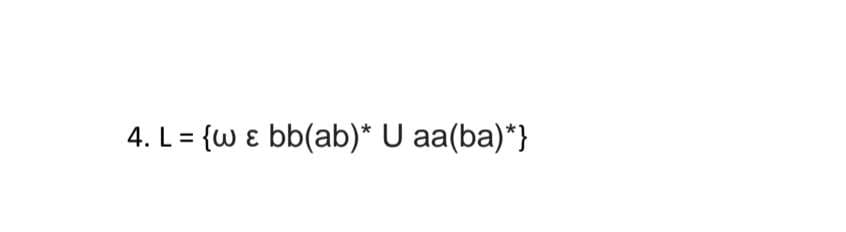
4. L = {w & bb(ab)* U aa(ba)*}
Q: Establish a distinction between batch and online data input methods. Give a concrete illustration of…
A: Batch and Online input methods Batch input methods: Batch input simply refers to entering data in a…
Q: Consider the system models' advantages and disadvantages.
A: Introduction: System modeling is constructing abstract models of a system, each of which gives a…
Q: Objective: Design and implement a word unscrambler game in Java. Details: Your program should read…
A: Given data, We need to design and implement a word unscrambler game in Java. The program should read…
Q: Please use R-programming. Please provide the WHOLE source code (please make it to where you can copy…
A: We need to solve the given scenario using R language.
Q: The point-to-point tunneling protocol uses what transport layer proto
A: An outdated technique for establishing virtual private networks is the Point-to-Point Tunneling…
Q: The identical file deletion process is used by Symbian, Android, and iPhone. How does this impact…
A: Introduction: It is designed for touchscreen mobile devices such as smartphones and tablets, but it…
Q: Explain how formative assessment may be used to get around user obstacles and improve a system's…
A: While we are in the process of evaluating Don Norman's conception, we have discovered that there are…
Q: Best First Search algorithm needs code in python for following image graph
A: create a queue Q mark v as visited and put v into Q while Q is non-empty remove the head u of…
Q: algorithm to Outline for simulating (n, k)-coded digital communications
A: The correct answer for the above mentioned question id given below steps
Q: What hardware is able to configure and manage networking devices both physically and virtually?
A: Introduction: SDN controller: A SDN is software-defined networking that functions as a centralised…
Q: Some claim that using commercially available software is the most effective way to reduce system…
A: Off the shelf software is mass-produced, available to the public, and ready for use. They provide a…
Q: COMPARING THE EFFICIENCY OF THE STRING AND STRINGBUILDER CLASSES
A: COMPARING THE EFFICIENCY OF THE STRINGAND STRINGBUILDER CLASSES:
Q: Comment on the advantages and disadvantages of using the significant figures rules to retain the…
A:
Q: What causes bugs in the first place? How does a computer program bug get in? Give a few examples.
A: Introduction: Bugs are caused by software development mistakes. As SDLC steps are interrelated, bugs…
Q: The OSI model's combined session, presentation, and application levels are referred to as the TCP/IP…
A: TCP/IP includes collection and techniques for coping with media access, session interaction, data…
Q: What is CMRR?
A:
Q: The following five justifications highlight the relevance of standard software patches and updates:…
A: INTRODUCTION: Patches: Software and operating system (OS) patches are updates that fix a program's…
Q: 5.16 LAB: Adjust list by normalizing (JAVA) When analyzing data sets, such as data for human…
A: Here I have taken input from the user and then using the input I have created the array. Next, I…
Q: Create a Java program with a method that searches an integer array for a specified integer value…
A: code- import java.util.Scanner; public class Main{ public static int returnindex(int[] haystack ,…
Q: 1. Suppose we are in the middle of a proof and our current goal is: S(c)→(∀d)(M(d)→R(d,c)) Suppose…
A: “Since you have asked multiple questions, we will solve the first question for you. If you want any…
Q: containing a high proportion of components that area unit zeros. Sparse matrices of large order are…
A: Sparse Matrix is a matrix in that most of the weather square measure zero. thin matrix represents a…
Q: ns exist between telephone and data communications? Consider them to be a single group. What proof…
A: Introduction: Information may be sent across great distances through a mechanism known as…
Q: Problem 1. Illustrate the operation of RADIX-SORT on the following list of English words: COW,…
A: “Since you have asked multiple question, we will solve the first question for you. If you want any…
Q: Which kind of network address translation enables a large number of users to access the worldwide…
A: Introduction: Port Address Translation (PAT) is an extension of Network Address Translation (NAT)…
Q: Describe the importance of user requirements documentation for systems analysts.
A: The above question is solved in step 2 :-
Q: Identify 5 syntax errors from the following code and write the correct code in the word document.…
A: Below I have provided a program for the given question. Also, I have attached a screenshot of the…
Q: What makes disk encryption distinct from file encryption?
A: Full-disk encryption is the term used to describe the encryption of a complete disc drive. With…
Q: Because microprocessor CPUs do not understand mnemonics as they are, they have to be converted to…
A: Microprocessors use binary machine code, commonly referred to as machine language. The central…
Q: Describe Vector clock algorithm with example.
A: The question is about one of the algorithms of a distributed system. I have to provide an…
Q: An Algorithm for Topological Sorting
A: An Algorithm for Topological Sorting :-
Q: Throughout the software development process, it is crucial to talk about what software security is…
A: Introduction: Advantages of a secure SDLC include:Includes all players in security planning.Early…
Q: Describe the qualities needed for test-driven development. If you wanted to utilize it as a teaching…
A: Test-Driven Development which are the one such practice that are now recognized as an efficient…
Q: The following three components are necessary for an effective network: What is a good illustration…
A: Hi please find the solution below and I hope it would be helpful for you.
Q: What makes disk encryption distinct from file encryption?
A: File encryption By encrypting files, file encryption helps to protect your data. It can only be…
Q: You have been given the duty of developing an integrated interactive solution to computerize…
A: This inquiry has to do with software engineering. The main thing a project manager does is go over…
Q: The two header files a.h and b.h both have a prototype for a single function. Both have at least two…
A: Please find the fix version below of this problem
Q: True or false? 1. 4+3n is O(n) 2. n+2 logn is O(log n) 3. logn+2 is 0(1) 4. n is 0(1.1")
A: True or false? 1. 4 + 3n is O(n) 2. n + 2 logn is O(logn) 3. logn+2 is O(1) 4. n50 is O(1.1n )
Q: Which is better, the improved binary search tree or the conventional binary tree?
A: The above question is solved in step 2 :-
Q: Make a note of all the significant steps you completed to identify classes while using a class-based…
A: A class can be thought of as an outline or as a collection of instructions for putting together a…
Q: what transport layer protocol is used by the point-to-point tunneling protocol?
A: Transport Layer Through flow control, segmentation & desegmentation, and error management, the…
Q: Why is hashing passwords stored in files preferable than encryption?
A: Hashed passwords cannot be decrypted and require an attacker to guess them, which can be made hard.…
Q: What is 60 seconds in a decimal format?
A: 60 seconds as a decimal - Time to Decimal Calculator
Q: Can defects be eliminated by clever software design? Is there a good or bad explanation for this?
A: A bug is a mistake, defect, failure, or fault in a computer programme or software system that…
Q: The advantages of using the Work Breakdown Structure (WBS) idea should be shown using a typical…
A: In project management and systems engineering, a work breakdown structure (WBS) is a technique used…
Q: at is CMRR
A: Solution - In the given question, we have to tell what is CMRR.
Q: Let S = {1,2,3}. Let be the relation on Sx S defined by (a, b) (c,d) a ≤ c and b>d (a) Show that is…
A:
Q: Predict the output of the following code "52"); ?> foreach(Sa as Sx => Sval) { echo = Sval"; } a.…
A: BELOW COMPLETE SOLUTION REGARDING YOUR PROBLEM :
Q: Write a program in java that reads a list of integers from input into an array and outputs "yes" if…
A: There is one Java Code given. I have to complete that code so that it can provide the output…
Q: When describing processes that are not a part of the systems analysis process, use structured…
A: It will be taught how to use structured English to describe processes that have nothing to do with…
Q: Assume that we have a free chain complex with a basis (C∗, Ω), and an acyclic matching M. Then C∗…
A: Assume that we have a free chain complex with a basis (C∗, Ω), and an acyclicmatching M. Then C∗…
Step by step
Solved in 2 steps with 1 images

- 5. A function can return a value of an enumeration type. True FalseT/F The << operator is overloaded to input data items of fundamental types, strings and pointer valuesUsing C Language Define a struct student that stores the information about a student (name, age, GPA, semester). Write a function that accepts an array of students and returns the number of students with GPA greater than or equal 3.4.
- MULTIPLE FUNCTIONS AND RECURSIVE FUNCTIONS Use #include<stdio.h>he function drawFractalLine is recursive. Write a script that draws the Koch snowflake. Define a function main that will draw a Koch snowflake with the following parameters when the program is run: Width = 200 Height = 200 Size = 150 Level = 4(Data processing) A bank’s customer records are to be stored in a file and read into a set of arrays so that a customer’s record can be accessed randomly by account number. Create the file by entering five customer records, with each record consisting of an integer account number (starting with account number 1000), a first name (maximum of 10 characters), a last name (maximum of 15 characters), and a double-precision number for the account balance. After the file is created, write a C++ program that requests a user-input account number and displays the corresponding name and account balance from the file.
- (Conversion) Write a C++ program that converts gallons to liters. The program should display gallons from 10 to 20 in 1-gallon increments and the corresponding liter equivalents. Use the relationship that 1gallon=3.785liters.If integer pointer aPtr is to point at a data item whose value may not change it must be declared as ... A. const int * const aPtr; B. int *aPtr; C. int *const aPtr; D. const int *aPtr;Ga.vafi a boolean array Apple. ~ Apple[i]=True represents apple is fresh. Apple[i]=False represents apple is rotten. Write a function that takes the array and array size as ~ parameter and print the number of fresh and rotten - In C++. Test the function using the array Apple[1-{1,
- Define argumentC Program Pass-by-reference in Functions Using Pointers Write a function swap that swaps the values of three integers x,y, and z. x is swapped to y, then y to z, and lastly z to x. In the main function, write a program that ask for theee integer inputs and pass in the reference of those variables by calling swap function. more details below the photo.Using C Program: Create a calculator program that works like a real calculator. It means that the user could enter as much number as they want. Ex: 1+1+1+1+1+1+2+2+2.... Create this by only using functions and arrays. Avoid using switch.









