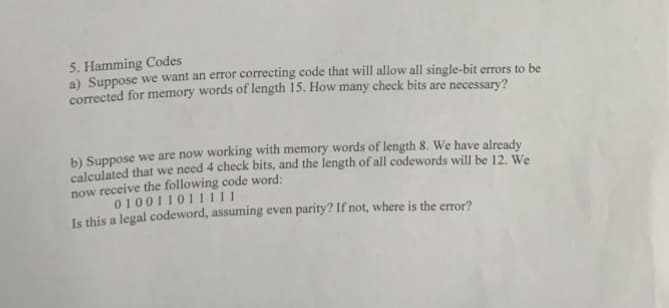
5. Hamming Codes a) Suppose we want an error correcting code that will allow all single-bit errors to be corrected for memory words of length 15. How many check bits are necessary? b) Suppose we are now working with memory words of length 8. We have already calculated that we need 4 check bits, and the length of all codewords will be 12. We now receive the following code word: 010011011111 Is this a legal codeword, assuming even parity? If not, where is the error?
Q: for incorrect. Do ri
A: From question Using banker's algorithm to define the states safe or note:
Q: Write a C# program to initialize three 2D integer array. The array size (row & column) should be…
A: C# Program: using System;class MatrixMultiplication{ static void Main() { int i=0, j=0;…
Q: This is the situation as a direct consequence of computers' recent advances in capabilities. How can…
A: Although the power of computers has been with us since birth, they are now ubiquitous. From school…
Q: Given x = [3 15 9 12 -1 0 -12 9 6 1], provide the command(s) that will a. Set the values of x that…
A: Matlab:- 1. Compiled programs can be executed by any number of users on their own computers without…
Q: What precisely do you mean when you state authentication's objectives? Contrast and compare the…
A: INTRODUCTION: Confirmation is the method of deciding whether somebody or something is, in reality,…
Q: What are the goals of employing a variety of visual aids? Describe how you would use three unique…
A: Visual aids are often utilized during presentations to ensure that the audience understands the…
Q: Give five recommendations to help stop ransomware attacks.
A: Five recommendations to help stop ransomware attacks. If you have been unfortunate enough to be the…
Q: Use two real-world examples to illustrate the major distinctions between synchronous and isochronous…
A: An asynchronous connection: Data is conveyed from one end to the other through communication. When…
Q: In the majority of retail locations, barcode scanners are already standard equipment. Include one…
A: Introduction: Optical scanners include barcode readers and barcode scanners. These…
Q: List the many preventive steps that may be taken to thwart phishing and spoofing techniques, and…
A: Given: Phishing schemes may be conducted through phone calls, emails, and other media.In order to…
Q: Explain operation of polyalphabetic cipher.
A: Let's see the answer:
Q: Every aspect of our culture has been influenced by computers, including the workings of our economy,…
A: The development of computers has had a significant influence on human existence, and artificial…
Q: The idea of two-factor authentication seems unclear to me. Does it make a difference in the…
A: Multi-factor authentication - (MFA), commonly referred to as two-factor or dual authentication,…
Q: Unlike datagram and virtual-circuit networks, circuit-switched networks do not need a routing or…
A: In this question we need to explain if in case of datagram or virtual switching networks switching…
Q: Selection structures are frequently used in programming, however they are not perfect. For a variety…
A: Introduction: The terms "frontend" and "backend" are the most frequently used in web development.…
Q: What do you think are some possible solutions to the issues that these people confront, and what…
A: The answer is given in the below steps Happy to help you ?
Q: List the many preventive steps that may be taken to thwart phishing and spoofing techniques, and…
A: Given: Phishing schemes can be conducted via phone calls, emails, and other media. In order to get…
Q: Suppose we apply the Mix Columns operation to a *column* vector [0x19, 0x85, 0x91, 0x02] (given with…
A: Introduction The process of changing one number in a number system to another is known as…
Q: What is a horse of Troy? Three instances.
A: How does a Trojan horse operate, and what precisely is it? Describe three situations in detail. The…
Q: An understanding of the present convergence of digital gadgets and how those technologies relate to…
A: Introduction Digital gadgets: Digital devices, sometimes known as gadgets, are innovative…
Q: Examine wearable computing, such as the Apple Watch and Android Wear, and remark on the influence…
A: Introduction: Wearable devices (iPod, Muse, Fitbits, GoPro, smart glasses, smart watches) are being…
Q: Give a description and an explanation of the CRUD procedure. What is it specifically, and how does…
A: Given: The CRUD approach and its connection to use cases need to be highlighted.We must also…
Q: I. Simplify the following expressions and draw the corresponding logic circuit. 1. 2. 3. 4. x'y'z +…
A: Logic circuits are given below:
Q: On the other hand, it has been suggested that a processor be used that can decode encrypted data and…
A: Given: The central processing unit (CPU) follows the instruction cycle, sometimes referred to as the…
Q: In many ways, laptop computers and mobile devices seem to be very unlike. Your argument should be…
A: Introduction: The most obvious distinction between a mobile phone and a personal computer is their…
Q: Using examples, explain the following components of the security triad for a college database that…
A: Confidentiality, integrity and availability, also referred to as the CIA triad, is a model designed…
Q: Find the Minimum Hamming distance d for the following codes: {01010,10101,11111,00000,00010}
A: Hello student
Q: What is a Trojan horse, and how does it operate? Provide three concrete instances.
A: These question answer is as follows
Q: How important is it to have spreadsheet software skills?
A: To understand the significance of spreadsheet application abilities. Spreadsheets are often used in…
Q: Compare the advantages and disadvantages of solid-state secondary storage devices to magnetic…
A: Intro Solid-state secondary storage devices: SSDs offer quicker startup times, perform speedy file…
Q: What would be the ultimate modifier in this case?
A: When you apply the final modifier, you indicate that something is fixed and cannot be changed. No…
Q: Do you agree that "there is no concept of client and server sides of a communication session" in a…
A: The answer of the question is given below
Q: What actions may be made to improve the security of cloud storage after a data breach? What are some…
A: The cloud is full of benefits, but they're also some risks and dangers. If your business depends on…
Q: Please do the exercise! Thank youuu
A: Truth Table : A truth table deconstructs a logic function by outlining all possible outcomes the…
Q: Programs created for zero, one, or two address architectures are thus more likely to be…
A: Longer instruction (more number of instrcutions). Let's examine the relationship between the…
Q: What are mobile apps exactly, and why are they so crucial?
A: Introduction: Mobile app: An application for mobile devices is a kind of software. The program was…
Q: Choose the answer option that corresponds most closely to the question. This category includes…
A: The correct response to this query is FALSE. The following are examples of utility applications:…
Q: What are the goals of employing a variety of visual aids? Describe how you would use three unique…
A: Introduction: In this context, "visual aids" refers to anything a viewer can see, such as graphs,…
Q: Understanding the factors that lead to video data requiring and using more storage space than other…
A: Why does video data need and consume more storage than other types of data? A video is a compilation…
Q: Do you agree that "there is no concept of client and server sides of a communication session" in a…
A: P2P (or peer-to-peer) is a file-sharing technique that is used in the field of computer networking.…
Q: 28. In a linear linked list, a. the next pointer of each node has the value NULL b. the last node…
A: In this question i will define , what is linkedlist.
Q: 2.13 How is a Hill cipher vulnerable to chose plaintext attack?
A: Hill Cipher which refers to the multilettered polyalphabetic cipher invented by Lester S. Hill…
Q: Do you agree that "there is no concept of client and server sides of a communication session" in a…
A: The answer of the question is given below
Q: What is the definition and implication of a poison package attack? Please provide two instances of…
A: Poison package attack: ARP Poisoning likewise alluded to as ARP Spoofing, is a sort of Web attack on…
Q: How do we Configure both Cisco Router (Standby and Active) and Cisco Switches to defend against HSRP…
A: The Hot Standby Router Protocol (HSRP) is a First Hop Redundancy Protocol (FHRP)(FHRP) designed to…
Q: Since our birth in this century, dubbed as the Information Age, everything from computers to tablets…
A: Technology has radically changed our planet and the way of life over time. Additionally,…
Q: Examine how solid-state and magnetic secondary storage systems vary from one another and from one…
A: Magnetic hard drives and solid-state drives have a few different features that make them optimal for…
Q: Use two real-world examples to illustrate the major distinctions between synchronous and isochronous…
A: Asynchronous connection: Data is sent from one end to another in communication. Asynchronous…
Q: What precisely is a Trojan horse and how does it work? Please provide three examples to support your…
A: Given: A harmful virus or piece of software that masquerades as legitimate but has the power to take…
Q: Since our birth in this century, dubbed as the Information Age, everything from computers to tablets…
A: The answer is given below.
Trending now
This is a popular solution!
Step by step
Solved in 3 steps

- c++ part2 and the rest plz 1- Given a set of numbers where all elements occur even number of timesexcept one number, find the odd occurring number” This problem can beefficiently solved by just doing XOR of all numbers.2- Use bitwise operators to compute division and multiplication by a numberthat is power of 2. For example: bitwise_divide/multiply(num,8/16/32/2/4/128) should use only bitwise operators to compute result.3- Write code that checks if a number is odd or even using bitwise operators.4- Write a program that checks if a number is positive/negative/zero.5- Write a function that returns toggle case of a string using the bitwiseoperators in place. this is the answer of the first exercice: #include <bits/stdc++.h> // include header file for standard header filesusing namespace std; int funintar[],intsizeintar[],intsizeintar[],intsize // start definition of function to check the odd occurences of the numbers{ int res = 0;…Computer Science it has to be done in c programming // Task 3 // For this function, you must return the largest power of 2 that// is less than or equal to x (which will be positive). You may// not use multiplication or some sort of power function to do this,// and should instead rely on bitwise operations and the underlying// binary representation of x. If x is 0, then you should return 0.unsigned largest_po2_le(unsigned x) {return x;}You are writing code that is equivalent to: X = A / (5 + B) Assume signed bytes and the following first 3 lines of code: mov al,A mov bl,B add bl,5 What is the one line of code that will perform the division correctly?
- c++ i want part 2 and the rest 1- Given a set of numbers where all elements occur even number of timesexcept one number, find the odd occurring number” This problem can beefficiently solved by just doing XOR of all numbers.2- Use bitwise operators to compute division and multiplication by a numberthat is power of 2. For example: bitwise_divide/multiply(num,8/16/32/2/4/128) should use only bitwise operators to compute result.3- Write code that checks if a number is odd or even using bitwise operators.4- Write a program that checks if a number is positive/negative/zero.5- Write a function that returns toggle case of a string using the bitwiseoperators in place. part1 #include <bits/stdc++.h> // include header file for standard header filesusing namespace std; int fun(int ar[], int size) // start definition of function to check the odd occurences of the numbers{ int res = 0; // declare the required numbers for (int i = 0;…1. Write a C++ program that takes two binary numbers of 8 bits eachrepresented with the letters Z and O (for zero or one) and displays thesum in binary with Zs and Os. Do this by converting the numbers to ints,adding the its using +, displaying the 3 ints, then converting the sum toZ and Os and displaying the result. 1 a.) Redo number 1, by doing a bit-by-bit addition, not forgetting the carry. 1b.) Write a program to take two numbers represented with romannumerals and display the sum. Assume the sum will be less than 20.Hints: Ask the user to terminate each number with a semicolon and usechars to hold the roman ‘digits’.The numbers are I, II, III IV, V, VI, VII, VIII, IX, X, XI, XII, XIII, XIV, XV…isfive, Change the program to allow the sum to go up to 49 See how large a number you can handle. L is 50, C is 100, M is 1000. Using basic C++ int, char, if- else statements, and switch statements, please! no functions, or strings, or Cmath etc.Question Asked Jul 9, 2020 3 views Python Programming- Computer-Assisted Instruction Part 1: Computer-Assisted Instruction (CAI) refers to the use of computers in education. Write a script to help an elementary school student learn multiplication. Create a function that randomly generates and returns a tuple of two positive one-digit integers. Use that function's result in your script to prompt the user with a question, such as: How much is 6 times 7? For a correct answer, display the message "Very good!" and ask another multiplication question. For an incorrect answer, display the message "No. Please try again." and let the student try the same question repeatedly until the student finally gets it right. Then, modify the program so that various comments are displayed for each answer. Possible responses to a correct answer should include 'Very good!' , 'Nice work!' and 'Keep up the good work!' Possible responses to an incorrect answer shojld include 'No. Please try again.' ,…
- Problem 7: Explain the outcome of each of the following code segment?(a)addi $t0, $zero, 0xFF2Bandi $t2, $t2, $t0 (b)ori $t2, $t2, 0x00E9 I NEED ANSWER ASAP. PLEASE DO FASTTask 3 Largest PO2 LE: Implement the largest_po2_le function as directed in the comment above the function. If the directions are unclear, run the code, and look at the expected answer for a few inputs. As specified in the comment, you may not use multiplication or some sort of power function, and should instead rely on bitwise operations. Consider how binary numbers are structured, and how you might find the largest power of 2 of a binary number. Code: #include <stdio.h>#include <stdbool.h>#include <stdlib.h> // BEGIN STRINGBUILDER IMPLEMENTATION // This code is a very rudimentary stringbuilder-like implementation// To create a new stringbuilder, use the following line of code//// stringbuilder sb = new_sb();//// If you want to append a character to the stringbuilder, use the// following line of code. Replace whatever character you want to// append where the 'a' is.//// sb_append_char(sb, 'a');//// Though there are some other functions that might be…need help adding OR, a binary logical calculator with operations AND, OR, NOT. def add(num1,num2):return num1 + num2 def sub(num1,num2):return num1 - num2 def mult(num1,num2):return num1 * num2 def divide(num1,num2):return num1 / num2 print("Select operation.")print("1.Add")print("2.Subtract")print("3.Multiply")print("4.Divide") option = int(input("Choose between 1,2,3,4: ")) a = int(input("First number: ")) b = int(input("Second number: ")) if option == 1:print(a, " + " ,b, " = ", add(a,b))elif option == 2:print(a, " - ",b," = ",sub(a,b)) elif option == 3:print(a, " * ",b," = ",mult(a,b)) elif option == 4:print(a, " / ",b," = ",divide(a,b))else:print("error")
- Consider the following code which includes a parity check for the third digit: C=(000,011,101,110). You get the third digit by adding the first two and then using the remainder on division by 2. Can this code detect and count single errors? how can this be implemented?10. Fill in the following addition table for base 3.+ 0 1 201211. Identify the following statements as TRUE OR FALSE. a) BCD stands for Binary Coded Decimal and encodes each digit of a decimal number to an 8-bit binary form. b) Unicode is a 16-bit code, occupying twice the disk space for text as ASCII or EBCDIC would require. c) A signed-magnitude integer representation includes more negative numbers than it does positive ones. d) A byte is 8 bits, but a word may vary in size (16-bits, 32-bits, etc.) from one architecture to another. e)The largest value that a 60-bit unsigned binary integer can represent is (260-1). f) A 2's complement integer representation includes more negative numbers than it does positive ones.T/F Bit arrays and bit fields are same.

