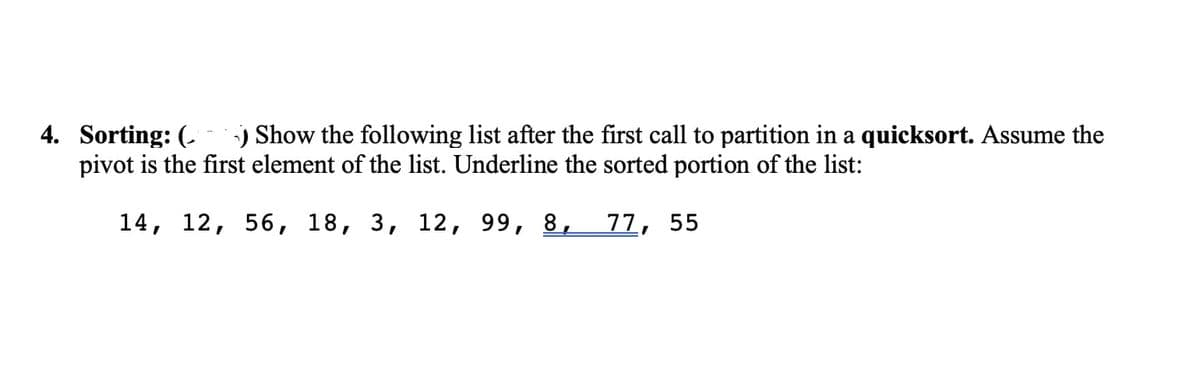
4. Sorting: ( Show the following list after the first call to partition in a quicksort. Assume the pivot is the first element of the list. Underline the sorted portion of the list: 14, 12, 56, 18, 3, 12, 99, 8, 77, 55
Q: Describe briefly five techniques for lowering the risk of an information security compromise.
A: Intro Launch: Risk Control Strategies are used by IT and Info Sec departments to limit…
Q: In computer security access management, discuss the differences between groups and roles.
A: Difference between Groups and Roles in computer security access management .
Q: Which parts of the information system are regarded organizational, managerial, and technical?
A: Given: Organizational, administrative, and technical factors all have a role. Senior managers often…
Q: What are the specific advantages of running the server application ahead of the client application?…
A: Intro what's the point of running the server application before the client? Which software should…
Q: How does the security of a cloud computing environment compare to that of a traditional data centre…
A: On-premises data center: The term "on-perm" refers to private server farms that businesses maintain…
Q: The OSI security architecture contains a wide array of advanced precautions to ensure the…
A: Introduction: All packets take the same path between their origin and destination.
Q: When testing, I get the following error, Can you please help…
A: java.lang.OutOfMemoryError: Java heap space Increase the heap size is not fix it is 100% temporary.…
Q: ble for an application to receive a reliable data transmission while it is simultaneously operating…
A: Introduction: UDP is more appealing in applications like as streaming and VOIP, which can tolerate…
Q: Are ScoutSuite, Pacu, and Powler all cloud-based security solutions? A cloud environment's…
A: Introduction: As cloud development evolves, it's not unusual for IT teams to identify flaws in…
Q: When it comes to cloud security, what exactly do you mean when you refer to the shared…
A: Launch: A shared responsibility paradigm is a cloud security perspective that establishes the…
Q: The study of computers Which protocol uses secure socket layer (SSL) or transport layer security…
A: Which protocol uses secure socket layer (SSL) or transport layer security (TLS) to encrypt…
Q: Software development utilizes a large variety of models, each with varying importance depending on…
A: Introduction: Several models are used in software development, with each model having a different…
Q: Was the algorithm used to erase files affecting the performance of the Symbian, Android, and iPhone…
A: Introduction: The algorithm impacted Symbian, Android, and iPhone. Android was affected by Detection…
Q: How can one distinguish between the positive and bad elements of various authentication procedures,…
A: Intro Authentication determines whether a person or object is who or what they claim to be.…
Q: To what extent may a universal programming language have a negative impact?
A: Universally understood programming language: Every every coder has something to gain from learning…
Q: here are a number of languages that may be used to write computer code. Each thing on the following…
A: Given: What are the various computer programming languages? Give a quick summary of each. A total of…
Q: Isn't it by design that different systems store disc folders at different track places on the disc?…
A: Intro The advantages of establishing many partitions include the following:" Because the operating…
Q: 8. without using any standard template library Write code for DAG shortest path algorithm to find…
A: For a general weighted graph, we can calculate single source shortest distances in O(VE) time using…
Q: In this discussion, we will focus on the role that the operating system plays in the application I/O…
A: Introduction: In this discussion, we will focus on the role that the operating system plays in the…
Q: A computer network is defined as what exactly? What are the many different parts that make up the…
A: A computer network is defined as what exactly? A computer network, likewise alluded to as an data…
Q: Number of edges in connected undirected graph must be many than vertices. Answer = True or False?
A: Here in this question we have asked weather the given statement is true or false. Number of edges in…
Q: What are the obstacles to implementing mobile technology? Is the average household saving the same…
A: Mobile technology : The primary applications for mobile technology are in cellular communication and…
Q: X If a program requires 270,000.000 clock cycles to execute on a processor running on a clock of…
A:
Q: Model-driven engineering has many advantages, but how successful is it in practice?
A: Intro Network security: Data is a company's most important resource, thus network security is…
Q: There are significant distinctions between software modeling and software development. Explain how…
A: Intro The Methods Used in the Creation of Software: In software engineering, the practise of…
Q: Please identify the three methods for recording WORM discs.
A: Introduction: There are three options for recording WORM discs available to users:
Q: For cloud security, what are the implications of the shared responsibility paradigm and identity and…
A: GIVEN: What does identity and access management (IAM) and the shared responsibility model imply for…
Q: create a program that calculate area of a circle: add this buttons: calculate button, reset button,…
A: The program is written in Java. Check the program screenshot for the correct indentation. Please…
Q: How would you define the fundamental parts of an HTML website?
A: Intro Doctype, Comments, Elements or Tags, Attributes, and Frames that contain other HTML pages may…
Q: What is the postfix form of the phrase that looks like this: (A+ B)*(C*D- E)*F / G a) AB+ CD*E – FG…
A: The Answer is in Below Steps
Q: What operating system should I use for greater security and efficiency? Please provide at least one…
A: Introduction It's no secret that the operating system you're using has a big influence on your…
Q: Software development utilizes a large variety of models, each with varying importance depending on…
A: Answer: A software process model is a reflection of the software improvement process. The models…
Q: FDM is an analog multiplexing technique that combines ____ signals. a discrete b analog…
A: FDM is a analog multiplex that combines .
Q: Describe the steps involved in the program's analysis phase.
A: Introduction: The Analysis Phase is when the project's lifespan begins. The Analysis Phase is when…
Q: Give some instances of how two-tier and three-tier application architectures differ and how they are…
A: Introduction: The end-user and the organisation both stand to gain from the use of a web…
Q: Is it feasible to capture data flows in a number of different ways?
A: To talk about how to record data flow: Data Flow is divided into two categories. The physical…
Q: Is the development of network apps significantly different from the development of other kinds of…
A: Introduction: A set of instructions, programs, data, or used to control computers and perform…
Q: What are the advantages of merging several logical divisions and subsystems on a single piece of…
A: Given: We have to discuss What are the advantages of merging several logical divisions and…
Q: When someone claims that data granularity has been specified, what precisely does it mean?
A: Granularity of the data: What exactly does "Data Granularity" mean? A data structure's amount of…
Q: Which of the below access lists blocks a single PC from
A: to access list bloks of single PC from accessing DNS service on a server that has an IP 10.10.10.10…
Q: Explain connection (GND/PIN 13/3.13 v) For this code (Light Sensor arduino): const int ledPin =…
A: Connections for LDR sensor: Place the LDR on the breadboard and attach the 10k ohm resistor to one…
Q: What are the key advantages of using a virtual private network (VPN) as opposed to other options for…
A: Introduction: VPNs enable users to mask their network information and access the web securely…
Q: Non-systems analysis methodologies should be explained in well-organized language. The use of…
A: Introduction: It's important looking into how structured language can be used to explain processes…
Q: jective of the notes page view in
A: Notes Page view is one of ten views available in PowerPoint 2019 for Windows. This view shows you…
Q: What are the motivations behind the broad variety of partitioning techniques used by the many…
A: Given: Memory partitioning is a method of dividing the memory of a computer into portions that are…
Q: What are the primary distinctions between a two-tier and three-tier application architecture? Which…
A: Intro Three tire database architecture runs faster than two tier database architecture and three…
Q: Which of these is true for Single Layer Perceptrons? O Have exactly one hidden layer O Cannot be…
A: SLPs are the most basic artificial neural networks.
Q: Is it possible for a data breach to have a substantial impact on the security of cloud storage? Is…
A: Data breach:- This means the leaking of confidential information, or the theft of intellectual…
Q: Determine the most crucial components of an information technology system. To have a…
A: Introduction: The fundamental elements of an information system
Q: Is there an organization, management, and technology element of an information system?
A: Introduction: Information system An information system is a cohesive set of components that gather,…
Step by step
Solved in 2 steps with 2 images

- Assume the following list of keys: 16, 38, 54, 80, 22, 65, 55, 48, 64, 95, 5,100, 58, 25, 36 This list is to be sorted using quicksort as discussed in this chapter. Use pivot as the middle element of the list. a.) Give the resulting list after one call to the partition b.) Give the resulting list after two calls to the partitionStarter Code: def find_zero(L): pass def bubble(L, left, right): pass def selection(L, left, right): pass def insertion(L, left, right): pass def sort_halfsorted(L, sort): '''Efficiently sorts a list comprising a series of negative items, a single 0, and a series of positive items Input ----- * L:list a half sorted list, e.g. [-2, -1, -3, 0, 4, 3, 7, 9, 14] <---neg---> <----pos-----> * sort: func(L:list, left:int, right:int) a function that sorts the sublist L[left:right] in-place note that we use python convention here: L[left:right] includes left but not right Output ------ * None this algorithm sorts `L` in-place, so it does not need a return statement Examples -------- >>> L = [-1, -2, -3, 0, 3, 2, 1] >>> sort_halfsorted(L, bubble) >>> print(L) [-3, -2, -1, 0, 1, 2, 3] ''' idx_zero = find_zero(L) # find the 0 index sort(L, 0, idx_zero) # sort left half sort(L, idx_zero+1, len(L)) # sort right halfHow is an array stored in main memory? How is a linked list stored in main memory? What are their comparative advantages and disadvantages? Give examples of data that would be best stored as an array and as a linked list.
- Quicksort's partition function might be modified as follows: Count the amount of values that are strictly fewer than the leftmost value to determine where the leftmost value should go. The final figure is the precise index for the required value. The value at the indexed position should be swapped out with the value on the left. Does this provide an accurate quicksort with the remaining code in place? If not, please explain.2. Searches for any number within the sorted list using Binary search. Searches for any number that is not exist in the sorted list. Use exception handling to print out the corresponding error messageUsing the following instruction below, write a header class for unorderedLinkedList with a function of search, insertFirst, insertLast and deleteNode. Use the library to write a program to show an operation on an unordered linked list. write in C++ program. - Include the unorderedLinkedList.h library in the codes - Initialize a list1 and list2 as unorderedLinkedList type - Declare a variable num as integer data type - Print out an instruction for user to input a numbers ending with -99 - Get a numbers from user input - Use a while loop to insert the numbers into list1 ending with -99 - Print out the current elements in List 1 - Assign list 2 to list 1 - Print out the elements in list 2 - Print the length of list 2 - Get user input for the number to be deleted - Delete the number requested by user in list2 - Print out the elements in the list after delete operation - Print the length of list 2 - Declare the intIt variable to be linked list iterator - Print out the elements in List 1…
- 8.26 LAB: Word frequencies (dictionaries) Implement the build_dictionary() function to build a word frequency dictionary from a list of words. Ex: If the words list is: ["hey", "hi", "Mark", "hi", "mark"] the dictionary returned from calling build_dictionary(words) is: {'hey': 1, 'hi': 2, 'Mark': 1, 'mark': 1} Ex: If the words list is: ["zyBooks", "now", "zyBooks", "later", "zyBooks", "forever"] the dictionary returned from calling build_dictionary(words) is: {'zyBooks': 3, 'now': 1, 'later': 1, 'forever': 1} The main code builds the word list from an input string, calls build_dictionary() to build the dictionary, and displays the dictionary sorted by key value. Ex: If the input is: hey hi Mark hi mark the output is: Mark: 1 hey: 1 hi: 2 mark: 1 Use Python, please.PP 12.7 Using stacks, create a postfix-to-infix converter. Until the user exits, the application should read a postfix expression and print the identical infix expression. If the postfix expression entered is illegal, throw an exception. PP 12.8 Create a ReverseWords class that uses a stack to produce a set of components entered by the user in reverse order.True or False For each statement below, indicate whether you think it is True or False. provide a description of your answer for partial credit in case you are incorrect. 1) Given a stack implemented as an array, and the following functions performed: Push(A), Push (B), Push(C), Pop(), Push(D), Push(E), Pop(), Push(F) a. The array will be [A][B][D][F] and the “top” of the stack will be at index 3 where [F] is b. The next element that will be removed when Pop is called will be A c. If we Push(G), [G] will be inserted at index 0
- 1. In a loop, fill an array for up to 50 even numbers and a set for up to 50 odd numbers. Use the merge() algorithm to merge these containers into a vector. Display the vector contents to show that all went well. (In C++ language) 2. Write a program that copies a source file of integers to a destination file, using stream iterators. The user should supply both source and destination filenames to the program. You can use a while loop approach and a list container with integer data type. Within the loop, read each integer value from the input iterator and add the value to the list container by using push_back() function, then increment the input iterator.Finally, use an output iterator to write the list to the destination file. (In C++ language)11.13 (Python please) Locate the largest element) Write the following function that returns the location of the largest element in a two-dimensional list: def locateLargest(a): The return value is a one-dimensional list that contains two elements. These two elements indicate the row and column indexes of the largest element in the two-dimensional list. Write a test program that prompts the user to enter a two- dimensional list and displays the location of the largest element in the list. Here is a sample run: Enter the number of rows in the list: 3 (press enter) Enter a row: 23.5 35 2 10 (press enter) Enter a row: 4.5 3 45 3.5 (press enter) Enter a row: 35 44 5.5 11.6 (press enter) The location of the largest element is at (1, 2) (press enter)Assume the following list of 16 keys:18, 40, 16, 82, 64, 67, 57, 50, 37, 47, 72, 14, 17, 27, 35, 20 This list is to be sorted using Merge Sort, the number of recursive levels required to finish dividing steps this list is: 4 8 16 3



