55 60 65 75 70 80 85 90
Q: What benefits come from ICT use in business and education?
A: ICT, or information and communications technology, is the infrastructure and components that make…
Q: If a large computer process or program is broken down into smaller ones, do the resulting subsystems…
A: Processes are segmented. Segments are non-uniform software portions. Segmentation gives users a…
Q: Below is an explanation of the differences between MonthCalender and DateTimerPicker.
A: Please find the answer in next step
Q: How important is it for students to use technology to help them with their studies when it comes to…
A: How important is it for students to use technology to help them with their studies when it comes to…
Q: Briefly outline the idea of the BestFit memory allocation strategy in the context of a variable…
A: Introduction BestFit memory: The free/busy list is maintained using this manner from smallest to…
Q: What kind of cyber security dangers will you be preparing for when developing an integrated…
A: Introduction: Cybersecurity hazard means your organisation might lose money from a cyber-attack or…
Q: Draw the exchanges of numbers for a four-dimensional hypercube, using the parallel hypercube…
A: Introduction: An algorithm is used to solve a problem or conduct a calculation. Algorithms function…
Q: An analog signal carries 4 bits in each signal unit. If 1000 signal units are sent per second, then…
A: The question is solved in step2
Q: how can technological competiveness of smart greenhouse be further achieved for both the consumer…
A: The above question is solved in step 2 :-
Q: In this python practice problem, you should be able to filter a dictionary based on upper and lower…
A:
Q: An explanation of how the DBMS could combine several heuristic rules and cost estimation tactics…
A: Introduction: A software program called a database management system (DBMS) is used to store and…
Q: Which IP address should you set your firewall to block from entering your internal network?…
A: IP address : Each device (such as a computer or printer) connected to a computer network and using…
Q: Find a recursive formula for the sequence: 2, 5, 10, 17, 26 Not the closed formula or non-recursive…
A: Dear Student, The recursive formula is given below -
Q: Thank you! Need references for this answer
A: References for an answer are : 1) Comparison of Neighbor Discovery to ARP and Related IPv4 protocol…
Q: Question AAch Full explain this question and text typing work only We should answer our…
A: Interpretation of the question As per the graph the following points are given :- This graph…
Q: you
A: Dear Student, The answer to your question is given below -
Q: Write a C program to print "Hello World" in the output.
A: The above question that is to write C program to print Hello world in the output is answered in…
Q: How about you summarise the findings of annual surveys and surveys funded by agile product companies…
A: Introduction: Agile methodology is a strategy that encourages continuous iteration of development…
Q: Compare different systems performance measurement tools such as availability, throughput, turnaround…
A: Availability is defined as the quality of bringing available things. In other words, it is…
Q: Give a recursive definition for the set X of all binary strings with an even number of 0's. B₁. λ is…
A: Recursive Function: In programming, a recursive function is a routine that calls itself…
Q: Give a recurrence relation for W(n),
A: A recurrence is an equation or inequality that describes a function in terms of its values on…
Q: ough the benefits of cloud storage and why businesses need to back
A: The cloud storage can be denoted as a model of computer data storage where digital data is stored in…
Q: Please use C++ and make sure it's for a sorted array Write a function, removeAll, that takes three…
A: To Write a function removeAll()
Q: The technology team needs 157 addresses. How large is the subnet space being assigned to them?
A: The above question is solved in step 2 :-
Q: When it comes to backing up your data, what are the most crucial factors to consider?
A: To talk about why backups are important and how to avoid data loss Solution: Backup is the process…
Q: discuss why End-User License Agreement (EULA)is important in software security.
A: End-User License Agreement (EULA) : An End-User License Agreement (EULA) is a legal contract between…
Q: Where does MySQL excel and where does it fall short?
A: It is renowned for having a safe and trustworthy database management solution. Transactional tasks…
Q: L₁ = {a"ba": n ≥ 0,m>0} Use the rule of contradiction, prove that following language is regular or…
A: I have given written solution of the above problem. See below steps.
Q: Discuss the most common sources of risk in IT projects and the steps used to lessen or eliminate…
A: IT: IT stores and retrieves data using computer systems. It's leveraging technology to make business…
Q: Recursive formula for 2, 5, 10, 17, 26 in the form of a_n = a_n-1 + Cn + D
A: Recursive formula " defines any term of a sequence in terms of its preceding term(s)"
Q: Ara Howard created a project called Fattr which implements a common desire among Ruby developers: a…
A: Here is an illustration of the issue. You would have to create the method yourself in order to…
Q: What applications of ICT may there be?
A: This paper examines the application of ICT and the use of ICT tools in academic libraries, the…
Q: Create a C++ programme that displays the following menu: 1. Determine the Area of a Circle 2.…
A: The source code of the program #include<iostream> #include<iomanip> #define PI 3.142…
Q: In the classic problem FizzBuzz, you are told to print the numbers from 1 to n. However, when the…
A: Implementing FizzBuzz in a single thread will be the first step.
Q: Cross-validation can be used to get rid of A Local minima B none of the answers ⒸOverfitting D…
A: Cross-validation : Cross-validation is a technique used to evaluate and validate the performance of…
Q: How do I fix this code please read intructions( in java)
A: The java program is given below:
Q: 3. Translate the following Caesar Cipher: (Key, Shift alphabet to the left by 2) Gd wms ayl peyb…
A: - We are currently working on ceaser cipher where we have to shift left two alphabets.
Q: For what reasons will consumers benefit from digital financial services?
A: Digital financial services benefits include: 1.An innovative corporate culture: Only 26% of…
Q: Is there a regulatory framework that addresses cyber security, and if so, what are its strengths and…
A: Introduction:- A cybersecurity framework is a set of guidelines that, when followed, provide a…
Q: Match the following Windows PE commands to their description. Set - Tree - Vol - WPEUTIL ✓ Set ✓…
A: Solution: Given,
Q: The intent of the DSL is to specify commands which forward to another object, but which always…
A: The question is solved in step2
Q: An analog signal carries 4 bits in each signal unit. If 1000 signal units are sent per second, then…
A: Given: The signal carries 4 bits in each signal unit, it means 4 bit/signal unit. 1000 signal units…
Q: Fattr makes the decision that the getter method color will not merely be a getter, but can function…
A: Fattr decides that the getter method colour will have the ability to act as both a declarative…
Q: Convert the following subnet masks to /k notation, and vice-versa: (a). 255.255.240.0 (b).…
A: The octet division table is shown. On the basis of that, we will answer the questions below.
Q: In Fibonacci's model, rabbits live forever. The following modification of Definition 3.1 accounts fo…
A: G(1) = 1 G(2) = 1 G(3) = 2 G(4 ) = 3 G(5) = 5 G(6) = 8 G(7) = 13 G(8) = 21…
Q: In Java Assume code that has imported Scanner and instantiated it for keyboard input as stdln.…
A: In java process to create array is: first declare array ://sets variable with data type then…
Q: Consider the following recurrence relation: P(n) = {. P(n-1) + 1 Prove by induction that P(n) = 50 -…
A: Introduction Recurrence relation:An equation that represents a sequence based on a rule is called a…
Q: If you create a thorough information management strategy for your company, how many cyber dangers…
A: Introduction: Internet- and digitally-dependent businesses are transforming cyber security.…
Q: What constitutes a good security awareness program when there is no yearly cyber security training,…
A: Introduction: Network protection and cybersecurity threat best practisesYour company's data is…
Q: create a function my_code(u) that sorts a list of words alphabetically using a FOR loop. example:…
A: As we are talking about "list" for representing the array values, the programming language we are…
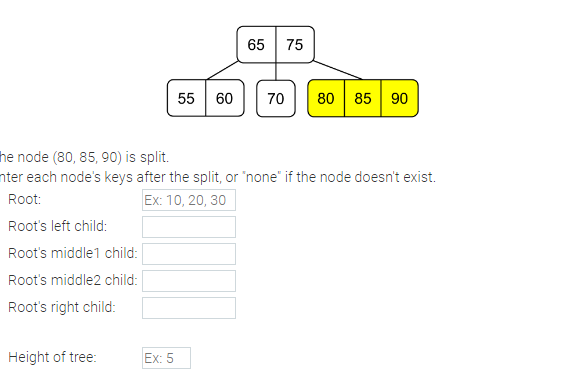
Java - The node (80, 85, 90) is split. Enter each node's keys after the split, or "none" if the node doesn't exist.
Trending now
This is a popular solution!
Step by step
Solved in 2 steps

- 1) In a tree, an interior node is a node that has no children. a. True b. False 2) In a tree, the root item has no parent item. a. True b. Falseclass BST: def __init__(self, root = None): if root != None: root.setparent(None) self.__root = root def getroot(self): # Returns the root node of the tree ####################################################################### # Remove the pass and write your code ####################################################################### pass ####################################################################### # End code ####################################################################### def setroot(self, node): # Sets the root node of the tree ####################################################################### # Remove the pass and write your code ####################################################################### pass ####################################################################### # End code…Part 1: create random binary trees For each tree, create a tree according to the following procedure. Toss a fair coin up to 100 tossesStart from the root node as current node. A: Perform a toss: determine whether the current node will have at least one descendent. If Head, there is at least one descendent. Then go to B. If Tail, there is no descendent. Then go to D. B: Perform a toss: determine whether the current node will have one or two children. If Head, the current node will have one child. Then go to C.If Tail, the current node will have two children. Assign two random integer values to the two children. Then go to D. C: Perform a toss: determine whether the current node will have left or right child.If Head, the current node will have a left child. Assign a random integer value to the child. Then go to D.If Tail, the current node will have a right child. Assign a random integer value to the child. Then go to D. D: move the current node to the next node (using…
- int doo(node<int>*root){ if(root !=0 ) { if(root->left==0 && root->right==0) return root->data; int L=doo(root->left); int R=doo(root->right); if(L>R) return R; else return L;} } this code used for a. find the sum of leaves items in a binary tree b. find the minimum item in a binary tree c. find the minimum item in the leaves of a binary tree d. the maximum item in the leaves of a binary treeHuffman coding assigns variable length codewords to fixed length input characters based on their frequencies. More frequent characters are assigned shorter codewords and less frequent characters are assigned longer codewords. All edges along the path to a character contain a code digit. If they are on the left side of the tree, they will be a 0 (zero). If on the right, they'll be a 1 (one). Only the leaves will contain a letter and its frequency count. All other nodes will contain a null instead of a character, and the count of the frequency of all of it and its descendant characters. For instance, consider the string ABRACADABRA. There are a total of characters in the string. This number should match the count in the ultimately determined root of the tree. Our frequencies are and . The two smallest frequencies are for and , both equal to , so we'll create a tree with them. The root node will contain the sum of the counts of its descendants, in this case . The left node will be the…int doo(node<int>*root){ if(root !=0 ) { if(root->left==0 && root->right==0) return root->data; return doo(root->right); } } this code used for a. find the maximum item in a binary search tree if it has a right sub tree b. find the number of right leaves in a binary tree if it has a right sub tree c. find the maximum item in a binary tree if it has a right sub tree d. find the first right item in the binary tree if it has a right sub tree
- Please draw the following:Form a binary tree with the root node holding 20, the left and right child of the node holding 20 respectively holding 75 and 43. The next level nodes hold the data 84, 90, 57 and 71 from left to right. The node holding 84 has left and right children that respectively hold 96 and 91 and the node holding 90 has a left child that holds 93.Implement a Binary Search Tree (BST). Implement the following tree operations: a. new (create a new tree) b. isEmpty (determine if the BST is empty. Will display either True or False) c. isLeaf (determine if the node is a leaf. Will display either True or False) d. path (will display the path in BST from a root to the node. If the node is present it will will display the complete path otherwise will display "Null") e. search (will search the BST for a key/value. if the key is present it will will display "Present" otherwise will display "Absent") f. insert (will insert a key as a node in the BST; acts as root, left and right from the prior activity) g. delete (will delete a key from the BST) h. transversal (will display all the nodes in a BST; Use either Breadth or Inorder transversal from the prior activity)Postorder: 7 6 8 5 2 9 4 10 3 1 Inorder: 6 7 2 5 8 1 4 9 3 10 After drawing the tree, at what level does node 10 belongs? (Numeric Answer ONLY)
- In Java, True or False: Every binary tree has at least one node. TRUE FALSE Every non-empty tree has exactly one root node. TRUE FALSE Every node in a binary tree has at most one child. TRUE FALSE Every non-root node in a binary tree has exactly two parents. TRUE FALSERefer to the tree on the picture and answer the following questions 1. Aside from its children, list 2 other descendants of node C. Your answer must be values that are adjacent when the nodes are arranged alphabetically in ascending order. For example, the descendant nodes are: ABX Y. You cannot answer A X since you have skipped B and B Y since X has been skipped. * 2. What is the path from node A to node L? * 3. What is the length of the path from node C to node N? Note: answer with the number's symbol and not the word form of the number.* 4. List 2 nodes that are at level 2 of the tree. Your answer must be values that 1 point are adjacent when the nodes are arranged alphabetically in ascending order. For example, the nodes at a certain level are: A B X Y. You cannot answer A X since you have skipped B and B Y since X has been skipped. * 5. What is the height of the tree? Note: answer with the number's symbol and not the word form of the number.* 6. What is the height of node C? Note:…Postorder: 7 6 8 5 2 9 4 10 3 1 Inorder: 6 7 2 5 8 1 4 9 3 10 After drawing the tree, what/who is the parent node of node 8? (Numeric Answer ONLY)











