3.6 LAB: Number pattern Write a recursive function called print_num_pattern() to output the following number pattern. Given a positive integer as input (Ex: 12), subtract another positive integer (Ex: 3) continually until 0 or a negative value is reached, and then continually add the second integer until the first integer is again reached. For coding simplicity, output a space after every integer, including the last. Do not end output with a newline. Ex. If the input is: 12 3 the output is: 12 9 6 3 0 3 6 9 12 409106.2543518.qx3zay7
3.6 LAB: Number pattern Write a recursive function called print_num_pattern() to output the following number pattern. Given a positive integer as input (Ex: 12), subtract another positive integer (Ex: 3) continually until 0 or a negative value is reached, and then continually add the second integer until the first integer is again reached. For coding simplicity, output a space after every integer, including the last. Do not end output with a newline. Ex. If the input is: 12 3 the output is: 12 9 6 3 0 3 6 9 12 409106.2543518.qx3zay7
Chapter5: Looping
Section: Chapter Questions
Problem 12E
Related questions
Question
def print_num_pattern(num1, num2):
if num1 <=0:
print("0", end="")
return
print(num1, end="")
print_num_pattern(num1 - num2, num2)
print(num1, end="")
if __name__ == "__main__":
num1 = int(input())
num2 = int(input())
print_num_pattern(num1, num2)
Transcribed Image Text:CTU Assignment List
SCTU Messenger
zy Section 3.6 - CS 219T: Python Pro X
✰ learn.zybooks.com/zybook/CS219-2203A-03-2203A/chapter/3/section/6
=zyBooks My library > CS 219T: Python Programming home > 3.6: LAB: Number pattern
409106.2543518.qx3zqy7
LAB
3.6.1: LAB: Number pattern
ACTIVITY
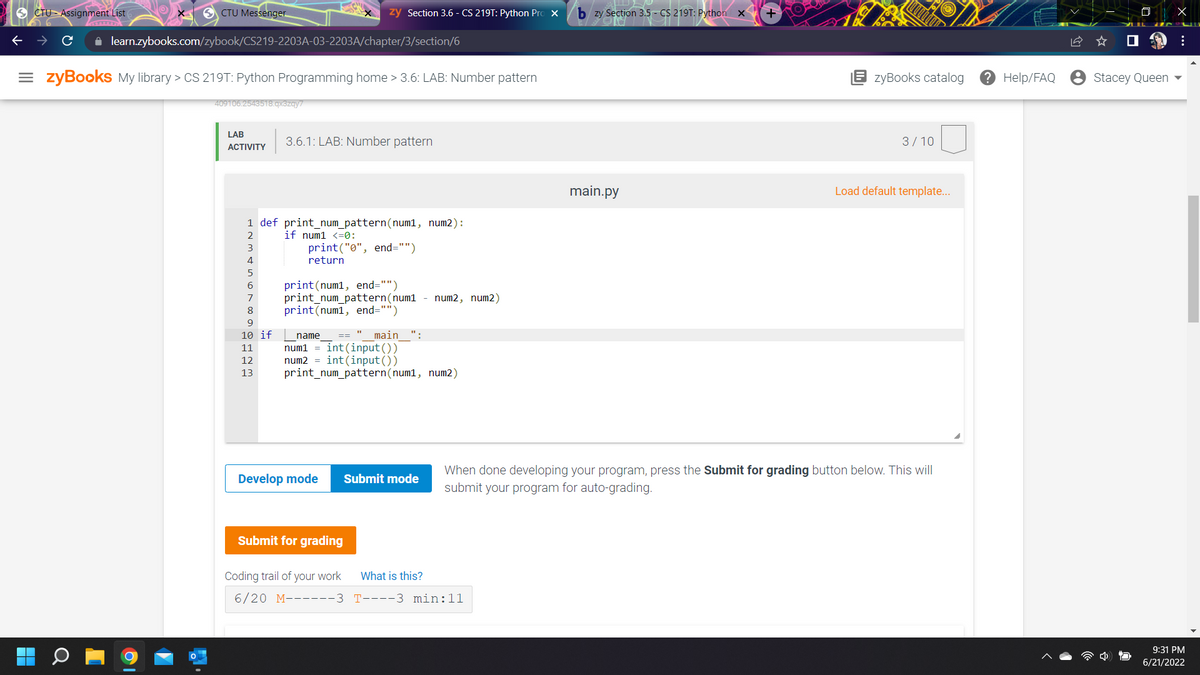
1 def print_num_pattern(num1, num2):
if num1 <=0:
3
print("0", end="")
return
5
6
print (num1, end="")
print_num_pattern (num1 - num2, num2)
8
print (num1, end="")
9
10 if
name == main ":
11
num1 = int(input())
12
num2= int(input())
13
print_num_pattern(num1, num2)
Develop mode
Submit mode
Submit for grading
What is this?
Coding trail of your work
6/20 M------3
T----3 min:11
bzy Section 3.5- CS 219T: Python X
main.py
+
zyBooks catalog
3/10
Load default template...
When done developing your program, press the Submit for grading button below. This will
submit your program for auto-grading.
? Help/FAQ
Stacey Queen
X
:
9:31 PM
6/21/2022
Transcribed Image Text:CTU Assignment List
SCTU Messenger
zy Section 3.6 - CS 219T: Python Pro X
+
✰ learn.zybooks.com/zybook/CS219-2203A-03-2203A/chapter/3/section/6
=zyBooks My library > CS 219T: Python Programming home > 3.6: LAB: Number pattern
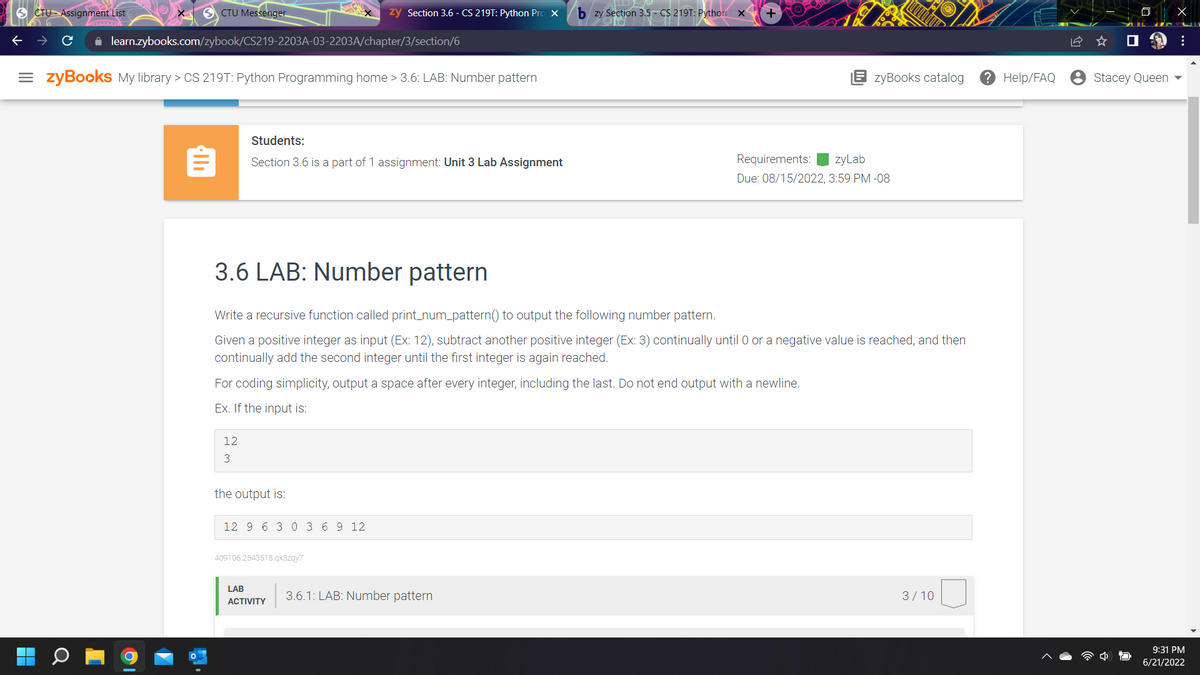
Students:
Section 3.6 is a part of 1 assignment: Unit 3 Lab Assignment
Requirements: zyLab
Due: 08/15/2022, 3:59 PM -08
3.6 LAB: Number pattern
Write a recursive function called print_num_pattern() to output the following number pattern.
Given a positive integer as input (Ex: 12), subtract another positive integer (Ex: 3) continually until 0 or a negative value is reached, and then
continually add the second integer until the first integer is again reached.
For coding simplicity, output a space after every integer, including the last. Do not end output with a newline.
Ex. If the input is:
12
3
the output is:
12 9 6 3 0 3 6 9 12
409106.2543518.qx3zqy7
LAB
3/10
ACTIVITY
3.6.1: LAB: Number pattern
bzy Section 3.5- CS 219T: Python x
zyBooks catalog ? Help/FAQ
Stacey Queen
X
:
9:31 PM
6/21/2022
Expert Solution
This question has been solved!
Explore an expertly crafted, step-by-step solution for a thorough understanding of key concepts.
This is a popular solution!
Trending now
This is a popular solution!
Step by step
Solved in 2 steps with 1 images

Follow-up Questions
Read through expert solutions to related follow-up questions below.
Follow-up Question
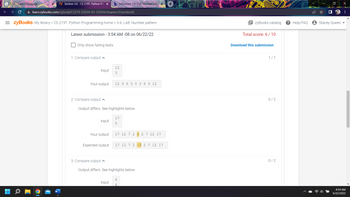
I am not sure why, but this second block is still not passing. The code gave me 6 out of 10 correct. I must be missing something.

Transcribed Image Text:CTU Class Homepage.
zy Section 3.6 - CS 219T: Python Pro X b Answered: 3.6 LAB: Number pati X
+
learn.zybooks.com/zybook/CS219-2203A-03-2203A/chapter/3/section/6
=zyBooks My library > CS 219T: Python Programming home > 3.6: LAB: Number pattern
zyBooks catalog
409106.2543518.qx3zqy7
LAB
3.6.1: LAB: Number pattern
6/10
ACTIVITY
main.py
Load default template...
1 def print_num_pattern(num1, num2):
2
if num1 <=0:
3
print("0", end=" ") # If first number is less than or equals to then print o
return
5
# print the first number before subtracting
print (num1, end=" ")
print_num_pattern (num1
num2, num2) # Recursive calling to subtract the second number by first number
print (num1, end=" ") # print the first number after subtracting
8
9 if
___name
main ":
num1 = int (input()) # Taking input for two numbers
num2 = int (input())
print_num_pattern(num1, num2)
Submit mode
Run your program as often as you'd like, before submitting for grading. Below, type any needed
input values in the first box, then click Run program and observe the program's output in the
second box.
Input (from above) →→→
main.py
(Your program)
Output (shown below)
10
11
12
Develop mode
Enter program input (optional)
12
3
Run program
? Help/FAQ
Stacey Queen
X
:
4:54 AM
6/22/2022
Transcribed Image Text:zy Section 3.6 - CS 219T: Python Pro X b Answered: 3.6 LAB: Number pat X +
CTU Class Homepage.
✰ learn.zybooks.com/zybook/CS219-2203A-03-2203A/chapter/3/section/6
= zyBooks My library > CS 219T: Python Programming home > 3.6: LAB: Number pattern
Latest submission - 3:54 AM -08 on 06/22/22
Only show failing tests
12
3
12 9 6 3 0 3 6 9 12
1: Compare output
2: Compare output
Input
Your output
Output differs. See highlights below.
Input
17
5
Your output
17 12 7 2
2 7 12 17
Expected output
17 12 7 2 -3 2 7 12 17
3: Compare output
Output differs. See highlights below.
6
Input
zyBooks catalog
Total score: 6/10
Download this submission
1/1
0/2
0/2
? Help/FAQ
Stacey Queen
X
:
4:54 AM
6/22/2022
Solution
Knowledge Booster
Learn more about
Need a deep-dive on the concept behind this application? Look no further. Learn more about this topic, computer-science and related others by exploring similar questions and additional content below.Recommended textbooks for you

Microsoft Visual C#
Computer Science
ISBN:
9781337102100
Author:
Joyce, Farrell.
Publisher:
Cengage Learning,

Microsoft Visual C#
Computer Science
ISBN:
9781337102100
Author:
Joyce, Farrell.
Publisher:
Cengage Learning,