5. In what way is the difference between the kernel mode and user mode function as a basic principle of operating system protection.
5. In what way is the difference between the kernel mode and user mode function as a basic principle of operating system protection.
Chapter5: Advanced Personalization And Customization
Section: Chapter Questions
Problem 1AYK
Related questions
Question
100%
Transcribed Image Text:IT 313 OPERATING
EMS
Referehces
Mailings
Review
View
Page Layout
Enable Editing
le originated from an Internet location and might be unsafe. Click for more details.
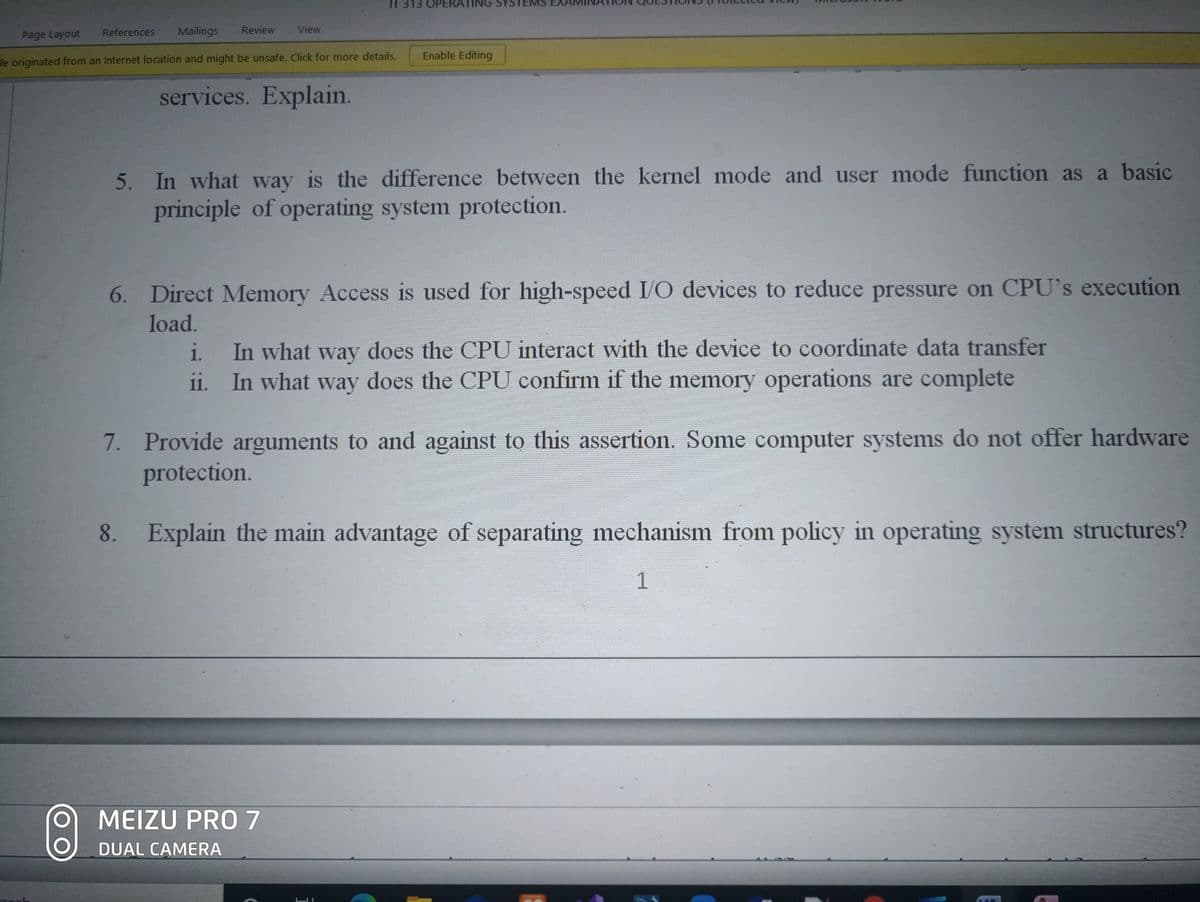
services. Explain.
5. In what way is the difference between the kernel mode and user mode function as a basic
principle of operating system protection.
6. Direct Memory Access is used for high-speed I/O devices to reduce pressure on CPU's execution
load.
In what way does the CPU interact with the device to coordinate data transfer
ii. In what way does the CPU confirm if the memory operations are complete
i.
7. Provide arguments to and against to this assertion. Some computer systems do not offer hardware
protection.
Explain the main advantage of separating mechanism from policy in operating system structures?
1
MEIZU PRO7
DUAL CAMERA
8.
Expert Solution
This question has been solved!
Explore an expertly crafted, step-by-step solution for a thorough understanding of key concepts.
This is a popular solution!
Trending now
This is a popular solution!
Step by step
Solved in 3 steps with 3 images

Knowledge Booster
Learn more about
Need a deep-dive on the concept behind this application? Look no further. Learn more about this topic, computer-science and related others by exploring similar questions and additional content below.Recommended textbooks for you

Microsoft Windows 10 Comprehensive 2019
Computer Science
ISBN:
9780357392607
Author:
FREUND
Publisher:
Cengage

LINUX+ AND LPIC-1 GDE.TO LINUX CERTIF.
Computer Science
ISBN:
9781337569798
Author:
ECKERT
Publisher:
CENGAGE L

A+ Guide To It Technical Support
Computer Science
ISBN:
9780357108291
Author:
ANDREWS, Jean.
Publisher:
Cengage,

Microsoft Windows 10 Comprehensive 2019
Computer Science
ISBN:
9780357392607
Author:
FREUND
Publisher:
Cengage

LINUX+ AND LPIC-1 GDE.TO LINUX CERTIF.
Computer Science
ISBN:
9781337569798
Author:
ECKERT
Publisher:
CENGAGE L

A+ Guide To It Technical Support
Computer Science
ISBN:
9780357108291
Author:
ANDREWS, Jean.
Publisher:
Cengage,

Principles of Information Systems (MindTap Course…
Computer Science
ISBN:
9781305971776
Author:
Ralph Stair, George Reynolds
Publisher:
Cengage Learning