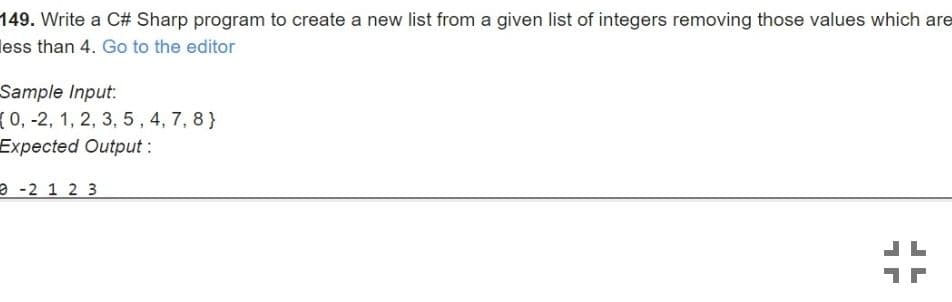
Write a C# Sharp program to create a new list from a given list of integers removing han 4. Go to the editor
Q: The turning points in the historical development of computers are based on the echnology incorporate...
A: In the above question, we need to check whether the statement is true or false. The origins of compu...
Q: Which fibre is utilised to protect the inner core and prevent the cable from straining in fiber-opti...
A: Introduction: Fiber optic cable is a form of network cable that is commonly used to carry data. It i...
Q: What was the overall effect of the Capital One security breach? Is there any way this could have ...
A: Intro What was the overall effect of the Capital One security breach? Is there any way this could ...
Q: Consider a two-link network where Host A is connected to the router by a 1 Mbps link with 10 ms prop...
A: What is the transmission delay (in ms) of the packet from therouter to Host B?
Q: Discuss the internet's evolution and the underlying technological foundations.
A: Intro According to the question, The Internet began in the 1960s as a way for government researchers...
Q: When do you use description? When do you use definition?
A: Intro When do you use description? When do you use definition?
Q: How would you characterize the global rise of Internet use?
A: Here is the explanation:
Q: 1. Write a program to find the largest of 3 numbers.
A: the answer is given below:-
Q: Explain why it is important that software products are developed and delivered quickly ?
A: When a customer submits his or her requirements to the firm, both the company and the client agree o...
Q: What is the purpose of a test management review, and why is it necessary?
A: Introduction: The action of managing a testing process is frequently referred to as test management....
Q: Explain how the Transport layer in the OSI model ensures error-free data transport.
A: Introduction: Layer 4 of the OSI Model: Transport Layer enables transparent data transmission betwee...
Q: What are the recommended procedures for assuring a local area network's resilience and availability?
A: Introduction: LAN: It is a collection of small computers or other workstation devices connected by a...
Q: 1. What is Failover-Clustering and why do you think it is so widely used?
A: Introduction: What is Failover-Clustering and why do you think it is so widely used?
Q: Website Compatibility: Gigantic Life Insurance is planning the implementation of Windows 10 for its ...
A: Answer : Enterprise mode is a company mode that runs on Internet explorer 11 on windows 7 and above....
Q: Employee: (EID, Name, City, Address) Department: (DID, Department_Name, City, budget) Works_IN: (EID...
A:
Q: Show the representation of –22 (assuming 8-bit registers) using a) Signed-magnitude representation. ...
A: The question is to show the representation of -22 to the given formats.
Q: Describe the whole process of developing and deploying a database.
A: Intro: Describe the whole process of developing and deploying a database.
Q: Given a number which is the measurement of a distance in millimeter. Change the representation of th...
A: here in this question we will write program to convert millimeters into centimeters and meters as sh...
Q: A GSM system uses 124 channels and each dhannel is divided into 8 time slots. What is the maimum num...
A: A time slot is assigned to a user where the user can send the data on only that given time slot and ...
Q: What are the issues that can prevent a transaction processing system from scaling up linearly? In ea...
A: This parallel database system aims to boost performance by parallelizing numerous tasks involving da...
Q: Write a lisp function f8 that returns the sum of all integers everywhere in a list. Example: (f8 ‘(2...
A: LISP expressions are composed of forms. The most common LISP form is function application. LISP repr...
Q: Convert the Tic-Tac-Toe game into a class. Overload the < operator to print the boar Write a test pr...
A: #include<iostream> class ScoreList{private://Structure representing a node in the linked lists...
Q: Write a Python program to remove all the occurrences of the number 1 from the list given below and d...
A: Write a Python program to remove all the occurrences of the number 1 from the list given below and d...
Q: To represent 65 unsigned decimal numbers, what is the smallest amount of binary bits required?
A: SUMMARY: -Hence, we discussed all the points.
Q: When it comes to storage, what exactly is a cloud service?
A: Intro When it comes to storage, what exactly is a cloud service?
Q: Why is the completion of one entire pattern referred to as a Cycle?
A: Introduction: A cycle is the completion of a complete pattern.
Q: Q3. How would you get a confidence score (i.e., a score indicating how confident the model is in its...
A: Let's see the solution in the next steps
Q: Consider the following AND/OR graph to describe a simple automobile diagnostic system using IF-THEN ...
A:
Q: Vector Graphics are composed of a number of objects defined by mathematical formulae. True or False
A: Given To know about the vector Graphics.
Q: How to systematically improve a Linux computer's security.
A: Answer- First of all the Linux systems are secure as compared to another operating systems. Now if y...
Q: 32/4 = 8 components (2-bit wide) I need the answer to part two, please If the size of each 4-bit mem...
A: The answer is
Q: Explain how each device in a mesh topology has a specific topology of Multipoint connecting.
A: Introduction: There is no central connecting point in a mesh structure. Instead, each node is linked...
Q: . Write a Python program to remove all the occurrences of the strings other than "Python" from the l...
A: logic:- Use for loop in lst check if word==“Python” then update lst By word. end.
Q: = ax2 + bx + c. • Ask the user for the coefficients a, b and c of a quadratic function f (x) Output ...
A: Hi, as per the given question, we are given a Python problem along with the code and sample output. ...
Q: What exactly is input injection, and what are the various methods for performing it?
A: the answer is given below:-
Q: Alice and Bob use the ElGamal scheme with a common prime q = 131 and a primitive root a = 6. Let Bob...
A: The answer is
Q: How do you ensure that each computer uses its own private key pair while using IPsec?
A: Intro ensure that each computer uses its own private key pair while using IPsec?
Q: ease don't copy Write a lisp function f4 that returns the maximum value of an integer list. Example:...
A: Given Please don't copy Write a lisp function f4 that returns the maximum value of an integer li...
Q: What is the significance of information security management?
A: Introduction: Information security management refers to the collection of policies and procedures us...
Q: Explain the many types of interrupts in a microprocessor system.
A: Introduction: Interrupt: It is a signal generated either from hardware or software and has higher p...
Q: Give two reasons why a database could include null values.
A: Answer : 1. If the value is unknown.For example, if you have a form where the zip code is not mandat...
Q: Write a function sumArray with: • Inputs . the first input is an int array called inputArr • the sec...
A:
Q: what is the output in namechnage file and what inouts did u use? do this as if you are usingn a linu...
A: The function will take files as inputs in which we have to replace the sentences or characters or le...
Q: must be able to identify individual hosts (sUch as a computer, printer, router, etc.) and individual...
A: The answer is
Q: Complete the following code for a method that returns true if there is at least one element with a y...
A: public boolean practice(student[] aArray, int yearLevelToSearch){ boolean found=false; for(int x=0;x...
Q: Write a Python program to all the occurences of the strings other than "Java" from the list given be...
A: As per the requirement program is written in python. Algorithm: Step 1: Initialize a str_list with r...
Q: Design the CMOS diagram for the following Table: (A, B & C are the inputs and Y is the output in the...
A: According to the information given:- We have to design CMOS diagram on the basis of the truth table ...
Q: Design a 3-bit comparator and write Verilog code using gate level modeling. Write a Verilog test ben...
A:
Q: What is the output of the unit testing? #include using namespace std; class TempConvert { publ...
A: Ans: the output of the unit testing is: #include <iostream>using namespace std; class TempConv...
Q: Consider the following P = {P1, P2, P3, P4, P5) R = {R1, R2, R3, R4} E = {P3>R1, P2→R2, R4 P4, R2→P1...
A: (a)
Step by step
Solved in 2 steps

- Write a python code deciding and printing the data types of a given list on the screen by using multiple if statements. Assume that the given list is UserList=[[1,3], '*' , 3.14, 1+2j ,2], such that the output is as in the picture below:Write a C++ program that asks the user to enter an integer n followed by n other and store it in a list. Then, asks the user to enter an integer m followed by m other and store it in another list. The program will generate two lists. List one is a copy the first list (List A) after removing all the numbers that are less than or equal to the minimum in second list (List B). List two is a copy the first list (List B) after removing all the numbers that are greater than or equal to the maximum in fist list (List A). Then, display both lists generated. In this exercise, use the STL list. Output is: List A: 10 20 30 40 50 60 70 List B: 10 30 50 70 90 110 130 List 1: 20 30 40 50 60 70 List 2: 10 30 50Create a script in Python. The script should ask the user for two integers, v and t. Using the * and + operators for lists, print a list first containing t copies of the integer v followed by v×t copies of the integer v**2. As an example, Enter an integer v: 3 Enter an integer t: 4 [3, 3, 3, 3, 9, 9, 9, 9, 9, 9, 9, 9, 9, 9, 9, 9] #note there are four 3's followed by 3*4 9's
- C1- a- Write a Python program to input user’s name and how many people are in the dinner party tonight. If the number of people is more than 8, print a message that they have to wait, otherwise print that table is ready. In both situations the message must mention the user name as follows: I’m sorry, Sameh has to wait for a table. OR Sameh’s table is ready b- Remove all instances of “dog” from the list where pets = ['dog', 'cat', 'dog', 'goldfish', 'cat', 'rabbit', 'cat']. Display the list before and after removing.Write a python program that has the following functionality:1. Your program should contain a global list (empty to start)2. prompt the user to enter a number (int or float, validation is not required at this moment)3. add the user input to the list as a float4. continue steps 2 and 3 until the user enters ‘q’ or ‘Q’ 5. ask the user if they would like the ceiling or the floor of all the numbers. The user should enter c for ceiling and f for floor. The input should be validated and if incorrect, the user should be prompted again.6. the program should print each of the ceilings / floors of the number, making use of the ceil() and floor() functions from the math module (you can check this link to know more about ceil and floor functions in python https://docs.python.org/3/library/math.html).7. Be sure to write your own functions to do certain functionality where it makes sense and call those functions in the main() function to execute the entire program.8. Include the guard for the main…Create a new C# project then write a code equivalent to solve the problem given below. Create a program that will generate twenty (20) random numbers from the range 1 to 9. The twenty random numbers shall be stored to a generic list. Print a horizontal histogram, representing the occurrence of each digit. Display also the generated combinations.
- Given a list in Python [1,2,3,4,5,6,7,8,9,10]. Write a Python program to create a new list that contains the even elements of the given list in the same sequence using the filter() function.Write a program in python which will read an integer k from standard input. Use the list function and the range function to print a list of the even integers from -10 up to k (inclusive). Notice the form of the output is a list. NOTE: If k is less than -10, your range command should automatically produce an empty sequence, resulting in an empty list being printed. See the provided examples. For example: Input Result 5 [-10, -8, -6, -4, -2, 0, 2, 4] -11 [] 11 [-10, -8, -6, -4, -2, 0, 2, 4, 6, 8, 10] 2 [-10, -8, -6, -4, -2, 0, 2]Write a program in python which will read two integers, j and k, from standard input. Use the list function and the range function to print a list of integers from k down to j (inclusive). Notice the form of the output is a list. You may assume that j is less than or equal to k. For example: Input Result 2 5 [5, 4, 3, 2] 0 0 [0] -3 3 [3, 2, 1, 0, -1, -2, -3]
- Write a program in python that takes a sequence of non-negative numbers and performsthe computation suggested by the examples in the picture sent. A negative number is used toterminate the input but is not part of the sequence. USING ONLY THESE CODING LANGUAGES: while loop, len(list), List accessor: list[k], Create empty list: list = [ ], List append: list.append(k)Write a C program using Doubly Linked list following instructions [As same as function name]int deleteLastOccurrence(int item); // Delete the last occurrence of the item in the Doubly Linked listint deleteFirstItem(); // delete the first item of the Doubly Linked listint deletelastItem(); // delete the last item of the Doubly Linked listWrite to Anamul H AdarWrite a Python program to create a list by taking input from user and then find thedifference between consecutive numbers in the list. Let’s assume that the list is: [1, 1, 3, 4, 8, 5, 6, 7], then the output list will be as follows:Difference between consecutive numbers of the list: [0, 2, 1, 4, -3, 1, 1]

