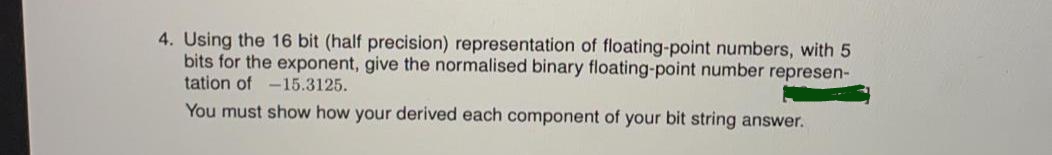
4. Using the 16 bit (half precision) representation of floating-point numbers, with 5 bits for the exponent, give the normalised binary floating-point number represen- tation of -15.3125. You must show how your derived each component of your bit string answer.
Q: Create a function that returns true if there's at least one prime number in the given range (n1 to…
A: 1. Create the method with 2 argument 2. created the isprime constant 3. created the arrow function…
Q: 4. Consider this set of processes. Create the Gantt chart and compute the response time (RT), wait…
A: Here is the calculation of response time, wait time and turnaround time.
Q: When is it suitable to store data using conventional files?
A: The term "conventional file organization" refers to the practice of storing information in paper…
Q: Why and how do numerous Linux commands behave in the same way on Macs and Linux systems,…
A: Linux is the most popular open-source operating system, and it is also one of the most well-known.…
Q: Describe the usage of databases in an organization's information systems. Give the example of any…
A: A data set is data that is set up for simple access, the executives and refreshing. PC data sets…
Q: how to define turing machine in best possible and simple way?
A: A machine that accepts a recursive enumerable grammar, that is, type-0 grammar, is called as a…
Q: What does "design workstation" mean? Use examples and figures to illustrate the subject.
A: Answer: A Work Station is a high performance computer system that is primarily intended for a single…
Q: JAVA Script | A Happy Year is the year with only distinct digits. Create a function that takes an…
A: Algorithm - Take one integer as input. Now use the below logic if(count==1) return false;…
Q: Create a function that takes two "sorted" arrays of numbers and returns an array of numbers which…
A: In this problem we need to design the Java script program. Input - that takes two "sorted" arrays…
Q: Where does Windows store deleted files when you use File Explorer or Windows Explorer to remove them…
A: The question is Where does Windows store deleted files when you use File Explorer or Windows…
Q: What is a virtual machine (VM) defined as? Is there a reason I would want to use a virtual machine?…
A: A Virtual Machine, also shortened as VM, is the same as any other physical computer, such as a…
Q: Wireless networks experience a wide range of issues as a result of their inherent characteristics.…
A: In a business setting, Wi-Fi is an essential component of your IT infrastructure. Improper planning…
Q: Create a function that takes an integer n and returns multiplication table of 1 to n numbers up to n…
A: function multTable(n) { var arr = [] for (let i = 1; i <= n; i++) { var hold = [] for (let j = 1;…
Q: Explain in detail the various strategies that may be used to prevent OS invaders.
A: The various strategies that may be used to prevent OS invaders are
Q: t exactly are virtual computers, what can you do with them, and what advantages can they of
A: Introduction: Virtual objects are those that are imagined, exist conceptually but not physically, or…
Q: What is open source in computer science?
A: please check the solution below
Q: What are the many entry points that might be exploited by malicious software to get access to a…
A: Introduction: Malware Analysis: Malware analysis is the process of understanding the behavior and…
Q: 15C. Find the signed integer representation of negative twenty-nine (-29) in a byte sized register.
A:
Q: Assume the following C code is stored in a file named main.c. Please split it into two files where…
A:
Q: How do stored procedures and scripts vary from one another? Why are stored procedures advantageous?
A: A prepared SQL statement saved on the database server as a Stored Procedure can be utilized several…
Q: hat Do You Mean by Net
A: Introduction: Two or more computers connected together to share resources (such printers and CDs),…
Q: List the justifications for why a company could want firewalls for physical security measures.
A: Firewall - A firewall is a network device that offers network security based on security policies.…
Q: What are the benefits of using a layered architectural approach?
A: Layered architecture is the processing of data that occurs at several levels. Basically, multitiered…
Q: Trace each pass of selection, insertion, bubble and quick sort for the list of values below. For…
A: The answer is written in step 2
Q: What is the method that DMA uses to increase the concurrency of the system? In what ways does it…
A: DMA represents the DIRECT MEMORY ACCESS. Means there is a direct way to access the memory not by the…
Q: Declare a string of 20 unsigned bytes named bArray and initialize all the elements to zero
A: INTRODUCTION: A source operand, a destination operand, or both are possible requirements for each…
Q: What three factors are taken into account while choosing hardware?
A: The question has been answered in step2
Q: What possible use may a motherboard power connection in the SATA type serve?
A: SATA Serial ATA (Serial Advanced Technology Attachment or SATA) is an order and transport…
Q: To further increase the statistical knowledge of your fight, count the number of times a certain…
A: function countNumberofOccurrences(nums) { //function declaration let a = Object.values(nums)…
Q: Take into account a job in selling computer gear. Do you believe that the strongest sales…
A: Computer hardware is, in the simplest terms, the physical parts required by a computer system. It…
Q: What does it mean to be "busy waiting"? What other sorts of waiting are there in an operating…
A: A "busy waiting" process does multiple checks to see if a condition has been met. However, even…
Q: Report key similarities and differences between HTML and XML with the use of examples to distinguish…
A: NOTE: AS PER THE BARTLEBY GUIDELINE IF THERE ARE MULTIPLE QUESTION THEN WE ARE ALLOWED TO ANSWER ONE…
Q: Explain the differences between the two primary types of defences against buffer overflow attacks.
A: BUFFER OVERFLOW ATTACK - It is a temporary area for data storage. If more data gets placed by a…
Q: Who among these organisations is participating in the various stages of the developm
A: Systems Development Life Cycle System development life cycle (SDLC) is an Information system…
Q: What various kinds of data structures exist?
A: A data structure is a collection of "values" of the data type that are stored and organized to…
Q: The Common TCP/IP Ports are an example. To correctly design security, businesses must comprehend the…
A: Answer- TCP/IP stands for Transfer Control Protocol/ Information Protocol. During a data transfer,…
Q: IN JS Someone has attempted to censor my strings by replacing every vowel with a *, 1*k* th*s.…
A: In this problem we have a censored string and a censored vowel string. Need to provide a solution in…
Q: Explain what is meant by the term "caching" when referring to shared memory.
A: term "caching" when referring to shared memory is given below
Q: What are the many programmes I may use to backup Windows 10? Also, please explain the main…
A: answer is
Q: 3 A computer consists of a processor and an I/O device D connected to main memory M via a shared bus…
A:
Q: What advantages might a RAID Level 2 system provide to a university payroll system? What, if any,…
A: The answer of the question is given below
Q: How about demonstrating and outlining the actual use of virtual servers and services?
A: A virtual server should ideally mirror dedicated server features. Numerous digital servers may be…
Q: Assume that after installing a motherboard, someone forgets to connect the wires from the casing to…
A: Numerous wires protrude from the front panel of the computer casing and link to the motherboard's…
Q: describe
A:
Q: JAVA Problem Create a function that determines whether elements in an array can be re-arranged to…
A: The complete JAVA code is given below with OUTPUT screenshot Happy Coding ?
Q: Write c# code to reverse order of words in string Input : this is me Output : me is this…
A: As given, we need to write a C# code to reverse words in a string. I have provided the complete code…
Q: a. If the last operation performed on a computer with an 8-bit word was an addition in which the two…
A: please check the solution below
Q: Give an explanation of how buffer overflow attacks are carried out and what the results of such an…
A: Buffer overflow : takes place when an application or manner tries to write greater records to a…
Q: s the benefits and drawbacks of utilising HRIS.
A: What Is HRIS? HRIS stands for a human resource information system that is software used for various…
Q: Create a comparison table comparing HTTP and WebSocket differences.
A: HTTP and WebSocket are communication protocols that can be utilized in client-server communications.
Step by step
Solved in 2 steps with 2 images

- A(n) __________ is an integer stored in double the normal number of bit positions.Represent the following numbers to its 6-bit binary representation and perform binary subtractionusing 2’s compliment representation 50-30?1) Using IEEE 754 representation for single precision floating point, give the 32-bit binary encoding for the numbers below.Show the sign, exponent, and mantissa (significand).a. -2.40625b. 11.2265625 2) Given the following binary number: 1101.0111, what will be its decimal numberequivalent?
- 1)Using IEEE 754 representation for single precision floating point, give the 32-bit binary encoding for the numbers below.Show the sign, exponent, and mantissa (significand).a. -2.40625b. 11.2265625 2) Given the following binary number: 1101.0111, what will be its decimal numberequivalent?With step by step solution please Using IEEE 754 representation for single precision floating point, give the 32-bit binary encoding for the numbers below. Show the sign, exponent, and mantissa (significand). a. 11.2265625Given a 10-bit floating-point number with a 4-bit exponent field which follows IEEE floating point rules except for the above sizes: What is the hexadecimal representation of the bit-pattern representing minus infinity? Give the hexadecimal representation of the bit-pattern and the decimal value of the smallest positive number. Give the hexadecimal representation of the bit-pattern and the decimal value of the smallest positive normalized number. Give the hexadecimal representation of the bit-pattern and the decimal value for the most negative number which is not minus infinity. Give the smallest and largest ULP values possible in this representation. You should use a calculator to solve this problem.
- Perform the following operation for the binary equivalent of the decimal numbers (-14) 10+ (-15) 10 The solution in 8 bit representation ?If an unsigned 8-bit integer were to be extended to a 16-bit one, the first 8 most significant bits (MSB) would be filled with ones, creating a signed 16-bit representation. Pick a solution from these two options: Is it true or false that...?Determinethe Decimal Value (Base 10) of the following IEEE-754 32-bit floating-point representation. Show your working. (Hint: identify the sign bit, the biased exponent and the trailing significand /mantissa). 0 01111111 110 0000 0000 0000 0000 0000
- 1)Using IEEE 754 representation for single precision floating point, give the 32-bit binary encoding for the numbers below.Show the sign, exponent, and mantissa (significand).a. -2.40625b. 11.2265625please answer with proper explanation and step by step solution. Question What decimal number does the bit pattern 0xC2280000 represent if it is: A two's complement integer? An unsigned integer? A floating point number assuming the IEE 754 single precision format6. Using IEEE 754 representation for single precision floating point, give the 32-bit binary encoding for the numbers below. Show the sign, exponent, and mantissa (significand).b. 11.2265625

