk about frequency multiplexing as well as time division multiplexing (According to commuter…
A: Multiplexing is the sharing of a medium or bandwidth. It is the process in which multiple signals…
Q: One of the most important parts of a personal computer is called the Central Processing Unit, or CPU…
A: As a result: The Central Processing Unit (CPU) is one of the most important components of a…
Q: Provide an explanation of how database managers may make effective use of views to facilitate user…
A: Views in the database management is a subset of database and this is based on the query which runs…
Step by step
Solved in 2 steps

- Write an ARM assembly program to convert temperatures from Celsius to Fahrenheit orfrom Fahrenheit to Celsius. Here are the two formulas for your reference. Use variable toread and store values, you can initialize any integer value into the variables (Do not expectdecimal results we are only doing integer operations).C = 5 × (F − 32) / 9F = (9 × C / 5) + 32Name the file TempConvert.s add the below commenting statements in the program;Name:;Date:;Give which expression you useWrite programs that will accomplish the desired tasks listed below, using as few lines of code as possible.Use only opcodes that have been covered in class. Comment on each line of code. m) Copy the external code byte at address 007Dh to the SP n) Copy the data in register R5 to external RAM address 032Fh o) Copy the internal code byte at address 0300h to external RAM address 0300h p) Swap the bytes in TIMER 0 ; put TL0 in TH0 and TH0 in TL0 q) Store DPTR in external RAM locations 0123h (DPL) and 02BCh (DPH) r) Exchange both low nibbles of registers R0 and R1 ; put the low nibble of R0 in R1, and the low nibble of R1 in R0Write the assembly code for the safe_input function in the C program given below. Name the file as safeinputfile.asm. #include <stdio.h> int safe_input(char *buffer, unsigned length ); int main(){ char buffer[32]; printf("Your name: "); fflush(stdout); safe_input(buffer,32); printf("Pleased to meet you, %s!\n",buffer); return 0;}
- Write programs that will accomplish the desired tasks listed below, using as few lines of code as possible.Use only opcodes that have been covered in class. Comment on each line of code. m) Copy the external code byte at address 007Dh to the SPn) Copy the data in register R5 to external RAM address 032Fho) Copy the internal code byte at address 0300h to external RAM address 0300hp) Swap the bytes in TIMER 0 ; put TL0 in TH0 and TH0 in TL0q) Store DPTR in external RAM locations 0123h (DPL) and 02BCh (DPH)r) Exchange both low nibbles of registers R0 and R1 ; put the low nibble of R0 in R1, and the lownibble of R1 in R0s) Store the content of register R3 at the internal RAM address contained in R2. (Be sure the addressin R2 is legal)t) Store the content of RAM location 20h at the address contained in RAM location 08hu) Store register A at the internal RAM location address in register AResearch on your own, provide at least 1 example of code setInterval(), clearInterval(), andrequestAnimationFrame() running on your machine in VSC function fastFunction(){ console.log("fast function completed") } function slowFunction(){ var now = new Date().getTime(); while(new Date().getTime() < now + 5000){ /* processing*/} console.log("Slow function completed "); } function asyncslowFunction(){ console.log("asyncslowFunction was called") setTimeout(slowFunction, 5000); } fastFunction() slowFunction() fastFunction() slowFunction() /*---------*/ fastFunction() asyncslowFunction() fastFunction() asyncslowFunction()Can you show me the screen shot of the output consoleof the following assembly code please INCLUDE Irvine32.inc .DATA whiteProb BYTE 3 ; probability of white is 30% blueProb BYTE 1 ; probability of blue is 10% greenProb BYTE 6 ; probability of green is 60% .CODEmain PROC call Randomize ; initialize random number generator mov ecx, 20 ; loop 20 times jmp displayText ; jump to displayText to start the loop displayText: ; generate random number between 0 and 9 call RandomRange ; returns random number in EAX mov edx, 0 ; set default color to white cmp eax, whiteProb ; compare with white probability jbe whiteSelected ; jump if less than or equal to white probability cmp eax, blueProb ; compare with blue probability je blueSelected ; jump if equal to blue probability cmp eax, greenProb ; compare with green probability ja greenSelected ; jump if greater than green probability whiteSelected: mov…
- Write an ARM assembly program to convert temperatures from Celsius to Fahrenheit or from Fahrenheit to Celsius. Here are the two formulas for your reference. Use variable to read and store values, you can initialize any integer value into the variables (Do not expect decimal results we are only doing integer operations). C = 5 × (F − 32) / 9 F = (9 × C / 5) + 32 Name the file TempConvert.s add the below commenting statements in the program ;Name: ;Date: ;Give which expression you use Please use LDR/STRPerform a desk check of the following code by walking thru the program and executing it like a computer would. A complete desk check must include: 1. An evaluation of all decision logic indicating the line number of the decision replacing variable names with their values at the time of the evaluation and then indicating if it was true of false.2. A PseudoMonitor™ that shows the output3. A memory map/table that tracks all variable values. Be sure to have three separate areas (three sheets of paper if needed) to document the above. State whether the algorithm represented by the code produces valid results given the obvious objective of the program. If not, explain why not. Even if it works with the given data set, does it contain potential hazards? Explain. Can you optimize the code in any way? You may not execute every line of code depending on the logic of the code and program inputs. Use the following incoming data for your program desk check. INCOMING DATA 3 6…Write a Pep/9 assembly language program that reads an integer value from the keyboard, and displays a table that shows the quotient when the input value is divided by successive powers of 2, between 2 and 32. Your program should produce exactly the same output as the following C program: #include <stdio.h> int inpVal; int divis; int quotient; int main() { printf("? "); scanf("%d", &inpVal); divis = 2; quotient = inpVal / divis; printf("%d / %d = %d\n", inpVal, divis, quotient); divis *= 2; quotient /= 2; printf("%d / %d = %d\n", inpVal, divis, quotient); divis *= 2; quotient /= 2; printf("%d / %d = %d\n", inpVal, divis, quotient); divis *= 2; quotient /= 2; printf("%d / %d = %d\n", inpVal, divis, quotient); divis *= 2; quotient /= 2; printf("%d / %d = %d\n", inpVal, divis, quotient); } **************************** IMP I need in this below example format please don't answer in other ways********************************************
- Develop a python program that will determine the required mass of one compound based on three parameters: (1) compound name, (2) liters of solution, and (3) molarity The input should be in a single text file (input.txt). The required mass should be in a single text file (output.txt). Only two decimal places should be included in the output.txt. Example: *input.txt* compound,liter,molarity NH4Cl, 0.1, 2.5 NaCl, 0.5, 0.25 Na2CO3, 0.75, 1.25 *output.txt* 13.37 7.31 99.36Create a three address statement and convert the three address statement into machine code fromthe following program input snippet:int x=0, k = 0;do{if (k%2==0 && x>0) x++;else x--;k++;} while (k<5);We will use Venus RISC-V simulator for the lab. Please save screenshot of code and output Based on fib.s, please rewrite the code to print full Fibonacci sequence to the console. For example, if n = 5, print 0, 1, 1, 2, 3. Test your program by varying n. Please save the screenshot of the two following test cases: 1) n = 10 2) n = 18 Save your code as task1.s. Here is the fib.s: .data .word 2, 4, 6, 8 n: .word 9 .text main: add t0, x0, x0 addi t1, x0, 1 la t3, n lw t3, 0(t3) fib: beq t3, x0, finish add t2, t1, t0 mv t0, t1 mv t1, t2 addi t3, t3, -1 j fib finish: addi a0, x0, 1 addi a1, t0, 0 ecall # print integer ecall addi a0, x0, 10 ecall # terminate ecall

