3. Multiple Choice For each question, select all that apply What can a malicious Bitcoin miner do? a) Create valid transactions originating from someone else's address b) Prevent a valid transaction from getting any confirmations c) Ignore the longest valid branch rule when proposing a new block A 51% attacker (a=0.51) can potentially: a) Steal coins from an existing address b) Make it unprofitable for other miners to mine c) Change the block reward d) Suppress transactions from the block chain If two conflicting transactions A → B and A → C are both broadcast almost simultaneously from different nodes, what determines which one will eventually end up in the block chain? a) The transaction that reaches the majority of nodes first will win b) The transaction that was broadcast first will win c) The miner who finds the next block will likely resolve the tie by including one of the transactions in the block d) Each node has its own version of the block chain containing the transaction that it heard about first
3. Multiple Choice For each question, select all that apply What can a malicious Bitcoin miner do? a) Create valid transactions originating from someone else's address b) Prevent a valid transaction from getting any confirmations c) Ignore the longest valid branch rule when proposing a new block A 51% attacker (a=0.51) can potentially: a) Steal coins from an existing address b) Make it unprofitable for other miners to mine c) Change the block reward d) Suppress transactions from the block chain If two conflicting transactions A → B and A → C are both broadcast almost simultaneously from different nodes, what determines which one will eventually end up in the block chain? a) The transaction that reaches the majority of nodes first will win b) The transaction that was broadcast first will win c) The miner who finds the next block will likely resolve the tie by including one of the transactions in the block d) Each node has its own version of the block chain containing the transaction that it heard about first
Computer Networking: A Top-Down Approach (7th Edition)
7th Edition
ISBN:9780133594140
Author:James Kurose, Keith Ross
Publisher:James Kurose, Keith Ross
Chapter1: Computer Networks And The Internet
Section: Chapter Questions
Problem R1RQ: What is the difference between a host and an end system? List several different types of end...
Related questions
Question
Detailed answer please else I will downvote
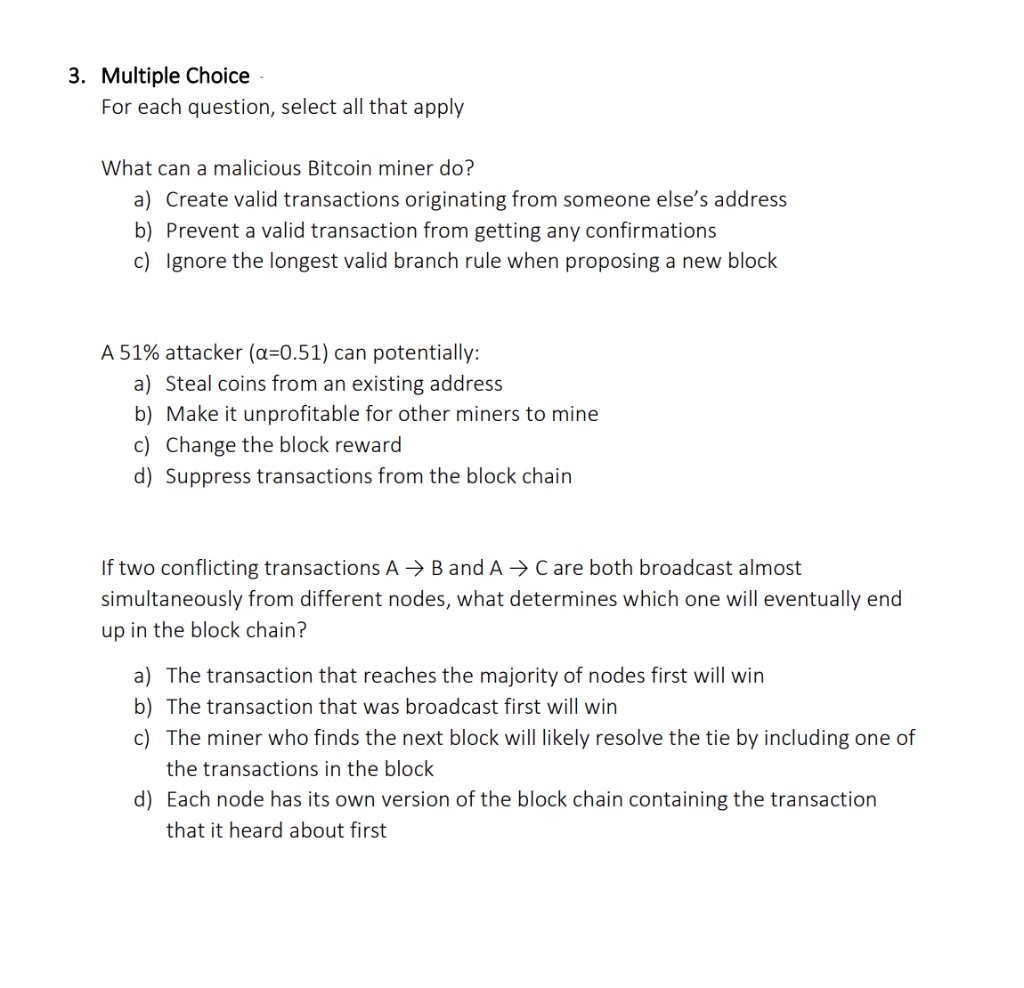
Transcribed Image Text:3. Multiple Choice
For each question, select all that apply
What can a malicious Bitcoin miner do?
a) Create valid transactions originating from someone else's address
b) Prevent a valid transaction from getting any confirmations
c) Ignore the longest valid branch rule when proposing a new block
A 51% attacker (a=0.51) can potentially:
a) Steal coins from an existing address
b) Make it unprofitable for other miners to mine
c) Change the block reward
d) Suppress transactions from the block chain
If two conflicting transactions A → B and A → C are both broadcast almost
simultaneously from different nodes, what determines which one will eventually end
up in the block chain?
a) The transaction that reaches the majority of nodes first will win
b) The transaction that was broadcast first will win
c) The miner who finds the next block will likely resolve the tie by including one of
the transactions in the block
d) Each node has its own version of the block chain containing the transaction
that it heard about first
Expert Solution
This question has been solved!
Explore an expertly crafted, step-by-step solution for a thorough understanding of key concepts.
This is a popular solution!
Trending now
This is a popular solution!
Step by step
Solved in 3 steps

Recommended textbooks for you

Computer Networking: A Top-Down Approach (7th Edi…
Computer Engineering
ISBN:
9780133594140
Author:
James Kurose, Keith Ross
Publisher:
PEARSON

Computer Organization and Design MIPS Edition, Fi…
Computer Engineering
ISBN:
9780124077263
Author:
David A. Patterson, John L. Hennessy
Publisher:
Elsevier Science

Network+ Guide to Networks (MindTap Course List)
Computer Engineering
ISBN:
9781337569330
Author:
Jill West, Tamara Dean, Jean Andrews
Publisher:
Cengage Learning

Computer Networking: A Top-Down Approach (7th Edi…
Computer Engineering
ISBN:
9780133594140
Author:
James Kurose, Keith Ross
Publisher:
PEARSON

Computer Organization and Design MIPS Edition, Fi…
Computer Engineering
ISBN:
9780124077263
Author:
David A. Patterson, John L. Hennessy
Publisher:
Elsevier Science

Network+ Guide to Networks (MindTap Course List)
Computer Engineering
ISBN:
9781337569330
Author:
Jill West, Tamara Dean, Jean Andrews
Publisher:
Cengage Learning

Concepts of Database Management
Computer Engineering
ISBN:
9781337093422
Author:
Joy L. Starks, Philip J. Pratt, Mary Z. Last
Publisher:
Cengage Learning

Prelude to Programming
Computer Engineering
ISBN:
9780133750423
Author:
VENIT, Stewart
Publisher:
Pearson Education

Sc Business Data Communications and Networking, T…
Computer Engineering
ISBN:
9781119368830
Author:
FITZGERALD
Publisher:
WILEY