5. Given the following "Super Simple CPU" program: LDI 6 SUB ONE ADD TWO DONE STO ONE STP DAT 1 DAT 2 ONE TWO b. ; Load 6 into accumulator ; Subtract the value in memory location ONE from accumulator ; Add the value in memory location TWO to accumulator ; Store accumulator in memory location ONE ; Stop the program ; A data value, the constant 1 ; A data value, the constant 2 Trace the code, write the values of Accumulator, Memory (ONE), and Memory (TWO) in a table (sample table is shown below), and record their changes after each instruction. Assembly instruction Accumulator ONE TWO LDI 6 6 1 2 Write a pseudocode that performs the same program.
5. Given the following "Super Simple CPU" program: LDI 6 SUB ONE ADD TWO DONE STO ONE STP DAT 1 DAT 2 ONE TWO b. ; Load 6 into accumulator ; Subtract the value in memory location ONE from accumulator ; Add the value in memory location TWO to accumulator ; Store accumulator in memory location ONE ; Stop the program ; A data value, the constant 1 ; A data value, the constant 2 Trace the code, write the values of Accumulator, Memory (ONE), and Memory (TWO) in a table (sample table is shown below), and record their changes after each instruction. Assembly instruction Accumulator ONE TWO LDI 6 6 1 2 Write a pseudocode that performs the same program.
C++ Programming: From Problem Analysis to Program Design
8th Edition
ISBN:9781337102087
Author:D. S. Malik
Publisher:D. S. Malik
Chapter7: User-defined Simple Data Types, Namespaces, And The String Type
Section: Chapter Questions
Problem 16SA
Related questions
Topic Video
Question
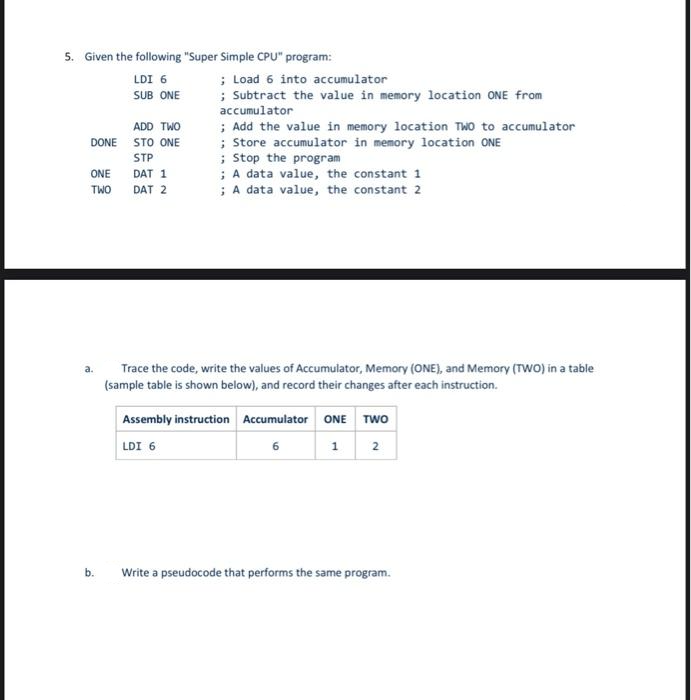
Transcribed Image Text:5. Given the following "Super Simple CPU" program:
ADD TWO
DONE STO ONE
STP
ONE
TWO
a.
LDI 6
SUB ONE
b.
DAT 1
DAT 2
; Load 6 into accumulator
; Subtract the value in memory location ONE from
accumulator
; Add the value in memory location TWO to accumulator
; Store accumulator in memory location ONE
; Stop the program
; A data value, the constant 1
; A data value, the constant 2
Trace the code, write the values of Accumulator, Memory (ONE), and Memory (TWO) in a table
(sample table is shown below), and record their changes after each instruction.
Assembly instruction Accumulator ONE TWO
LDI 6
1 2
6
Write a pseudocode that performs the same program.
Expert Solution
This question has been solved!
Explore an expertly crafted, step-by-step solution for a thorough understanding of key concepts.
Step by step
Solved in 3 steps with 1 images

Knowledge Booster
Learn more about
Need a deep-dive on the concept behind this application? Look no further. Learn more about this topic, computer-science and related others by exploring similar questions and additional content below.Recommended textbooks for you

C++ Programming: From Problem Analysis to Program…
Computer Science
ISBN:
9781337102087
Author:
D. S. Malik
Publisher:
Cengage Learning

C++ Programming: From Problem Analysis to Program…
Computer Science
ISBN:
9781337102087
Author:
D. S. Malik
Publisher:
Cengage Learning