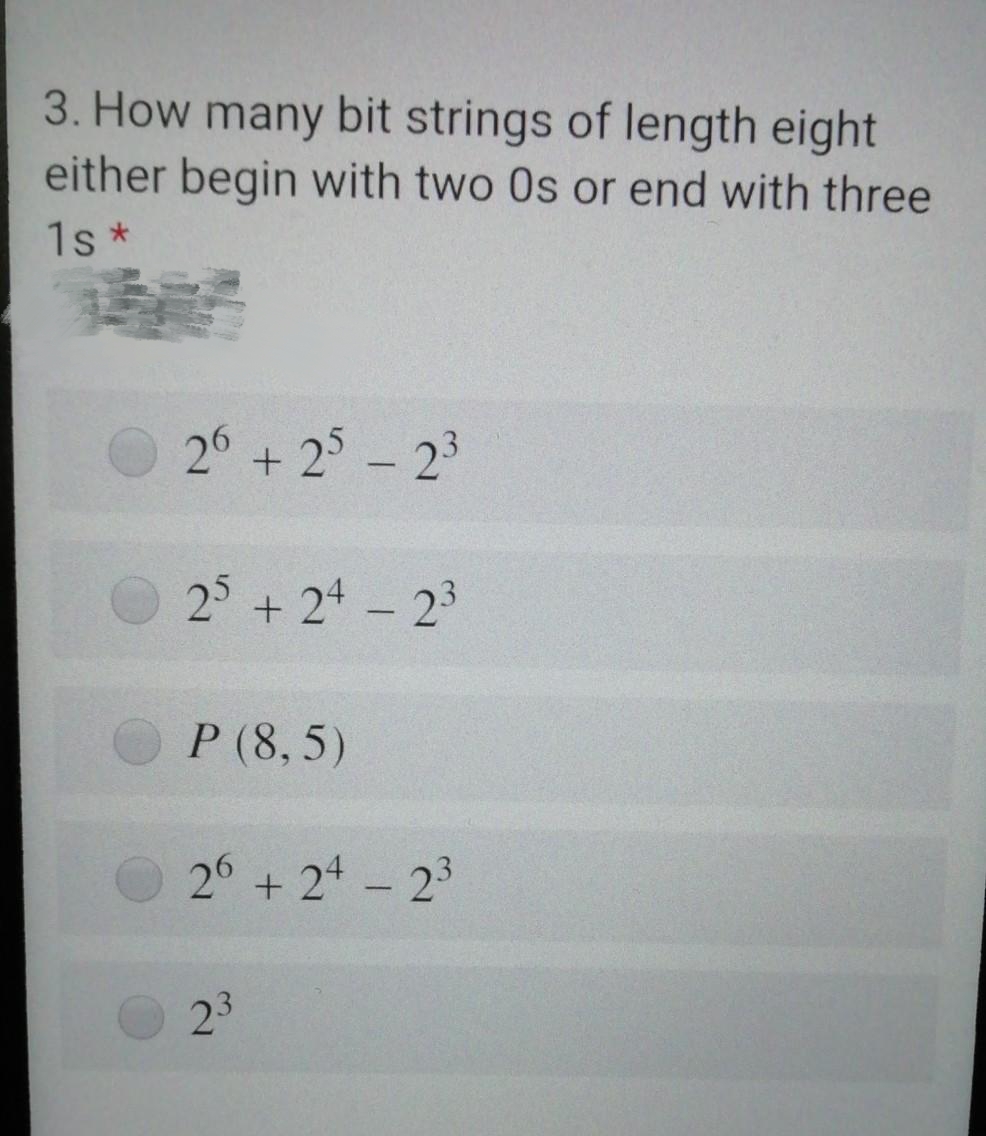
3. How many bit strings of length eight either begin with two Os or end with three 1s* 26 +25 - 23 25 +24 - 2³ P (8,5) 26 + 24 - 23 23
Q: Using multiple approaches, managers may be able to more easily compare and comprehend the results of…
A: Analysis of Performance Result: The most important and technically complex part of performance…
Q: Imagine you get a notification from the mail server of your business informing you that your…
A: The malware that performs password hacking is known as a phishing attack, in which the computer…
Q: Is there a reason why various OSes use different tracks on drives to store directory files? Which of…
A: Introduction: Logical file data is mapped to a physical sector position on the disc using disc…
Q: Write GUI Math Game programme in Java. The programme should generate and display 2 random numbers…
A: The complete GUI Java code is given below in the next steps with code and output screenshots Happy…
Q: You may get the same objectives by generating an Excel workbook instead of a template.
A: IN MICROSOFT EXCEL: It's a spreadsheet containing graphing tools, pivot tables, and a calculator.…
Q: What should you do to defend yourself in the event of a downgrade attack?
A: Introduction:Downgrade attack: This is a form of cryptography attack against a computer system or…
Q: The following are the main distinctions between Scilab and C++:
A: Let's examine what a Scilab is, why it is so popular, and some of its characteristics. Scilab is…
Q: Java - Suppose you have a directed graph representing all the flights that an airline flies. What…
A: Hello student
Q: For those in charge of a group, what do you anticipate from them? What do you like about management,…
A: In charge of a group mainly plays the role of a leader. He or She is responsible for taking all the…
Q: Describe the steps that lead to a downgrade assault.
A: In a downgrade attack, a network channel is forced to move to an unsecured or less secure data…
Q: Give advice on how to maintain a secure wireless network in your house.
A: Your answer is given below.
Q: Run a search on the Internet and visit the website for the Google Book Search Copyright Class Action…
A: The lawsuit alleges "massive copyright infringement" by making digital copies of copyrighted…
Q: There is no restriction on the number of arguments that may be used in a catch block.
A: Introduction: A typical sort of blunder that a modified could experience is a consistent mistake,…
Q: From the perspective of the end user, discuss the advantages and disadvantages of regular software…
A: Software is a term that refers to a collection of instructions, programmed, processes, and other…
Q: What qualities do computer graphics need to have in order to function properly?
A: Quality of computer graphics measured by the image width and height in pixels and also number of…
Q: As an example, consider a database for an airline that makes use of "snapshot isolation". Executions…
A: Consider a database system that uses snapshot isolation for an airline. Reason: Take into account…
Q: Think about software that enables online surgical assistance from a surgeon in one location to…
A: The solution is: We are only allowed to react to the first three subpart, according to the rules:…
Q: Give a brief summary of the nonvolatile solid-state memory technologies that are becoming more and…
A: An explanation will be given on recent advancements made in the area of nonvolatile solid-state…
Q: Give a brief summary of the nonvolatile solid-state memory technologies that are becoming more and…
A: An explanation will be given on recent advancements made in the area of nonvolatile solid-state…
Q: 2.7.1: String with digit. Set hasDigit to true if the 3-character passCode contains a digit.
A: According to the information given:- We have to follow the instruction in order to get the desired…
Q: Give a brief summary of the nonvolatile solid-state memory technologies that are becoming more and…
A: Given: memory that is nonvolatile and made of solid-state. Memory that is resistant to manipulation…
Q: What are some specific ways in which the use of technology may have an effect on educational…
A: Technology is altering the manner in which we learn. From zero to legend, technology has gone a wide…
Q: Using particular examples, describe the key distinctions between a two-tier and a three-tier…
A: These architectures are commonly used to represent database systems and their interconnections. The…
Q: The recommended practices for screening and evaluating vulnerabilities are covered in this article.
A: In light of the facts provided, we must define the vulnerability scanning and assessment sector.…
Q: an you please answer in coral language? The answer is wrong.
A: We need to update numCups variable using coral language.
Q: R6. In CSMA/CD, after the fifth collision, what is the probability that a node chooses K 4…
A: After the collision occurs, for every retransmission, the node will construct a set of numbers known…
Q: Why are linear memory and paging related?
A: Paging is a function that allows a computer to run a combination of applications that would not…
Q: What are the many types of data processing, what does serial and parallel processing include, and…
A: what does serial and parallel processing include, and what are some instances of each? Parallel…
Q: Describe the variations between EPROM, EEPROM, and Flash Memory in your own words.
A: 2. EPROM (erasable programmable ROM) and UV-EPROM EPROM was invented to allow making changes in the…
Q: defining the term and giving specific examples of how to gauge vulnerability?
A: The process of defining, detecting, categorizing, and prioritizing vulnerabilities in an IT system…
Q: Why should a college or institution replace conventional desktop PCs with thin clients? In that…
A: Advantages of using thin customers Thin clients of various enterprises and their IT infrastructure…
Q: For network security and cybersecurity, firewalls are crucial. To illustrate the term's commercial…
A: What are firewalls? A firewall is a network security device that prevents unauthorized access to a…
Q: Java - Suppose you have a game with 5 coins in a row and each coin can be heads or tails. What…
A:
Q: Should companies outsource all of their technology requirements to software service providers only?…
A: The topic that was posed was whether or not businesses should hand over all of their technological…
Q: Exactly what is meant by the term "Memory Management Unit" (MMU)? Just what is its purpose, and how…
A: Memory Management Unit MMU: Virtual addresses utilised by software must be converted into physical…
Q: It is advised that individuals discuss network and cyber security breaches as well as strategies for…
A: justification: Everyone should be aware of the various network and cyber security breaches. 1.…
Q: A small organization is given a block with the beginning address and the prefix length 205.25.36.64,
A: The answer is
Q: Is there a reason why various OSes use different tracks on drives to store directory files? Which of…
A: Below is the complete information about the given question in detail.
Q: Learn more about the many operating systems out there and choose the one that best fits your needs.…
A: File management, memory management, process management, input/output management, and control of…
Q: The operation of "two-tier" and "three-tier" application architectures must be explained. Which of…
A: The patterns and methods used to design and construct an application are described in an application…
Q: The operation of "two-tier" and "three-tier" application rchitectures must be explained. Which of…
A: The answer of this question is as follows:
Q: Why will the existing environmental conditions cause American businesses to face new challenges? How…
A: Business environments change frequently and require consideration when planning and conducting…
Q: Exactly what challenges does the company face when trying to build a diverse workforce? Extend the…
A: Ans- The company faces many challenges when the company tries to build a diverse workforce - 1- The…
Q: Microsoft may no longer update or fix Windows Server, but it is still likely installed on hundreds…
A: Answer: When a vendor quits supporting a piece of software or hardware technology, there are serious…
Q: Which sorts of computerized information systems are most often used now?
A: A computerized information system is the study of how data is stored and processed and the study of…
Q: Is there a certain kind of virus that affects the whole planet, and if so, why
A: Virus is basically something which affects the normal functioning of a system. Here whole planet…
Q: Is it feasible for a business to deploy social computing, a system of technology that incorporates…
A: Solution: Social computing is a network that describes the way individuals communicate their…
Q: The identification and documentation of four sources of vulnerability intelligence are necessary.…
A: Vulnerability Intelligence is a particular type of danger insight zeroed in on the collection or…
Q: If a class B is derived from A, identify which of the following terms can be used to describe A:
A: the answer is an ALL OF THE OPTIONS as given below : Ancestor class Base class Parent class…
Q: You may get the same objectives by generating an Excel workbook instead of a template.
A: MICROSOFT EXCEL: This spreadsheet tool has pivot tables, a graphing calculator, and a macro…
Step by step
Solved in 2 steps with 1 images

- 1. Compact discs record two channels (left and right) of music at a sampling frequency of ??=44.1kHz for each channel. If each sample is encoded with 16 bits, and one byte is 8 bits, how many bytes are required to store 48.1 seconds of music? 2. Consider a system that uses 8-bit ASCII codes to encode letters. How long (in microseconds) will it take to transmit the bit sequence encoding Hello-World! if we use a bit time of 4 samples per bit, and transmit samples at a rate of 1MHz? 3. The ASCII table below gives the ASCII codes for common alphanumeric characters and symbols listed from MSB to LSB. What is the bit sequence encoding the message 113? Assume that we transmit the codes of each character in sequence with the LSB first.1024K words need at least how many address bits?Determine the gi, pi, Pi, and Gi values of these two 16-bit numbers: a: 0001 1010 0011 0011two b: 1110 0101 1110 1011two Also, what is CarryOut15 (C4)?
- (Non-negative signed binary numbers) What happens if all of the zeros on the left side of a non-negative signed binary number are removed? In general, how does one convert a non-negative N-bit signed binary number to an M-bit unsigned binary number, where N ≤ M?3. Consider the generator, G = 10011, and suppose that D has the value 1010101010, and number of CRC bits is r = 4. What is the value R?In other words, how many address bits does 1024K words require?
- How many bit strings of length 10 contain a) exactly four 1s? b) at most four 1s? c) at least four 1s?Consider a SEC code that protects 8 bit words with 4 parity bits. If we read the value 0x375, is there an error? If so, correct the error.Can you tell me how many address bits are required for 1024K words?
- How many bit strings contain exactly five 0’s and ten 1’s if every 0 must be immediately followed by a 1?31 Convert the hexadecimal IEEE format floating point single precision number 0x40200000 to decimal: First convert hex to binary (Provide a space between four bit groups. Example 111 1010 not 1111010) Sign bit Exponent in decimal after removing excess 127. Just the exponent. Example 3 not 23 Mantissa or Significand (Provide a space between four bit groups. Example 111 1010 not 1111010) Put it together and convert to decimalHow many bit strings of length 10 a) begin with 101? b) have weight 3 and begin with 101? c) have weight 5 and begin with 101?

