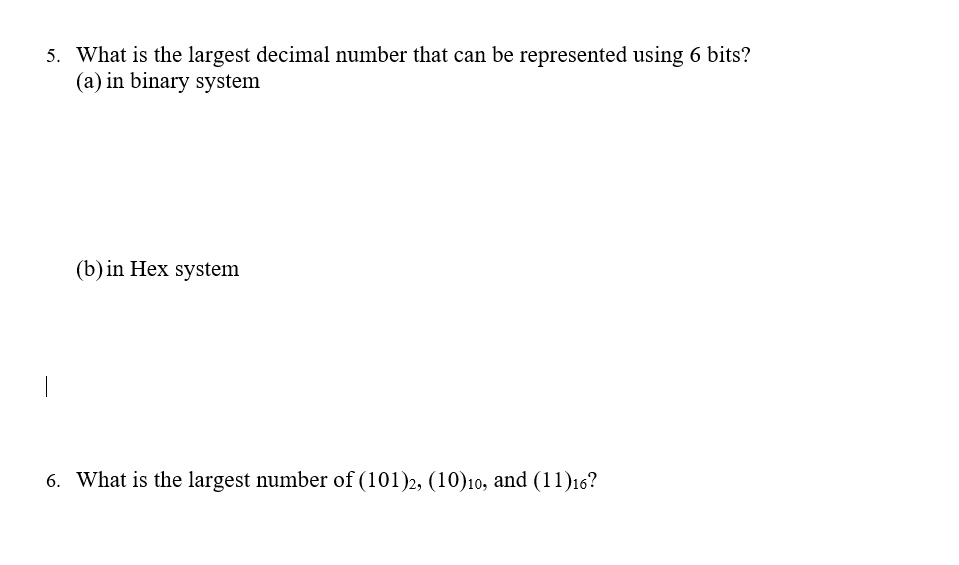
5. What is the largest decimal number that can be represented using 6 bits? (a) in binary system (b) in Hex system 6. What is the largest number of (101)2, (10)10, and (11)16?
Q: Write a Java program to take a list of string from the user & print a list where each string has all…
A: Code: import java.util.*;public class StringReplace { public static void main(String args[]) {…
Q: Use this tutorial to determine the kind of motherboard you have.
A: Introduction: Motherboards are the primary circuit boards that are found within computers, according…
Q: What exactly is pipelining?
A: Answer
Q: Do you know how today's computers were created?
A: Introduction: Different types of hardware and software have been produced in computer science in…
Q: What precipitated the Information Revolution
A: Introduction: The information revolution, which began in the twentieth century, was fueled largely…
Q: The abacus was first used in what year and in what manner?
A: INTRODUCTION: Known as the "World's First Computing System," the abacus was used by people to…
Q: a) Explain what the program below performs line by line: import numpy as np import matplotlib.pyplot…
A: see the expiation of code line by line
Q: Computer A cannot ping Computer B. Wwhich reason for the problem is most likely true?…
A: Given diagram contains two Routers R1 and R2.Each Router contains two ports and each port contains…
Q: What kind of memory is being utilised for the primary storage?
A: - We need to talk about the type of memory utilised for primary storage.
Q: Which programming principle indicates that code should be stored in the same structure as the data…
A: INTRODUCTION: The proper phrase for the object-oriented programming principle states that code…
Q: What is the Classic CPU Performance Equation and how does it work?
A: Introduction: Computer programs are executed by a central processing unit (CPU), sometimes known as…
Q: Explain to the following terminologies with illustrations: Bandwidth Latency Roundtrip Throughput…
A: Solution: Given, Explain to the following terminologies with illustrations: Bandwidth:…
Q: 8. If Eve wants to decode the message, she will need to know the inverse of the matrix you used to…
A: We need to find the total number of possible 3x3 matrices with entries belonging to the set…
Q: The logical operator that returns TRUE if the prepositions are the same. a.) NAND b.) EX NOR c.)…
A: Logic gates are the fundamental components of the any digital system. It's an electrical circuit…
Q: a Gantt chart of the process scheduling using preemptive, priority-based scheduling. Determine the…
A:
Q: 3. Create a script that will find the average of {-100, 97, 83, 21, -50, 20, 101, 30}. [THE USER…
A: Answer
Q: In what year did John von Neumann come up with the idea for the computer?
A: We will learn when did John von Neumann come up with the idea for the computer.
Q: In a buffer, what exactly happens to the data stored within is a mystery.
A: Introduction: Suppose the corporations whose data has been collected by the National Security…
Q: What are the steps involved in installing local software, portable software, and Web-based…
A: Introduction: A portable application (portable app) is a piece of software that can be moved from…
Q: Write a Java program to take a list of string from the user & print a list where each string has all…
A: PROGRAM INTRODUCTION: Import the required libraries. Start definition of the function to remove the…
Q: What skills do you think are needed in the call center industry
A: Communication skills (including continuous listening)The most important skill of a call center is…
Q: The default appearance of the Desktop in MATLAB three windows * :will appear. They are Current…
A: Three default appearance window given below :
Q: four websites, including Microsoft, Oracle and Cisco's websites, that are all among the most popular…
A: Introduction: Websites dedicated to the most up-to-date information about the security. Microsoft…
Q: Explain how SETI Institute computers work together to create an even more powerful system.
A: Introduction: SETI (Search for Extraterrestrial Intelligence) is an abbreviation that stands for the…
Q: The Fibonacci sequence is a sequence of numbers beginning with 0 and 1, in which every number after…
A: As per the requirement pseudocode is provided. Note: As per our guidelines we should not provide any…
Q: What are the three kinds of data that a computer saves in its memory?
A: Introduction: Memory on a computer Memory refers to the temporary storing of data for processing in…
Q: he tasks shown in the table late the Utilization he help of Gantt chart, prove that these tasks are…
A:
Q: Identify, identify, and define the six components of an information system.
A: -An information system is combination of six major components namely hardware ,software, network…
Q: Using DML SQL, write the appropriate SQL query for each of the following: Insert A new customer…
A: SEE ANSWER IN STEP NO. 5
Q: To open M-File in MATLAB we type edit open O start
A: Answer for the given question in in step-2.
Q: Which of the following is a concern when considering the use of a demilitarized zone (DMZ) firewall…
A: The above question belongs to web security domain of computer science and is solved below.
Q: recise distinction b
A: System space: Userspace is the concept in Linux which gives a block or set of virtual addresses…
Q: Q37 b/ Write a program in C++ to generate and print the following form: I 2 3 4 5 234 5 345 4 5
A: C++ program to generate a program in C++ to generate and print the pattern: 123452345345455…
Q: In what context do you use the term parallel computing?
A: Parallel computing is a kind of calculation where numerous estimations or cycles are completed at…
Q: 1) IEEE 754 Floating Point Standard: This standard is used to represent floating-point numbers (real…
A:
Q: What prompted the development of the computer?
A: Introduction What prompted the development of the computer?
Q: How can you ensure that your iOS apps have adequate test coverage?
A: We can ensure our iOS apps have adequate test coverage by doing 2 types of testing 1.iOS UI test…
Q: The reason why storage businesses put their lockers up for sale without first exposing what's inside…
A: Introduction: Auction: An auction is a process used to buy and sell properties and products. The…
Q: Describe in detail the concept of cloud computing, including the benefits of employing it?
A: Describe in detail the concept of cloud computing, including the benefitssofemploying it?
Q: Write a Python program that will ask the user for his/her weight (in kilograms), then compute and…
A: As given, we need to write a Python program that takes user weight(in kilogram) as input, compute…
Q: Using security engineering approaches, explain the DDoS attack in detail (Use-Case diagram and…
A: DDoS stand for "Distributed Denial of Service Attack" and it is a cybercrime in which the attacker…
Q: Computer Science You have been hired as a systems analyst to work with two other analysts. Your…
A: Name: apply for post office box Actors: user Description: For availing PO services user needs to…
Q: What exactly is a write buffer?
A: Introduction: A write buffer is a data buffer found in Intel's x86 and AMD64 CPU cache designs.
Q: It is permissible in certain cases to provide the client copies of the auditor's previous documents.…
A: Documentation of Audits Audit Documentation - This term refers to the auditors' track records of…
Q: Using C as a programming language, Implement a queue using: I) array and II) linked list
A: Implement queue using Array Linked list
Q: Give some instances of key operational and customer performance indicators that might be included in…
A: Introduction: A key performance indicator (KPI) or metric for operations is a discrete measurement…
Q: What qualities does Von Neumann's architecture possess?
A: INTRODUCTION: The CPU accepts instructions and data from an input or memory in most computer…
Q: A square number is an integer number whose square root is also an integer. For example 1, 4, 81 are…
A: The answer is
Q: When utilising IPsec, how do you ensure that each workstation has its own private key pair?
A: Introduction: Internet Protocol Security (IPSEC) is an acronym for Internet Protocol Security. In…
Q: Write a program that reads from the user the initial KiloMeters of the car, the current KiloMeters,…
A: Answer
Trending now
This is a popular solution!
Step by step
Solved in 3 steps with 3 images

- A(n) __________ is an integer stored in double the normal number of bit positions.A)The decimal number 162 what is the binary representation of it ? B)the decimal number of -53 what is the binary representation of it ?D. What is the minimum number of binary bits needed to represent each of the following unsigned decimal integers?I) 65II) 409III) 16385
- 2) What is the largest binary number that can be expressed with 16 bits? What are the equivalent decimal and hexadecimal numbers?1. Write down the mathematical notation for fixed point representationand floating representation and also explain each term. 2. Consider the following machine number in 64 bit and Precisely represent the above machine number in decimal digits. 0 10000000011 1011100100010000000000000000000000000000000000000000Computer Science In a 16-bit big endian machine, how is the text “TX” stored in a word? In a 32-bit little endian machine, how is the text "Arkansas" stored in two words? Write down the binary bits.
- Assume a 24-bit word on a computer. In these 24 bits, wewish to represent the value 295.1. a) How would the computer represent the decimal value295?2. b) If our computer uses 8-bit ASCII and even parity, howwould the computer represent the string 295?3. c) If our computer uses packed BCD with zero padding, howwould the computer represent the number +295?1,(2504)_8 to hexadecimal. 2,(413.51)_6 to base 9. 3, decimal numbers A = 5, B = 16, Why A = 5 = 00010 and B = 16 = 010000?4.2 a. What is the ASCII representation for the numeral −3.1415 in binary? in octal? in hexadecimal? in decimal? b. What is the EBCDIC representation for the numeral +1,250.1? (Include the comma.)
- 1. The _______________ of a number system determines how many digits are used in the system and the value of digit positions. 2. A single binary digit is called a(n) _______________. 3. A group of eight bits is called a(n) _______________. 4. Bytes can be grouped together into a(n) _______________, the size of which is machine-dependent. 5. What is the decimal equivalent of the hexadecimal number 1C9F? ______________2) What is the largest binary number that can be expressed with 16 bits? What are the equivalent decimal and hexadecimal numbers? 3) Convert the hexadecimal number 64CD to binary, and then convert it frombinary to octal.5. Assume the simple floating point model (i.e., 14-bits of storage) correctlya. How would we represent the numbers 67.25 and 47.98?b. Add the two numbers together. Show the calculation and the final format ofthe result. PS: Please do them in a word processor not hand-written nor in a JPEG screenshot Format!!

