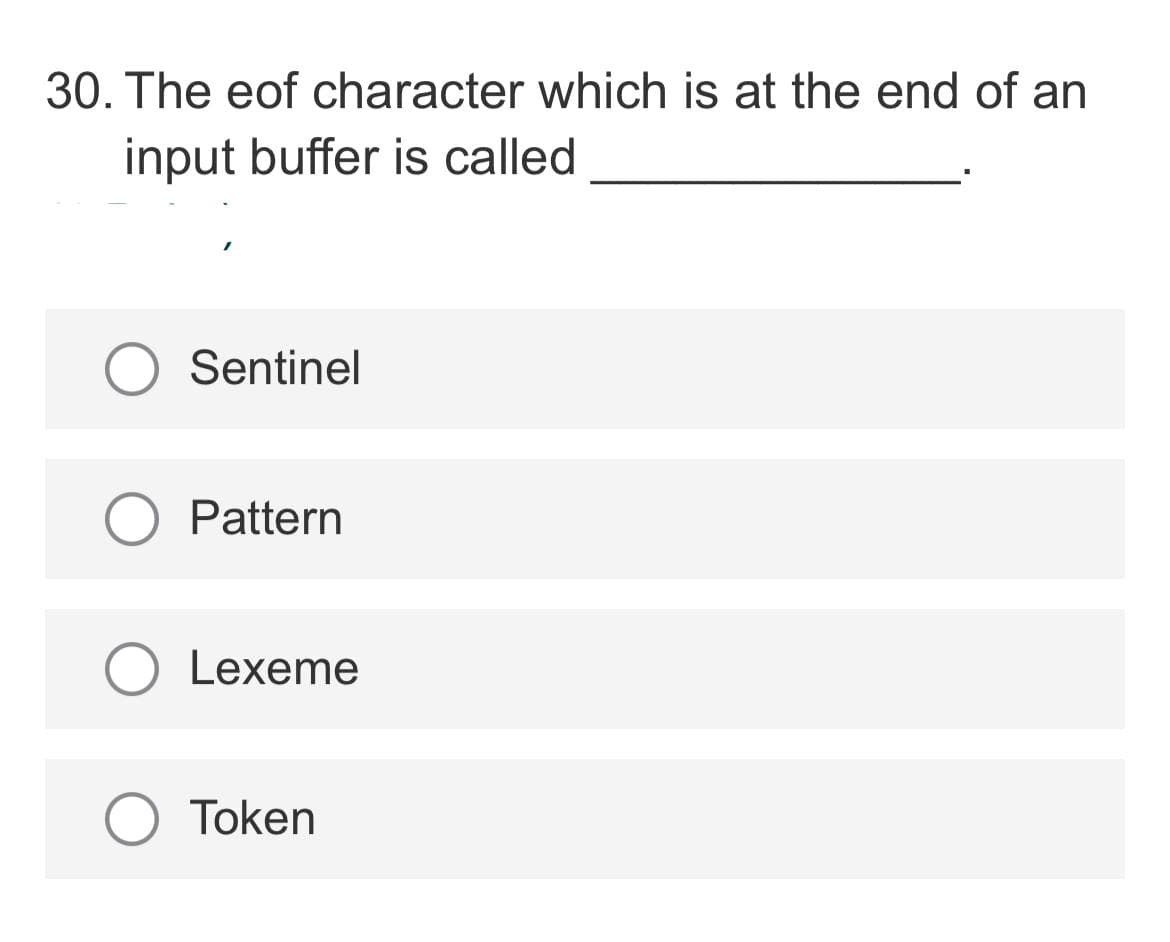
30. The eof character which is at the end of an input buffer is called Sentinel Pattern Lexeme O Token
Q: How many networks has the routing protocol learned? Computer science
A: Introduction: Routing protocols are means for exchanging routing information between routers in orde...
Q: What what is dynamic scoping, and how should it be applied? What effect does dynamic scoping have on...
A: Intro According to the question The scoping control done how to variable value is the resolved and ...
Q: What exactly is a class? What exactly is a superclass?
A: Intro A superclass is a class that may be used to build a large number of subclasses. The attribute...
Q: Create the following table in your database with the following schema: Table: Products I Column Name...
A: Create table syntax : CREATE TABLE TABLE_NAME( column_name data_type, column_name data_type, ...
Q: Find f (1), f (2), f (3), and f (4) if f(n)-f(n+1)-f(n)2 +f(n)+1 where f(0)-1.
A: The function can be evaluated by consider the previous function. The type of the function in the que...
Q: Explain all of the options available to you during Linux configuration and installation.
A: Linux is an open-source operating system that is free to download and install on any computer. There...
Q: Sustaining and disruptive innovation are two types of innovation.
A: Intro Sustained innovation is defined as the improvement of an existing product. Companies that prod...
Q: Short answer Why are disk files broken up into blocks and scattered across the disk surface(s)? Co...
A: Introduction: In a computer, a disc is used to store data. To boost the speed of data storage, the d...
Q: Is there a connection between an individual's educational process and his or her physical and cultur...
A: Introduction: When attempting to understand human nature and ability, sociocultural, evolutionary, a...
Q: What happens when an array is sorted using a selection sort
A: Introduction: The smallest element in an unsorted array is brought to the front of the selection sor...
Q: What perspectives should be taken into account while developing models for software-intensive system...
A: Intro In order for academics and practitioners to use and construct very big and complex systems, p...
Q: Explain the words multidimensional and parallel using an example.
A: Introduction: Multidimensional databases: A multidimensional database (MDB) is a special type of dat...
Q: write a void function that has two parameters- a value parameter called num that receives a floating...
A: Start main function: Accept the number Calling function pass floating-point number and reference par...
Q: Question 4 Endianness Assume that a snippet of memory is shown below (in hex), starting with the byt...
A: 4. Given, Address starts with 0x10. Data is : | 77 | AB | 69 | CA | 0D | F0 | 12 | BE | The system ...
Q: In Java, please comment and comment with output please This programming assignment involves learn...
A: The below program is written in Java and complete code is provided below:
Q: Recently your company discover that there were several alerts for software that your company uses. ...
A: For the Given Situation the presentation to the executives and managers has written below.
Q: eat trees or threat asset seem the best way to develop a secu
A: would threat trees or threat asset seem the best way to develop a security assessment methodolgy
Q: What is the third natural state, in your opinion? How do you transform a two-dimensional design into...
A: The third standard form is: The normalization process reaches its third level using the third standa...
Q: Please draw a 3D cube using OpenGL. Do not use glut or freeglut library. Thank you.
A: Open Gl 3D graph
Q: Discuss the areas of overlap between security and privacy and the areas that are distinct to either ...
A: Areas of overlap between security and privacy are: Accuracy: As Data is stored in the server of the...
Q: Network scheduling. Describe in detail the importance and relevance of network scheduling. What does...
A: Answer : Network Schedule Network Schedule (Scheduling) is a graphical representation of a logical o...
Q: Complete the Stadium class so that it has an inner class singleton Comparator (sorting strategy) cal...
A: ANSWER:-
Q: 1. Consider a schema R = (A, B, C, D, E). Assume that the following set F of functional dependencies...
A: The closure of attribute A is a set of those attributes which can be functionally determined by A an...
Q: Write a function median_filter(img, s) that takes as its argument a numpy img array representing an ...
A: Note : Answering the question in python as no programming language is mentioned. Input : Input imag...
Q: Philip Emeagwali, at 17, invented the world's fastest computer.
A: Introduction: Philip EmeagwaliBorn in 1954, Philip Emeagwali is a Nigerian computer scientist. He is...
Q: ;Address of q00003 ;Function q00003 ;Getting return ade q00003, AND fnc026 fnc026, CLE BSA pop STA t...
A: Below the Assembly code which resolve the error
Q: Which of the following is not included in the class table while developing an object-oriented design...
A: Object-oriented design consists of the architecture of the system that is going to be developed.
Q: AND fnc026 ;Address of qe0003 ;Function q00003 ;Getting return addres CLE BSA pop STA temp1 BSA pop ...
A: Below the code which resolve the error
Q: What are the advantages and disadvantages of installing software via the internet versus installing ...
A: Introduction: DVD: DVD is an abbreviation for Digital Versatile Disk or Digital Video Disk. Because ...
Q: When should you use a binary search?
A: It is an searching algorithm which follows the divide and conquer approach. In this approach the fir...
Q: How can you tell which motherboard you have?
A: A motherboard is the most essential part of the computer hardware which connects and make the system...
Q: What does the word "Speech Recognition" mean?
A: Introduction: We can express what we can accomplish by speaking solely to our gadgets thanks to spee...
Q: CREATE A BAR PLOT IN JUPYTER LAB USING MATPLOTLIB 1. Given the text below, create a bar plot (or...
A: The code is given below.
Q: How Critical Is Cybercrime Research
A: Let's see the solution
Q: What benefits does MATLAB have over other programming languages for tackling Computational Geometry ...
A: INTRODUCTION: MATLAB MATLAB is a programming platform created specifically for engineers, trainees, ...
Q: Q.2/ Write a program to enter a value of x and compute the value of y where y= x if x20 -x if x<0
A: As per the requirement program is developed. Note: In the question programming language is nor menti...
Q: Develop a program which deciphers the string "Wg ngeb3i3rtiw3y h2no dnt1e eh7f ni3psim2ddn2" which i...
A: The full JAVA code is given in next step along with output:
Q: Short answer What are the advantages of using virtual memory? Computer science
A: Introduction: Virtual memory is a memory management approach that permits idealised abstraction of a...
Q: Do you believe that if you hit a key on the keyboard while a programme is creating a disc file, the ...
A: Introduction: An IRQ (interrupt request) value is a spot on the computer where it may anticipate a s...
Q: How far have robots come, and how intelligent do you believe they will become in the future?
A: Introduction: Some experts believe that by 2045, robots will outsmart humans. Others believe it will...
Q: What exactly is a consistent database state, and how does it come about?
A: Solution A database constitutes a set of data relevant to some real-world aspect. For a certain miss...
Q: What is a host-based IDS?
A: Introduction: A HIDS allows you to see what's going on with your important security systems in real-...
Q: reate prolog predicates for non-self-balancing 2-3 Trees. Details: add(X, T1, T2) is true if addin...
A: answer is given below step:-1 The term predicate is utilized in one of two ways in semantics and its...
Q: A jiffy" is the scientific name for 1/100th of a second. Given an input number of seconds, output th...
A: As given, we need to write a Java program that converts the input number of seconds into number of j...
Q: Assembly to Binary 2 An LC-3 assembly language program contains the instruction LEA R6, Z The symbol...
A: Explaination, As we know that the value stored at Y ie at x3005 will be the 16 bit binary code for t...
Q: 1. How many stacks are required for evaluation of prefix expression? a) one b) two <) three d) four
A: Lets see how many stacks needed for prefix expression evaluation and what are the names of those sta...
Q: Identify and briefly describe four of the causes of the rising number of computer-related errors.
A: Intro With the increase in use of computer at work or at personal level, humans are dependent on com...
Q: What are some of MongoDB's drawbacks?
A: Introduction: MongoDB is a document database that is utilized to build highly accessible and scalabl...
Q: What is the definition of normalization in a database management system?
A: Normalization: - It is a technique in database architecture that decreases data redundancy and remov...
Q: What happens when an array is sorted using a selection sort?
A: Here, we are going to discuss what happens when an array is sorted using a selection sort.
5
Step by step
Solved in 2 steps with 2 images

- The notion of a buffer overflow should be explained.191. In the buffer where there is no space for another block, the bllock can be inserted using a. Pinned block strategy b. Forced output block c. Buffer replacement strategy d. All of the mentionedDescribe the format of a read buffer, along with the code for the rio_readinitb function that initializes it.
- 142. The subsystem responsible for the allocation of buffer space is called as _______ a. Buffer allocator b. Buffer manager c. Buffer enhancer d. Buffer intermediaryc or c++ program for producer consumer example for unbounded buffer or when buffer size is n in operating system194. The frequently used buffer replacement strategy is a. Most recently used b. Least recently used c. Longest block d. All of the mentioned
- 513. A buffer where the data will be read into and written from is a. LPVOID Buffer b. LPOut Buffer c. LPIN Buffer d. LBLOCK BufferA buffer overflow is a concept that has to be laid out.Subject: Microcpmputer Interface and Technology 1. Assume that a chunk of data is stored in a memory block that starts with variable BUFFER. The memory block contains 50 bytes in total. Write a program that can count the number of positive numbers in the chunk of data and store the result of counting into a variable NUMBER.
- 190. The subsystem responsible for the allocation of buffer space is called the ___________ a. Buffer b. Buffer manager c. Storage d. Secondary storage195. In case the buffer manager do not write the blocks properly then the buffer manager uses a. Replacement strategy b. Forced strategy c. Crash recovery system d. Both Replacement and Forced strategyThe ReadString procedure reads a string from the keyboard, stopping when the user presses the Enter key. Pass the offset of a buffer in EDX and set ECX to the maximum number of characters the user can enter, plus 1 (to save space for the terminating null byte). The procedure returns the count of the number of characters typed by the user in EAX. Sample: .data buffer BYTE 21 DUP(0) ; input buffer byteCount DWORD ? ; holds counter remrk byte “Enter a string: “,0 .code main proc mov edx,OFFSET buffer ; point to the buffer mov ecx,SIZEOF buffer ; specify max characters call ReadString ; input the string mov byteCount,eax ; number of characters ReadString automatically inserts a null terminator in memory at the end of the string. The following is a hexadecimal and ASCII dump of the first 8 bytes of buffer after the user has entered the string “ABCDEFG” Question: Reverse a string but the string from a user using ReadString procedure. Please comment…



